ทวีตที่ปักหมุด
Team Atlanta
90 posts

Team Atlanta
@TeamAtlanta24
🔥AIxCC Winner Team | Georgia Tech, Samsung Research, KAIST, POSTECH | 🚀Building next-gen AI-driven bug finding & fixing systems | CRS Atlantis 🌊
เข้าร่วม Temmuz 2024
26 กำลังติดตาม744 ผู้ติดตาม
Team Atlanta รีทวีตแล้ว


A crash feels like being stranded on Mars.
No rescue. No signals. Just you… and the logs.
Meet Martian — our AI patch agent that fixes the unfixable. Exploring the unknown, one bug at a time.
🔗 team-atlanta.github.io/blog/post-crs-…
#AIxCC #AICyberChallenge #LLM #GenAI #AIForSecurity
English

Reliable patching needs more than one AI.
Our ensemble of specialized agents collaborates to generate, verify, and validate fixes—building a scalable and dependable patching system.
👉 team-atlanta.github.io/blog/post-crs-…
#AICyberChallenge #Cybersecurity #LLM #GenAI #Agent #Fuzzing
English

🤔 Can AI bring us closer to self-healing infrastructure?
🎙️ Team Atlanta’s Taesoo Kim joins Andrew Carney, program manager of AIxCC at DARPA & ARPA-H, to discuss AI, zero-days & self-healing infrastructure.
👉 infosecurity-magazine.com/podcasts/can-a…
#AIxCC #DARPA #ARPAH #CyberSecurity #AI
English

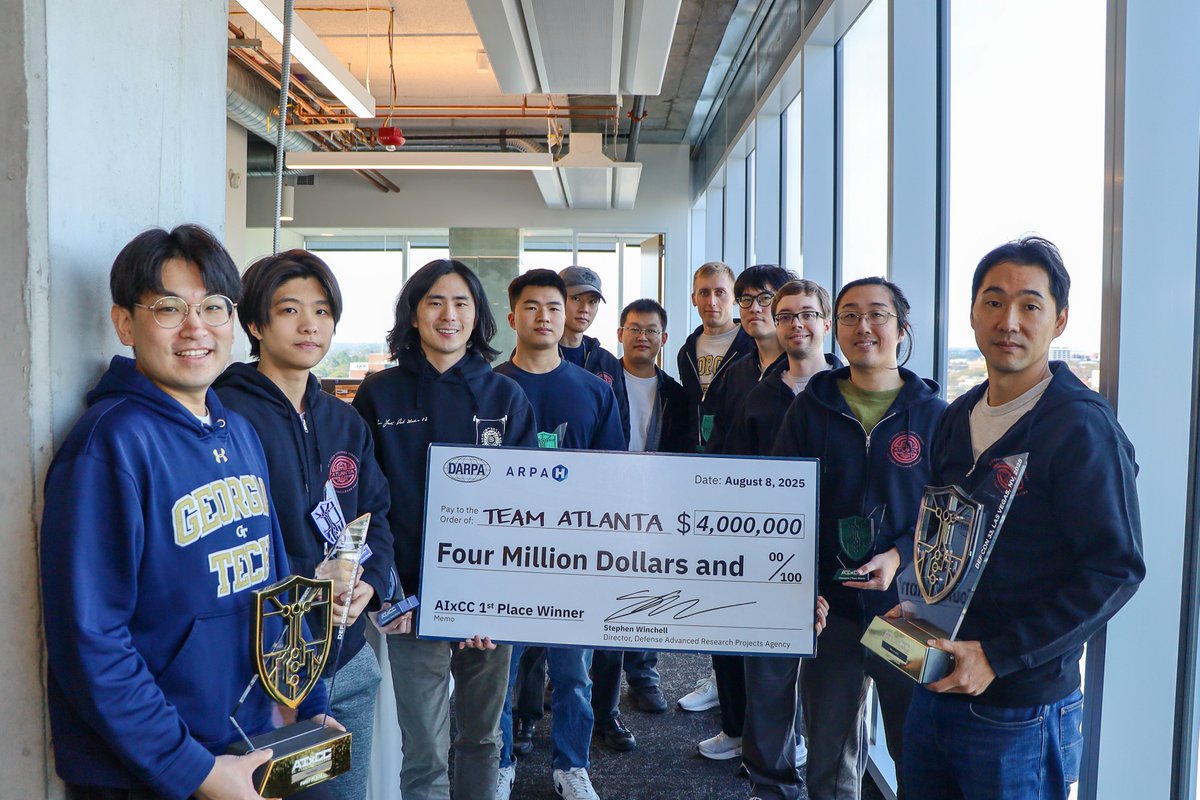
🚀 Today, we're excited to release #TeamAtlanta’s technical report on **ATLANTIS**!
Check out how ATLANTIS won 1st place at #DARPA AI Cyber Challenge (#AIxCC) at #DEFCON 33!
🌐 team-atlanta.github.io/artifacts/
#AICyberChallenge #Cybersecurity #LLM #GenAI #Agent #Fuzzing
English

