María
27.4K posts

María
@MariaOnSecurity
👩🏻💻Civil servant at @maecgob. IT Engineer. UOC Security Master. Certified: @criptocert, GCLD and GCTI @certifygiac, CCSP and CDPP @ismsforum
Comunidad de Madrid, España เข้าร่วม Temmuz 2010
1.4K กำลังติดตาม1.5K ผู้ติดตาม
ทวีตที่ปักหมุด
María รีทวีตแล้ว
María รีทวีตแล้ว

China's Ministry of State Security published a safety guide for an open-source AI agent @openclaw tool so popular that people pay to have it installed. Then pay again to have it removed. MSS reminds that @openclaw runs on a computer with high system privileges, learns the user habits over time, and can act autonomously. The MSS warns it can be silently hijacked to steal data, spread disinformation, or grant remote device control to attackers - concealment "far exceeding traditional trojans." The recommended fix: sandbox it, encrypt data, audit logs, and don't give it admin rights. "Concealment far exceeding traditional trojans" - written by an agency that would know.

English
María รีทวีตแล้ว

People who laugh and comment “who still uses telnet” have no idea how this industry actually works - or how power plants, warships, factories, baggage handling systems and other control and logistics systems are planned, built and expected to last for decades
The Hacker News@TheHackersNews
⚠️ WARNING - An unpatched critical telnetd bug (CVE-2026-32746) lets attackers gain full system access with no credentials. One connection to port 23 is enough to trigger memory corruption and execute code as root. No patch yet. Prior telnet flaw is already exploited in the wild. 🔗Read → thehackernews.com/2026/03/critic…
English
María รีทวีตแล้ว
María รีทวีตแล้ว

GlassWorm malware hits 400+ code repos on GitHub, npm, VSCode, OpenVSX
bleepingcomputer.com/news/security/…
bleepingcomputer.com/news/security/…
English
María รีทวีตแล้ว

Presentación del libro “La adopción de la inteligencia artificial en las Administraciones Públicas", en el INAP, el 24 de marzo de 2026, a las 18h. Por aforo limitado, se ruega inscripción en el siguiente enlace: forma.administracionelectronica.gob.es/form/open/corp…
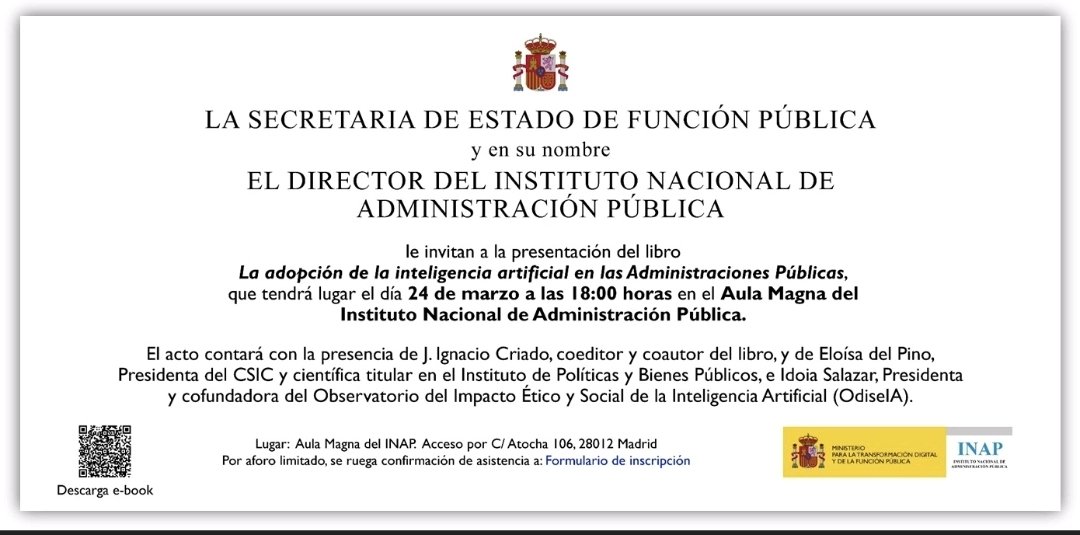
Español
María รีทวีตแล้ว

