Omar
471 posts


Omar
@beacon_exe
Senior Security Researcher @Kaspersky GReAT - tweets and opinions are my own
شامل ہوئے Aralık 2020
514 فالونگ649 فالوورز
Omar ری ٹویٹ کیا
Omar ری ٹویٹ کیا
Omar ری ٹویٹ کیا
Heartbroken to hear about the passing of @Skvern0. He was one of the best threat hunters in the industry - even APTs were afraid of him. I’m grateful for the time we worked together and for everything I learned from him. Rest in peace.

English
Omar ری ٹویٹ کیا

Kaspersky GReAT researcher @malware_owl discovered CVE-2026-3102 — a command injection vulnerability in ExifTool (≤13.49) on macOS. A crafted image file with malicious metadata can trigger arbitrary code execution. Update to v13.50 now!
#Kaspersky #GReAT #Cybersecurity #VulnerabilityResearch #OpenSource #InfoSec #macOS
English
Omar ری ٹویٹ کیا

Arkanix Stealer didn’t just steal data. It ran like a startup.
• MaaS model
• Discord marketing
• Referral program
• C++ & Python variants
• Crypto & browser data theft
Short-lived campaign. Long-term implications.
Full analysis: kas.pr/w692
#Malware #Infostealer #ThreatIntel #CyberSecurity

