
🚨 Cyvers Alerts 🚨
1.7K posts


@CyversAlerts
Preemptive prevention of security, fraud, and compliance threats in Web3. Trusted byBinance, Cryptocom, Ledger, Uphold & more. 📧 [email protected] | @Cyvers_

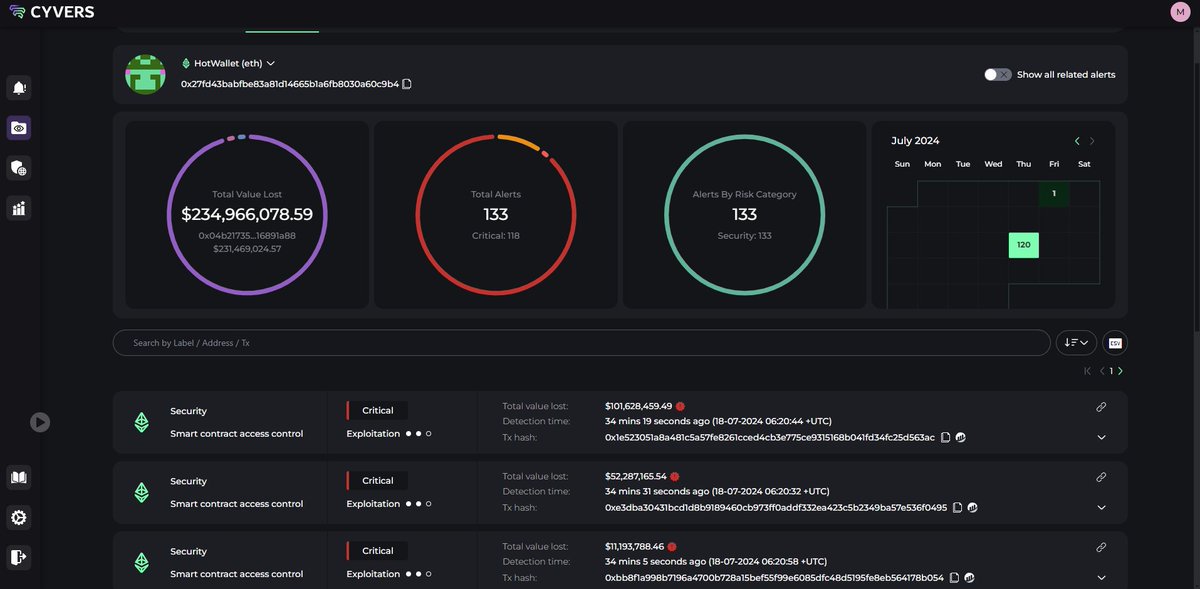






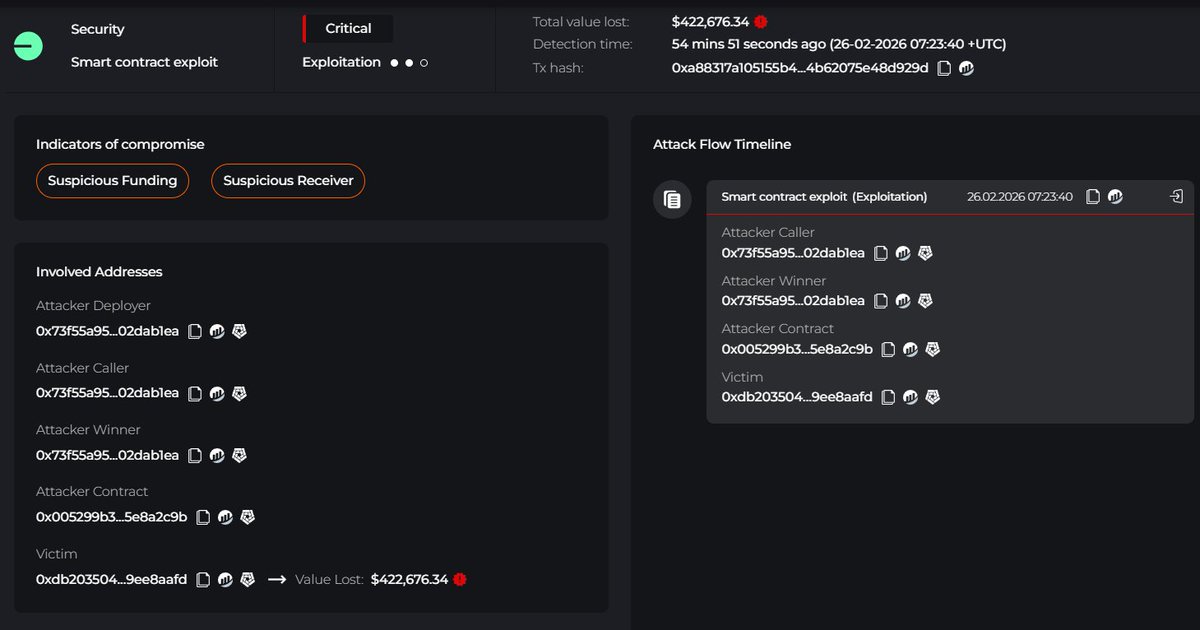

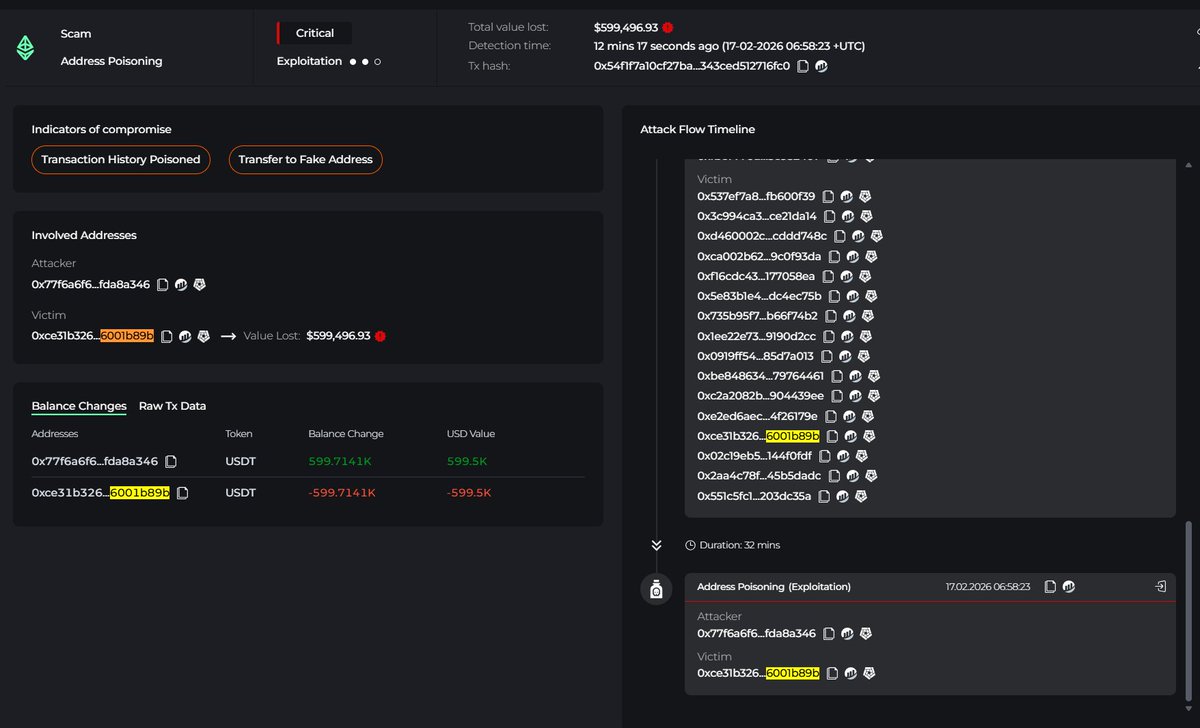













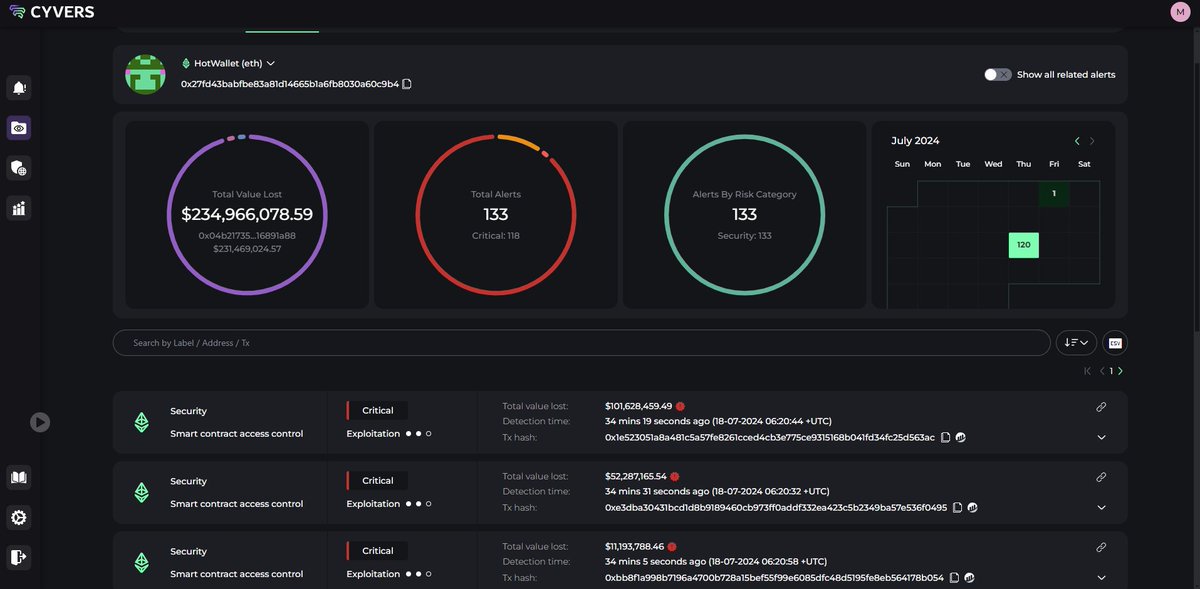
Unleash Protocol Incident Notice Earlier today, we detected unauthorized activity involving Unleash Protocol smart contracts, which led to the withdrawal and transfer of user funds. Our initial investigation indicates that an externally owned address gained administrative control via Unleash’s multisig governance and carried out an unauthorized contract upgrade. This upgrade enabled asset withdrawals that were not approved by the Unleash team and occurred outside our intended governance and operational