Mickey retweetledi

LABScon25 Replay 📺
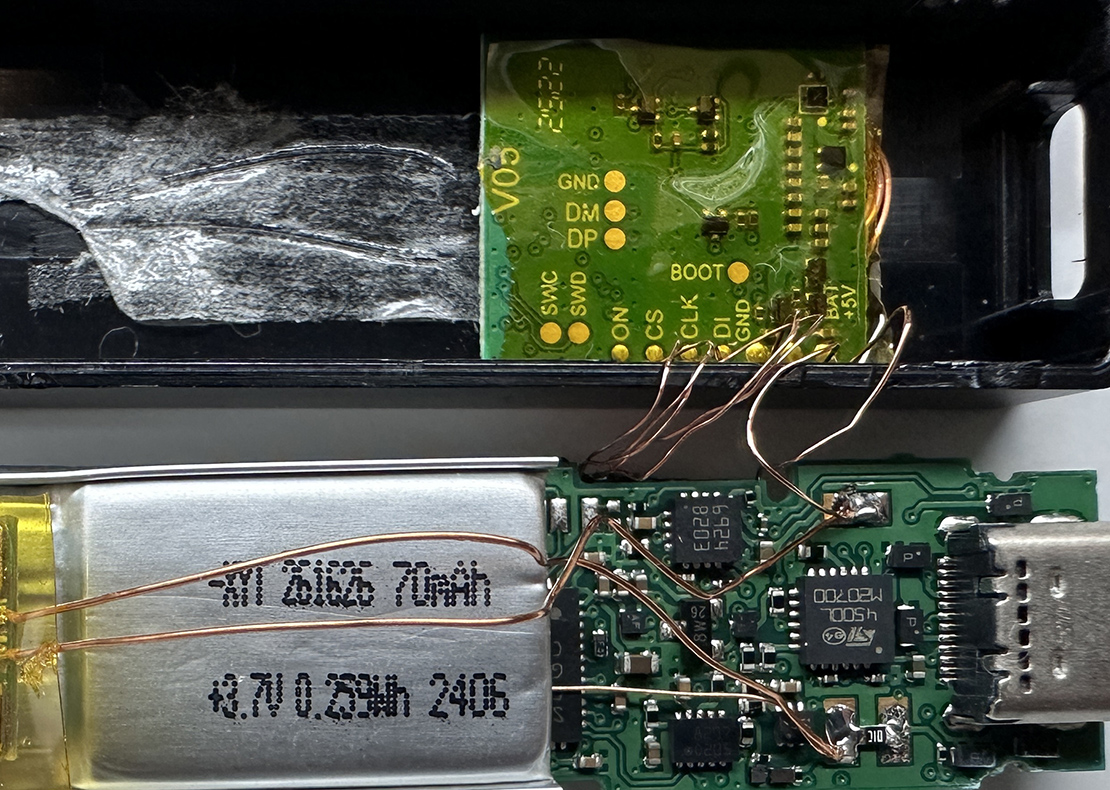
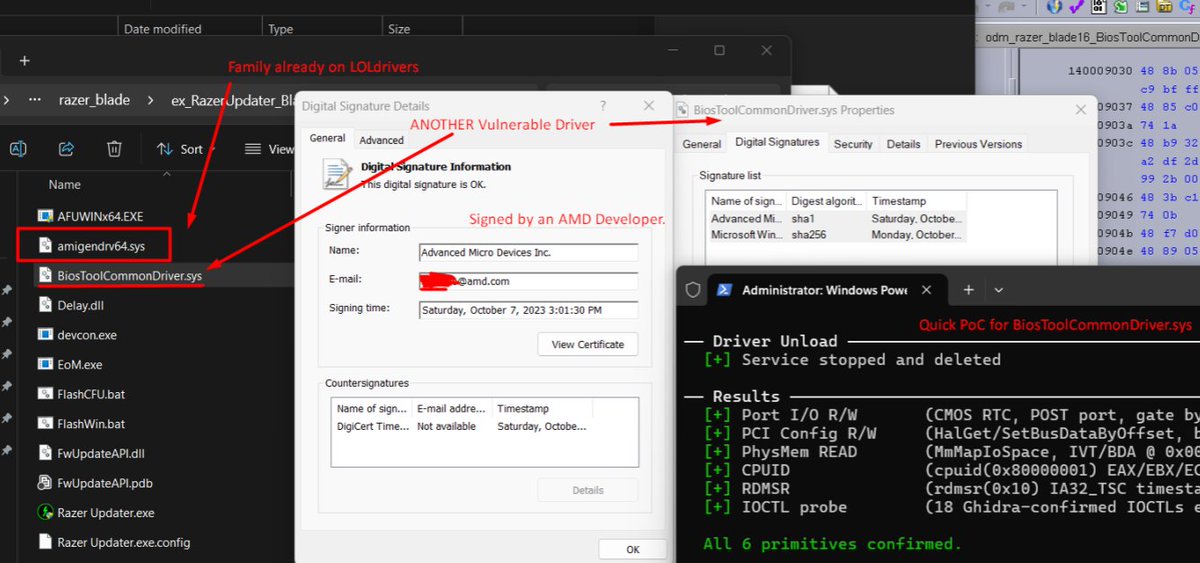
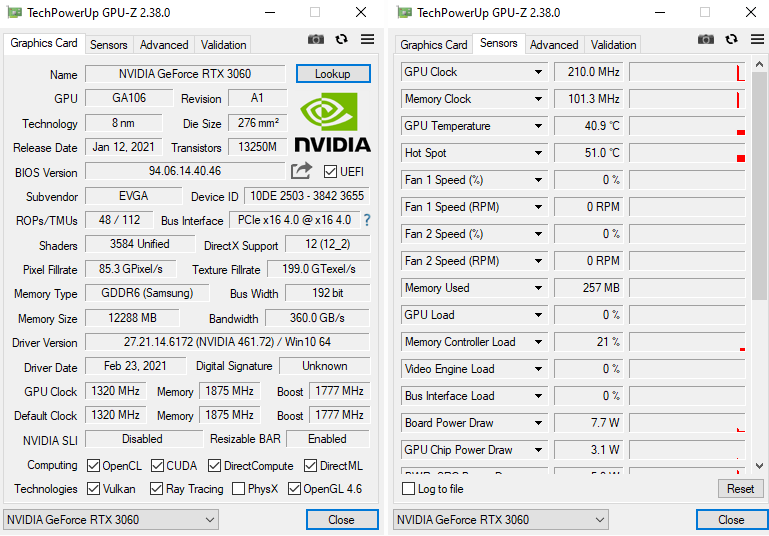
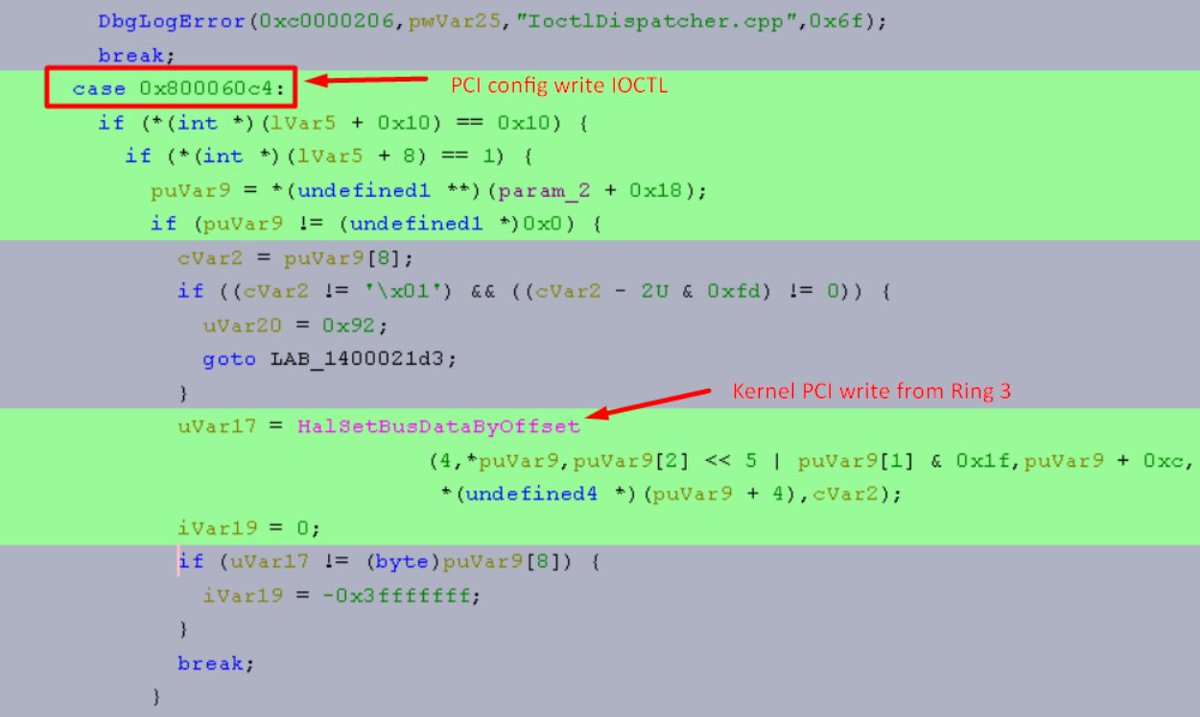
Joe Fitzpatrick: Please Connect to the Foreign Entity to Enhance Your User Experience (@securelyfitz)
sentinelone.com/labs/labscon25…
English
Mickey
7.1K posts


@HackingThings
Low hanging fruit maven. Cluster Head. Tweets are my own. https://t.co/NsUyMzcogk


We have started announcing Recon 2026 Presentations recon.cx/2026/en/speake… More talks to be announced soon once we have confirmations @frodosobon @realytcracker @allthingsida @hexnomad @0x464D @hunterbr72 @joegrand @clearbluejar @InvokeReversing @LennertWo @pinkflawd @Coiffeur0x90 @MathildeVenault @NicoleFishi19 @nicolodev @phLaul @SinSinology @i0n1c @mr_phrazer @tmanning @hex86_64 #REcon2026 #ReverseEngineering #InfoSec #cybersecurity