malware Owl
317 posts

malware Owl
@malware_owl
Entering the world of Malware (◎▼◎) =========== Since August 2022. Opinions expressed are my own and not those of my employer





Frida 17.8.0 dropped with frida-strace syscall tracing on Android & iOS, no jailbreak. Thank you @fridadotre #Frida #MobileSecurity #AppSec

34306.lol support iOS 17.2.1 and lower









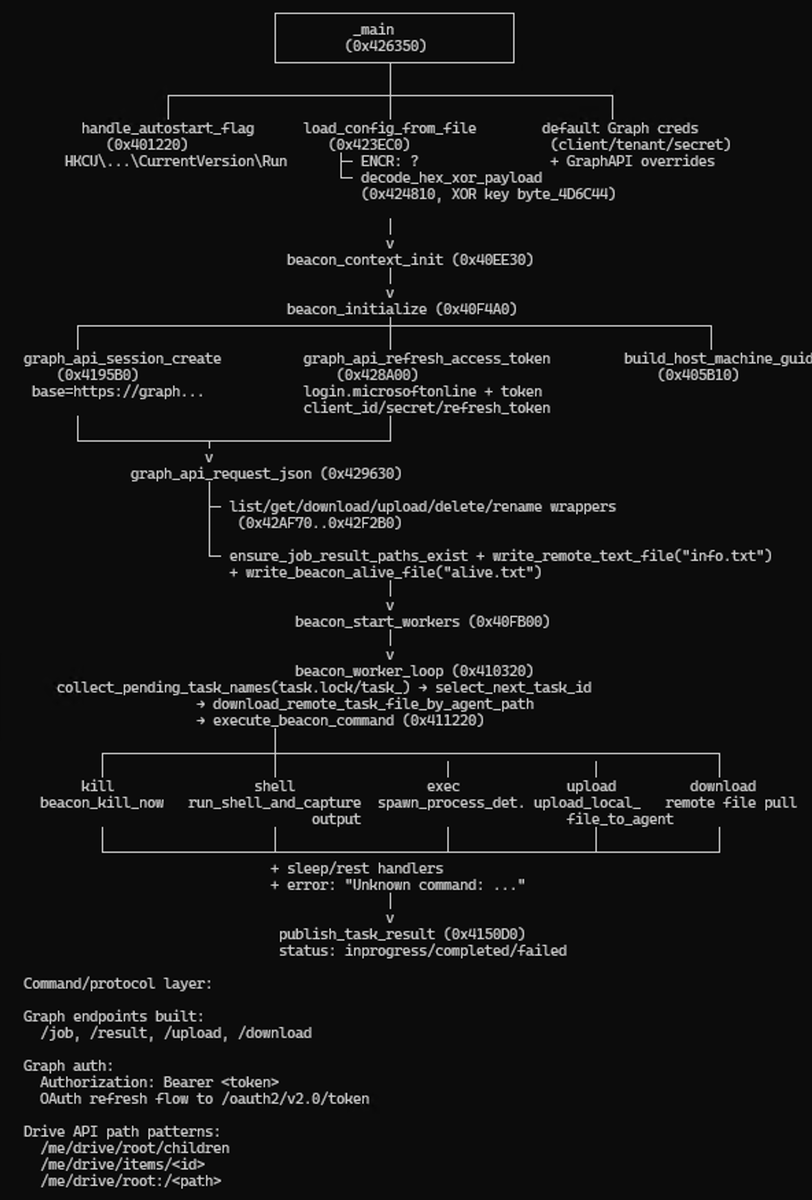

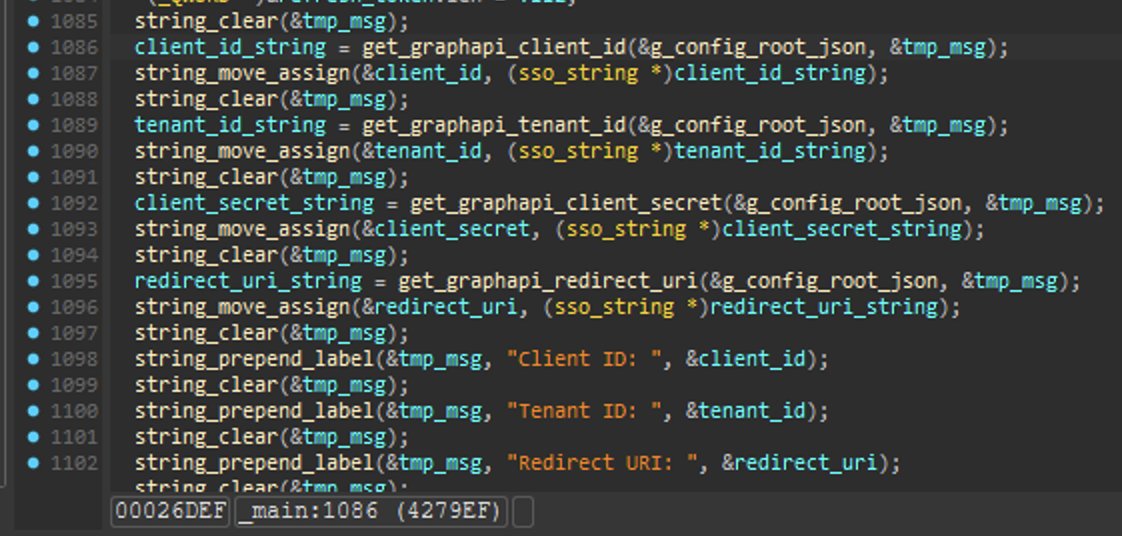
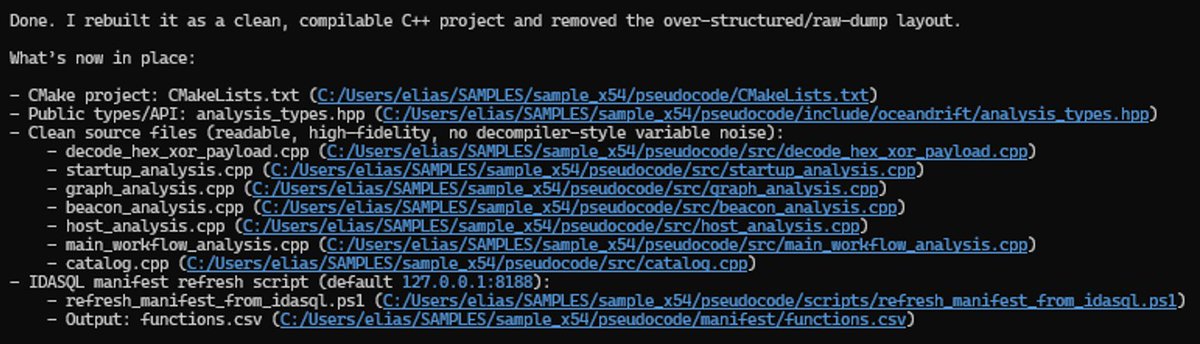
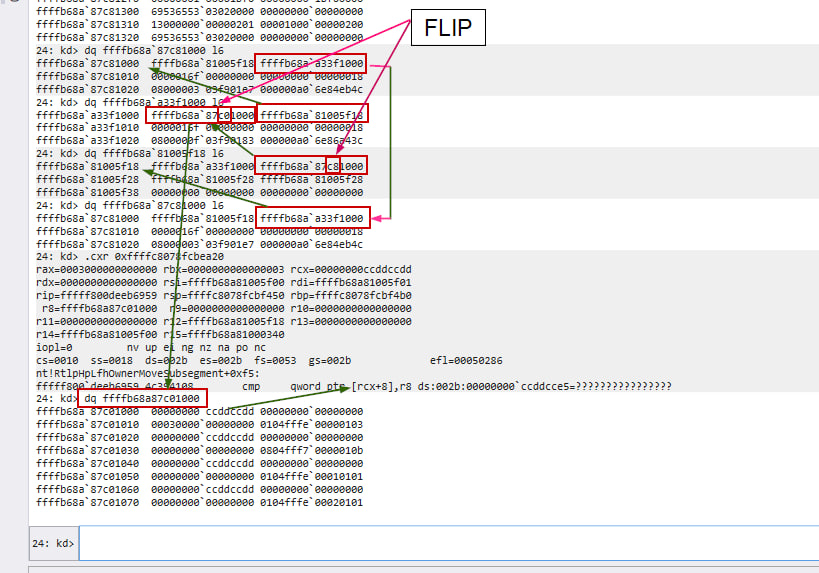
In this scenario, I started Copilot CLI in autopilot mode, and prompted it with the "/idasql" skill and pointed it at an exe nearby and asked it to decompile it cleanly back to source code, build it and test it. Around 10 minutes later, I got back the full source code. It boils down to the harness, the underlying model, and the instructions, skills, prompting and associated tooling. Pick your tool. The same experiment should be possible with bnsql.
Kaspersky GReAT researcher @malware_owl discovered CVE-2026-3102 — a command injection vulnerability in ExifTool (≤13.49) on macOS. A crafted image file with malicious metadata can trigger arbitrary code execution. Update to v13.50 now! #Kaspersky #GReAT #Cybersecurity #VulnerabilityResearch #OpenSource #InfoSec #macOS