@spendergrsec Correct, the main fix is the first commit you post. I think the second commit is not quite relevant
English
Ramdhan
1.8K posts
@n0psledbyte
CTF @SuperGuesser (pwn), Security Researcher @starlabs_sg









Last 7 DAYS LEFT to submit to our Off-By-One 2025 CFP! Got something exciting to share? Now’s your chance to speak at the conference. ⏰ Time is ticking! offbyone.sg/cfp Let’s make this unforgettable! #OBO2025 #Singapore


Collision - STAR Labs SG successfully demonstrated their LPE on #Ubuntu desktop. However, they used a bug that was previously reported. They still earn $5,000 and 1 Master of Pwn point.

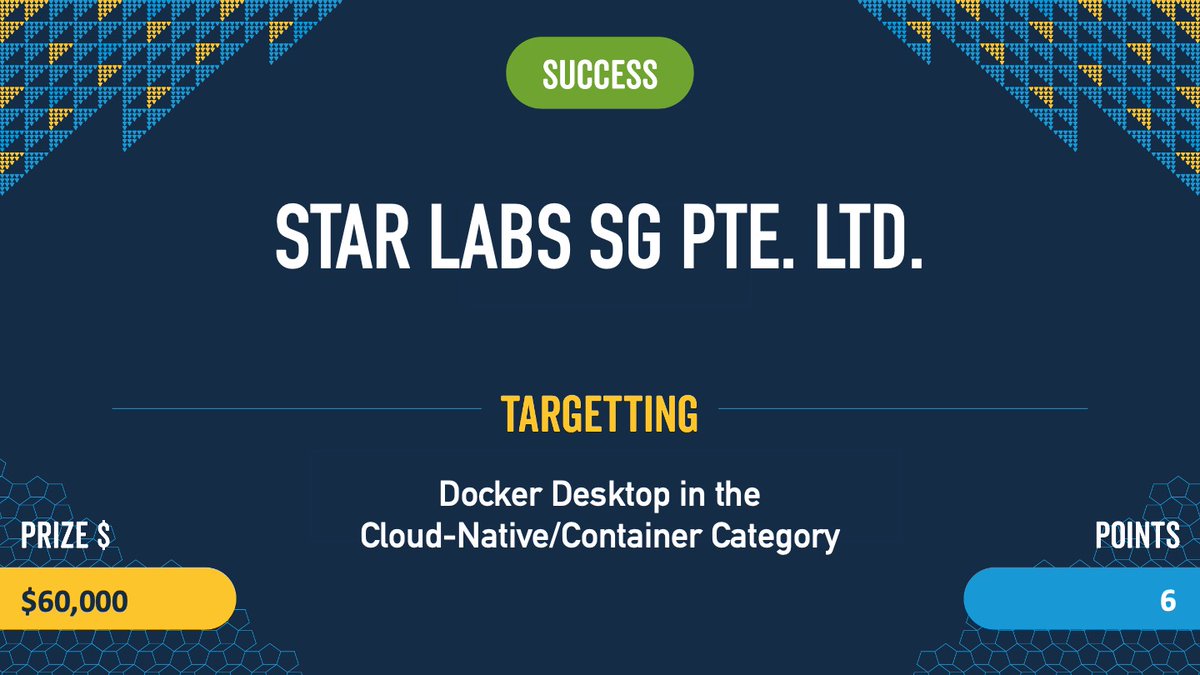

Verified! The first #Docker escape at #Pwn2Own involved two bugs, including a UAF. The team from STAR Labs SG did great work in the demonstration and earned $60,000 and 6 Master of Pwn points. #P2OVancouver