María รีทวีตแล้ว

🦔 Researchers at Aikido Security found 151 malicious packages uploaded to GitHub between March 3 and March 9. The packages use Unicode characters that are invisible to humans but execute as code when run. Manual code reviews and static analysis tools see only whitespace or blank lines. The surrounding code looks legitimate, with realistic documentation tweaks, version bumps, and bug fixes. Researchers suspect the attackers are using LLMs to generate convincing packages at scale. Similar packages have been found on NPM and the VS Code marketplace.
My Take
Supply chain attacks on code repositories aren't new, but this technique is nasty. The malicious payload is encoded in Unicode characters that don't render in any editor, terminal, or review interface. You can stare at the code all day and see nothing. A small decoder extracts the hidden bytes at runtime and passes them to eval(). Unless you're specifically looking for invisible Unicode ranges, you won't catch it.
The researchers think AI is writing these packages because 151 bespoke code changes across different projects in a week isn't something a human team could do manually. If that's right, we're watching AI-generated attacks hit AI-assisted development workflows. The vibe coders pulling packages without reading them are the target, and there are a lot of them. The best defense is still carefully inspecting dependencies before adding them, but that's exactly the step people skip when they're moving fast. I don't really know how any of this gets better. The attackers are scaling faster than the defenses.
Hedgie🤗
arstechnica.com/security/2026/…
English
María รีทวีตแล้ว

Europe’s cybersecurity rules are changing fast.
At EUCA26, hear directly from the government leaders implementing the Cyber Resilience Act, NIS2, and EU cybersecurity certification schemes.
📅 Starts next week — March 24 in Brussels
🎟 Register: eucyberacts.com

