nono.sh/blog/openclaw-…
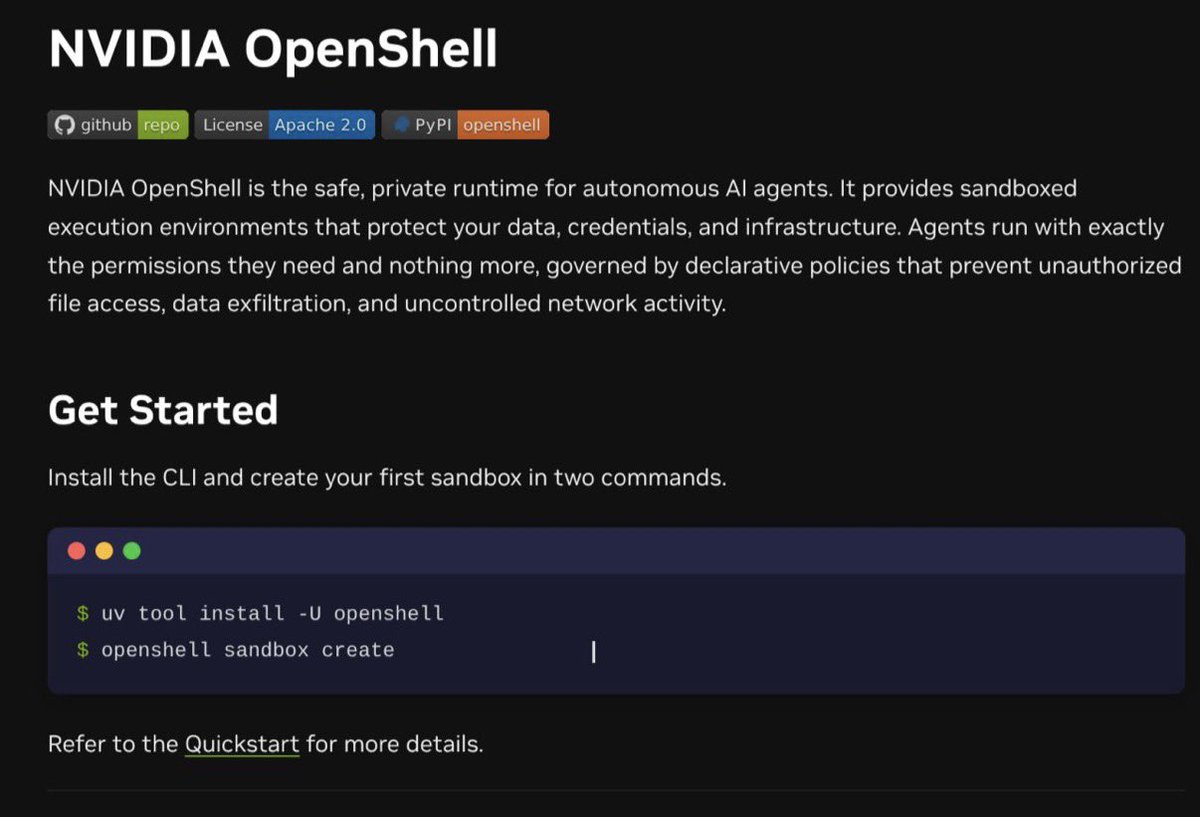
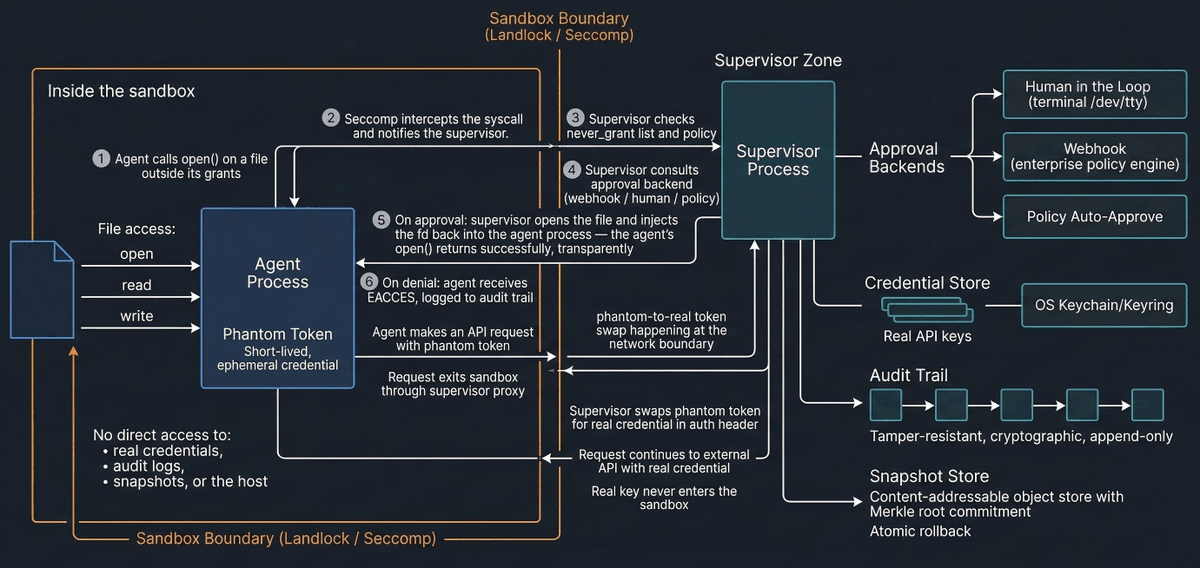
Had a lot of folks asking the difference between nono and @nvidia 's OpenShell shipped in Nemoclaw this week - as both had a significant shared feature surface and terminology - so I wrote an unbiased as possible teardown and it turns out they have quite different architectural differences and applications of use.

English