Olanrewaju Timilehin
105 posts

Olanrewaju Timilehin
@Cybertimi06
Cybersecurity Specialist
เข้าร่วม Kasım 2024
73 กำลังติดตาม6 ผู้ติดตาม

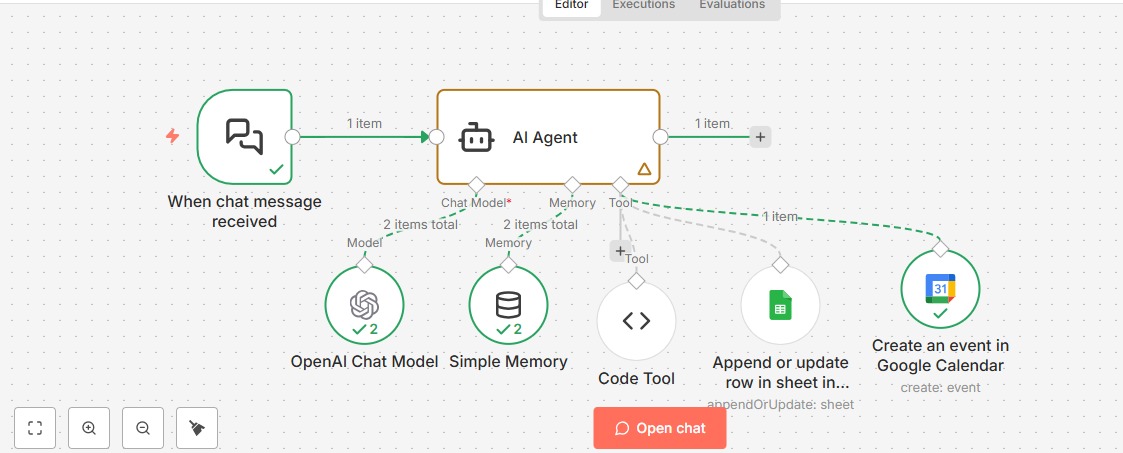
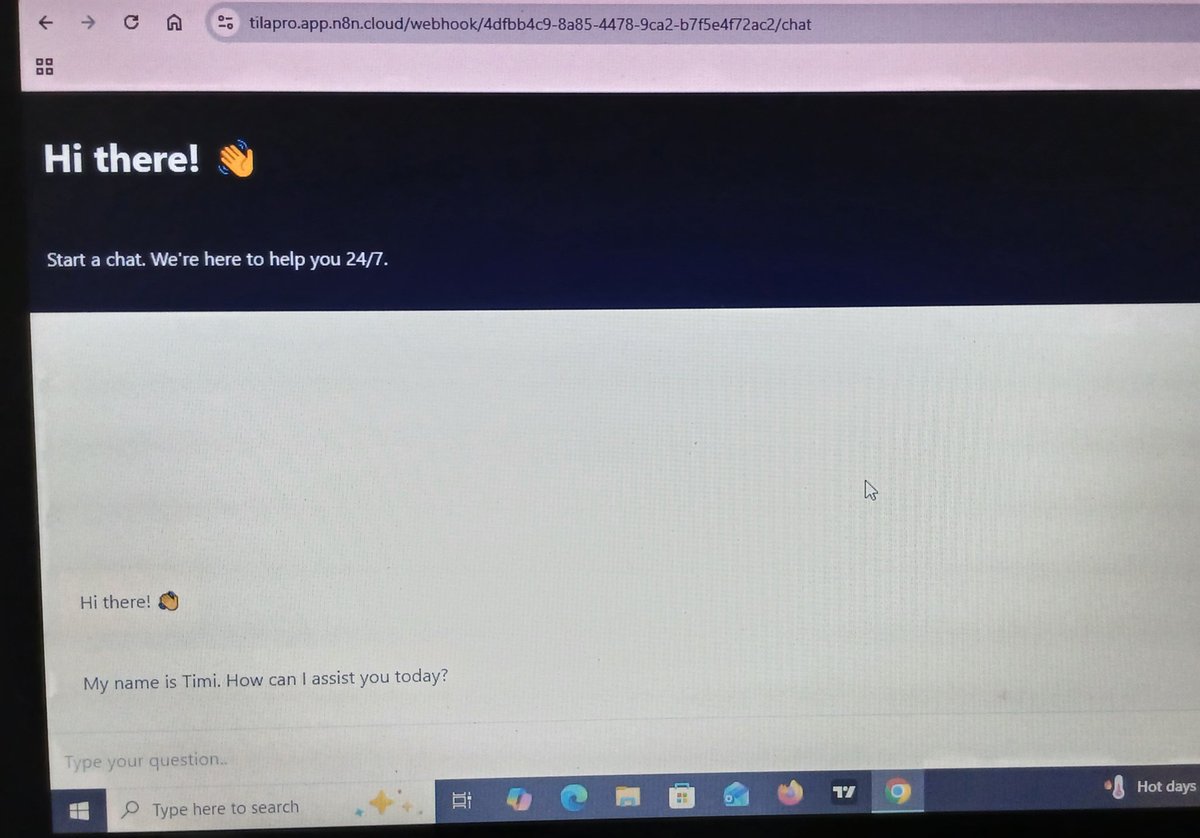
Day 2 of AI Automation. Today I signed up on n8n.io and also learnt how to run n8n locally using Docker.
English

