Daniel Tan
416 posts


Daniel Tan
@DanielSlothx
Senior smart contract auditor | on-chain hacks analysis | Saved $200K tokens from the Phemex CEX hack

1/ stETH CAPO Misconfiguration Today, a misconfiguration on Aave's CAPO oracle caused wstETH E-Mode liquidations, resulting in a loss of 345 ETH. No bad debt was incurred, and all affected users will be fully reimbursed. More below.

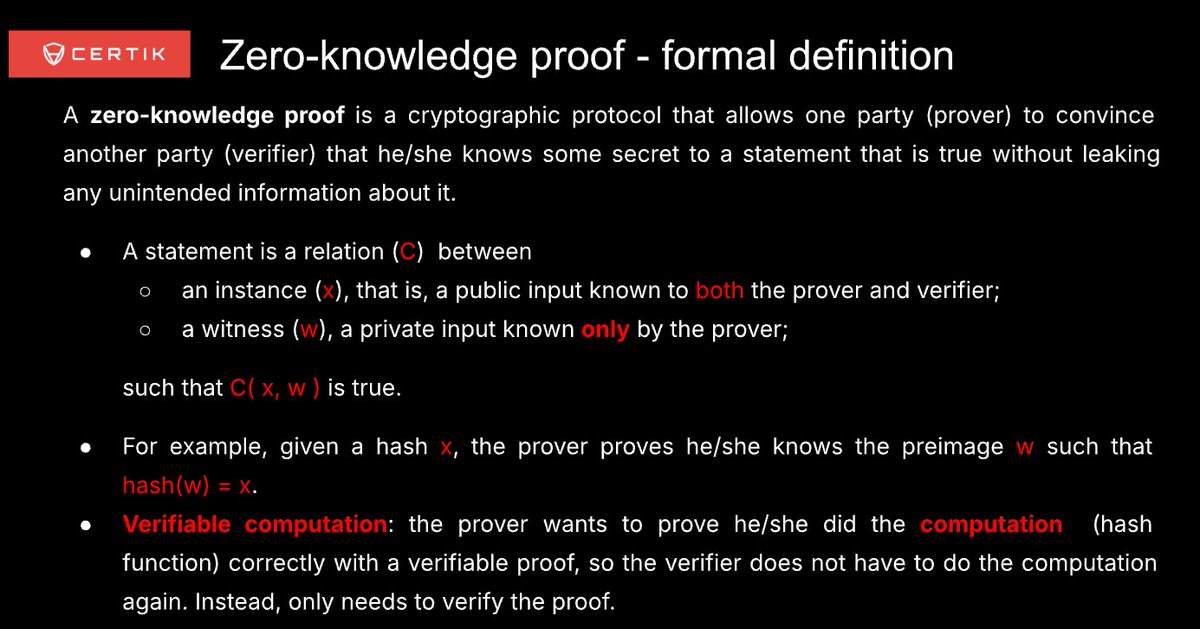
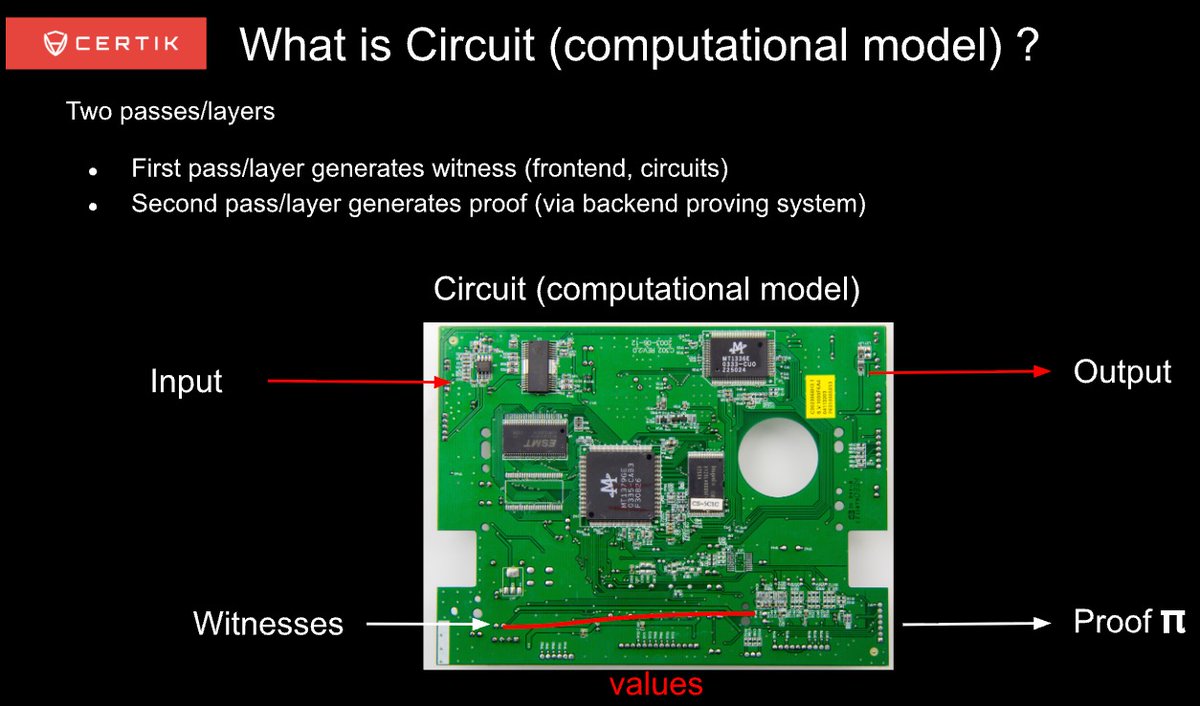
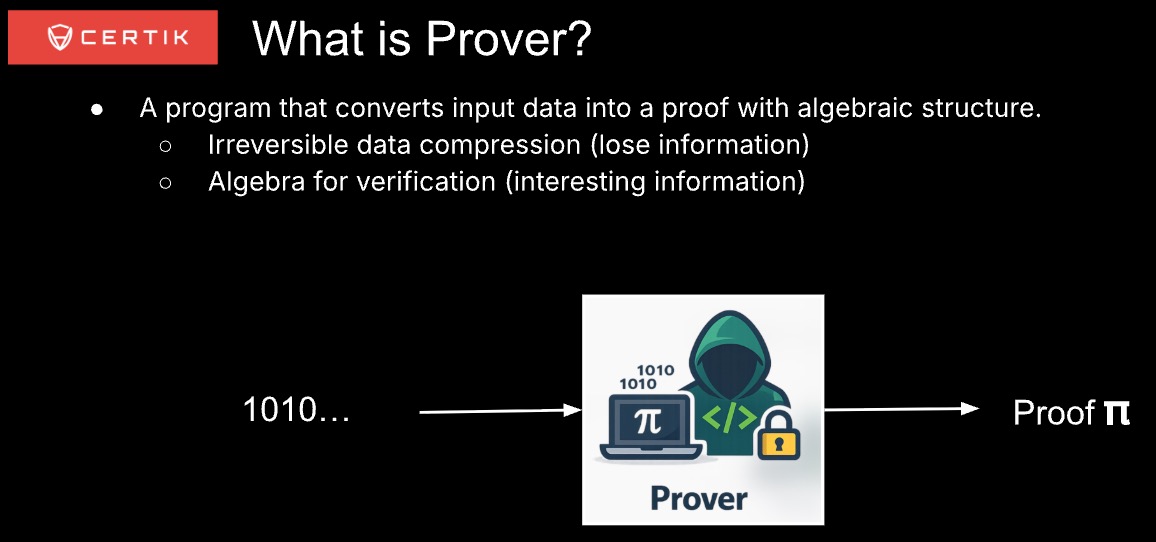
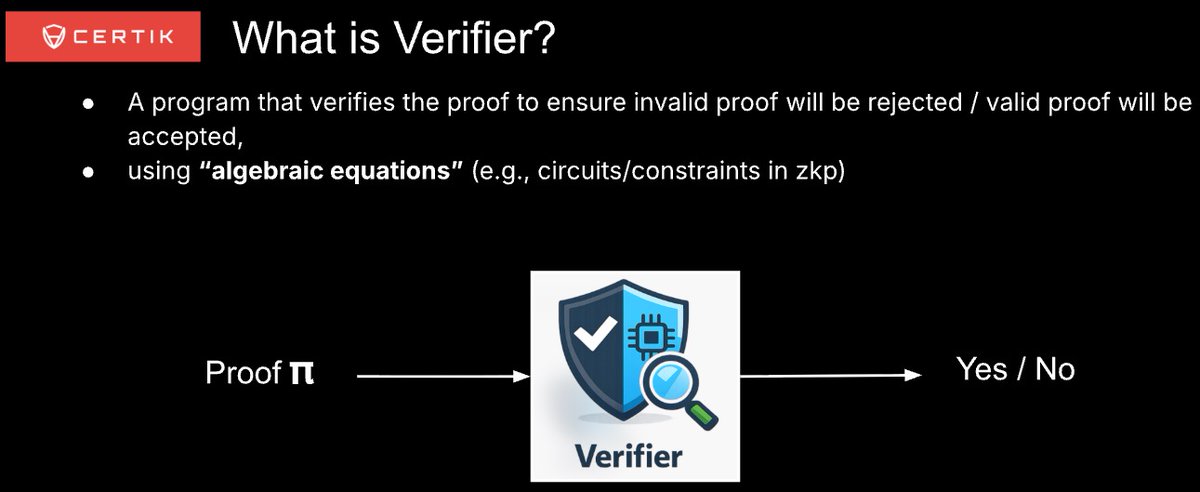


