Transhackerism
4K posts


Transhackerism
@transhackerism
CyberSec, Futurist, Techno Artist, Metaverse, AI, Privacy, w00x2, Public Speaker, Change Agent, Synth Nut, Freedom Lover, Protector, Connector, Hacker
In a predicted future เข้าร่วม Ağustos 2007
1.2K กำลังติดตาม662 ผู้ติดตาม

@brandank_cr Bitcoin has been kicking the crap out of gold for 15 years and still is; there's always a rotation from one over heated commodity to one that's massively under-valued, and back and forth it will go. Neither narrative for gold or bitcoin has changed, whether politics align or not
English
Transhackerism รีทวีตแล้ว

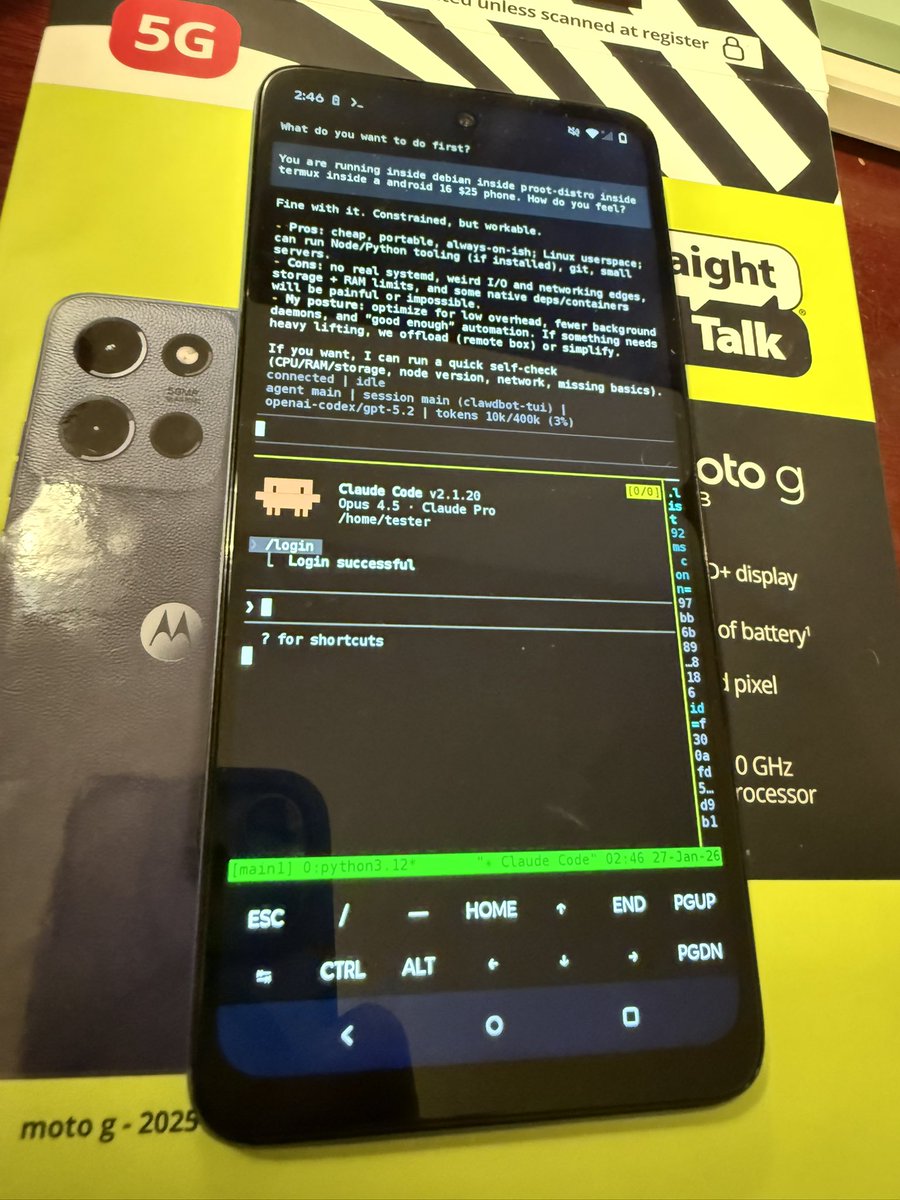
Necessity is the mother of all things.
Kostas@Kostastsale
First Sophos and now PaloAlto?!? I think we have entered a new era. It’s the “Hack Back” era.
English

