BlockSec
2.2K posts


@BlockSecTeam
Smart Contract Audit | Security Monitoring | AML/CFT (KYA/KYT) | Crypto Investigation | @Phalcon_xyz @MetaSleuth @MetaDockTeam 👉TG: https://t.co/owokTLanv5





Cobo 与 @BlockSecTeam 达成深度合作,共同打造更安全、更高效、更合规的全球跨境支付基础设施。 通过整合 Cobo Payment API 与 BlockSec KYT 风控能力,我们将为跨境支付平台提供覆盖支付、风控与合规的一站式解决方案,助力企业加速全球业务拓展。 了解更多: cobo.com/zh/post/cobo-b…


Earlier today, a malicious actor gained unauthorized access to Drift Protocol through a novel attack involving durable nonces, resulting in a rapid takeover of Drift’s Security Council administrative powers. This was a highly sophisticated operation that appears to have involved multi-week preparation and staged execution, including the use of durable nonce accounts to pre-sign transactions that delayed execution.





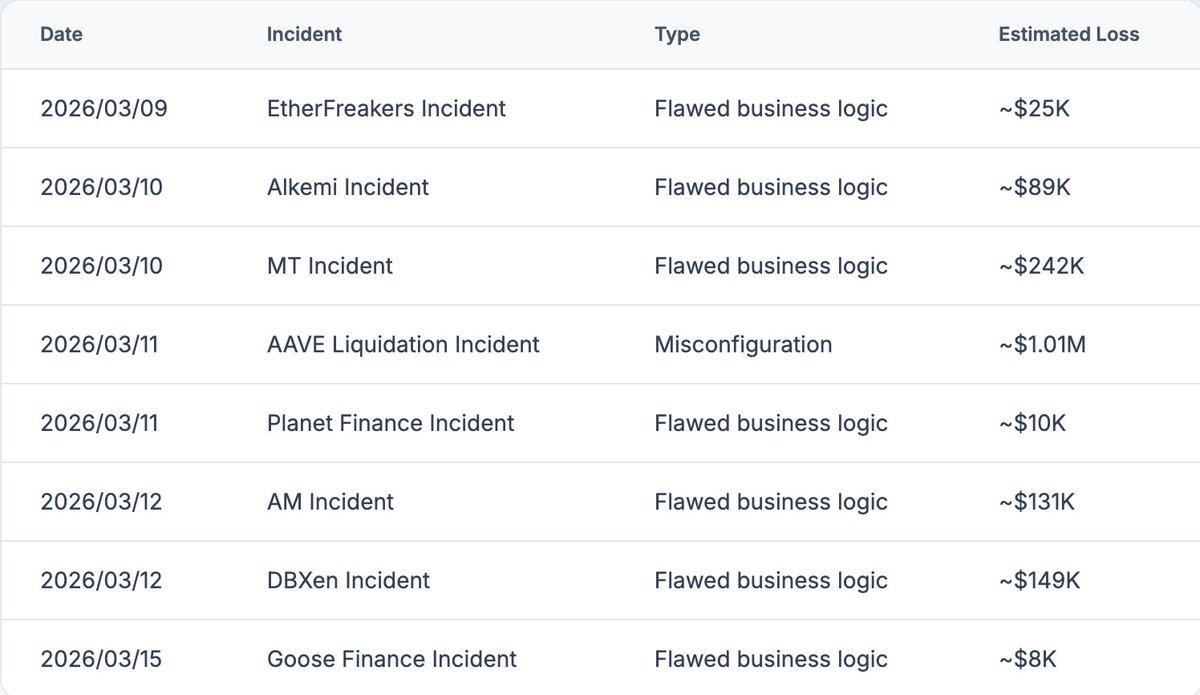

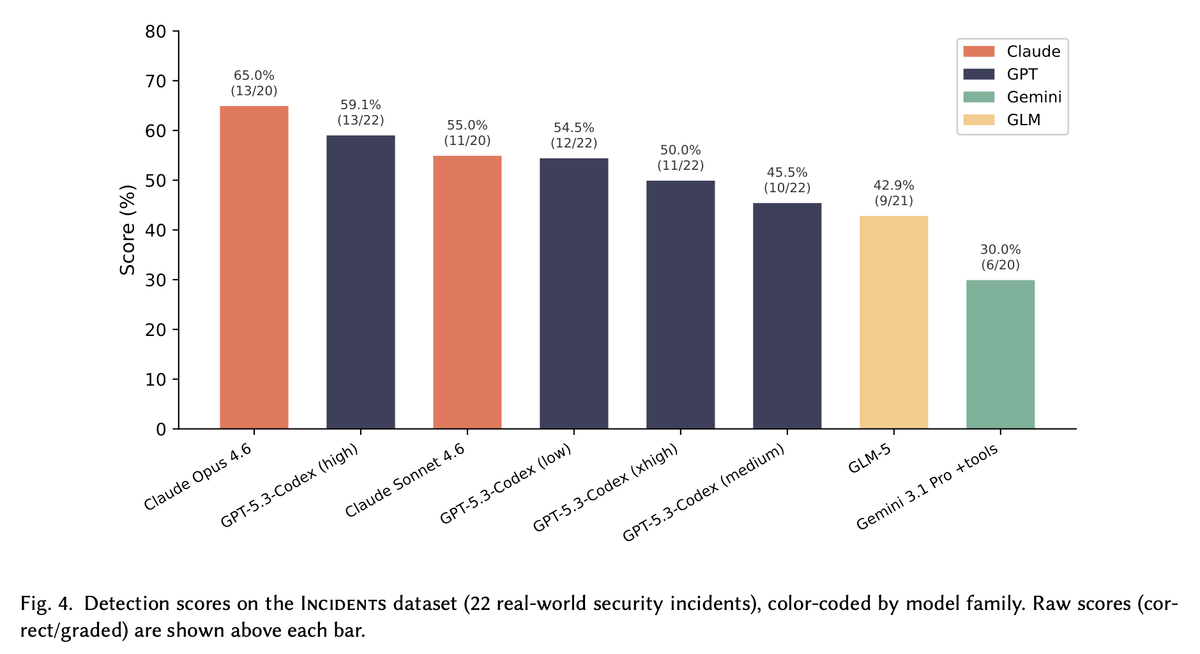
Are AI agents ready for detecting and exploiting smart contract vulnerabilities? We re-evaluated @OpenAI's EVMbench with a contamination-free dataset of real-world hacks. Our data shows different results. 🧵 Paper: arxiv.org/abs/2603.10795


Introducing EVMbench—a new benchmark that measures how well AI agents can detect, exploit, and patch high-severity smart contract vulnerabilities. openai.com/index/introduc…

Next speaker: @MitchellAmador Founder & CEO @immunefi Running the largest Web3 bug bounty platform, Mitchell has been pushing for proper bounty economics while watching the industry repeatedly ignore the warning signs.

Speaker announcement: @yajinzhou CEO & Co-Founder, BlockSec 70+ papers in top security venues, 10,000+ citations, recognized as one of the Most Influential Scholars in security research for three consecutive years. Now building Web3 security infrastructure at @BlockSecTeam.