💚
14.5K posts


💚 รีทวีตแล้ว
💚 รีทวีตแล้ว

let me explain the ramifications of this…
→ 150,000 people just got locked out of their own cars… across 46 states… for 6 days straight and counting
→ not a software bug. not a glitch. not AI permissions gone wrong.
→ hackers flooded Intoxalock’s servers and all these vehicles just stopped starting…
→ these are court ordered breathalyzer devices… people who messed up in the past but have been doing everything right since (hopefully)… and now they can’t drive to work because someone else’s security system failed
wild
connect the dots…
your electric car talks to a server to start. one breach and it’s a 50,000 dollar paperweight
your insulin pump syncs to a server. your pacemaker data lives on a server. one breach and it’s not a car that stops working… it’s a body
your smart home lock runs through a server. one breach and your front door either won’t open or won’t close
now zoom out…
Gartner projects $2.5 trillion going into AI this year… only $240 billion into securing the systems it runs on.
that’s a 10 to 1 bet that nothing goes wrong
the four biggest tech companies (Alphabet, Microsoft, Meta, and Amazon) are rumored to spend $700 billion on AI infrastructure this year alone…
while cybercrime is projected to cost the world $10.5 trillion
now imagine this happens to Tesla. to a hospital network. to the power grid…
every new AI integration is a new attack surface. every API is a new door. every device that “talks to the cloud” is one more thing that can be turned off by someone you’ll never meet
and I’m not saying every one of these systems will experience something
who really knows what’s secure or isn’t
but if you’re building right now…
security isn’t the last layer you add.
it’s the first one.
→ 150,000 people have just found out what happens when nobody prioritizes that…
archaic government systems and legacy businesses are likely first on the chopping block
I hope the rest of us continuously learn from it instead of living it
the weakest link in every system is the one nobody bothered to secure
like what wild system vulnerability will we see next? does someone hack Area 51?
Polymarket@Polymarket
BREAKING: Cyberattack against American breathalyzer test company locks out drivers across 45 states.
English
💚 รีทวีตแล้ว

@BrianRoemmele In the future, that many SIM cards together in one location will become obsolete. 🤠
English
💚 รีทวีตแล้ว
💚 รีทวีตแล้ว
💚 รีทวีตแล้ว
💚 รีทวีตแล้ว
💚 รีทวีตแล้ว
💚 รีทวีตแล้ว
The chronosphere (Event Horizon)
Heritage Matters🔱@HeritageMatterz
Celestial Globe with Clockwork by Gerhard Emmoser for Holy Roman Emperor Rudolf II, circa 1579.
English
💚 รีทวีตแล้ว

The Patterson-Gimlin film, a 59-second clip shot in 1967 near Bluff Creek in Northern California, has long been considered the most compelling piece of evidence for the existence of Bigfoot.
The footage, captured by Roger Patterson and Robert Gimlin, shows a large, hairy, upright-walking creature moving through a forested area, and has been analyzed for decades by scientists, anthropologists, and Hollywood costume specialists without definitive proof of a hoax.
That long-standing mystery is now being seriously challenged by a new documentary titled Capturing Bigfoot, directed by filmmaker Marq Evans.
Evans claims he was contacted in June 2024 by college professor Teresa Brooks, who asked him to develop a sealed canister of 16mm film found among her late father's belongings.
Her father was a Boeing film department head with ties to Patterson who had helped process the original 1967 footage.
After developing the film, Evans says he discovered a roughly 40-second clip showing a similar Bigfoot-like figure in the woods, with markings indicating it was filmed in 1966 — a full year before the famous encounter.
Evans believes the 1966 footage represents a rehearsal or test run deliberately staged before the 1967 filming.
Adding further weight to the claims, Patterson's own son, Clint, appears in the documentary and states that the encounter was staged, saying he had been sworn to secrecy for years.
Clint Patterson says he learned from his mother that the film was a fake and had long wanted to come forward with the truth.
He also claims he personally witnessed his father destroying the creature suit used in the footage, burning it piece by piece.
Bob Heironimus, a retired Pepsi bottler from Yakima, Washington, has separately and previously claimed he was the man inside the suit, a claim that has circulated for years.
Robert Gimlin, the only surviving participant in the 1967 filming, continues to deny all allegations of staging and insists what he and Patterson encountered was a real and unknown creature.
Meanwhile, a separate wave of Bigfoot activity is drawing attention in Ohio, where at least eight sightings have been reported since March 6, 2026, spanning communities including Mantua, Garrettsville, Streetsboro, Windham, Newton Township, and Lake Milton.
Witnesses in each case are described as locals familiar with rural Ohio wildlife, and their accounts share striking similarities — large, black-haired creatures with long arms, walking upright and producing grunting sounds.
Jeremiah Byron of the Bigfoot Society podcast has noted that the current generation of enthusiasts has never experienced a sighting flap of this scale.
Researcher Glenn Adkins and his Ohio Sasquatch Project team are actively following up on the sightings, hoping to find physical traces such as footprints.
So far, however, no photographs, video, or physical evidence has been recovered from any of the Ohio encounters, leaving the reports based entirely on eyewitness testimony.
The combination of the new documentary's explosive claims and the fresh Ohio sightings has reignited one of the most enduring and hotly debated mysteries in American folklore.
If the Patterson-Gimlin film truly was an elaborate hoax, it would mean the most scrutinized piece of Bigfoot evidence in history fooled the world for nearly 60 years — but for many believers, the debate is far from over.
#archaeohistories

