Sabitlenmiş Tweet

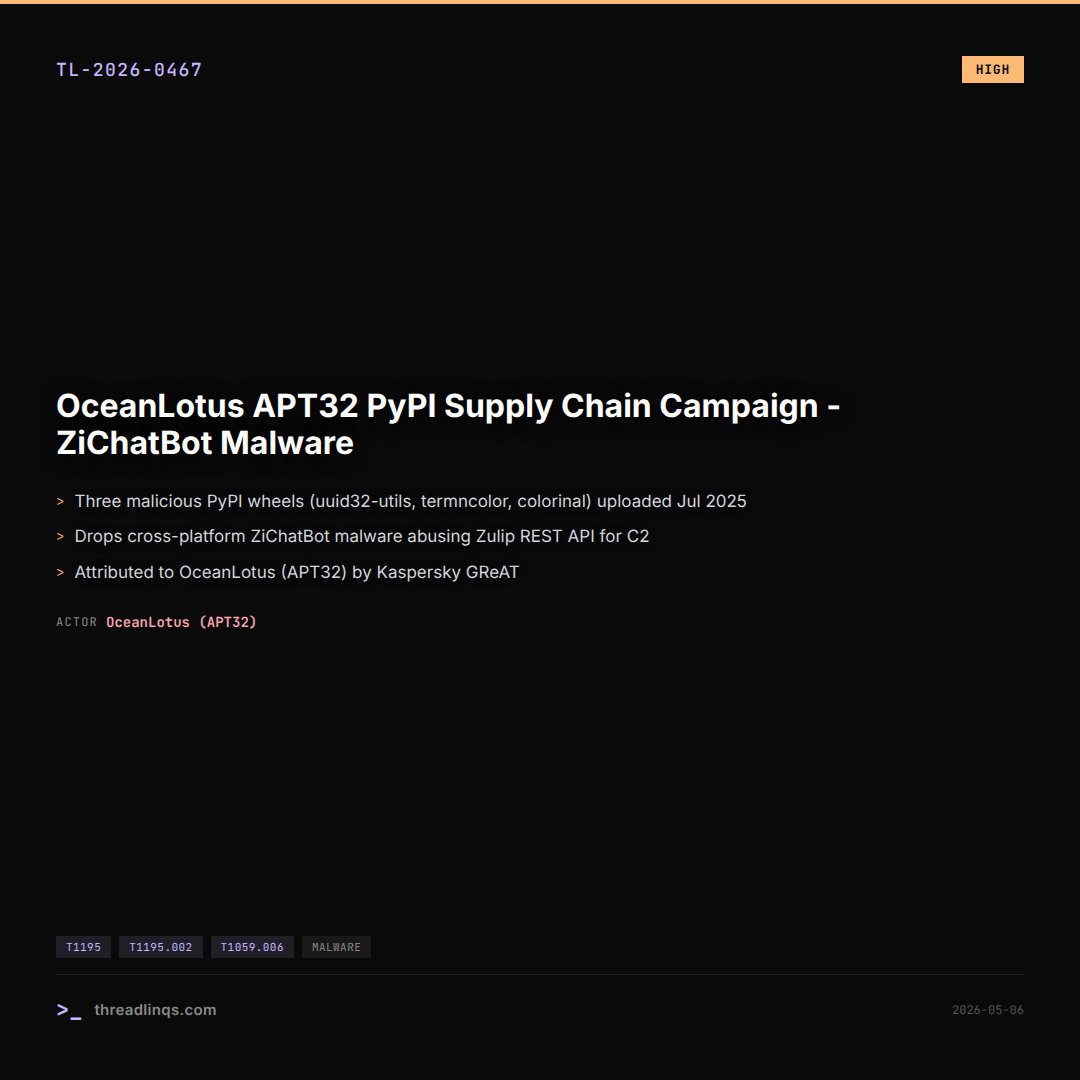
New Research!
