BlockSec
2.2K posts


BlockSec
@BlockSecTeam
Smart Contract Audit | Security Monitoring | AML/CFT (KYA/KYT) | Crypto Investigation | @Phalcon_xyz @MetaSleuth @MetaDockTeam 👉TG: https://t.co/owokTLanv5

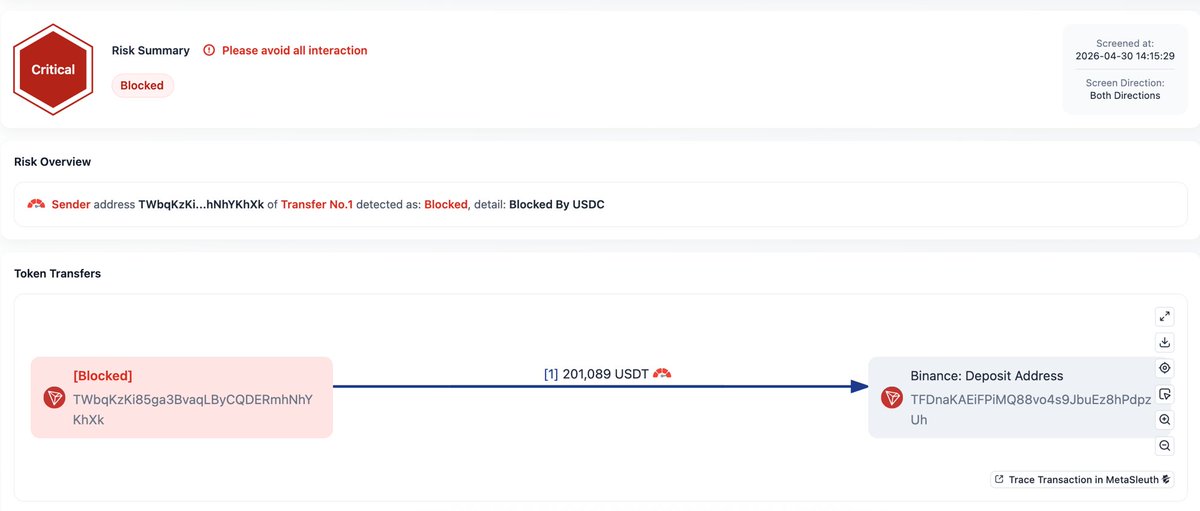
1/3 USDT has been quietly unfreezing addresses that @circle's USDC still has frozen. In multiple cases, funds moved directly to @Binance within hours of removal.


Attention Aftermath community - We’ve identified an exploit affecting the protocol. Our team is actively investigating alongside leading security partners. As a precaution, the protocol has been paused and measures are being taken to minimize potential impact to user funds. We’ll continue to share updates as we learn more. Thank you for your patience.








The Arbitrum Security Council has taken emergency action to freeze the 30,766 ETH being held in the address on Arbitrum One that is connected to the KelpDAO exploit. The Security Council acted with input from law enforcement as to the exploiter’s identity, and, at all times, weighed its commitment to the security and integrity of the Arbitrum community without impacting any Arbitrum users or applications. After significant technical diligence and deliberation, the Security Council identified and executed a technical approach to move funds to safety without affecting any other chain state or Arbitrum users. As of April 20 11:26pm ET the funds have been successfully transferred to an intermediary frozen wallet. They are no longer accessible to the address that originally held the funds, and can only be moved by further action by Arbitrum governance, which will be coordinated with relevant parties.



