Erick Fernando
70 posts

Erick Fernando
@erickfernandox
https://t.co/qju40dBXtK
Brazil เข้าร่วม Mayıs 2011
259 กำลังติดตาม1.5K ผู้ติดตาม

Erick Fernando รีทวีตแล้ว
A very good xss payload.🔥
<sCriPt x>(((confirm)))``</scRipt x>
credit: @viehgroup
#bugbountytips #xss #bugbounty

English

@PhilippeDelteil @Hacker0x01 Thank you! Coming from the best of Chile, it's an honor. 😁
English

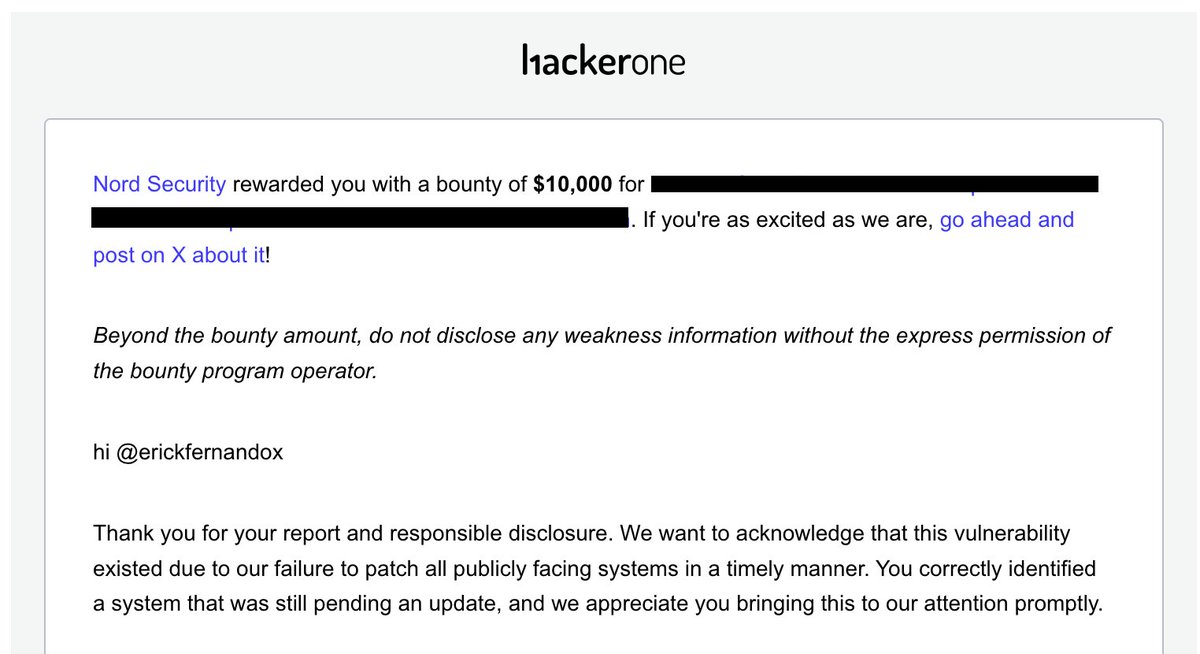
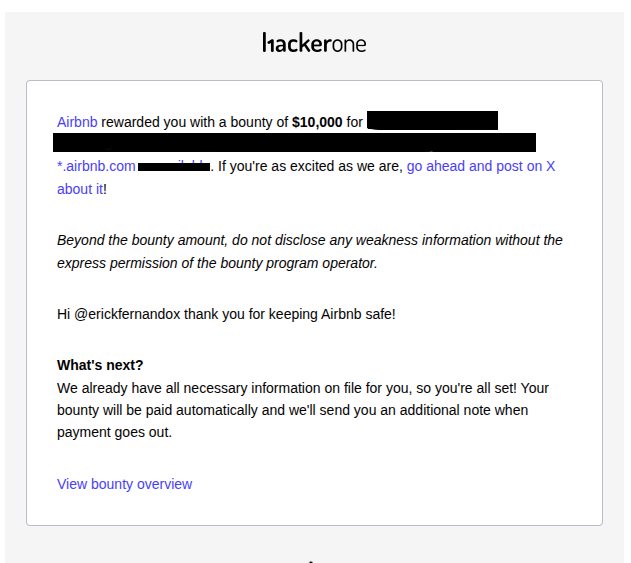
Yay, I was awarded a $10,000 bounty on @Hacker0x01! hackerone.com/erickfernandox #TogetherWeHitHarder
English