English
💚 รีทวีตแล้ว
💚 รีทวีตแล้ว

The FBI, @TheJusticeDept, the Defense Criminal Investigative Service (DCIS), and international partners announced the disruption of four of the world’s largest Internet of Things (IoT) botnets that together were responsible for millions of infected devices and hundreds of thousands of DDoS attacks worldwide. justice.gov/usao-ak/pr/aut…
The operation was conducted with related law enforcement actions in Canada and Germany, which targeted the individuals who operated the botnets. @DOD_IG / DCIS is investigating the case, with assistance from @FBIAnchorage.

English
💚 รีทวีตแล้ว
How the U.S. Air Force Turned PlayStations into a Supercomputer
In the late 2000s, deep inside the Air Force Research Laboratory (AFRL) in Rome, New York, a small team of engineers stared at a familiar problem: the Department of Defense desperately needed massive computing power for real-world defense work: processing high-definition satellite imagery, enhancing radar signals, spotting patterns in intelligence data, and experimenting with early artificial intelligence.
Traditional supercomputers could do the job, but they came with a brutal price tag: tens of millions of dollars, sky-high energy bills, and months of procurement red tape. Budgets were tight. Time was shorter.
Then Mark Barnell, director of high-performance computing at AFRL, had a spark of genius that sounded almost like a joke around the water cooler: What if we used Sony PlayStation 3s?
