Volo@volo_sui
🔒 Security Incident Update - Volo Protocol
We want to address our community directly and transparently about a security incident that occurred earlier today. Rest assured, Volo is prepared to absorb any loss.
What happened:
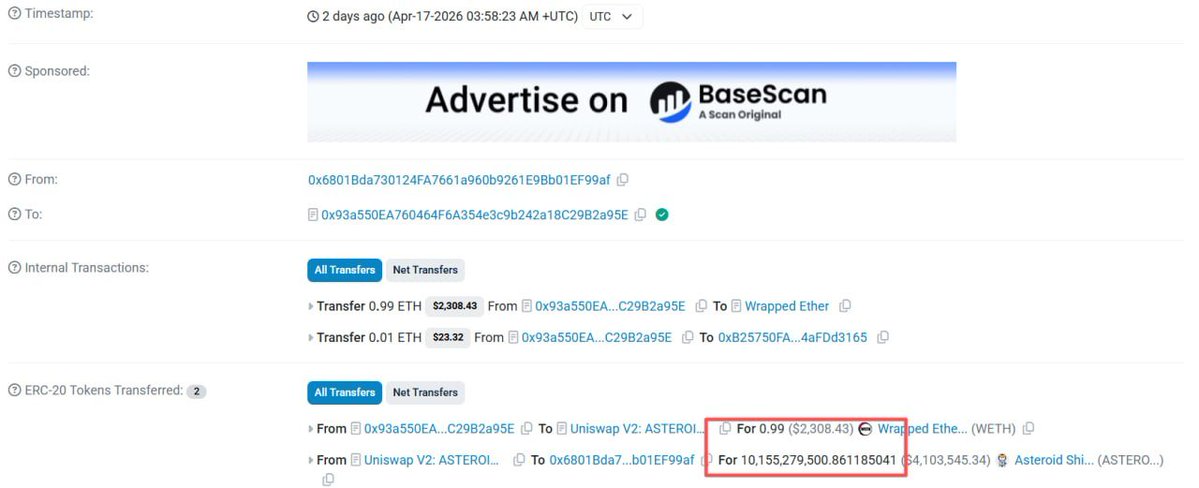
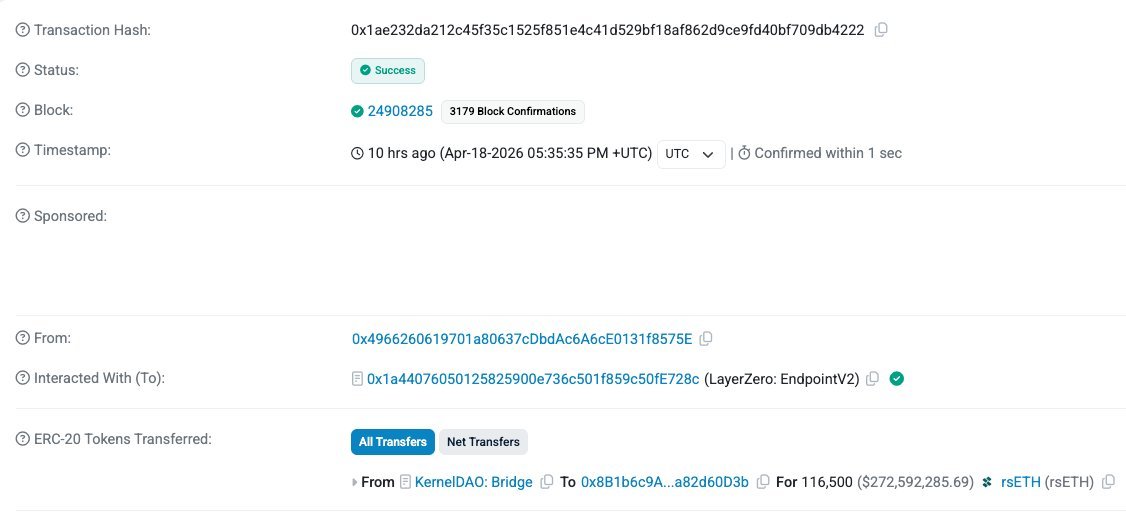
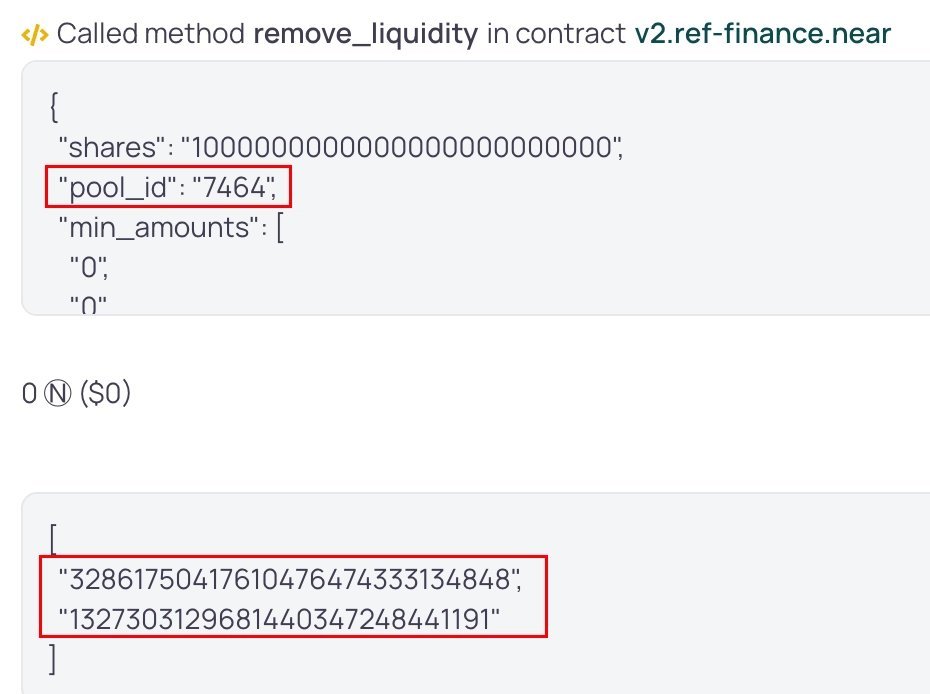
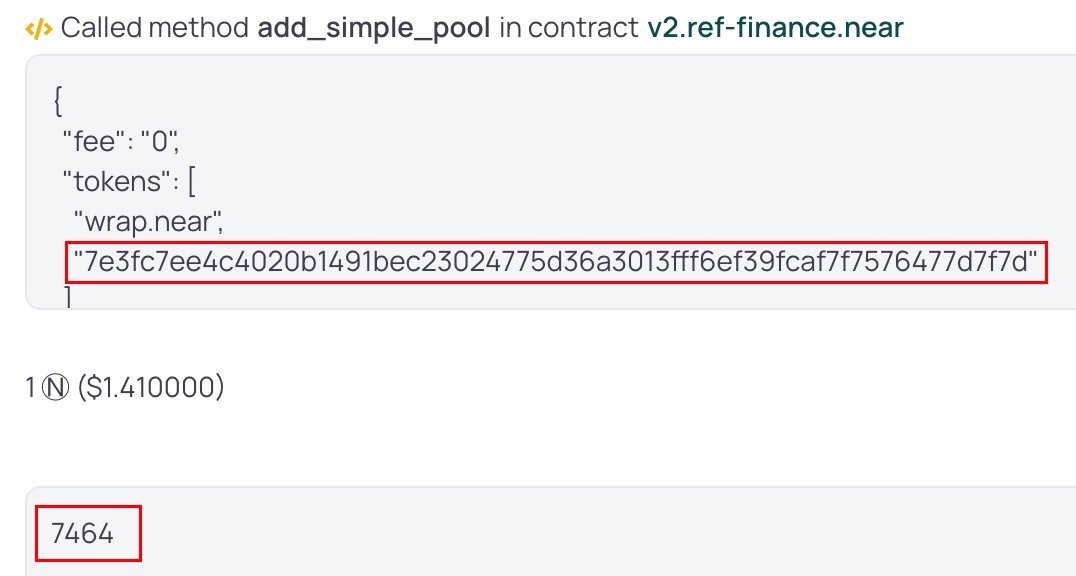
An exploit resulted in the removal of approximately $3.5M in assets (WBTC, XAUm, and USDC) from Volo Vaults.
We detected the attack, immediately notified the Sui Foundation and ecosystem partners to contain the damage, and froze the vaults to prevent any further exposure.
Current status:
🔹All Vaults are currently frozen pending a full post-mortem and remediation
🔹The remaining Volo Vaults carry no shared vulnerability and are safe
🔹We are actively working with on-chain investigators and ecosystem partners on further recovery
🔹A full post-mortem will be published once the investigation is complete
What this means for you:
The ~$28M in TVL across all other Volo vaults is safe. The exploit was isolated to 3 specific vaults, and we have confirmed no shared attack vector exists with the remaining vaults.
On absorbing the loss:
We want to be clear: Volo is prepared to absorb this loss. We will do our best not to pass this to our users.
We are in damage control mode now, but once that’s done, we will work out a remediation plan, and a full breakdown will be shared shortly.
We understand that trust is earned, and right now, we are focused entirely on actions.
Thank you for your patience and continued support.
The Volo Team