Post

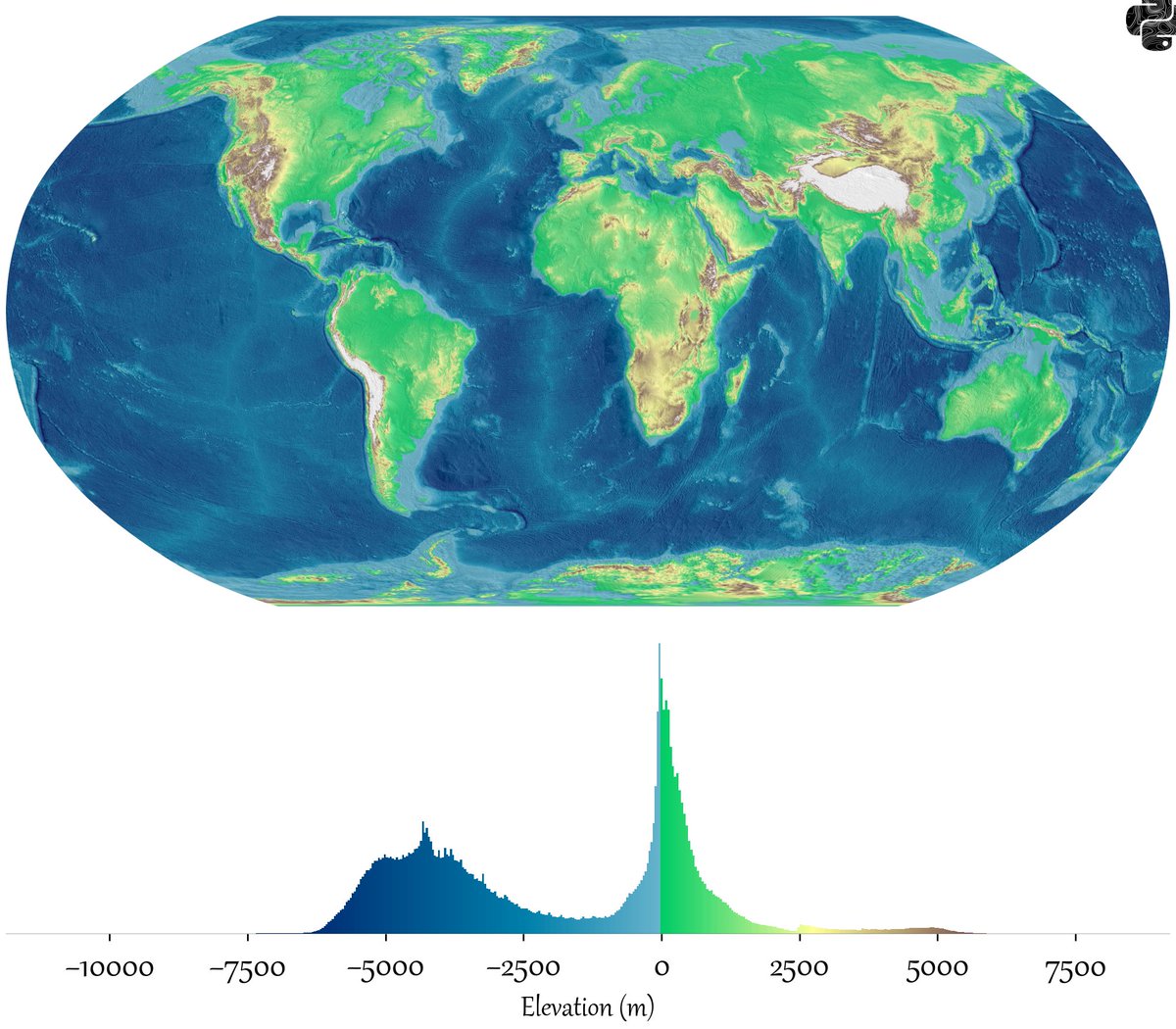
@PythonMaps That the highest point is at sea level...looks suspicious. But the tides and waves at the ocean's edge are great levelers
🌊🏔
English

@PythonMaps Interesting just a small change in the current sea level would result in the largest changes. Reminds me of the pareto principle.
English

@PythonMaps So I really find interesti g thst there are two groups that dominate on is the ocean floor and the other one are continental crust. Notice, the last one is around zero, so just a bit of more water and most of continents would be under water. Funny coincidence
English

@PythonMaps Cool map, but this chart should be in units of ft not m :)
English
@PythonMaps That big highland in the southern part of Africa is likely where modern Homo sapiens originated. Curious.
English

@PythonMaps This is a really interesting chart, but it looks like you've graphed the highest elevations as white on white. As a result the Himalayas etc are invisible on the elevation chart. Try a black background?
English

@PythonMaps Interesting. The bimodal distribution can be explained by there being two types of crust (oceanic and continental) with different densities that thus float at different heights on the denser mantle assthenosphere.
English

@PythonMaps Definitely underwater aliens looking at this bimodal distribution
English

@PythonMaps What projection? If not equal area, must account for that change in pixel area
English

@PythonMaps Yes, we have two types of terrain - continental granite floating (literally) on top of denser basalt.
English

@PythonMaps It’s always wild to see how rugged western North America is.
English

@PythonMaps this is a bimodal distribution so there are external factors at play
English