The idea wasn’t as crazy as it sounded. The PS3, released in 2006, hid a technological marvel inside its sleek black case: the Cell Broadband Engine processor, co-designed by Sony, Toshiba, and IBM.
This wasn’t just a gaming chip; it packed seven high-speed “synergistic processing elements” (SPEs) that excelled at the exact kind of parallel, vectorized calculations needed for scientific workloads.
Even better, Sony had built in an “Other OS” feature that let users install Linux. The consoles were cheap (around $400 each on the military’s bulk-buy discount), power-efficient, and already mass-produced by the millions thanks to the gaming market. Comparable specialized hardware would have cost $10,000 per unit.
Barnell and his team started small around 2006–2008, buying a handful of PS3s, ripping out the game discs, installing Linux, and clustering them together. The results were astonishing.
Early experiments proved the consoles could handle heavy scientific computing far better than anyone outside the lab expected. They published the first glimpse of their breakthrough in a technical paper on algorithm optimizations for PS3 clusters.
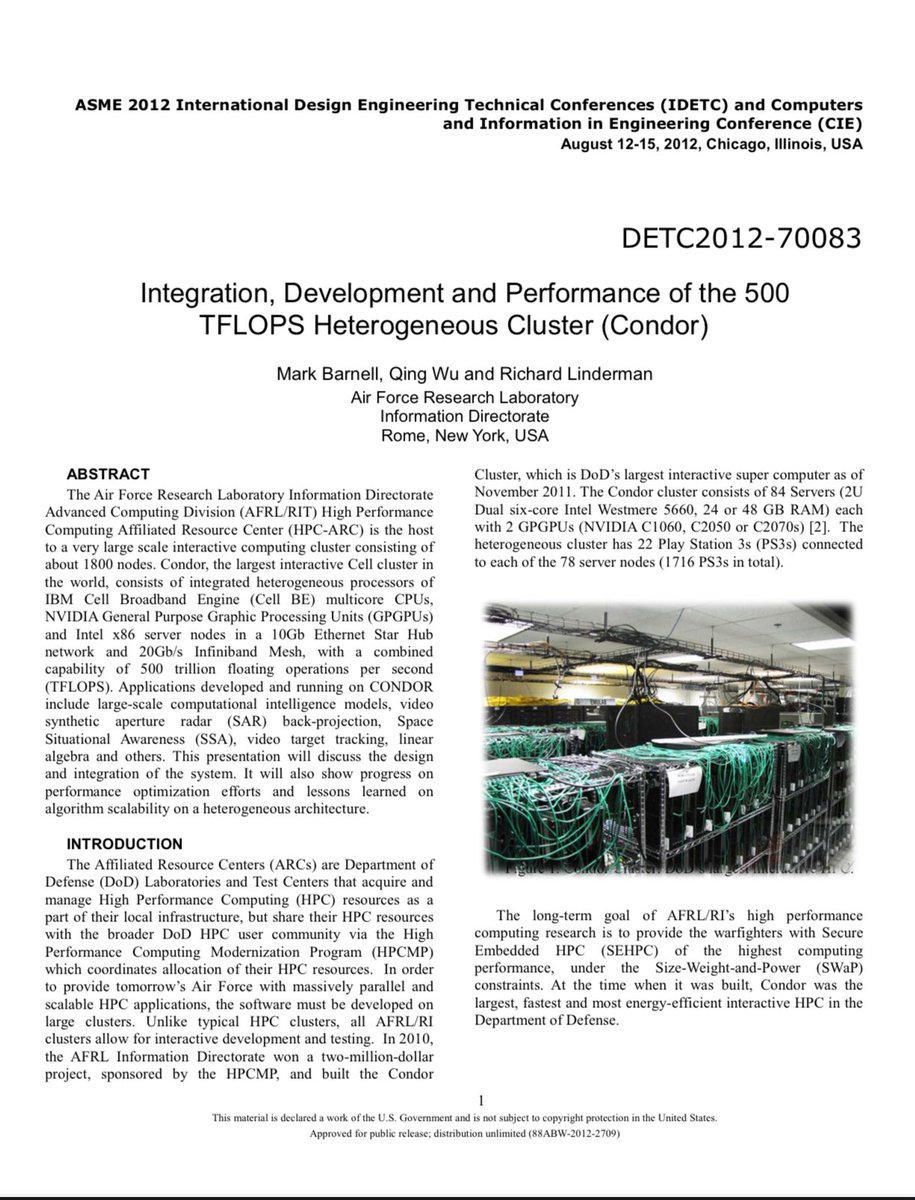
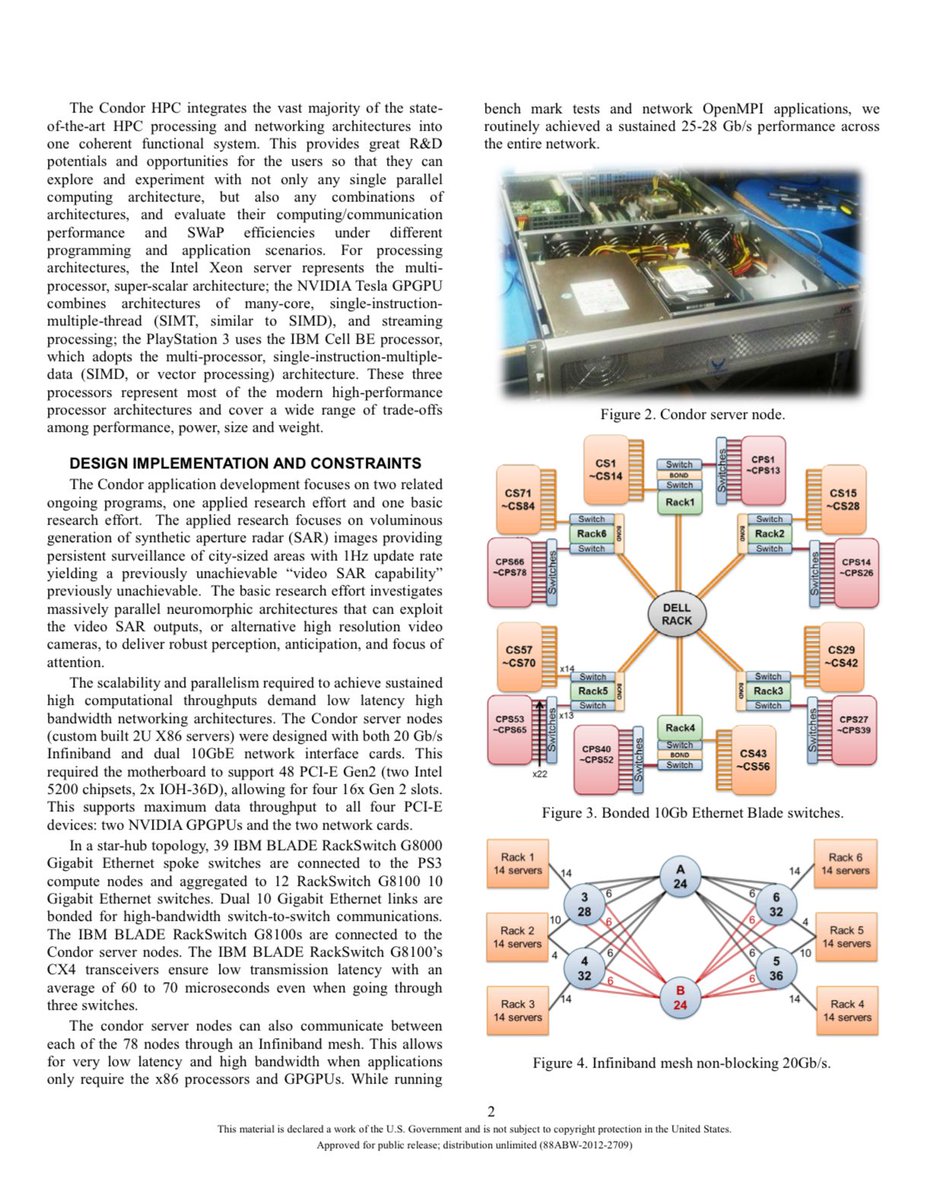
Emboldened, they scaled up. By November 2010, they had assembled the Condor Cluster: 1,760 PlayStation 3 consoles (some counts cite 1,716 as the exact core), networked with 168 GPUs and 84 coordinating servers running dual quad-core Intel Xeons.