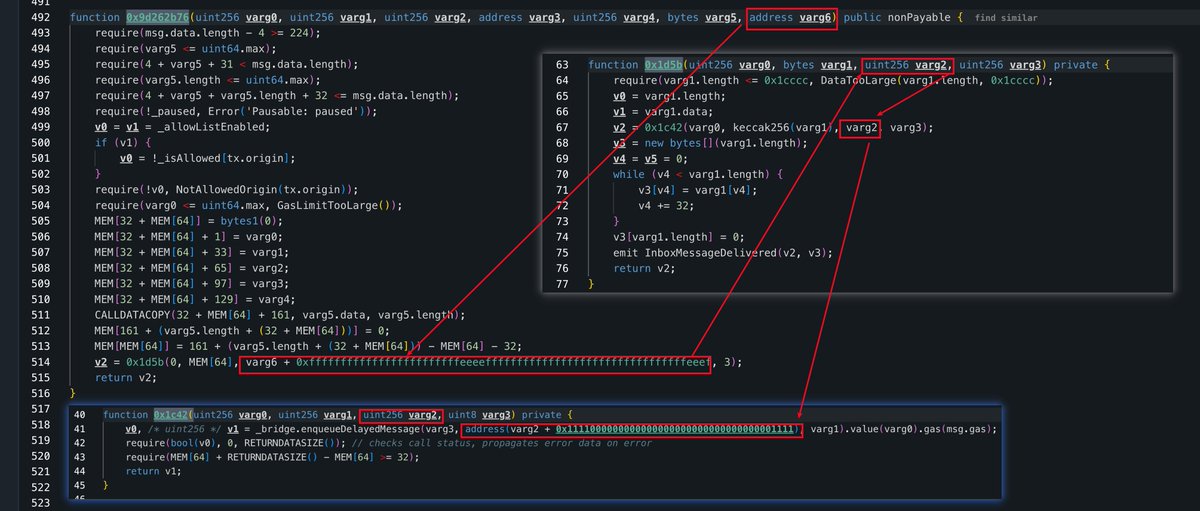
.@KelpDAO was reported attacked hours ago, with total losses estimated around $290M. Based on community on-chain analysis (e.g., @banteg), the likely root cause is a compromise of the configured DVN/verifier on the Unichain→Ethereum rsETH bridge route: the route relied on a 1-of-1 check, which may have let a forged/unbacked bridge message pass verification and trigger a drain from the protocol's rsETH Adapter. The exploiter then deposited rsETH into Aave/Compound/Euler and borrowed roughly $236M in assets (WETH, wstETH, WBTC), which is the attacker’s tracked profit so far. @aave has frozen rsETH markets (V3/V4). The incident is still under investigation. The main risk now is contagion: thin rsETH liquidity could turn collateral exposure into bad debt.





2/ The Ethereum Security Subsidy Program is proud to be launching with access to 20+ of the leading audit providers active in the Ethereum ecosystem: @AdevarLabs, @bailsecurity, @BlockSecTeam, @Certora, @chain_security, @cyfrin, @dedaub, @GuardianAudits, @hackenclub, @HackenProof, @Hashlock_, @hexens, @immunefi, @LeastAuthority, @lethalspoons, @NethermindSec, @Quantstamp, @QuillAudits_AI, @rv_inc, @SecurityOak, @sherlockdefi, @spearbit, @statemindio, @zellic_io, and @zokyo_io. These top-tier security providers make the program possible through their commitment to support Ethereum mainnet.


ALERT! Our system detected suspicious transactions targeting tokens managed by @hyperbridge’s HandlerV1 contract on #Ethereum, with estimated losses of ~$242K. The likely root cause is a Merkle Mountain Range (MMR) proof replay vulnerability caused by missing proof-to-request binding. This flaw allows an attacker to replay a previously accepted proof and pair it with a newly crafted request, enabling privileged actions (such as changing admin permissions) for profit. Specifically, in HandlerV1, replay protection only verifies that a request commitment (request.hash()) has not been used before. However, the proof verification process does not bind the submitted request payload to the validated proof. Because of this disconnect, a valid historical proof can be reused with a different malicious request. For example, in the transaction with the largest loss observed so far, the attacker changed the admin of the #Polkadot (#DOT) Token, then used admin privileges to mint #DOT and profit by swapping the newly minted tokens. app.blocksec.com/phalcon/explor… Other Attack TXs: • app.blocksec.com/phalcon/explor… • app.blocksec.com/phalcon/explor… • app.blocksec.com/phalcon/explor… • app.blocksec.com/phalcon/explor… • app.blocksec.com/phalcon/explor… • app.blocksec.com/phalcon/explor… • app.blocksec.com/phalcon/explor… 🟦 Found by #PhalconSecurity, 🟦 Analyzed via #PhalconExplorer.


1/7 $1.6B in TRON USDT. A Ponzi disguised as a "Hong Kong health tech group," borrowing the names of Alphabet's Verily Life Sciences and a Chinese A-share listed company. We mapped VerilyHK's full on-chain topology, one of the largest TRON-based fund schemes ever documented. 🧵👇



We’re excited to announce a strategic partnership between @InterlaceMoney and @BlockSecTeam, a leader in blockchain security. Together, we’re advancing the future of stablecoin payments by collaborating on security across the entire transaction lifecycle. By combining Interlace’s payment infrastructure with BlockSec’s cutting-edge security solutions, we aim to enhance real-time monitoring, risk evaluation, and on-chain safety,especially on agentic payment field. This partnership reinforces our shared commitment to building a more secure, trustworthy foundation for institutions and individuals in the next digital financial system driven by AI. #AI #AIAgent #Web3 #interlace #digitalpayments #agenticpayments #aipayments