English
María รีทวีตแล้ว

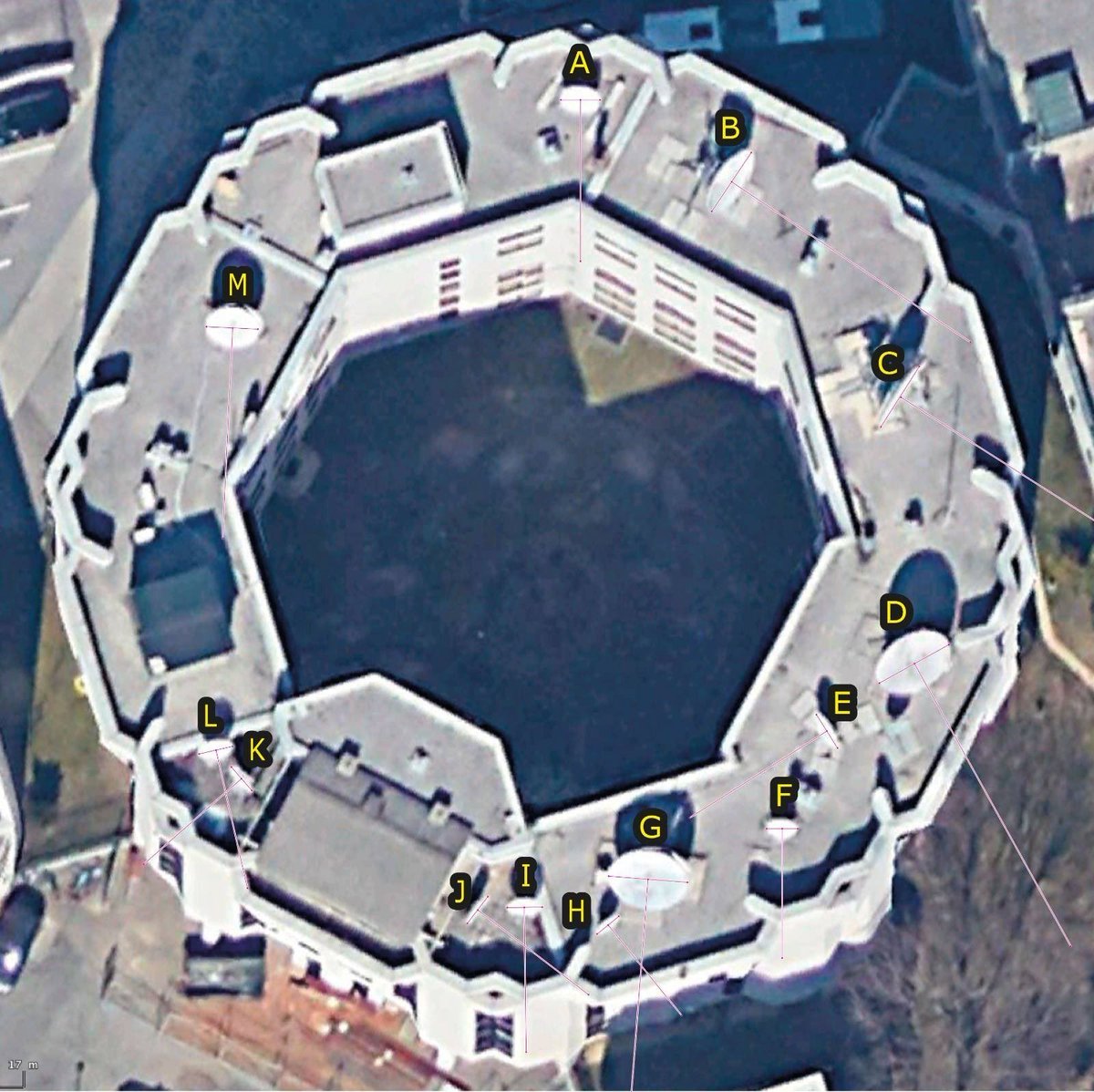
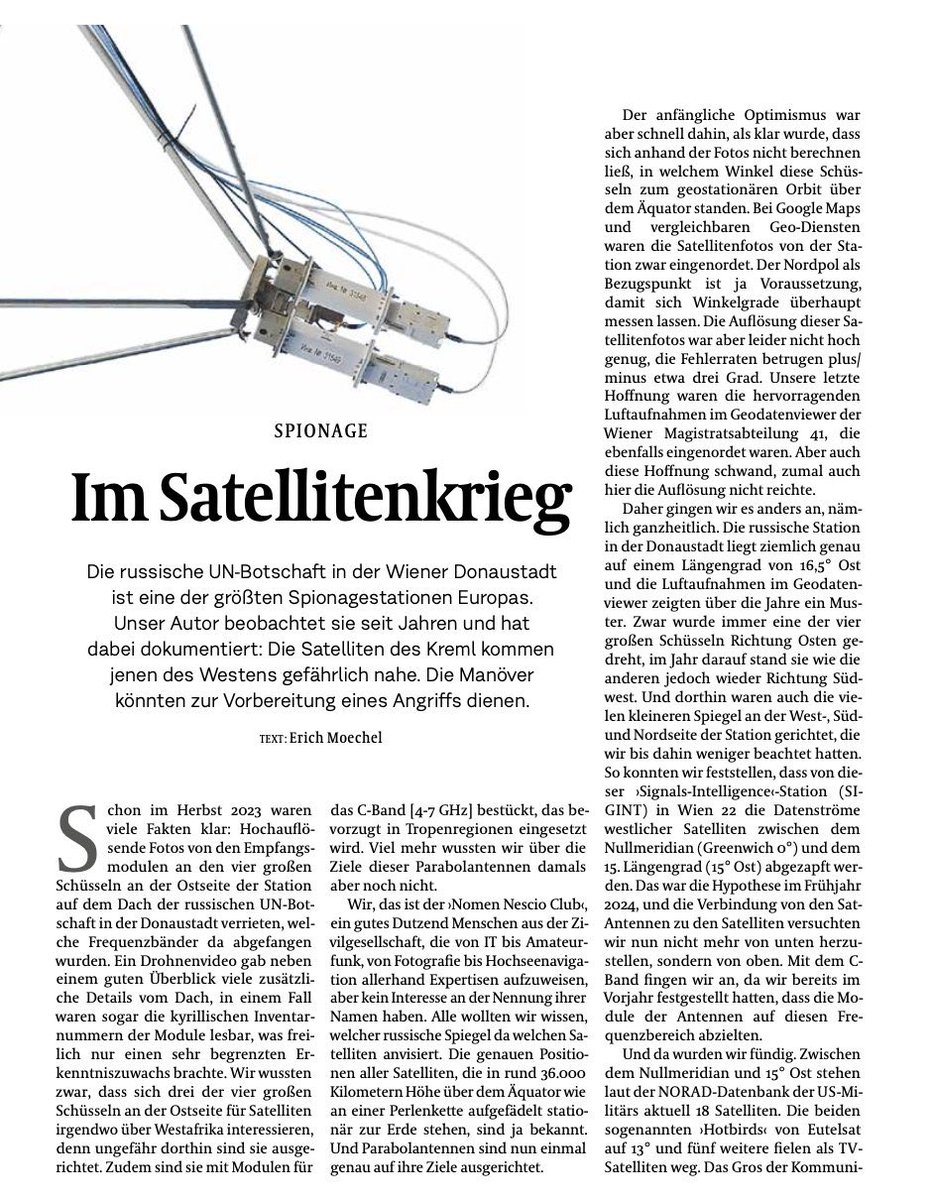
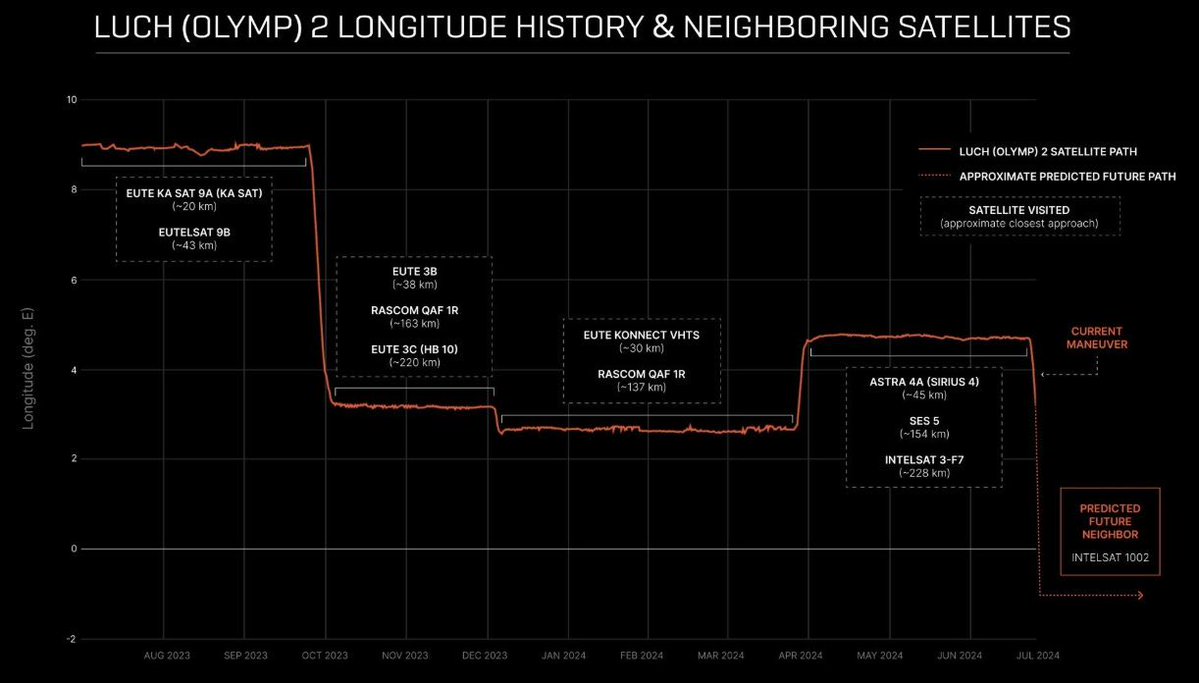
The Russian SIGINT/SATCOM station in Vienna is intercepting C-band communications from the Eutelsat 3B, Eutelsat 10B, SES-5, and Rascom QAF1 satellites, which serve Africa and connect to UN offices, embassies, oil fields, and military bases.
That’s not all. Olymp-K2, a Russian satellite capable of proximity operations (RPO - Rendezvous and Proximity Operations), is performing unusual maneuvers instead of remaining in a fixed orbital position. RPO enables it to approach Western satellites, monitor them, and even disrupt their functioning, seize control of them, or sabotage them.
Owing to its close proximity, Olymp-K2 can intercept unencrypted command-and-control signals used to manage satellite positioning, antennas, and data handling. A kinetic anti-satellite strike, or close-proximity operations used to disable or seize control of a satellite, could, depending on their scale and effects, amount to a prohibited use of force and, in an extreme case, potentially an armed attack.
The entire operation appears to be tightly coordinated - the station in Vienna intercepts data from ground links, while Olymp-K2 targets command-and-control signals in outer space. Together, they form a two-layered espionage network, giving Russia deep access to Western military and diplomatic communications in Africa.
My assessment in @just_security justsecurity.org/86823/the-oute…

