Lan Vu 🇻🇳
100 posts


Lan Vu 🇻🇳
@lanleft_
she/her | coffee delivery at Qrious Secure @qriousec |

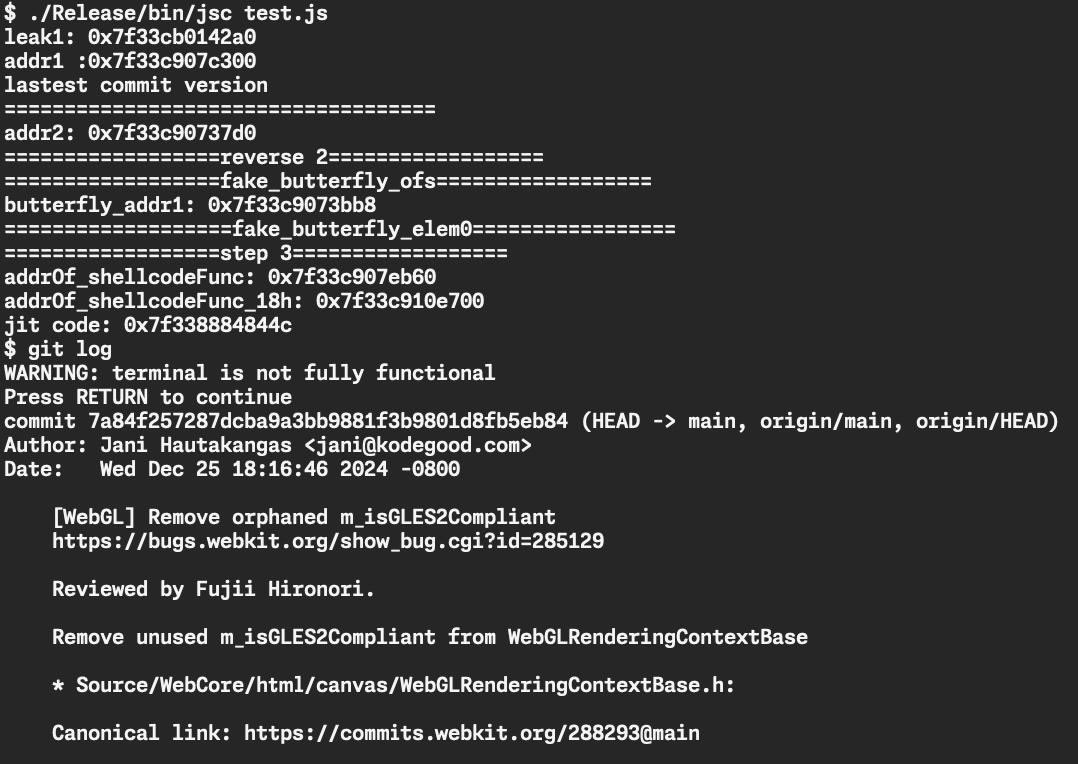
@lanleft_ has convinced firefox GC to give her a shell 🤪



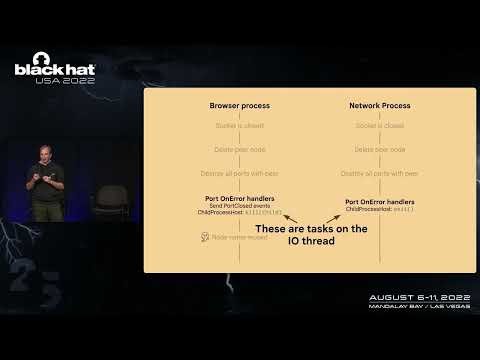
Check out our newest blog about how we took advantage of a WebGPU feature to turn an integer underflow bug into an arbitrary read in Chrome’s WebGPU. This bug was fixed by Google long ago, but our ticket is still restricted. qriousec.github.io/post/oob-angle/ by @lanleft_ + @__suto

Whoah... $250000 (CVE-2025-4609, similar to CVE-2025-2783/412578726)[412578726][Mojo][IpczDriver]ipcz bug -> renderer duplicate browser process handle -> escape sbx is now open with PoC & exploit(success rate is nearly 70%-80%) issues.chromium.org/issues/4125787… #comment11" target="_blank" rel="nofollow noopener">issues.chromium.org/issues/4125787…