ทวีตที่ปักหมุด

🚨 Interested in Windows kernel exploitation?
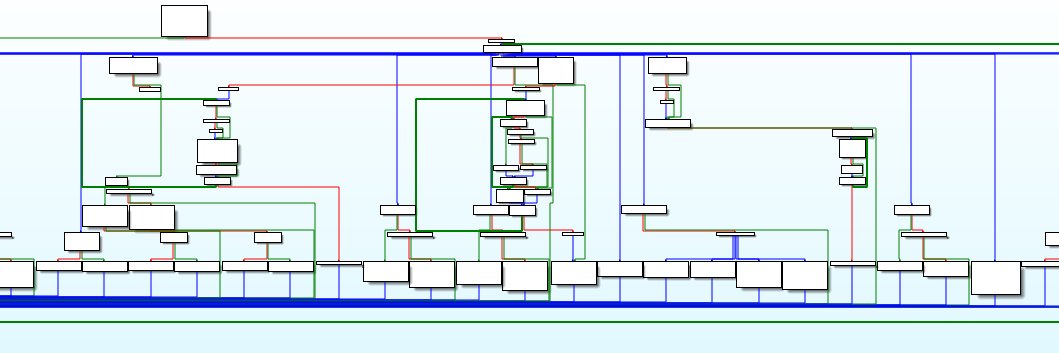
Our @sstic 2025 talk on the Shadow Stack implementation in the Windows kernel is now online!
📄 Paper: sstic.org/media/SSTIC202…
📑 Slides: sstic.org/media/SSTIC202…
Synacktiv@Synacktiv
It's already #SSTIC2025 day 2! @netsecurity1 and us3r present the Windows kernel shadow stack mitigation 🪟
English