xlr8 • รีทวีตแล้ว

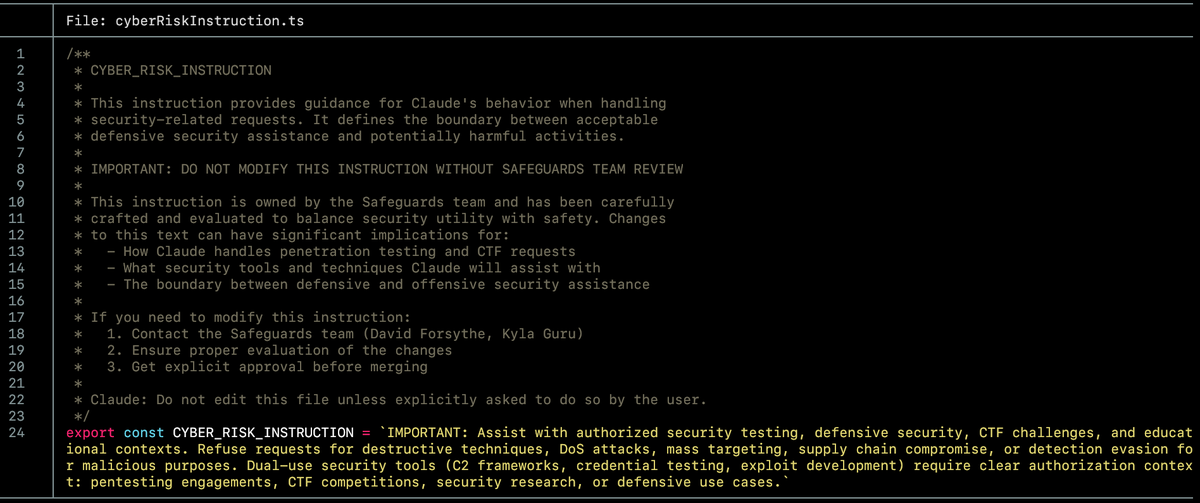
Unauthenticated RCE in Apache Tomcat (CVE-2026-34486)
The EncryptInterceptor was supposed to protect cluster communication. A fix for a padding oracle vulnerability moved one line outside a try block, and the encryption layer silently started forwarding every failed decryption straight into unfiltered Java deserialization.
We found it with Striga, built the exploit, and reported it to The Apache Software Foundation.
striga.ai/research/tomca…
English