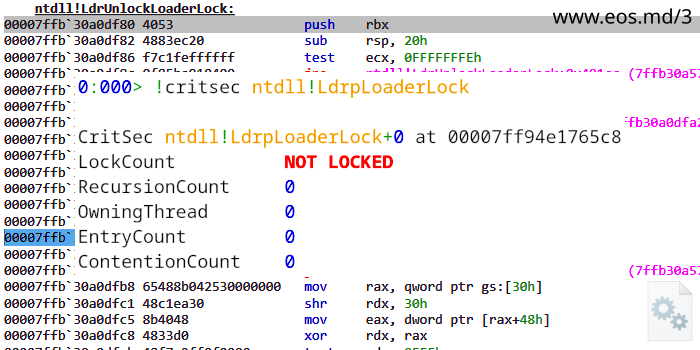
Calling all experts in Windows internals and low-level systems architecture! 'The Root of DllMain Problems' (or 'DllMain Rules Rewritten') is now in preparation for its final publication! Feedback and sign-offs from the community are greatly appreciated.
#the-root-of-dllmain-problems" target="_blank" rel="nofollow noopener">github.com/ElliotKillick/…
English