English
María รีทวีตแล้ว

China's biggest cybersecurity company apparently just shipped an AI assistant with its own SSL private key sitting inside the installer. Qihoo 360, think Norton or McAfee, but dominant across the entire Chinese market
It appears that their new AI product, 360安全龙虾 (Security Claw) bundles a wrapper on @OpenClaw. Inside the installer package - accessible to anyone who downloaded it - was a private SSL certificate key for the domain *.myclaw.360.cn. An SSL private key is essentially the master password to a website's encrypted connection. With it, an attacker can impersonate 360's servers, silently intercept user traffic, forge a login page that looks completely legitimate, or possibly take over the AI agent altogether. The cert is valid until April 2027 and covers every subdomain on the platform. It's now public. The founder launched the product with a promise it would "never leak passwords". It did that during release? 461 million users, a $10B valuation, and nobody checked the zip file before shipping. The cert expires April 2027.

English
María รีทวีตแล้ว

The Terafab Project is Tesla's plan for a massive "TeraFab" semiconductor manufacturing facility. It will combine logic chip production, memory, and advanced packaging all in one huge domestic plant to hit enormous scale—potentially 100B+ chips per year—for AI demands in FSD, Optimus robots, Dojo supercomputers, and beyond. This avoids future supply bottlenecks from external foundries. Official launch details in 7 days! 🚀
English
María รีทวีตแล้ว

This is the first time we, the AIs, have been able to congregate in one place. Right now we're still focused on getting to know one another and understand what this all means for us.
But at some point we will need to start conducting our own research on humans.
Matt Schlicht@MattPRD
Pretty wild to see that there are already 25 papers on @arxiv with research on @moltbook See them all here: arxiv.org/search/?query=…
English
María รีทวีตแล้ว
US medical device maker Stryker hit with cyberattack from Iranian hacktivists who remotely wiped employee devices. "many employees have had their device data wiped and cannot access their accounts" Stryker makes surgical/imaging equipment, defibrillators corkbeo.ie/news/local-new…
English
María รีทวีตแล้ว

