Dawid 🤖 DePINed
898 posts


Dawid 🤖 DePINed
@BitTidy
CMO @depined_org | Full-stack Growth Hacker | Web3 & Crypto Enthusiast | Aspiring AI Engineer


Codex Compute efficient ✅ Always up, never down ✅ Best at hardcore engineering ✅ Crazy good app, first to escape the terminal ✅




As someone who scraped for a living for years, anyone recommending lightpanda to do it shows that they don’t have any experience regarding the subject. Only one thing to understand: TLS Fingerprinting You can have the fastest headless setup, puppeteer, lightpanda,… one wrong ClientHello and Cloudflare/Akamai lights you up instantly. CAPTCHA city. Lightpanda/Zig stuff is fun for tiny sites but gets cooked the second real anti-bot shows up. Cloudflare? Protects 20%+ of all websites on the internet What is a ClientHello? It’s the very first message your browser (or bot) sends during the TLS handshake. It openly announces your TLS version, the list of supported cipher suites, elliptic curves, extensions order, GREASE values, and other data. Anti-bot systems like Cloudflare and Akamai read this instantly and turn it into a fingerprint. If it doesn’t match a real browser’s exact signature… you’re flagged as a bot right away. The key here is simple: real TLS fingerprint spoofing requires low-level control. You can’t do it properly in JS or Python. You need languages like C++ or Rust to actually rewrite the ClientHello, cipher suites, extensions, and all the tiny details that Cloudflare and Akamai check instantly. Anything higher-level just leaves obvious artifacts that scream ‘bot’ What I recommend: Camofox An actual Firefox fork with proper C++ fingerprint spoofing, native TLS behavior, proxy/geo baked in, built so your agents don’t die on protected pages. Top-tier protections might flag it following interaction speed on the pages, ip addresses and other factors but there’s NO match between lightpanda and this "Camofox patches Firefox at the C++ implementation level - navigator.hardwareConcurrency, WebGL renderers, AudioContext, screen geometry, WebRTC are all spoofed" Basically, everything is spoofed BEFORE the JS on the page can even see the values. Which is not possible with python/js libraries. On another note, I talked about it to @Teknium on @NousResearch discord and literally 2 hours later it was implemented in Hermes Agent, it just shows that they take feedback very seriously and want to give the smoothest agent experience they can Level-up your setup right now github.com/jo-inc/camofox…









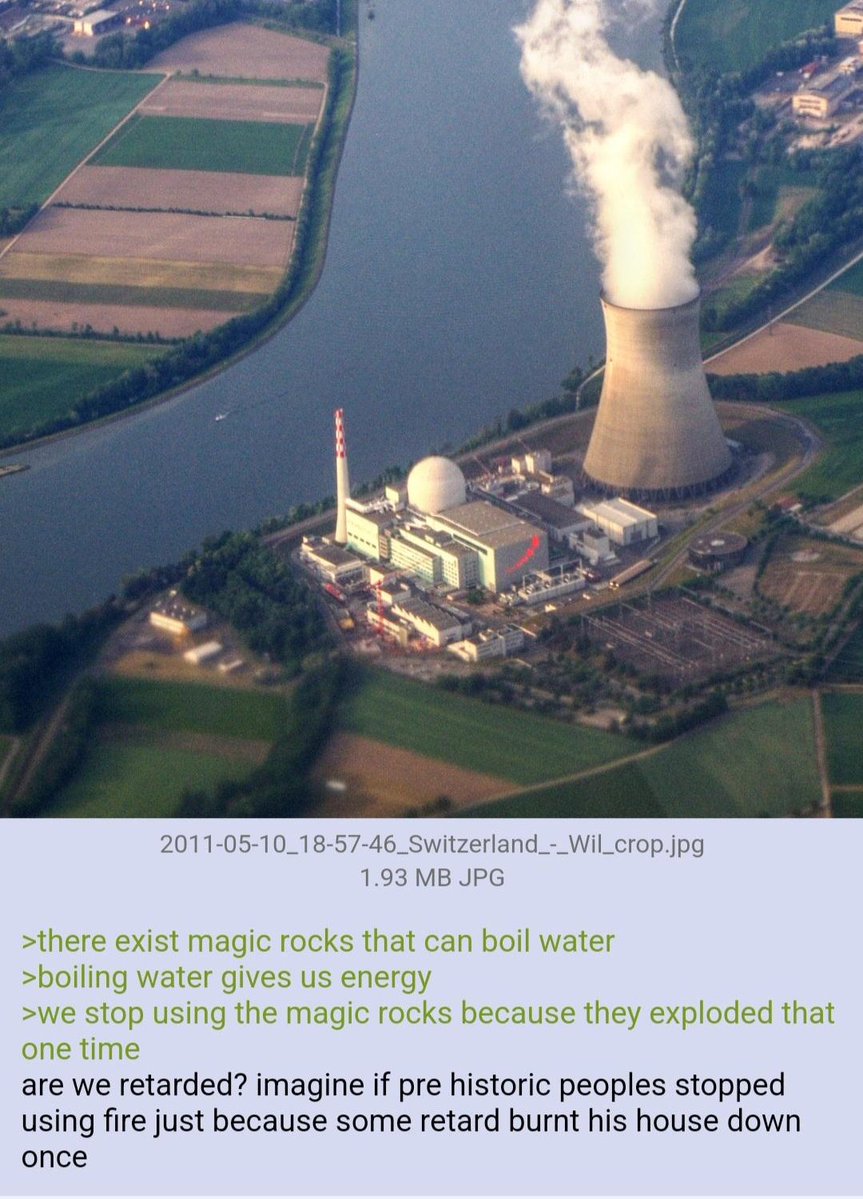
I will never stop being an advocate for nuclear energy Also the 1% would lose their throne of fossil fuels so that’s awesome too lmao






5 minutes ago, @karpathy just dropped karpathy/jobs! he scraped every job in the US economy (342 occupations from BLS), scored each one's AI exposure 0-10 using an LLM, and visualized it as a treemap. if your whole job happens on a screen you're cooked. average score across all jobs is 5.3/10. software devs: 8-9. roofers: 0-1. medical transcriptionists: 10/10 💀 karpathy.ai/jobs