Allison Wikoff
261 posts


Allison Wikoff
@SaltyWikoff
#threatintel Americas Lead @pwc. Hype woman. Beach Rat. Former Adjunct @Columbia. Lover of all the APTs. | All views are my own.

A comprehensive database containing complete registration records of Ravin Academy students has been obtained by me, revealing detailed personal information of individuals enrolled in the organization's training programs. This database constitutes a significant intelligence asset, as it documents the systematic development of personnel for potential recruitment into MOIS cyber operations. The individuals identified in these records represent human resources that Ravin Academy cultivates and directs toward state-sponsored cyber activities targeting Iranian citizens, regional adversaries, and international entities on behalf of the Iranian government. blog.narimangharib.com/posts/2025%2F1…

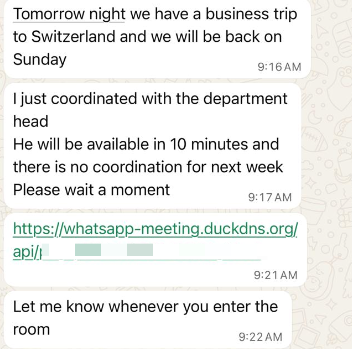
I wanted to do some commentary on the recent CharmingKitten leak, but the data and content seem to be mostly tampered with. Perhaps their future updates might show more, but as is, there's little to cover and makes me the UI playing along. All files have their metadata cleaned up and retouched, and by the few seconds time variance across them, it is possible that it's a much larger stash, taking few seconds to touch everything. On technical side, there's very little to highlight, other than using mostly opportunistic attempts and public PoC tools and exploits to gain access to targets, beside typical phishing campaigns. The irony in their logs and notes? They target a lot of domestic websites and Iranian orgs and companies :) That tells you how unhinged everything is out there in their org. Similar to the leak from few years ago related to OilRig internals, we're seeing heavily filtered and handpicked logs and target names and countries. How to get a better picture? Scan internet for live webshells with matching naming schemes. Detailed time logging and reporting might stand out at first glance, in a positive and interesting way, but it's worth noting that demanding that template mostly comes from deep mistrust between the ranked employers and operators, rather than following some sort of guard railing to monitor for internal policy violation, as it would be more common on the western side. Another noteworthy point one can see through the logs is that this is a team span across multiple locations and buildings, working in parallel. Typically staffed around 15-20, which is similar to dropped names here. At least some of the operators were participating in Ravin Academy's Red-Team classes, which is self explanatory. While Ravin can always take the plausible deniability route and claim they don't know who their students are, as someone closely familiar with that scene and echo system, I'd call that out. On the other hand, Ravin and similar entities are doing legitimate work within context of Iran's laws and in favor of their nation/gov. Training alone, cannot be a reason to question them. Attribution to incidents by overlapping TTPs, coding style and OpSec failures? Sure! Let's see what drops next and whether we will observe something significant. I also asked Gemini to crunch the logs and generate some notes: gist.github.com/Hamid-K/f4288d…

Chinese state-sponsored actors are targeting global telecommunications and other critical infrastructure orgs. We’ve joined others worldwide to call these actors out and publish hunting & mitigation guidance to reduce this ongoing threat. media.defense.gov/2025/Aug/22/20…



Former government officials join "Zero Day" executive producer & @nytimes reporter Michael Schmidt to explore the @netflix series’ chilling reflection of today’s threat landscape. Join us for this #RSAC 2025 Keynote. spr.ly/60132rvIH Thursday, May 1 9:40 AM - 10:30 AM PT






Sometimes I take for granted that on our team we have real-time visibility into hundreds of simultaneous intrusions from every APT & FIN group on the planet. Including many right now from apex threat actors that others wait a lifetime to experience. I look at new intrusion sets every single day as far “left of boom” as you can imagine. The tough part is turning this into meaningful protection at scale, prioritizing within an endless sea of suspicious activity data, and not losing your mind & your creative edge along the way with what it will teach you about the state of the security industry.