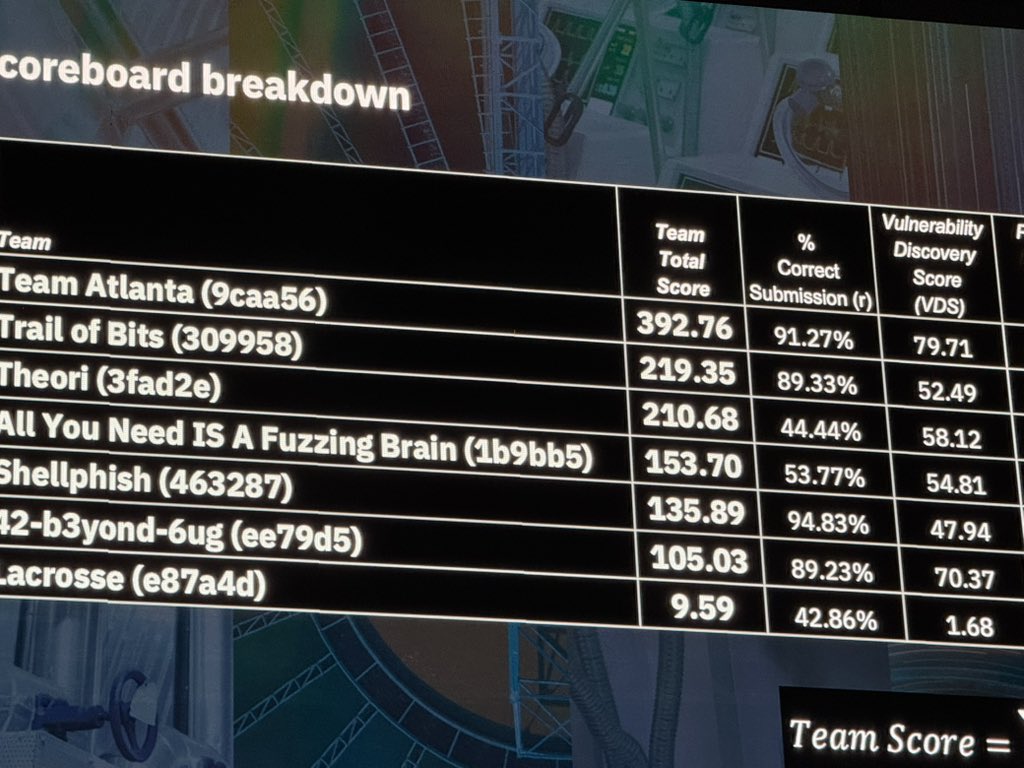
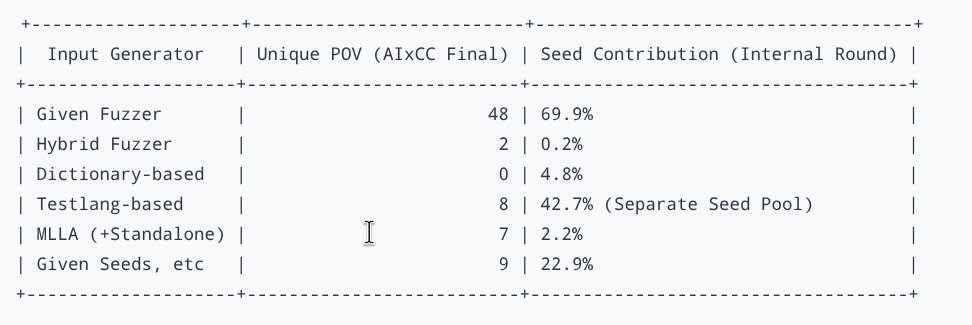
@cyan_pencil Thanks! Btw, it’s not “LLM 7 vs fuzzing 67.” Dictionary, Testlang, and MLLA are the LLM-powered modules. The key point is that LLM-integrated fuzzing goes beyond traditional fuzzing, finding PoVs in complex paths fuzzers alone couldn’t reach. More details soon in our tech report!
English

@TeamAtlanta24, congrats for your win!
Could you explain more the table at the end of team-atlanta.github.io/blog/post-crs-…?
Does this mean that the LLM-based fuzzing "only" found 7 bugs, while traditional fuzzing found 67?
English

🕵️ From noisy sinks to confirmed vulnerabilities.
BCDA traces paths, extracts key conditions, and confirms exploitable bugs — fueling our self-evolving exploit agents.
👉 team-atlanta.github.io/blog/post-mlla…
#DARPA #DEFCON #AICyberChallenge #Cybersecurity #LLM #GenAI #Agent #Fuzzing
English

🧭 Before exploits, you need code navigators.
Our agents (CPUA, CGPA, MCGA) cut through massive codebases and pinpoint potential sinks that power self-evolving exploits.
👉 team-atlanta.github.io/blog/post-mlla…
#DARPA #DEFCON #AICyberChallenge #Cybersecurity #LLM #GenAI #Agent #Fuzzing
English

🧩 Context Engineering: inside our self-evolving exploit agent
How did we boost reliability and achieve cost-effective performance in exploit generation?
👉 team-atlanta.github.io/blog/post-cont…
#DARPA #DEFCON #AICyberChallenge #Cybersecurity #LLM #GenAI #Agent #Fuzzing #ExploitDev
English

