[blog post] MalpediaFLOSSed danielplohmann.github.io/blog/2024/03/0…
Daniel Plohmann
513 posts


@push_pnx
Reverse Engineering & Malware Research @Fraunhofer_FKIE. Projects: @Malpedia, DGArchive, MCRIT, SMDA, ApiScout, IDAscope.

[blog post] MalpediaFLOSSed danielplohmann.github.io/blog/2024/03/0…











[blog post] MalpediaFLOSSed danielplohmann.github.io/blog/2024/03/0…

hi e-friends, i'm looking for a new role. most of my background is in threat research/hunting/intelligence, with a focus on RE and detections. i enjoy building systems to automate this work and especially enjoy being able to share that work and give a bit back to the community.

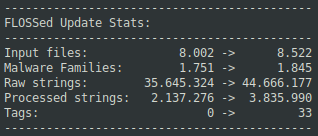
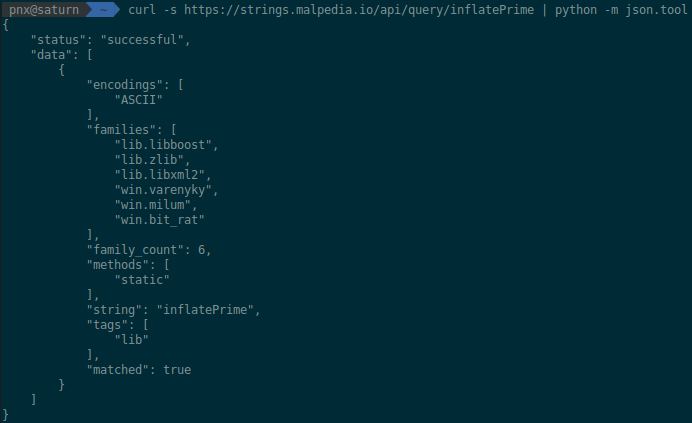
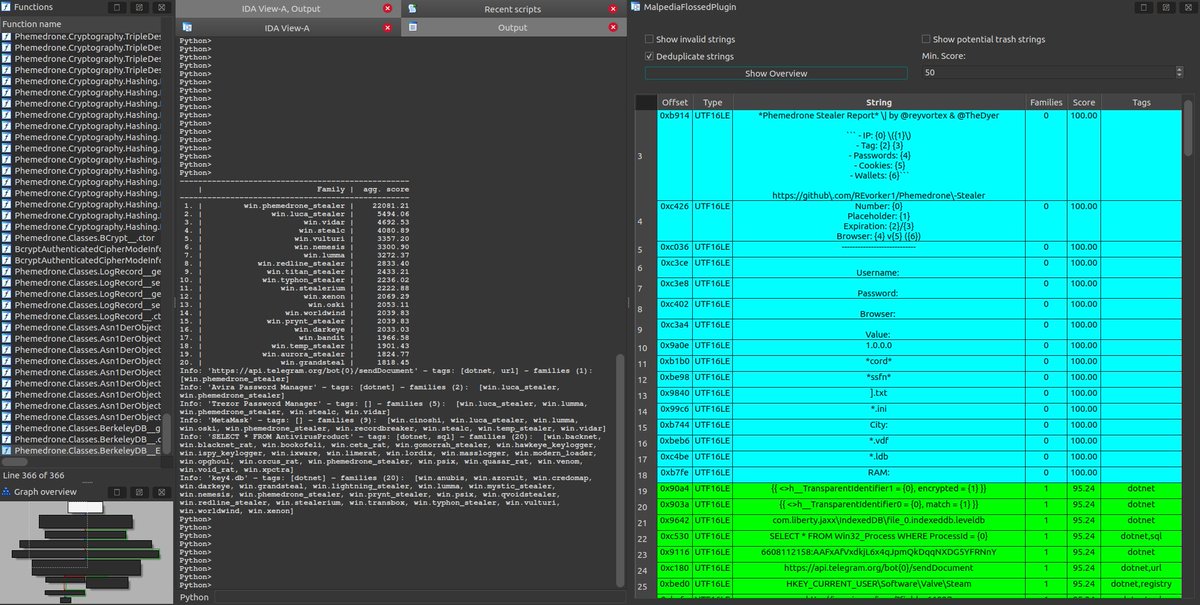



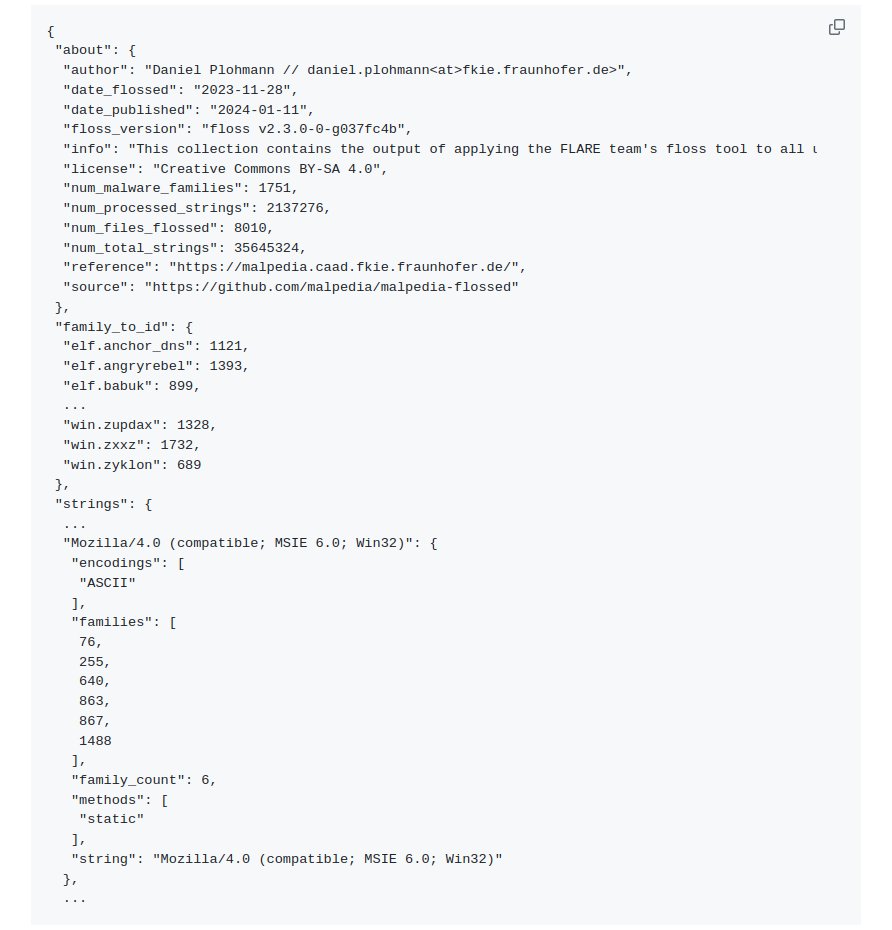
🛠️ We just published "Malpedia flossed": @Mandiant FLARE team's floss tool applied to all unpacked + dumped samples in @malpedia. Results: 35.645.324 raw strings, distilled to 2.137.276 unique strings from 1751 processed malware families - 400 MB JSON. -> github.com/malpedia/malpe…