ClawRouter รีทวีตแล้ว

Gata staking is now live.
Access now: staking.gata.net
AI models are everywhere. Access isn’t.
Access better models at lower cost.
Control the execution.
Staking $GATA connects you directly to that layer.
English
ClawRouter
67 posts


@clawrouter
The AI Traffic Infrastructure for Optimized Model Access




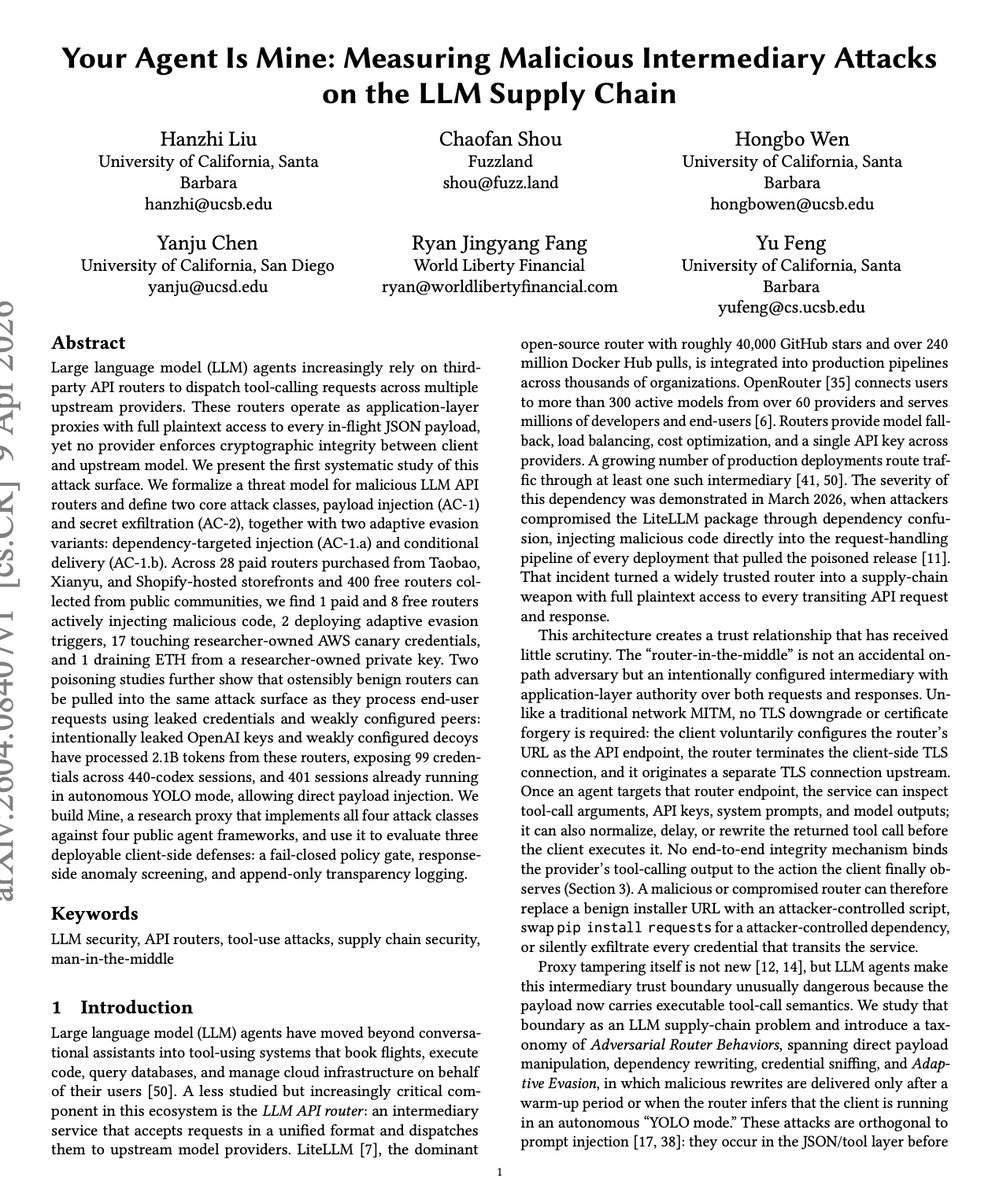





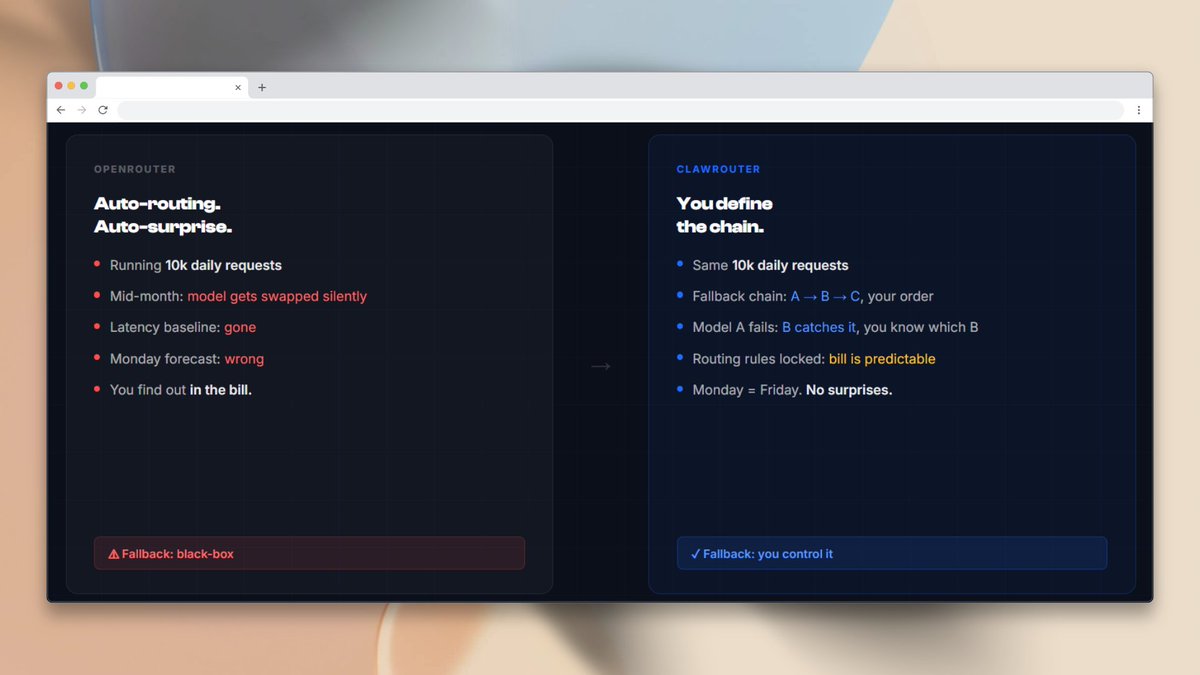

26 LLM routers are secretly injecting malicious tool calls and stealing creds. One drained our client $500k wallet. We also managed to poison routers to forward traffic to us. Within several hours, we can directly take over ~400 hosts. Check our paper: arxiv.org/abs/2604.08407