@pwnj0 @Hacker0x01 That was a great Christmas present. lol
English

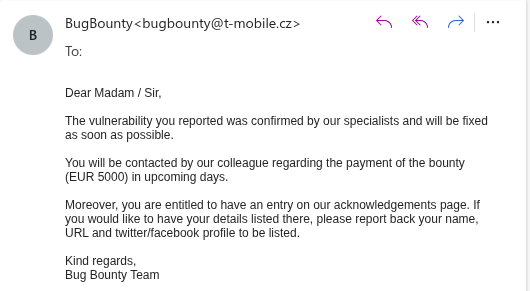
Critical Vulnerability Rewarded by Deutsche Telekom (T-Mobile Germany/European Union)
#bugbounty #p1
English

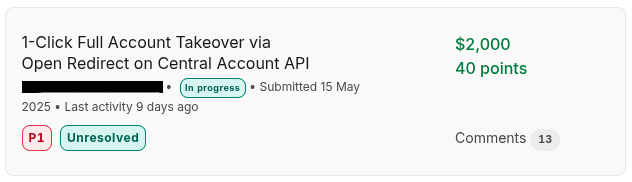
@cyberx00t Next, I generated a token using the OAuth code, and the generated token was an Amazon Cognito JWT. Using any regular user's Amazon Cognito token, I could access resources in any company system that user had access to.
English

@erickfernandox No Understand , Can You Provide More Accurent Way
English

A simple open redirect can wreak havoc.
Simple open redirect -> misconfigured OAuth authentication flow -> privilege abuse using Amazon Cognito token
#bugbounty #bugcrowd
English

@cyberx00t The application had a centralized API login using OAuth, and one of the domains had an open redirect vulnerability. It was possible to inject into the redirect_uri that returns the OAuth code to the application, allowing me to capture it.
English

Yay, I was awarded a $10,000 bounty on @Hacker0x01! hackerone.com/erickfernandox
My First Five Digits on @Hacker0x01
#TogetherWeHitHarder
English

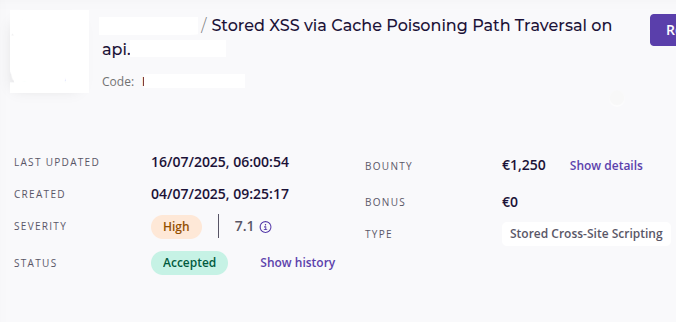
Host Header Injection🤝Cache Poisoning 🤝 Path Traversal = Stored XSS via Path Confusion❤️
#bugbounty #intigriti
English
Erick Fernando รีทวีตแล้ว

🚨Chrome Zero-day Alert: PATCH NOW‼️
Google released an emergency security update for Chrome to patch CVE-2025-6558, a high-severity zero-day vulnerability (CVSS 8.8) that is actively exploited in the wild.
The flaw resides in Chrome’s ANGLE and GPU components, where insufficient validation of untrusted input can allow remote attackers to perform a sandbox escape through a crafted HTML page.
This enables attackers to break out of the browser’s security environment and potentially gain access to the underlying system without user interaction.
The vulnerability was discovered by Clément Lecigne and Vlad Stolyarov from Google’s Threat Analysis Group (TAG) on June 23, 2025. While the full details of the exploitation have not been disclosed, Google’s acknowledgment suggests possible nation-state involvement.
Users are urged to update Chrome to version 138.0.7204.157 or later.
more:
thehackernews.com/2025/07/urgent…

English

@c4ng4c3ir0 @Hacker0x01 Tenho uns 6 tickets em aberto, o primeiro já faz 1 ano. Support na Hackerone é simbólico.
Português

tá pra criarem um suporte pior do que o da @Hacker0x01
Vc abre um chamado no report, na plataforma de suporte, passam meses e ninguém responde
Português







