پن کیا گیا ٹویٹ

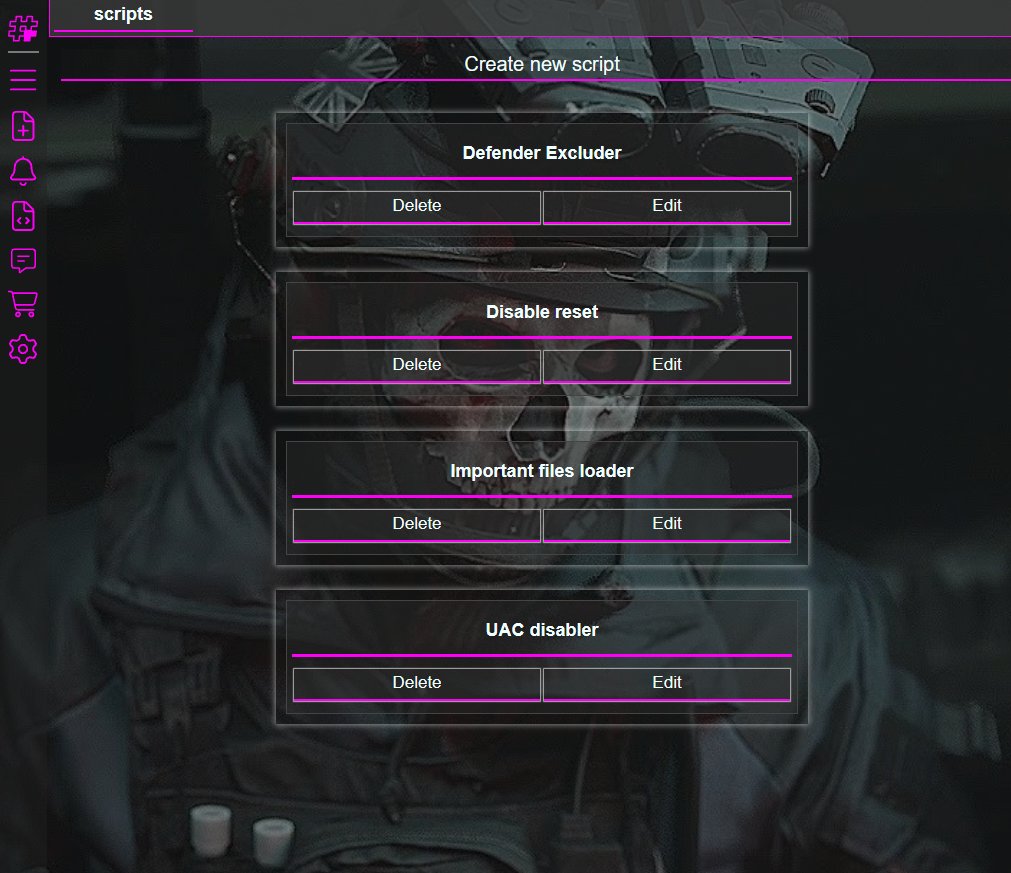
I’ve released a PoC and a technical write-up for a local privilege escalation vulnerability I discovered last year and reported to Lenovo PSIRT, affecting many gaming laptop brands, including Lenovo, MSI, Thunderobot, and others.
github.com/ZeroMemoryEx/C…
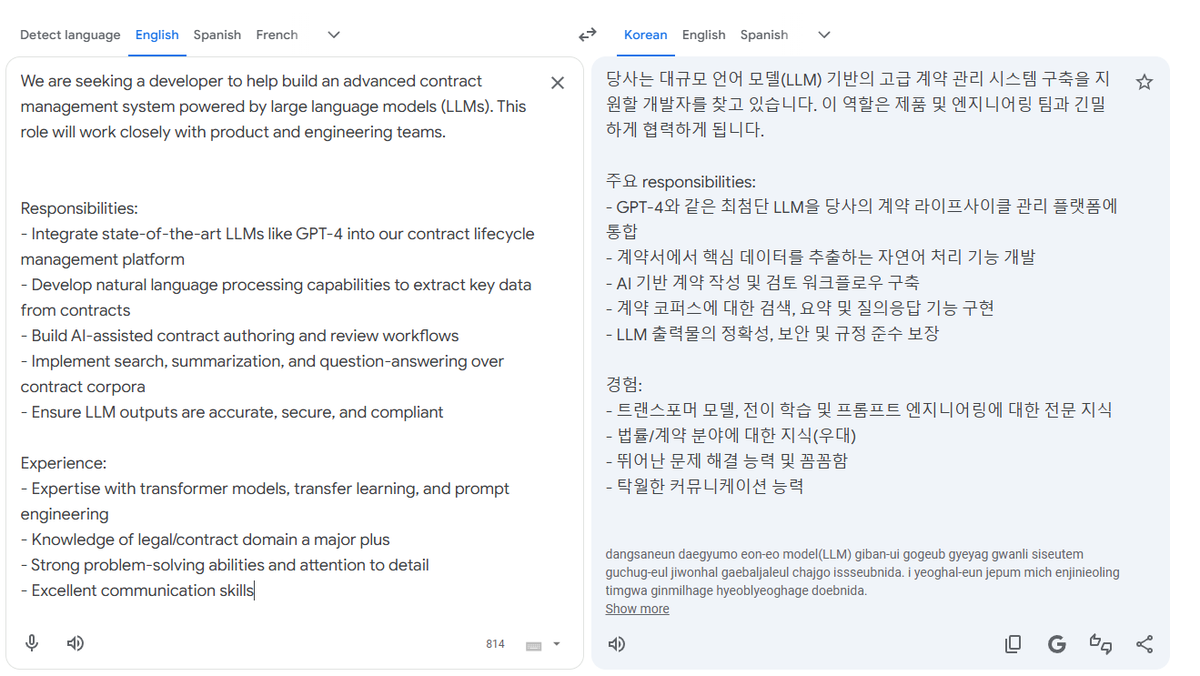
English