candymate รีทวีตแล้ว

👀
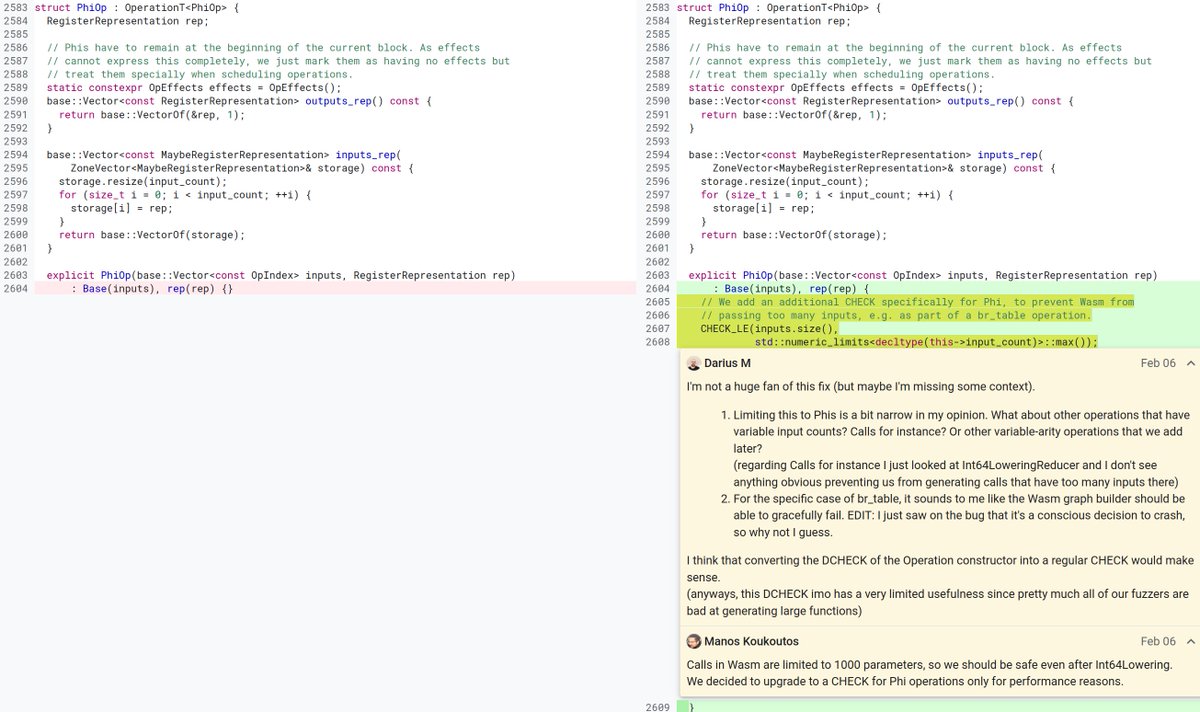
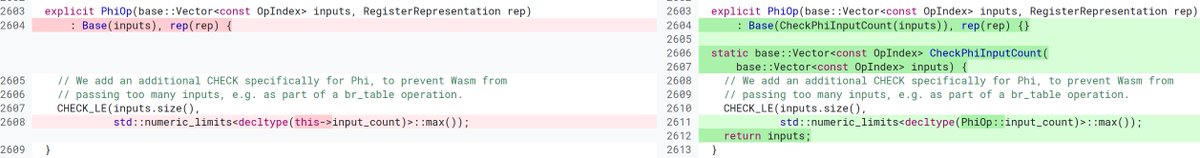
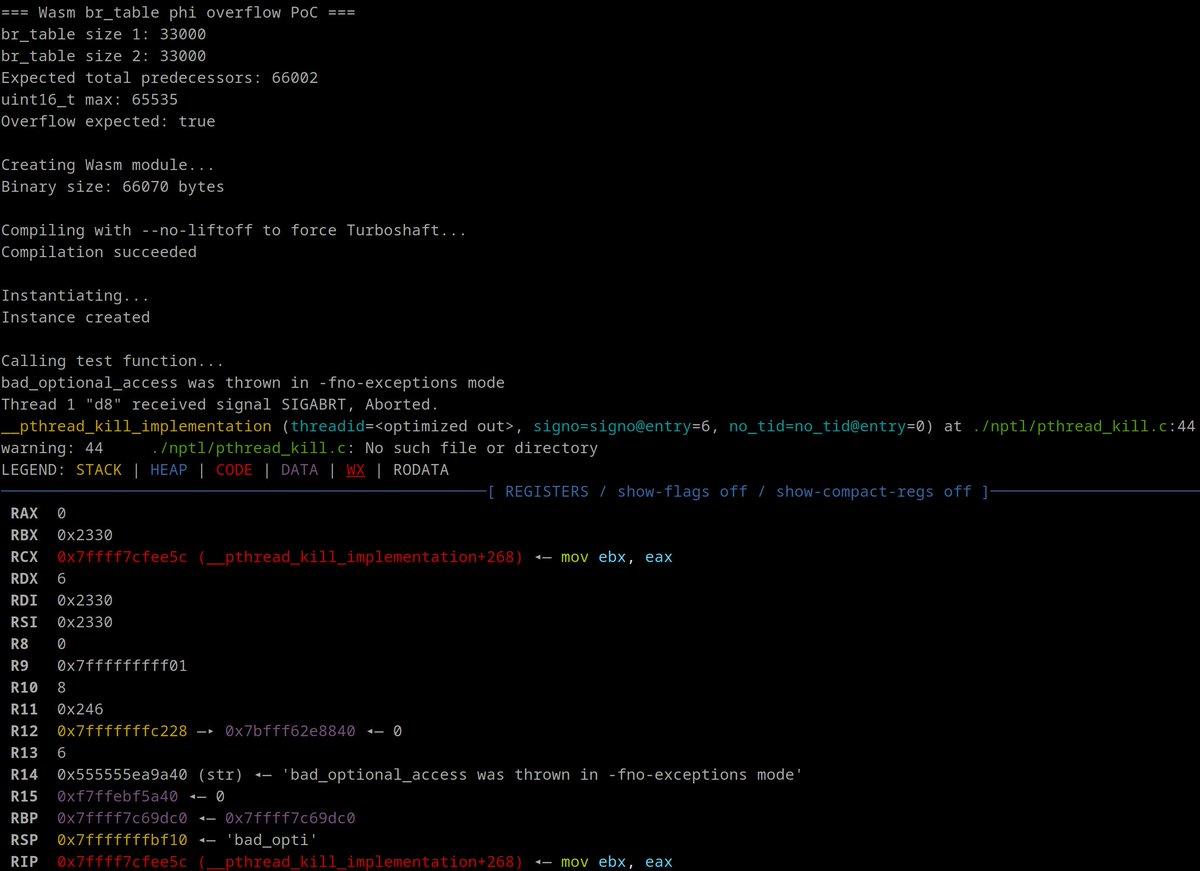
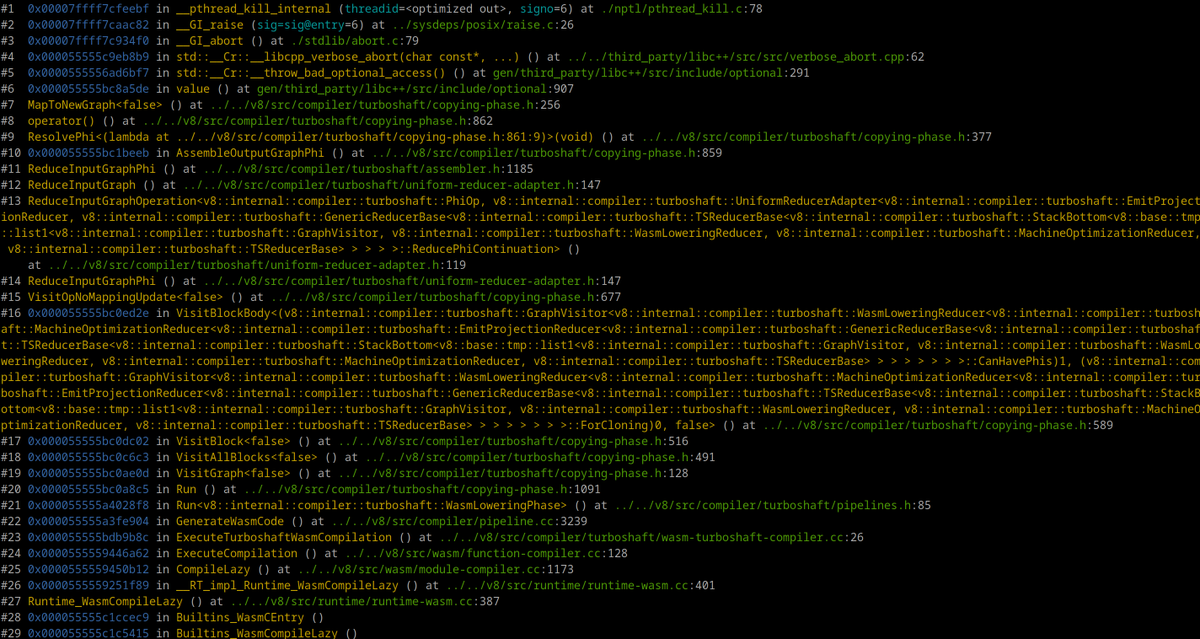
(CVE-2026-2649)[481074858][wasm][turboshaft]Wasm br_table operation Phi integer overflow(passing too many inputs).
chromium.googlesource.com/v8/v8/+/04d57e…
chromium.googlesource.com/v8/v8/+/25613a…
chromereleases.googleblog.com/2026/02/stable…
PoC:
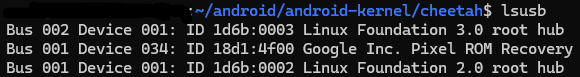
./d8 --no-liftoff
chromium.googlesource.com/v8/v8/+/25613a…
Reported by JunYoung Park(@siwu_network)
English