br.carbs
2.4K posts

br.carbs
@breadpir8
I rt/like cybery things, always striving to be better, thx for the help







Hello for Business works great with AD integrated apps (Kerberos/NTLM), but it requires setting up a trust model Very poorly generalized, Hello uses certificates that AD doesn't understand, so we need a way to request a Kerberos ticket with the certs This is crazy easy now 🧵

My goto recommendations for protecting against weak passwords: - lithnet ad password protection - specops password policy Of course there is also Entra Password Protection. Regardless, following some foundational rules does make a difference. Strong password policies. Enforce strong MFA, without exception. And if you’re feeling extra boss… look into the passwordless option.



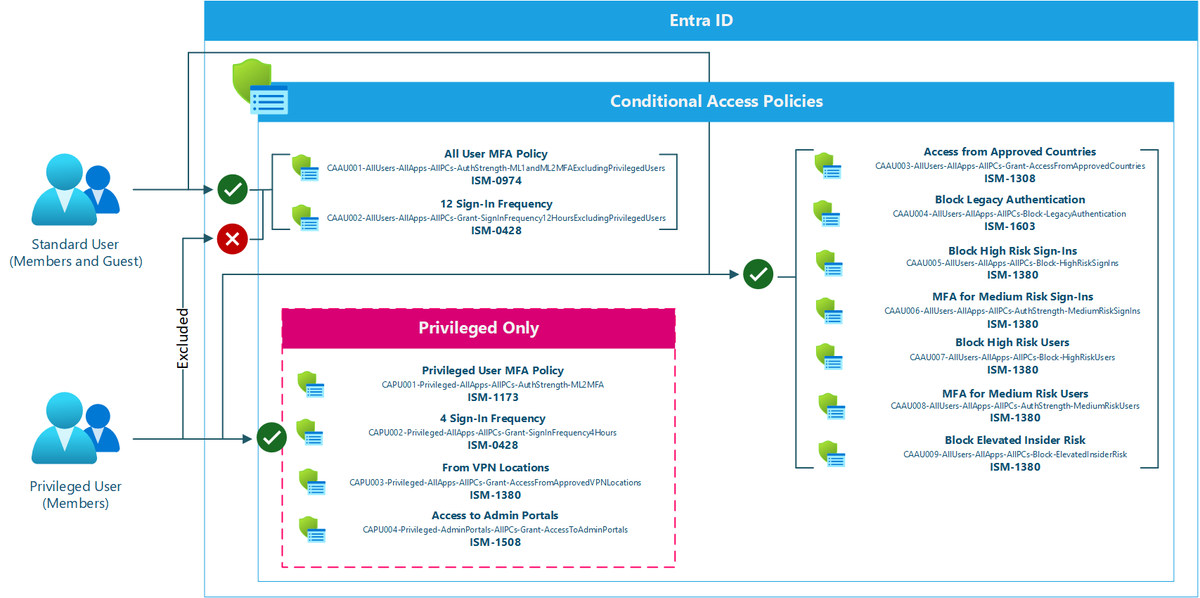





On 9/15, Microsoft starts enforcing mandatory MFA for Azure CLI, Azure PowerShell, Azure mobile app, and your IAC tools (non-Service Principal based) I created a CA template you can import (report-only) to audit these apps (add your IAC ones): github.com/nathanmcnulty/…

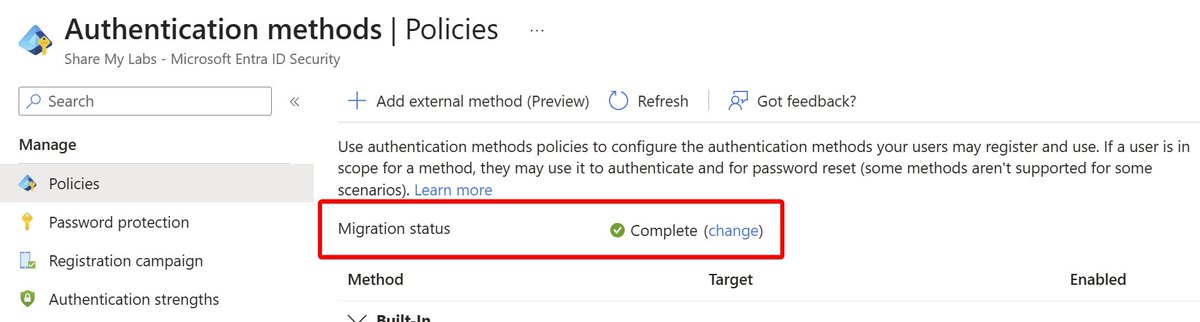
For anyone that hasn't migrated their authentication methods in Entra yet, I recorded a guide with some common gotchas I'm really just trying to learn OBS and my gear, sorry for the potato quality, it's probably not Twitter's fault :p Working on getting better at this format ;)




This went well other than Microsoft Authenticator app is trash