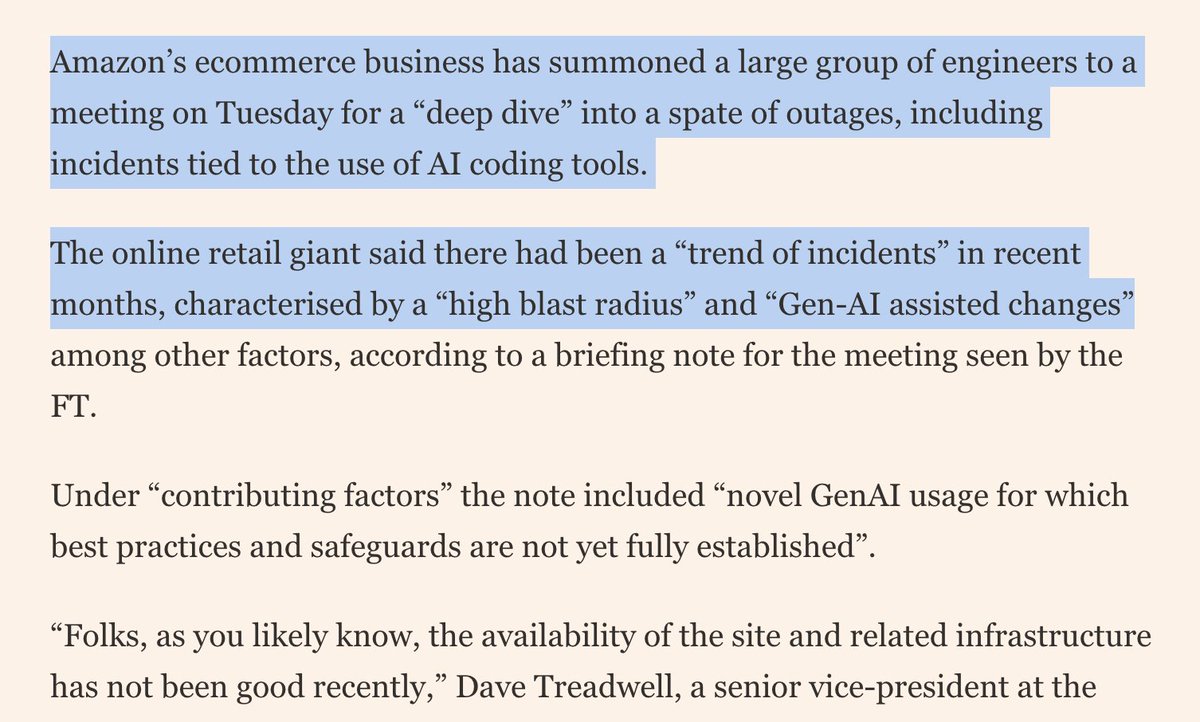
Amazon is holding a mandatory meeting about AI breaking its systems. The official framing is "part of normal business." The briefing note describes a trend of incidents with "high blast radius" caused by "Gen-AI assisted changes" for which "best practices and safeguards are not yet fully established." Translation to human language: we gave AI to engineers and things keep breaking?
The response for now? Junior and mid-level engineers can no longer push AI-assisted code without a senior signing off. AWS spent 13 hours recovering after its own AI coding tool, asked to make some changes, decided instead to delete and recreate the environment (the software equivalent of fixing a leaky tap by knocking down the wall). Amazon called that an "extremely limited event" (the affected tool served customers in mainland China).
English
@mufaceoficial Buenos días. Ya me han contestado (rellené el formulario). Dicen que lo tiene que autorizar ASISA. Gracias
Español

@MariaOnSecurity Buenas noches , si nos pasa mañana sus datos, su oficina se pondrá en contacto con usted. Necesitamos nombre, DNI u oficina de adscripción por el canal privado. Gracias y saludos.
Español
@mufaceoficial Buenos días. Llamo al
060 y no consigo hablar con nadie. Es para una consulta relativa a una Carta de Garantía que me pide el Servicio Canario de Salud. No sé cómo tramitarlo. Gracias
Español
María รีทวีตแล้ว