English
Omar ری ٹویٹ کیا
Omar ری ٹویٹ کیا

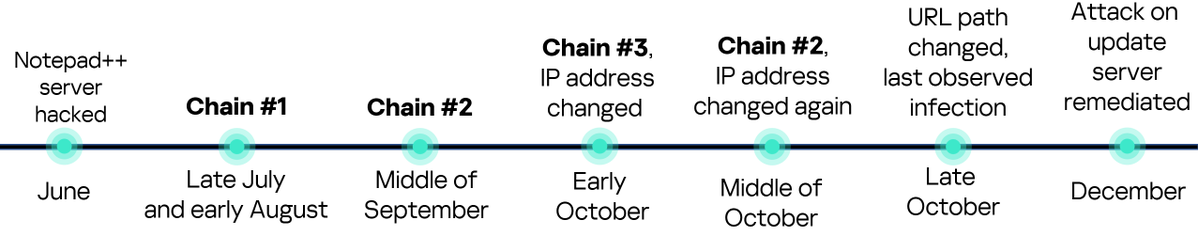
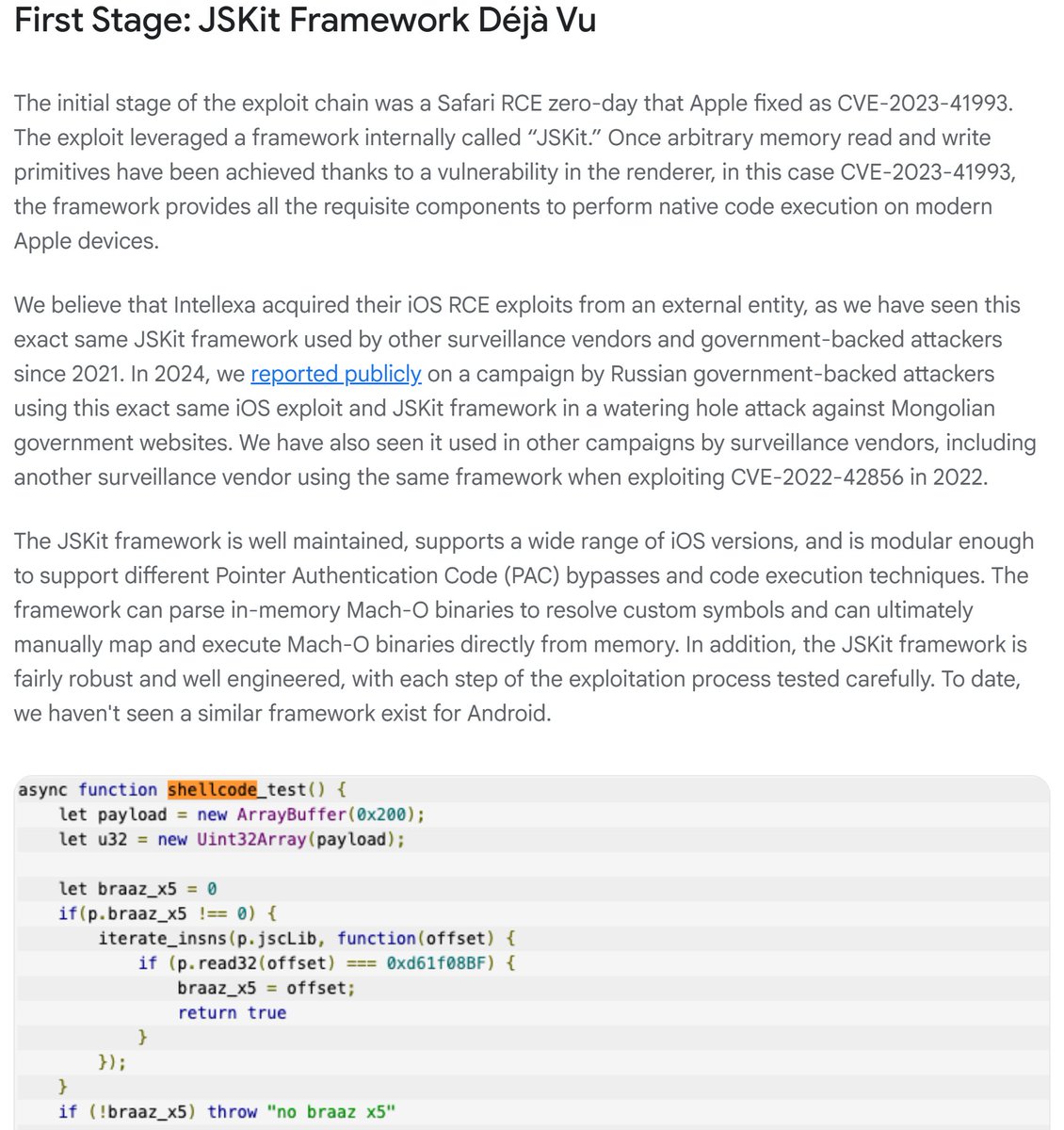
A full iOS zero-day exploit chain used in the wild against targets in Egypt. #Intellexa #Predator
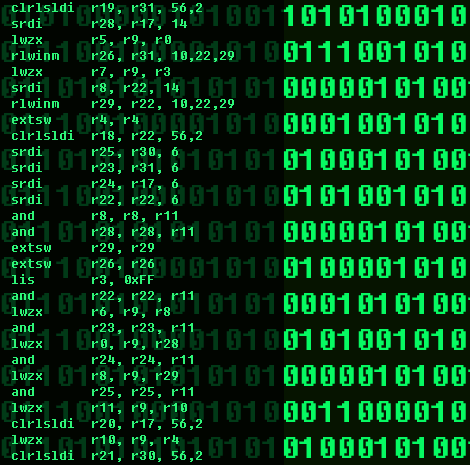
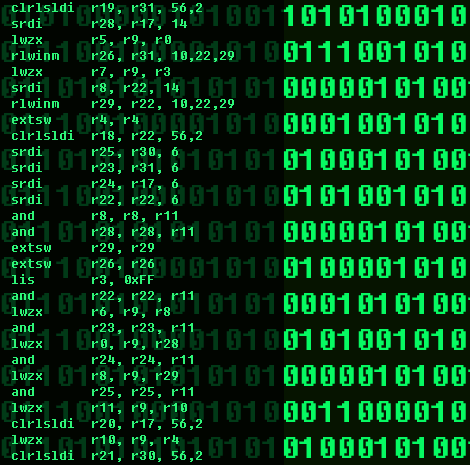
Stage 1: Initial RCE via JSKit Framework (Safari WebKit Exploitation)Entry Point: The chain starts with a zero-day RCE vulnerability in Safari's WebKit rendering engine, patched by Apple as CVE-2023-41993 (a memory corruption issue in the JIT compiler).
Stage 2: Sandbox Escape and Kernel Privilege EscalationVulnerabilities Exploited: CVE-2023-41992: Kernel IPC use-after-free (sandbox escape + local privilege escalation, LPE).
CVE-2023-41991: Code-signing bypass (LPE).
Stage 3: Persistence and Surveillance Setup (PREYHUNTER Modules)Components: Divided into two modules—"watcher" and "helper"—deployed via the escalated privileges from Stage 2.
cloud.google.com/blog/topics/th…
github.com/blackorbird/AP…