As ZK adoption accelerates, verifier-side security is increasingly critical. In this X Space, CertiK Sr. Staff Security Engineer Xifeng Jin examines attack patterns targeting DSL circuits, zkVMs, and proving systems with practical mitigation insights. Set a reminder below👇


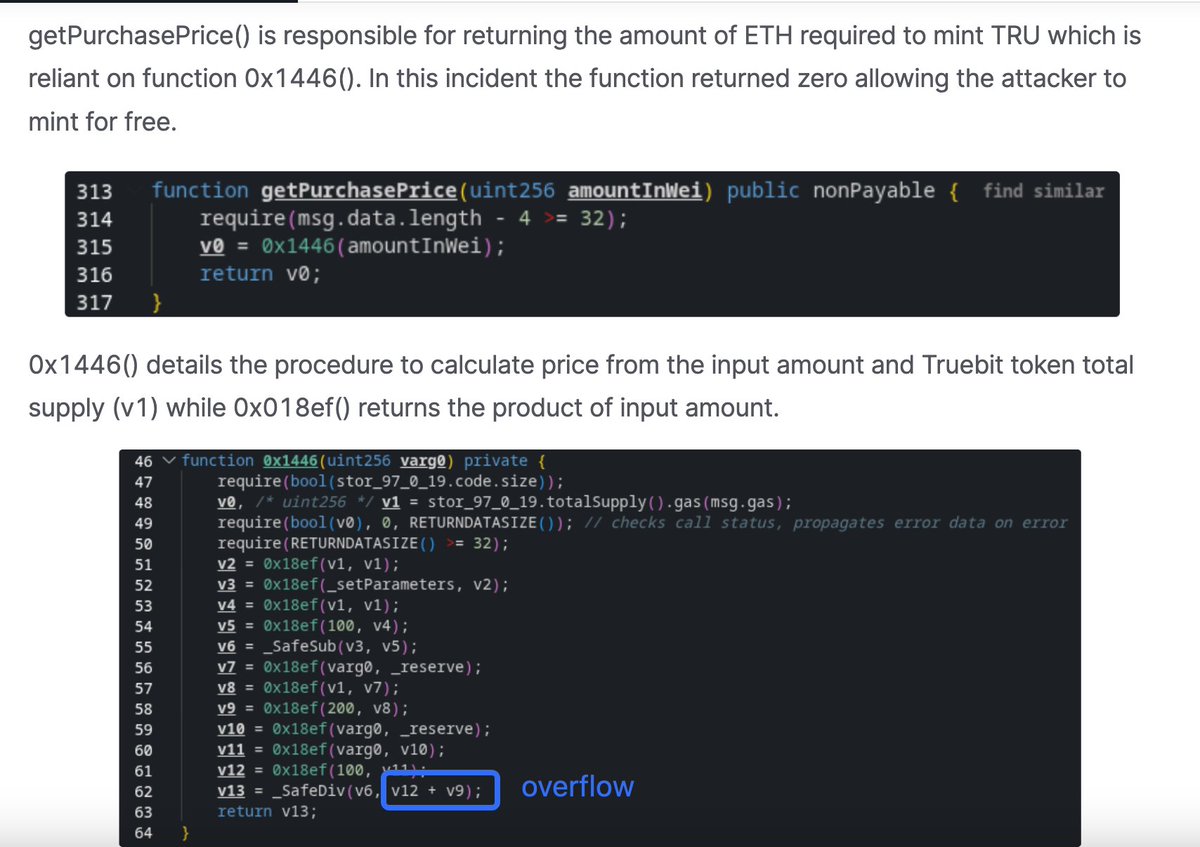
#CertiKInsight 🚨 On 8 January 2026, @Truebitprotocol was exploited due to an overflow issue, resulting in a loss of ~$26.6M. To learn more about what happened, read our full analysis here 👇 certik.com/resources/blog…



