Lee ری ٹویٹ کیا

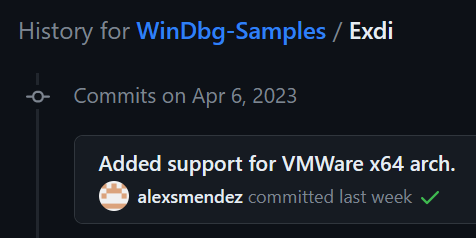
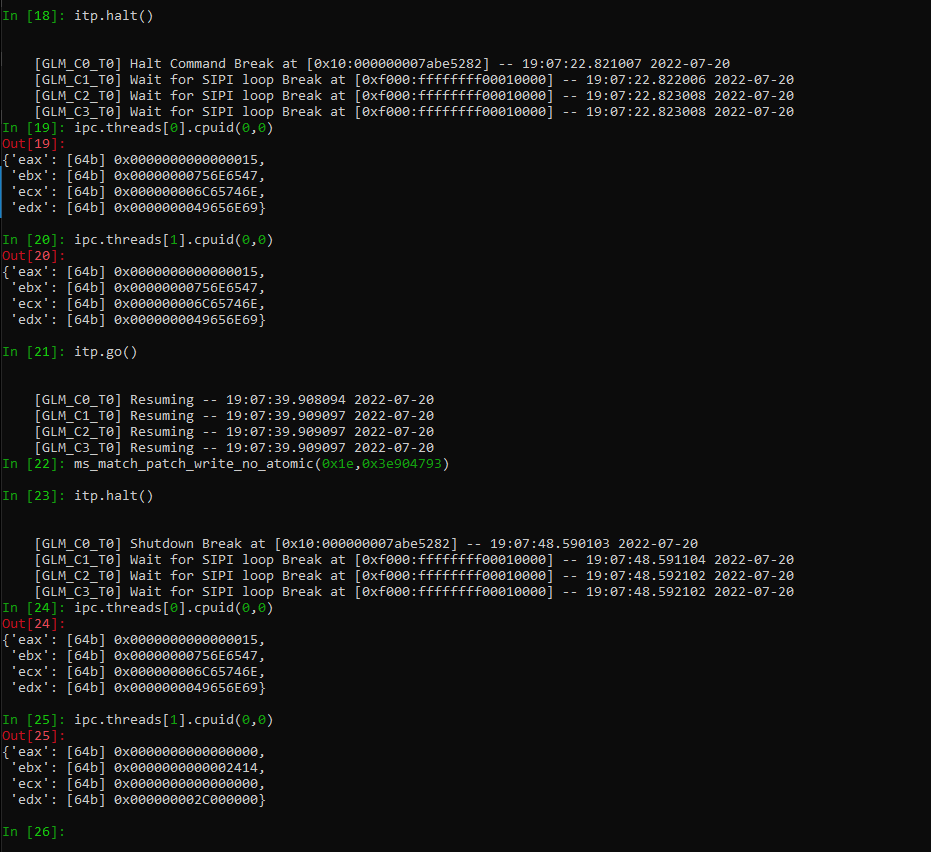
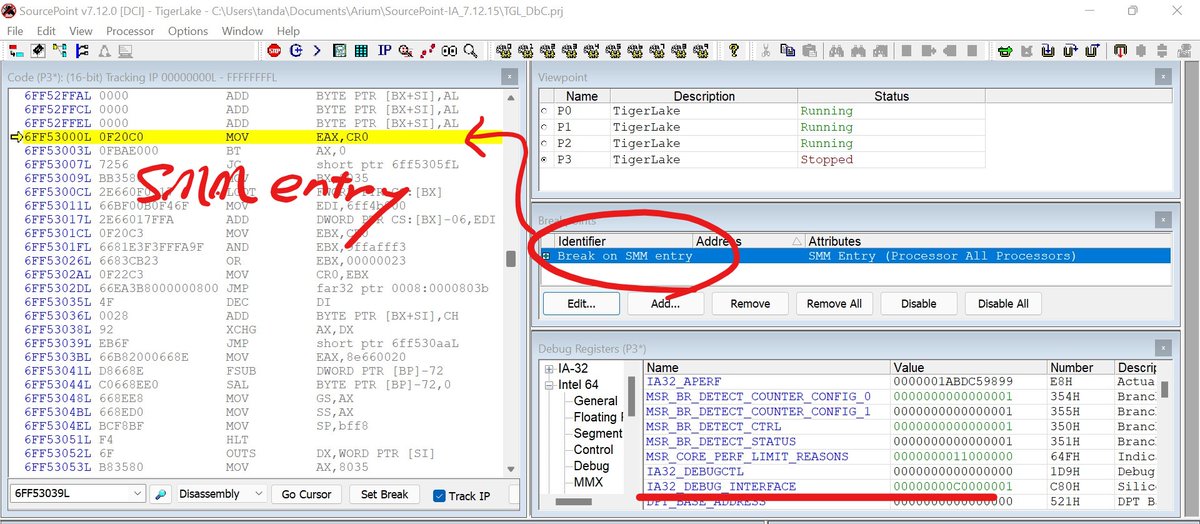
Hardware glitching masters have taken on Intel's microarchitecture - very, very cool! I'm so glad our work is contributing to research that was previously unimaginable. Research into hardware attacks on Intel processors has enormous potential...
download.vusec.net/papers/microsp…
English