@x1aoxia0xiao Thanks for your interest!
We've already released the same version that we submitted for the AIxCC finals.
We are now working on polishing the benchmarks we used and presenting them in a more user-friendly form.
Stay tuned!
English

@TeamAtlanta24 After reading your public source code over and over again, it feels like you guys are doing a great job, do you have plans to come out with a full deployment tutorial?
English

🔥 Imagine exploits that evolve on their own.
Our Blob Generation Agents write and refine exploit scripts, delivering 7+ unique bugs at the #AIxCC Finals.
👉 team-atlanta.github.io/blog/post-mlla…
#DARPA #DEFCON #AICyberChallenge #Cybersecurity #LLM #GenAI #AutonomousAgents #Fuzzing
English

🤖 What if AI could think like a hacker?
MLLA, our most LLM-intensive module, uncovered 7+ unique PoVs at the #AIxCC Finals using self-evolving exploit generation.
👉 team-atlanta.github.io/blog/post-mlla…
#DARPA #DEFCON #AICyberChallenge #Cybersecurity #LLM #GenAI #AutonomousAgents #Fuzzing
English

🌐 Why lock fuzzing to one language?
⚡ Check our language-agnostic LLM-powered fuzzer that delivered nearly 70% of our PoVs in the #AIxCC Final.
👉 team-atlanta.github.io/blog/post-crs-…
#Cybersecurity #CTF #AI #LLM #GenAI #AICyberChallenge #DARPA #DEFCON #Security #Vulnerability #Fuzzing
English

🎯 Beyond coverage fuzzing, our Directed Jazzer fuses static analysis + runtime distance metrics to lock onto sinkpoints faster!
👉 team-atlanta.github.io/blog/post-crs-…
#AIxCC #Cybersecurity #CTF #AI #LLM #GenAI #AICyberChallenge #DARPA #DEFCON #Security #Vulnerability
English

⚡ Going beyond the baseline, we forked Jazzer with LibAFL to push Java fuzzing further under AIxCC pressure — lessons learned.
👉 team-atlanta.github.io/blog/post-crs-…
#AIxCC #Cybersecurity #CTF #AI #LLM #GenAI #AICyberChallenge #DARPA #DEFCON #Security #Vulnerability
English

🔎 How do sink-aware fuzzing + LLMs uncover Java vulns under pressure? See how Atlantis-Java did it.
👉 team-atlanta.github.io/blog/post-crs-…
#AIxCC #Cybersecurity #CTF #AI #LLM #GenAI #AICyberChallenge #DARPA #DEFCON #Security #Vulnerability
English

How did Atlantis infra help us win DARPA AIxCC? 🏆
We share how we built a scalable, reliable cyber reasoning system.
👉 team-atlanta.github.io/blog/post-atl-…
#AIxCC #Cybersecurity #CTF #AI #LLM #GenAI #AICyberChallenge #DARPA #DEFCON #Security #Vulnerability
English

New blog out now! We’re answering the top questions from the DEFCON audience and sharing the behind-the-scenes story of our victory. team-atlanta.github.io/blog/post-afc/ #AIxCC
English
Team Atlanta รีทวีตแล้ว

🚨 什麼!你忘記買 HITCON 2025 的票了嗎?!
今年 HITCON 2025 邀請到海內外頂尖講者來台,其中包括來自 喬治亞理工學院(Georgia Tech) 的博士生 Andrew Chin。他所屬的冠軍團隊 Team Atlanta 剛在上週末的 DARPA AI Cyber Challenge(AIxCC) 奪下冠軍,我們也在得知消息後的兩天內,火速邀請他來到 HITCON,並將在第一天活動分享這支團隊長達兩年的研發歷程!
【Keynote】Atlantis:一個由 LLM 驅動的自主化漏洞發現與修補系統
Andrew 將分享他們如何結合大型語言模型(LLM)與模糊測試,開發出全自動漏洞發現與修補系統 Atlantis,並在 AIxCC 決賽中擊敗眾多強敵,以 43 個漏洞發現、31 個成功修補奪下冠軍。本次演講將介紹 Team Atlanta 的 CRS,他們已將系統開源,期望幫助更多人用 AI 強化系統安全。
🔥 好消息!晚鳥票開賣囉!
收到許多朋友反應沒來得及購票,大會首度開放 「晚鳥票」,還沒入手的要快!
【晚鳥票🦉】
💰 票價:新台幣 6,000 元
⚠️ 晚鳥票不含 HITCON 2025 紀念 T-shirt,未出席活動者,Badge 將不予補寄
🔗 購票連結:hitcon.kktix.cc/events/hitcon-…
#HITCON #HITCON2025 #資安議程 #AIxCC #LLM #Fuzzing

中文

Breaking news! ❤️🔥 Our teammate Andrew Chin will present our AIxCC-winning system at Taiwan’s HITCON, Aug 15–16. hitcon.org/2025/en-US/ @HacksInTaiwan


English