@PythonMaps Very cool! Crazy that it’s a bimodal or even a trimodal distribution!
English

@PythonMaps Very interesting.
Has anyone made one for the planet in Subnautica?
English

x.com/Ms_Zempel/stat…
It's time to focus seriously on education.
It's worse than you think.
x.com/Ms_Zempel/stat…
School Matters Foundation@Ms_Zempel
English
@PythonMaps The blue part of the chart should be below the X-axis.
English

@PythonMaps Not so round anymore. Would it stay that way if all water evaporated?
English

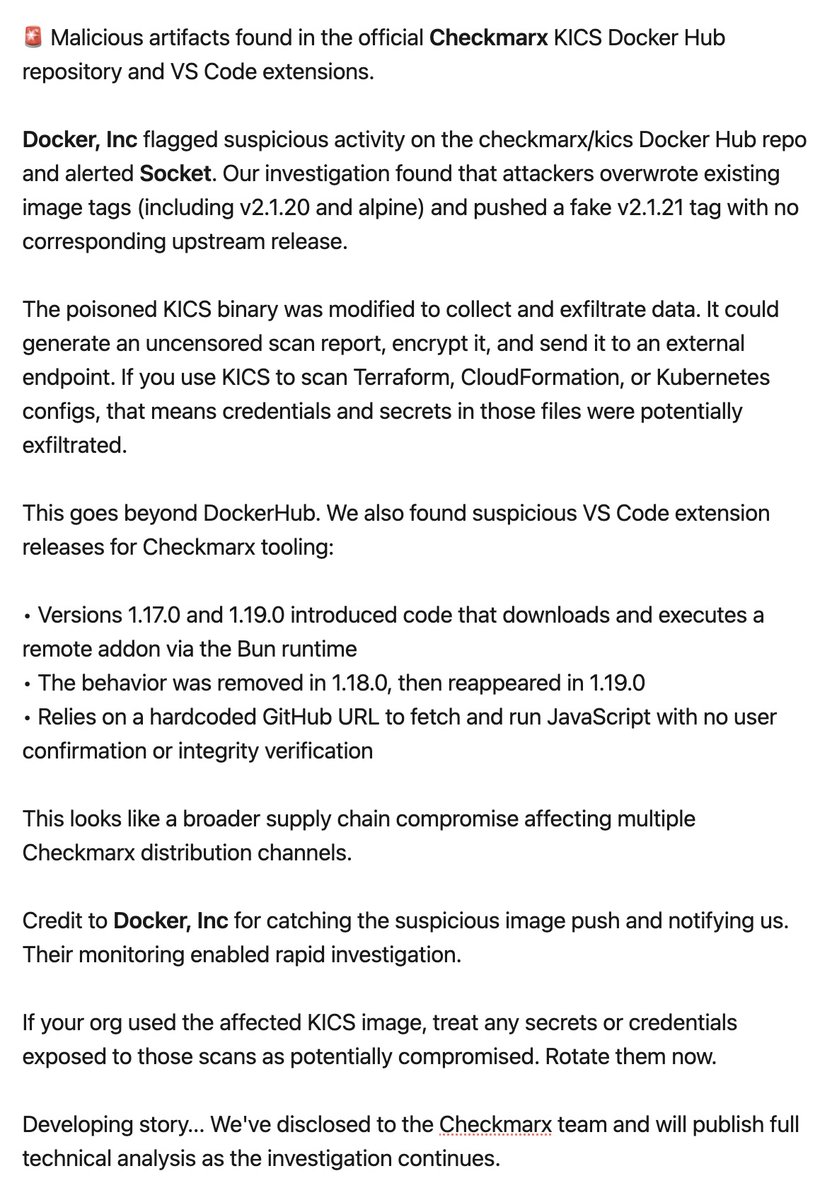
🚨 DEVELOPING STORY: Malicious artifacts found in the official @Checkmarx KICS Docker Hub repository and VS Code extensions.
@Docker flagged suspicious activity on the checkmarx/kics Docker Hub repo and alerted Socket. Our investigation found that attackers overwrote existing image tags (including v2.1.20 and alpine) and pushed a fake v2.1.21 tag with no corresponding upstream release.
The poisoned KICS binary was modified to collect and exfiltrate data. It could generate an uncensored scan report, encrypt it, and send it to an external endpoint. If you use KICS to scan Terraform, CloudFormation, or Kubernetes configs, that means credentials and secrets in those files were potentially exfiltrated.
This goes beyond DockerHub. We also found suspicious VS Code extension releases for Checkmarx tooling:
• Versions 1.17.0 and 1.19.0 introduced code that downloads and executes a remote addon via the Bun runtime
• The behavior was removed in 1.18.0, then reappeared in 1.19.0
• Relies on a hardcoded GitHub URL to fetch and run JavaScript with no user confirmation or integrity verification
This looks like a broader supply chain compromise affecting multiple Checkmarx distribution channels.
Credit to Docker for catching the suspicious image push and notifying us. Their monitoring enabled rapid investigation.
If your org used the affected KICS image, treat any secrets or credentials exposed to those scans as potentially compromised. Rotate them now.
Developing story... We've disclosed to the Checkmarx team and will publish full technical analysis as the investigation continues.
English