On to the next challenge — always learning. 💪
#CTF #RedTeam #OffensiveSecurity #CyberSecurity #LearningByDoing
English

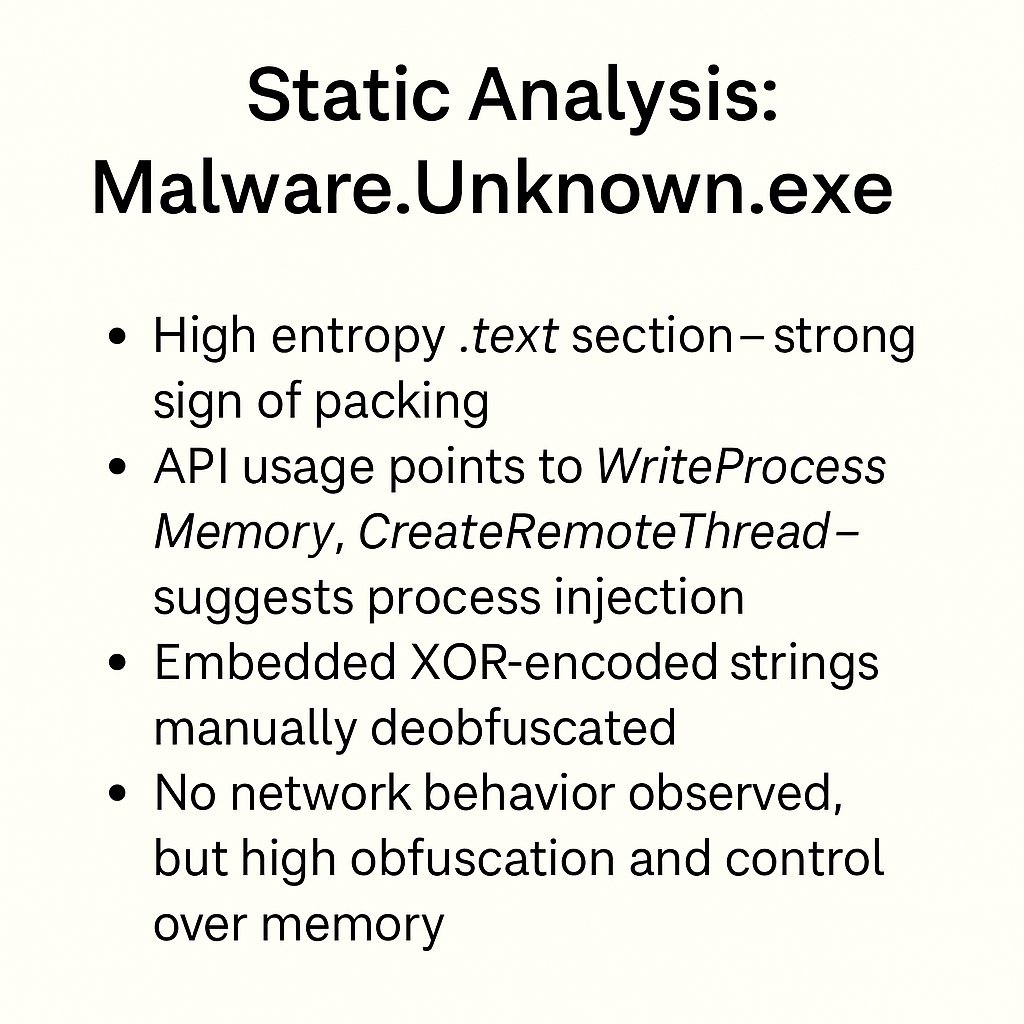
much can be uncovered.
📄 Full write-ups include PE header analysis, decoded strings, API mapping, and ATT&CK technique alignment.
#CyberSecurity #MalwareAnalysis #ReverseEngineering #RAT #StaticAnalysis #FLOSS #PEbear #InfoSec #DigitalForensics #BlueTeam #ThreatIntelligence
English

Reverse shells simulate real-world attacker behavior
Every input field in an app is a potential attack surface
💡 Ethical hacking is about learning how attackers think — so defenders can build stronger systems.
#Cybersecurity #EthicalHacking #ReverseShell #CommandInjection
English