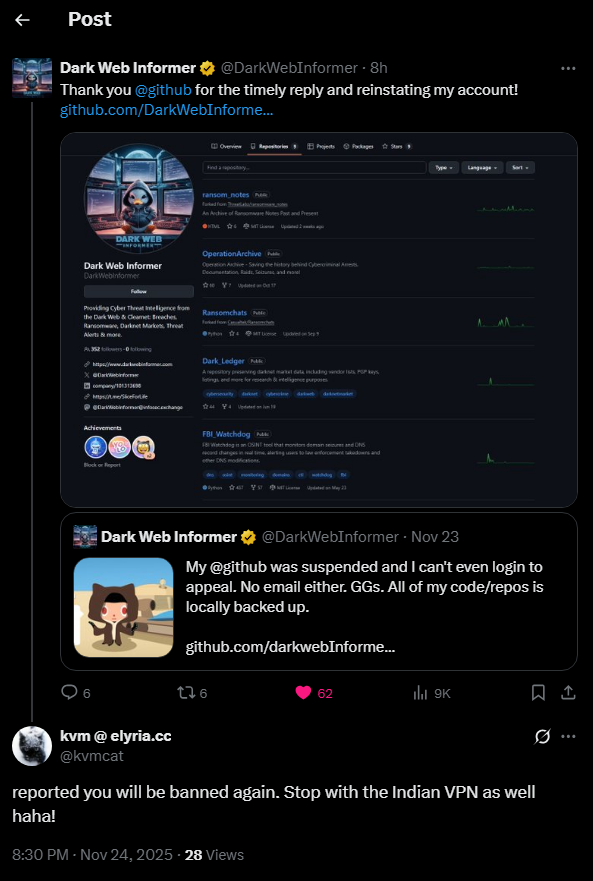
Rey
117 posts

Rey
@dulls
Old @ReyXBF | Signal: mkeaton.41 (PGP: https://t.co/Atkyxyols4)



Sevy's snitching on everybody





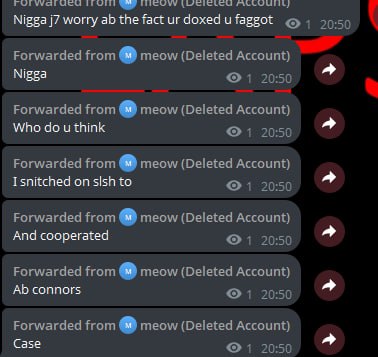
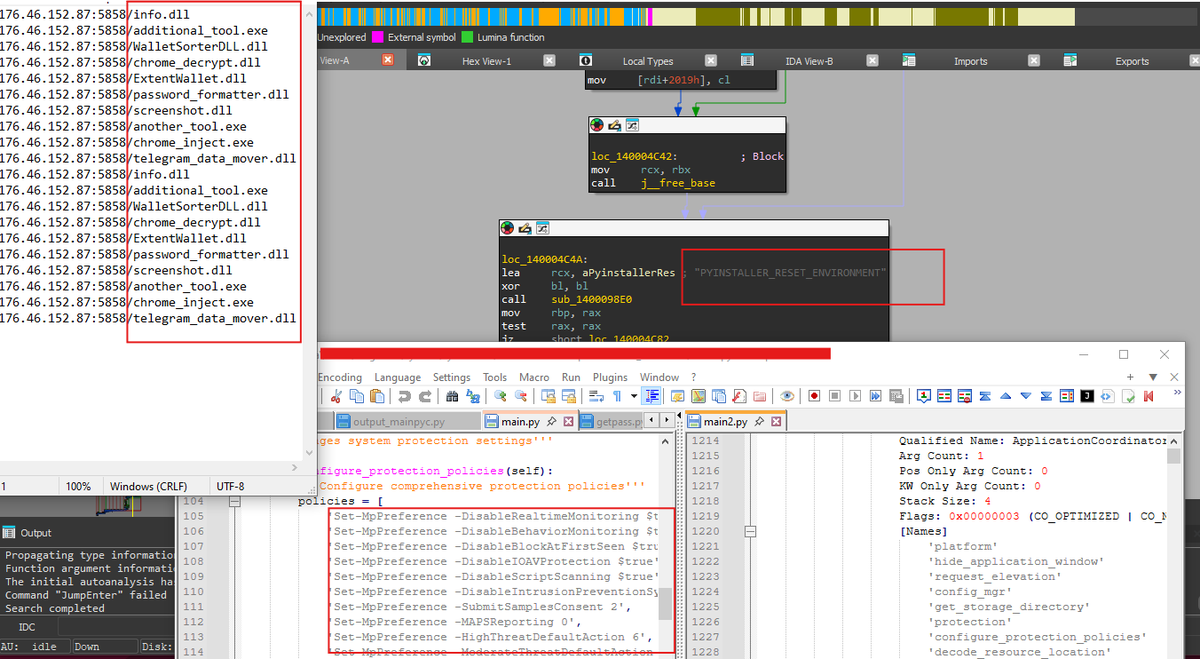
🚨 OSINT EXPOSÉ: FalconFeeds Cracks Open Scattered Spider's Hidden Iranian Nerve Center! 🚨 Deep in our undercover ops: Admin "Rey" (ilovethensa) pulling strings on "LAPSSUS$ Hunters Part 7" (t.me/comefacediswood)—the beating heart of their LAPSUS$ resurrection, as detailed in our Aug 2025 dossier. Bombshell trace: +98 919 362 **** (Iran MCI). Real identity? Maryam Rashidi. An Iranian operative deep in SS's global chaos?! Group chatter just lit up: Name-dropping us (FalconFeeds) while scheming hits on intel firms and OSINT hunters—textbook psyop + breach playbook (Porsche hacks, Epstein files recirc, firmware black market). Account flips: 25/11/25 → Rey; 01/10/25 → jolt30n (Jolt). This Iran-SS nexus? Game-changer for cybercrime tracking. We're mobilizing—OSINT pros, slide into support@falconfeeds.io for collab intel. Screenshots + full breakdown in thread. Who's exposed next? #ScatteredSpider #IranCyber #OSINTBombshell #ThreatIntel









🚨‼️ Law enforcement dismantled 1,025+ servers and seized 20 domains in Operation Endgame. Rhadamanthys infostealer, VenomRAT, and Elysium botnet were targeted. One VenomRAT-related arrest was made in Greece; 11 locations were searched in Germany, Greece, and the Netherlands.

#exploit High severity Windows vulnerabilities: 1⃣. CVE-2025-26686: RCE in Windows 10/11/Srv TCP/IP stack - github.com/mrk336/CVE-202… // leaves sensitive memory unlocked, allowing remote attackers to hijack systems. Exploitable over the network, it risks full compromise. Patch now.. 2⃣. CVE-2025-60710: LPE in Taskhost Windows Tasks - github.com/Wh04m1001/CVE-… // Improper link resolution before file access ('link following') in Host Process for Windows Tasks allows an authorized attacker to elevate privileges locally 3⃣. CVE-2025-54110: Windows Kernel Integer Overflow Privilege Escalation - github.com/ByteHawkSec/CV… // high-severity vulnerability in Windows Kernel that arises from improper handling of integer values during memory allocation 4⃣ CVE-2025-54918: Improper authentication in Windows NTLM- github.com/mrk336/From-Fo… // Simulated exploitation and mitigation of CVE-2025-54918 (Win NTLM flaw). Incl. detection scripts, Ansible patching, CI/CD hardening. Demonstrates PrivEsc from low-level access to SYSTEM in hybrid cloud environments