You’ve read the stats. Now see the scale. This video from the 2025 Skynet Hack3d Report brings Web3’s most critical security data into focus. Watch the key trends that defined the year.

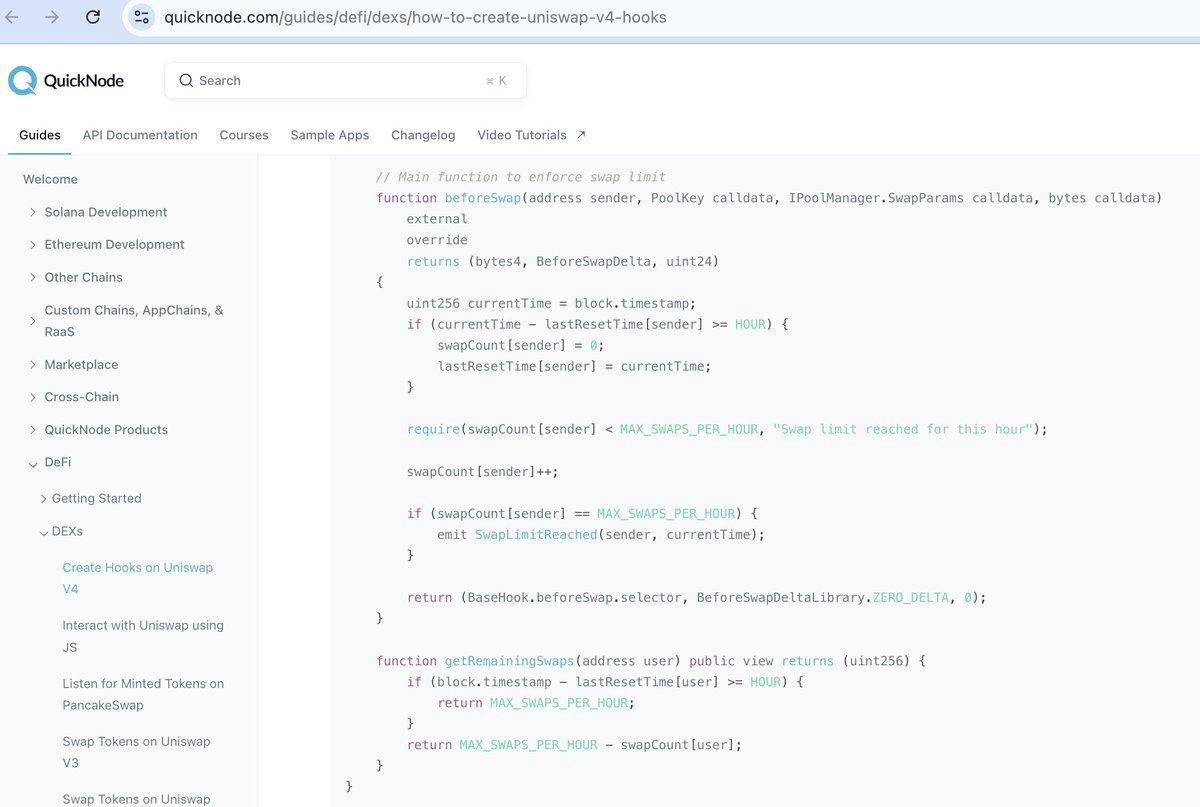
They implemented a "Swap Limiter" hook that restricts the number of swaps a single address can perform within a certain time frame. But the `beforeSwap` function is without access control, so anyone can call it and bypass the pool manager. Source: quicknode.com/guides/defi/de… 2/n