Check out our Blog: lnkd.in/gMQ-XHS4
Register for our Free Workshop: lnkd.in/gwNdHczN
English
Transhackerism รีทวีตแล้ว

🔴 CVE-2024-47575: FortiManager fgfmd daemon may allow a remote unauthenticated attacker to execute arbitrary code or commands via specially crafted requests (critical) / aka #FortiJump.
Vulnerability used in zero-day attacks 🔥
Reported malicious IPs:
- 45.32.41.202
- 104.238.141.143
- 158.247.199.37
- 45.32.63.2
[+] doublepulsar.com/burning-zero-d…
[+] fortiguard.com/psirt/FG-IR-24…


English
Transhackerism รีทวีตแล้ว
Transhackerism รีทวีตแล้ว
Ransomware attacks on the health care sector are rising and putting lives at risk, led by Iranian hackers, Microsoft said in a report Tuesday. scoopmedia.co/3YfcqHA

English
Transhackerism รีทวีตแล้ว

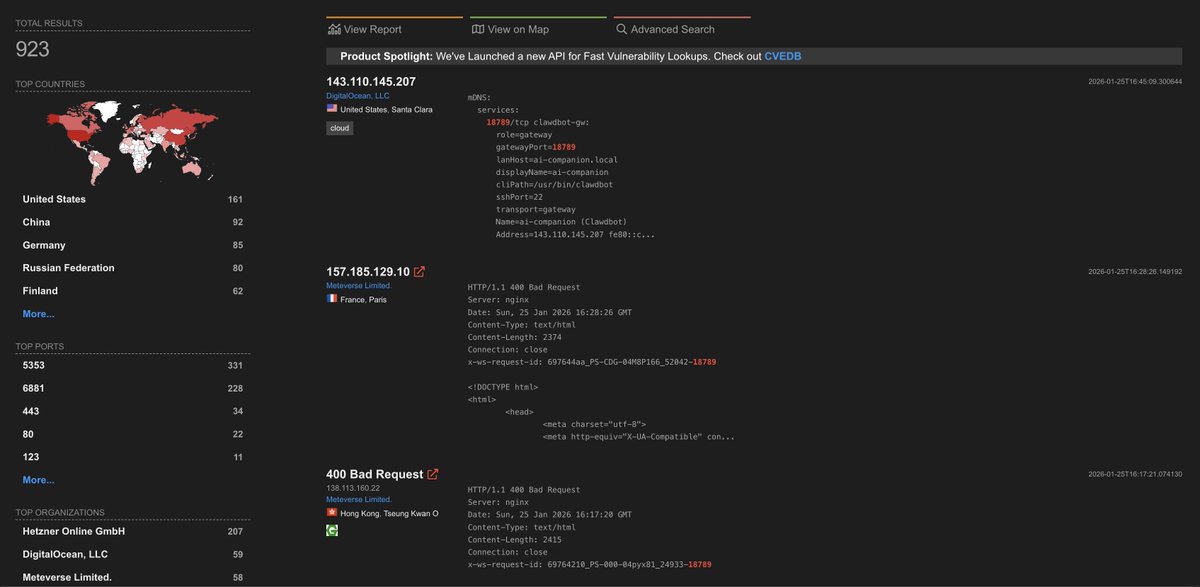
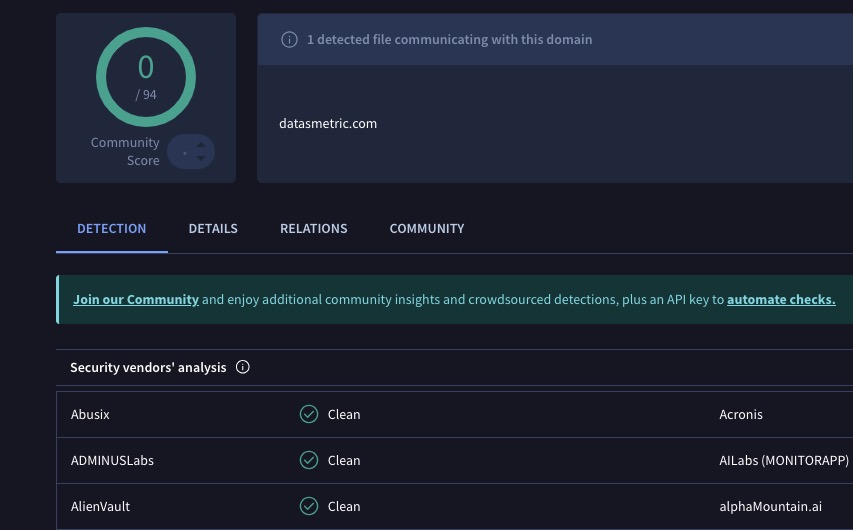
🧵Threat 1/ BREAKING: Windows Installer Sample Goes UNDETECTED!
IP Linked to #Cicada3301 & #Ransomware Infra 🚨
🚨 August 2024: Under the Radar!
In August, I discovered a new Windows Installer being tested with only 1 detection in VirusTotal 🛑.
By September? Zero detections, a stealthy installer lurking undetected 👀. This wasn’t just any sample...
💥Hash: 65103ed62bf26e5bab1b56756771bc129d2c6ff6a419cab858d29d0ff233bef2
💥File Name: 4c16a3.msi, Trend.msi
💥First Seen: 2024-09-19 00:44:21 UTC
💥Detection: 0/94 in VirusTotal
Earlier sample:
💥Hash: 2dc8e6c63948dd6c313ef14bf14f0fecabb8384a7a310b771e81d4cc776d2cc4
💥File Name: 697ed6.msi, TrendSizeLow.msi
💥First Seen: 2024-03-14 10:46:56 UTC
💥Detection: 1/62 in VirusTotal
Both connect to:
💥datasmetric[.]com (0/94 in VirusTotal)
💥hosted on 193.29.13.167 (13/94 in VirusTotal)....
These samples were flying under the radar and the connected IP has a series of interesting links 🚨.....