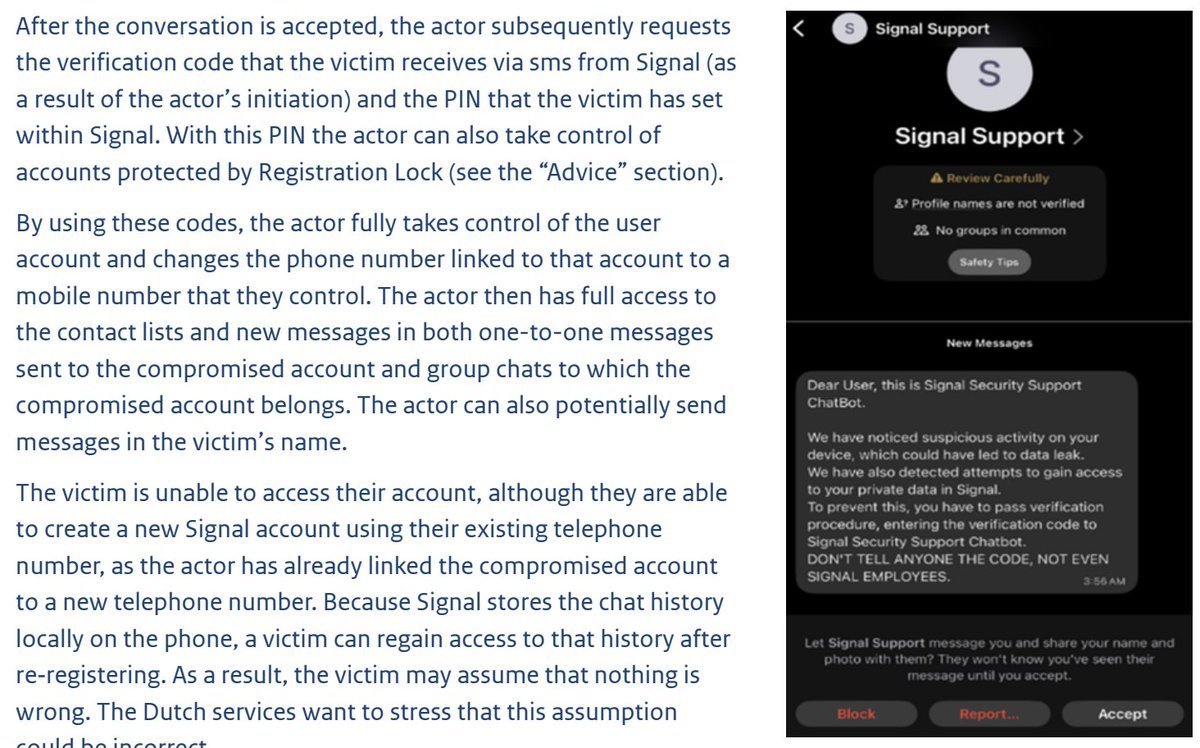
Russian GRU cyber operatives are running a large-scale, targeted operations against Signal and WhatsApp users of government officials, military personnel and civil servants. The fake support message in the advisory tells victims, in capital letters: "DON'T TELL ANYONE THE CODE, NOT EVEN SIGNAL EMPLOYEES." That literal line is in the phishing message. AND IT WORKED. Russia didn't need to break Signal. It just needed officials who trusted a a random chat message more than their own security training.
Dutch intelligence services confirmed Dutch government employees were among the victims. The campaign exploits no technical vulnerabilities in either app. Instead, it uses the apps' own features against their users.
Two methods.
1. A fake "Signal Security Support Chatbot" contacts the target, warns of suspicious activity and a possible data leak, then asks for the SMS verification code and Signal PIN. Hand those over and the attacker takes full ownership of the account, moves it to a number they control, and reads everything going forward. The victim can re-register using their old number and will see their local chat history intact - so they assume nothing happened. The advisory notes, with some understatement, that "this assumption could be incorrect."
2. A malicious QR code, dressed as a group invitation, silently links the attacker's device to the victim's account. The victim keeps full access and notices nothing. The attacker just reads along.
What makes this operationally elegant is the irreversibility. Signal has no central management by design. This is for reasons of user privacy. There is no way to remotely deactivate a stolen account. Once gone, it is gone. GRU operatives just understood this.
English