seqrite.com/blog/operation…
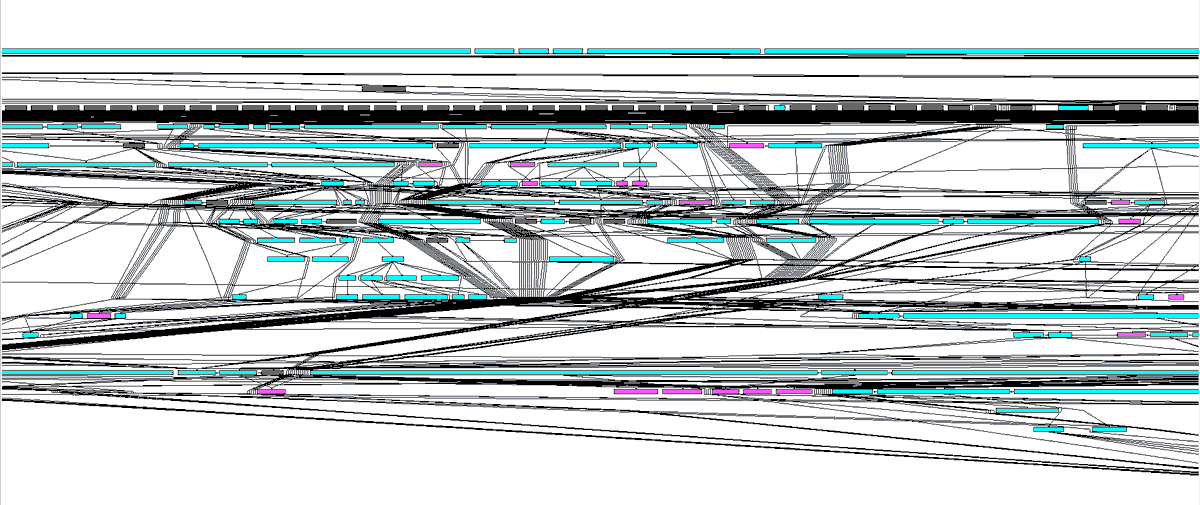
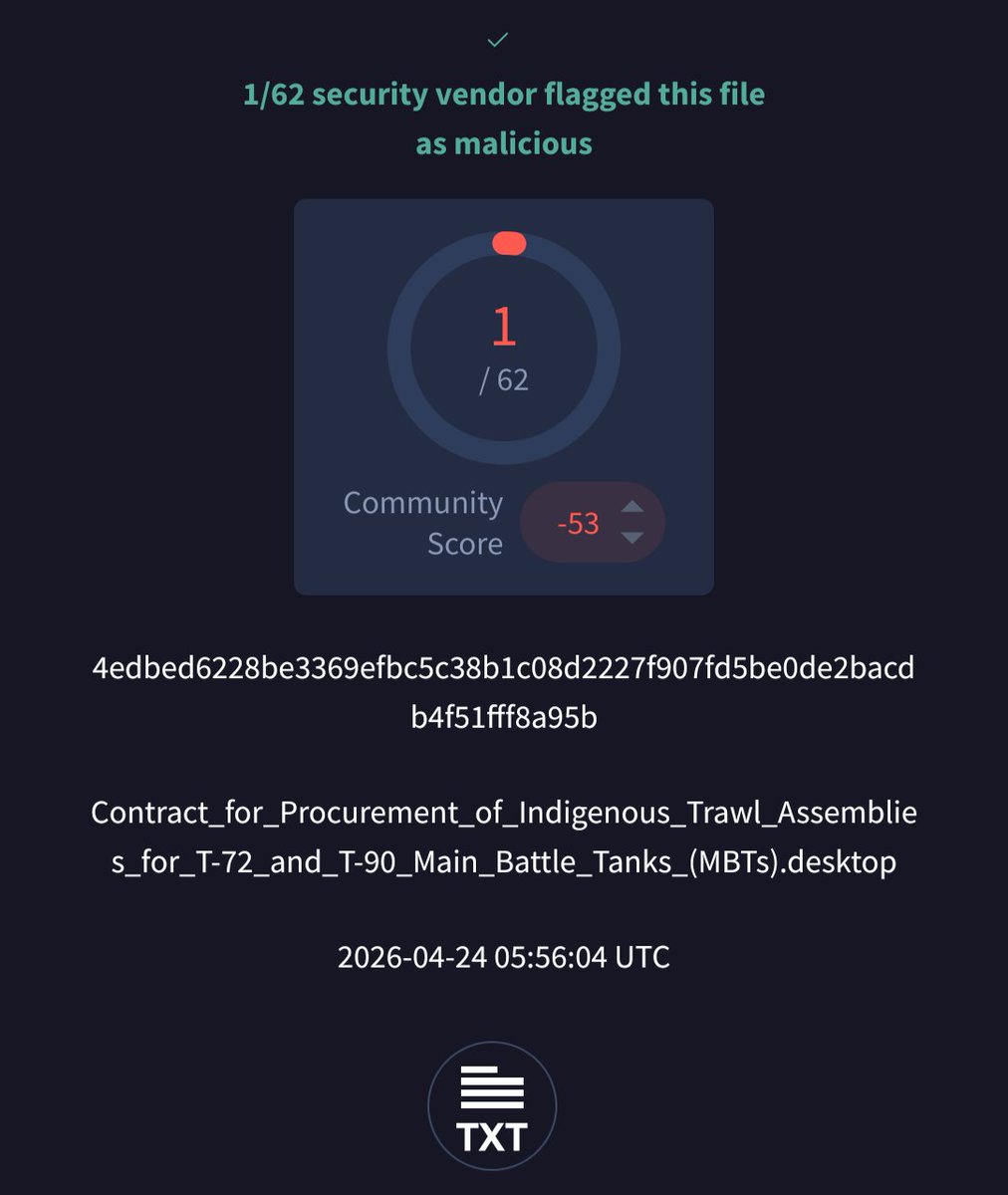
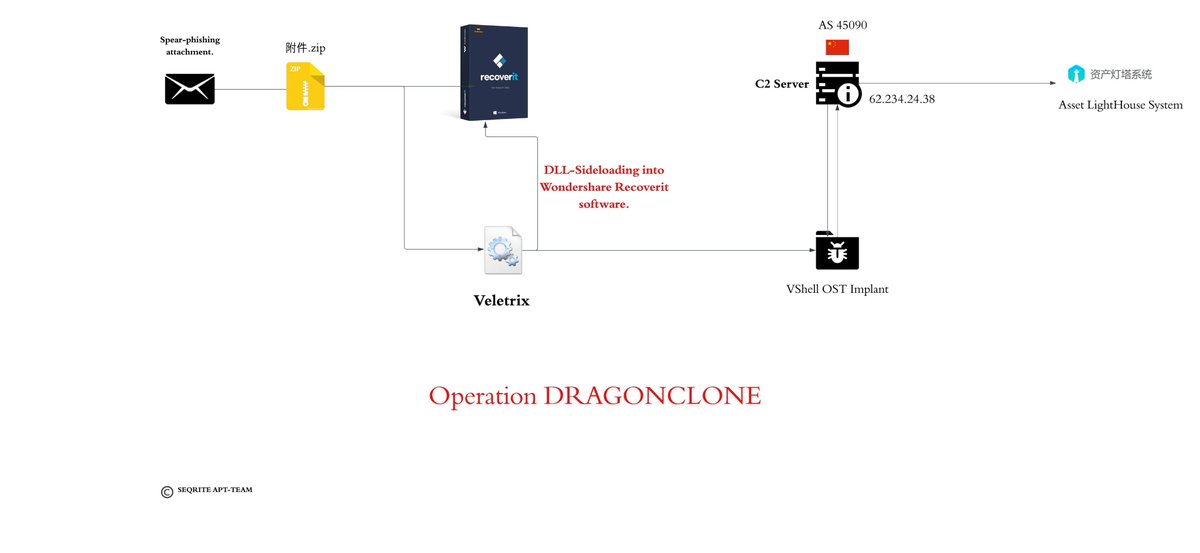
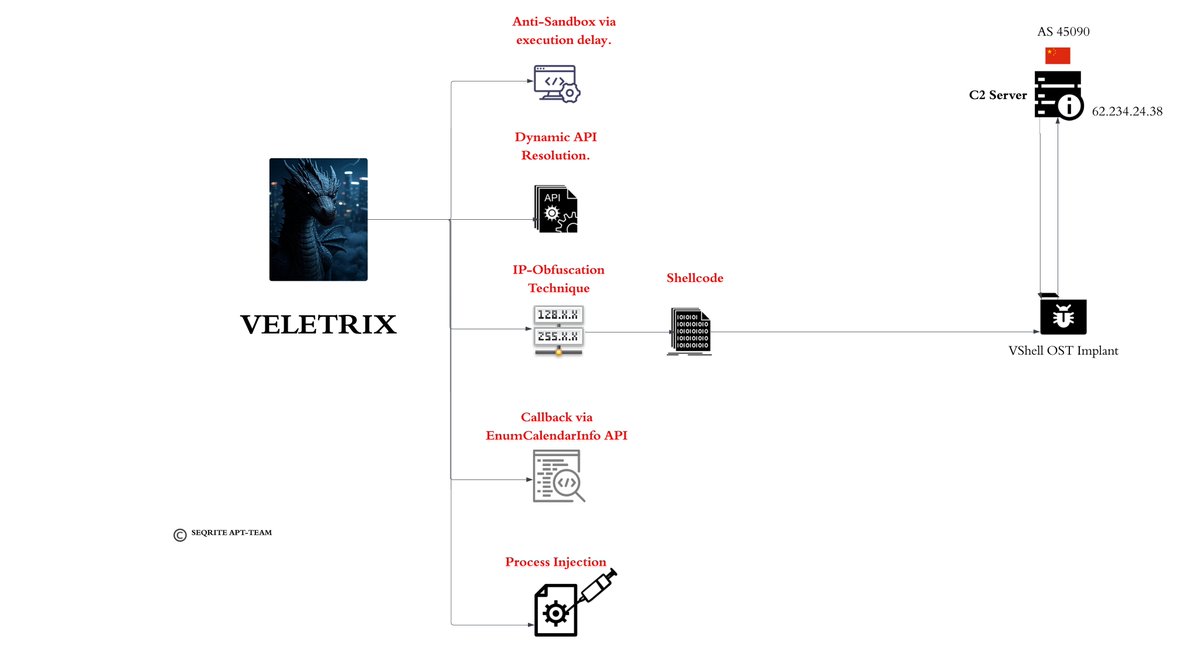