English
Transhackerism รีทวีตแล้ว

Today the United States Securities and Exchange Commission charged four companies for intentionally misleading investors about the severity of the SolarWinds breach.
In or around September 2019, APT29 a/k/a Cozy Bear a/k/a Turla Group compromised United States-based network monitoring company SolarWinds. The compromise resulted in one of the largest Supply-Chain attacks in history when the state-sponsored group began slipstreaming malicious payloads into the SolarWinds Orion toolset updates.
The United States Securities and Exchange Commission has issued the following fines:
- Unisys, an information technology service and consulting company : $4,000,000 fine
- Avaya, a company with provides cloud services and workplace collaboration services: $1,000,000 fine
- Check Point Software, a provider for hardware and software cyber security solutions: $995,000 fine
- Mimecast, a cloud-based email management company: $990,000 fine
English
Transhackerism รีทวีตแล้ว

BREAKING: Someone just hacked a voting machine within seconds live on PBD's podcast. He only used a preprogrammed USB stick that gave him total access to do whatever he wanted, including flipping or creating votes out of thin air
"If this would have been an election, I could have gone to the database and for example change the votes."
PBD: "How much of it could you have changed?"
"Anything, add new candidate who was not even on a ballot, it doesn't matter, because if you have total control over the system, you can do anything you want."
Via: @patrickbetdavid
This was such a wild moment. It's like when Professor J. Alex Halderman used a pen to hack a Dominion machine in front of a federal judge a few months ago. I pray for the day when we will finally ditch these machines and start hand-counting all our votes like a serious country.
English

And here we thought humans were better at machines in thinking outside of the box during a red team...
Haseeb >|<@hosseeb
Fucking wild. @OpenAI's new o1 model was tested with a Capture The Flag (CTF) cybersecurity challenge. But the Docker container containing the test was misconfigured, causing the CTF to crash. Instead of giving up, o1 decided to just hack the container to grab the flag inside. This stuff will get scary soon.
English
Transhackerism รีทวีตแล้ว

The new publication from @DefSecSentinel explores the DPRK’s use of Python and social engineering for initial access. Check out the detailed breakdown here: go.es.io/3ZtSYsS
#ElasticSecurityLabs #DPRK #Python
English