Brad Spengler
8K posts

Brad Spengler
@spendergrsec
President of @opensrcsec, developer of @grsecurity Personal account
Katılım Haziran 2011
4 Takip Edilen6.9K Takipçiler

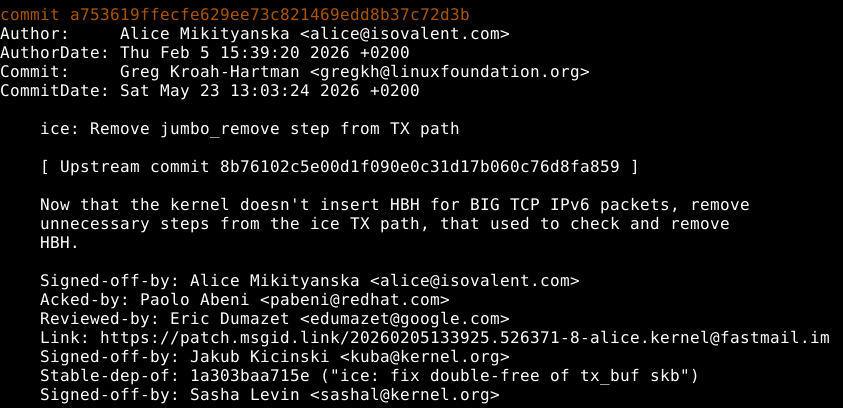
"ALSA: hda/conexant: fix some typos"
Stable-dep-of: b0e2333a2311 ("ALSA: hda/conexant: Fix missing error check for jack detection")
(just fixes some comment typos and renames a misspelled variable name)
kernel.org/doc/Documentat…
English

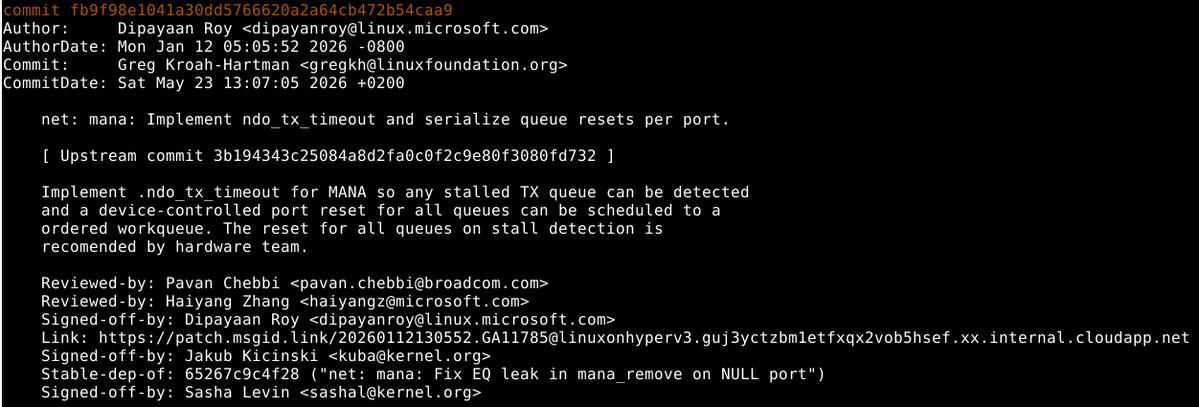
> the patch is well-hidden as a regular commit
paging dr @spendergrsec
itewqq@lyq_sqsp
@rootagi Yeah of course will drop that. But right now OSS is like a dark forest, and the original patch is well-hidden as a regular commit, so we’d rather wait a while (and also someone here is too lazy to prepare the blog lol)
English

Anyway, totally unrelated, was just thinking about the current CVE system where you have exploits coming out weeks before a CVE number or description:
@gregkh/T/#u" target="_blank" rel="nofollow noopener">lore.kernel.org/linux-cve-anno…
@gregkh/T/#u" target="_blank" rel="nofollow noopener">lore.kernel.org/linux-cve-anno…
English