The final machine delivered a blistering 500 teraflops (500 trillion floating-point operations per second). It ranked as the 33rd fastest supercomputer on the planet and the fastest *interactive* computer in the entire Department of Defense.
Total cost? Roughly $2 million: about one-tenth of what a traditional system would have demanded. Power consumption? A mere fraction of the energy a conventional supercomputer would gulp down.
The creativity was off the charts. This wasn’t just thriftiness; it was pure hacker ingenuity applied at the highest levels of national security. Instead of waiting for billion-dollar custom hardware, the team looked at the consumer electronics aisle and saw a supercomputer in disguise.
They turned gaming consoles: devices meant for Call of Duty marathons into a classified workhorse for analyzing spy-plane imagery, optimizing synthetic aperture radar, and exploring neuromorphic “computational intelligence.”
It was MacGyver meets Manhattan Project: resourceful, playful, and brilliantly subversive. Engineers joked that the PlayStations were “the only supercomputer you could buy at Best Buy.”
The Condor Cluster ran for years, delivering mission-critical insights until it was decommissioned around 2015.
Sony later patched out the “Other OS” feature in a firmware update, but the Air Force already had its fleet safely locked away. The project proved that sometimes the most powerful weapons aren’t built in secret labs: they’re bought off the shelf and reimagined.
English
💚 รีทวีตแล้ว
💚 รีทวีตแล้ว