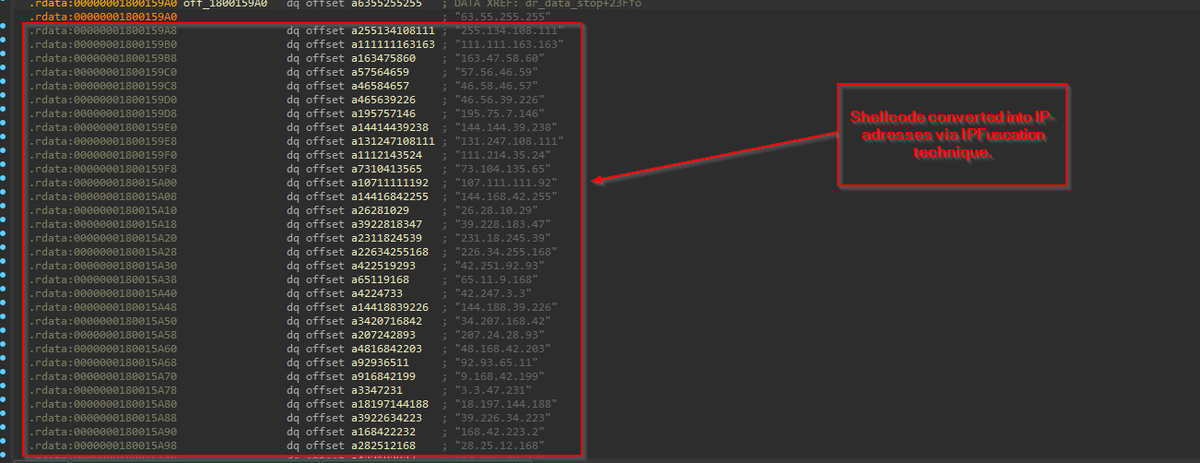
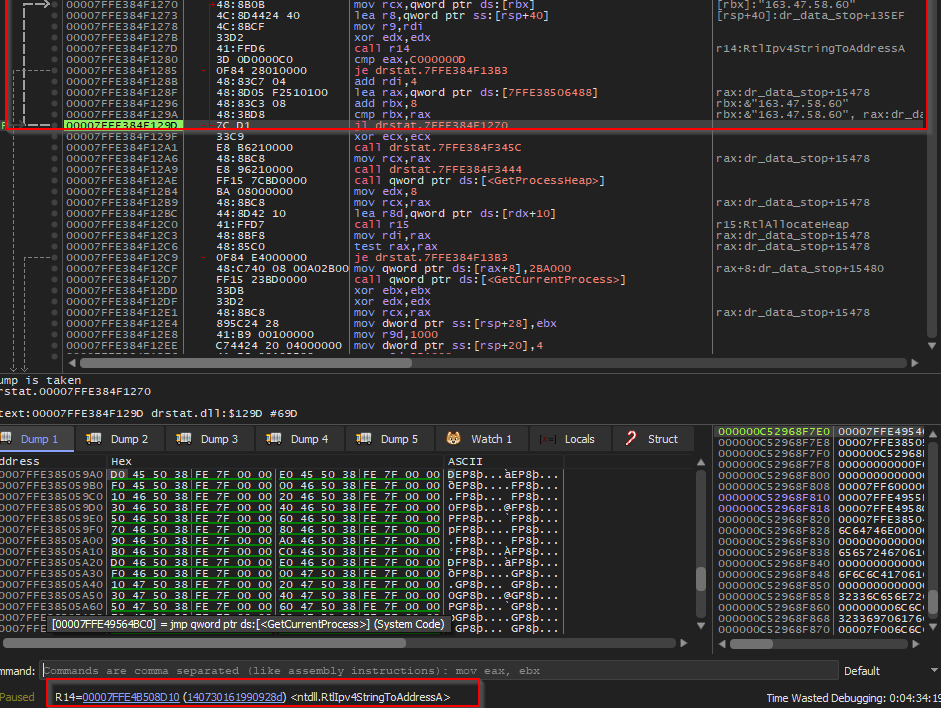
We have found an interesting campaign targeting an entity of Chinese telecom with VELETRIX implant. The implant uses anti-sandbox, shellcode obfuscation technique via IPV4 and execution via EnumCalendarInfo leading to Vshell implant.
English