ทวีตที่ปักหมุด
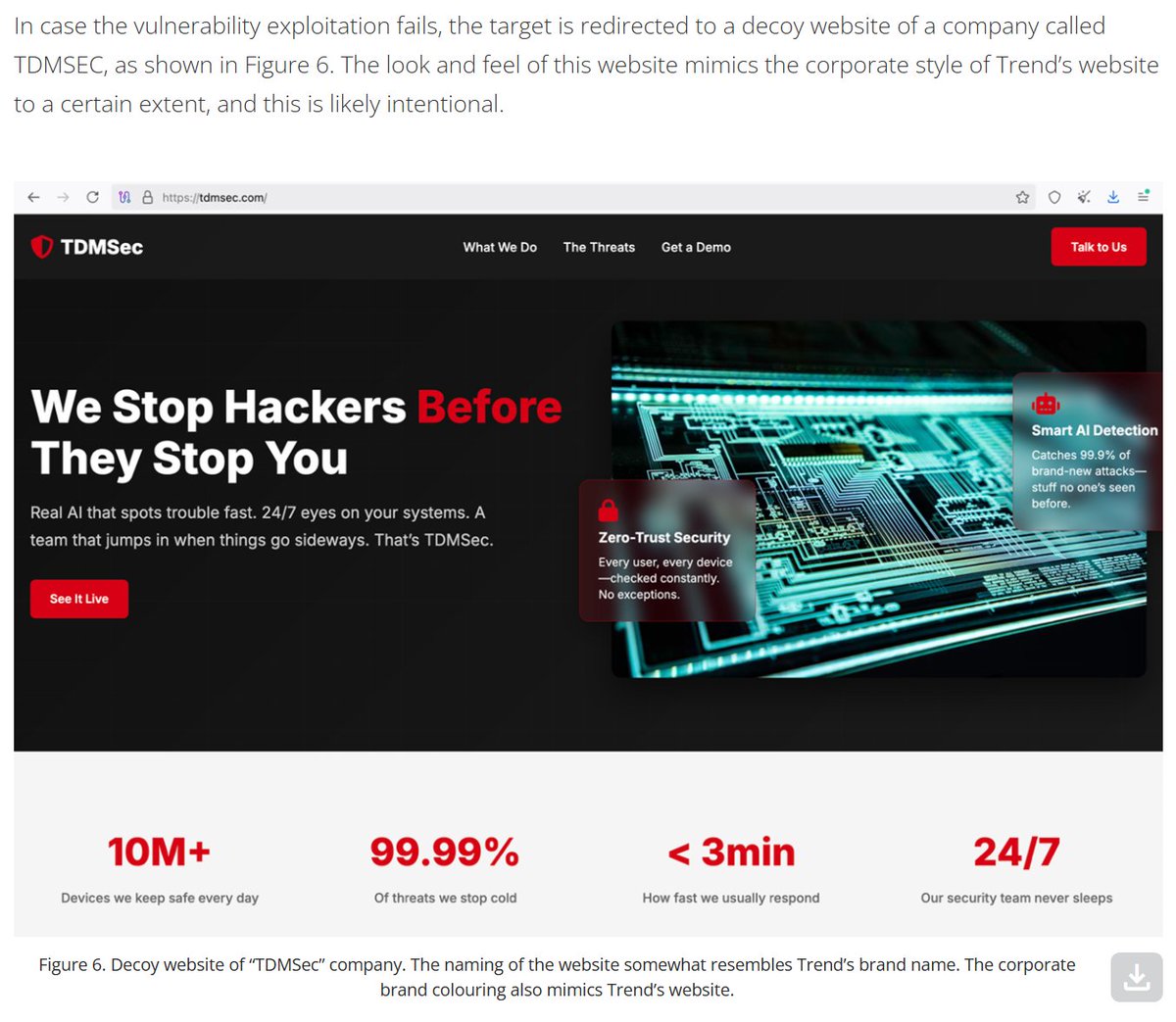
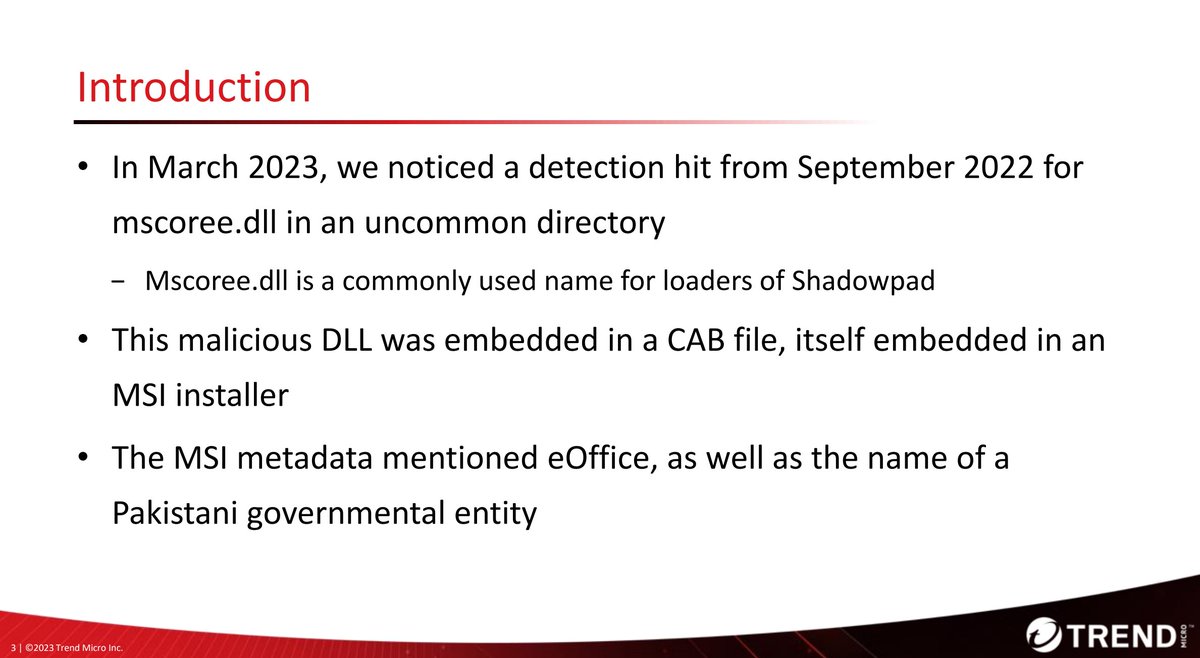
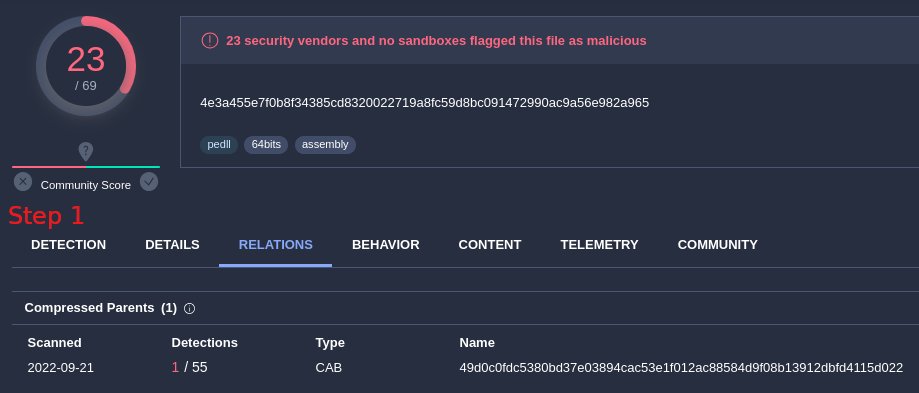
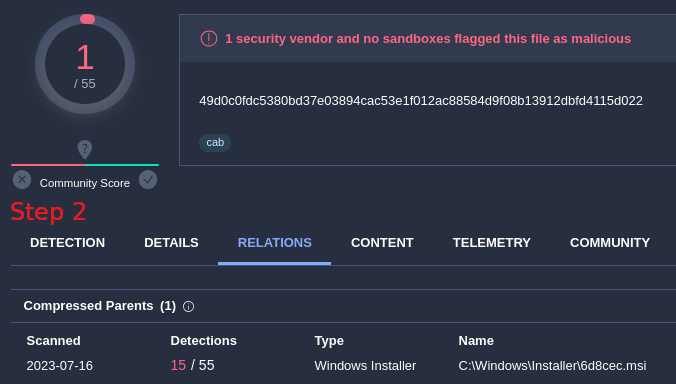
We saw Earth Estries, an advanced #APT group, sharing its access to Earth Naga (Flax Typhoon). We introduce the term "Premier Pass" to describe this behavior, and propose a four-tier classification framework for collaboration types among advanced groups trendmicro.com/en_us/research…




English