procedures. The assets identified as affected at this stage include: - WIP - USDC - WETH - stIP, vIP After the withdrawals, the assets were bridged using third-party infrastructure and transferred to external addresses. What we know at this point: - The incident originated within Unleash Protocol’s governance and permission framework - There is no evidence of compromise to Story Protocol contracts, validators, or underlying infrastructure - The impact appears limited to Unleash-specific contracts and administrative controls - The investigation is ongoing, and all conclusions will be confirmed before final disclosure What we are doing: - All Unleash Protocol operations have been immediately paused to prevent further risk - We are working closely with independent security experts and forensic investigators to determine the root cause - We are conducting a full review of multisig signer activity, key management practices, and governance processes - Relevant on-chain data is being preserved, and we are coordinating with ecosystem partners and infrastructure providers - We are evaluating remediation and recovery measures to be communicated once validated What users should do: - Please refrain from interacting with Unleash Protocol contracts until further notice - Follow only official Unleash communication channels for accurate updates - Further instructions will be provided once next steps are confirmed We take this incident with the utmost seriousness and fully acknowledge the impact on our users and partners. Our immediate focus is to gain a complete understanding of the situation, maintain transparent and responsible communication, and determine appropriate remediation actions. We will continue to share updates as soon as reliable information becomes available. Unleash Team