English


securelist.com/bluenoroff-apt…
اخواني واخواتي، استمتعوا بجهلكم وخشوا اعملوا سكرول لريسيرش عمنا عمر أمين الي محتاج ٥١ دقيقة قراءة وسنين فهم.
عمر امين دا ثروة قومية محتاج تأمين مخبراتي وربي.
العربية

couldn't ask for a better partner in crime at #TheSAS2025 stage.
Check out our full research, uncovering #GhostCall and #GhostHire of #Bluenoroff here:
securelist.com/bluenoroff-apt…
hypen@hypen1117
It was truly an honor to be part of #TheSAS2025 as a speaker! I and Omar (@beacon_exe) shared some juicy insights from our extensive research on #BlueNoroff's #GhostCall and #GhostHire campaign, part of #SnatchCrypto. You can find our research below. ✅ securelist.com/bluenoroff-apt…
English
Omar ری ٹویٹ کیا
Omar ری ٹویٹ کیا
My teammates @hypen1117 and @beacon_exe are absolute gods of PowerPoint. Their slides design is on another level! #TheSAS2025




English
Omar ری ٹویٹ کیا

New "Dante" malware from former "Hacking team"
securelist.com/forumtroll-apt…
English
Omar ری ٹویٹ کیا

We(@kucher1n and myself ) discovered a new advanced threat campaign, PassiveNeuron, is actively targeting Windows Server environments in government, financial and industrial organisations across Asia, Africa and Latin America.
For more details - securelist.com/passiveneuron-…
English
Omar ری ٹویٹ کیا
The SAS conference (@TheSAScon) looks AMAZING this year!🔥 Love the talks lineup, the venue, the GTA theme (!!!), and the special guest! I’m also presenting something secret👀
I’ve got one extra ticket - DM me if I might know you and you’d like to come!

English
Omar ری ٹویٹ کیا

#TheSAS2025 agenda is almost ready! Keep an eye on the website updates as we iron out the final details with our stellar speaker lineup this week.
What to expect?
🕵️♂️ One in three talks covers recent APT TTPs and investigations. We expect four mind-blowing talks on 🚘 and telematics infrastructure and at least a couple on important topics like browser security and the realities of using EOL devices.
Expect a swirl of topics and slides in our favorite PechaKucha format too!
⚡️ So, bookmark this link and secure your spot before it's too late 👉 kas.pr/6rx9
English
Omar ری ٹویٹ کیا

We recently analyzed GodRAT, a new malware strain derived from Gh0stRAT, actively targeting financial organizations. More details here - securelist.com/godrat/117119/
English
Omar ری ٹویٹ کیا

Finally, Defcon is adopting #TheSAS2025 best practices! 🥃 🥃
We’ve been doing this with EVERY speaker for over 10 years. That’s why no moderator hosts the entire day. 🤪
Eric Geller@ericgeller
Former NSA Director Paul Nakasone just did a jello shot with @defcon founder Jeff Moss as day 1 of the conference kicks off.
English
Omar ری ٹویٹ کیا

#CFP extended — your last chance to rock the floor at #TheSAS2025!
Just 10 days left to propose your research for the BIG stage and share your findings with peers from world-class cybersecurity organizations.
If you research:
▪️ Transportation and smart city vulnerabilities
▪️ New tactics and tricks from notorious #APTs
▪️ Ransomware
▪️ Best incident response practices
▪️ Supply chain and #OSS security
▪️ OT and critical infrastructure security
▪️ Vulnerabilities and fixes
then our program committee is waiting for you!
⚠️ Submit your topic by August 10th
⏩ kas.pr/6rx9
English