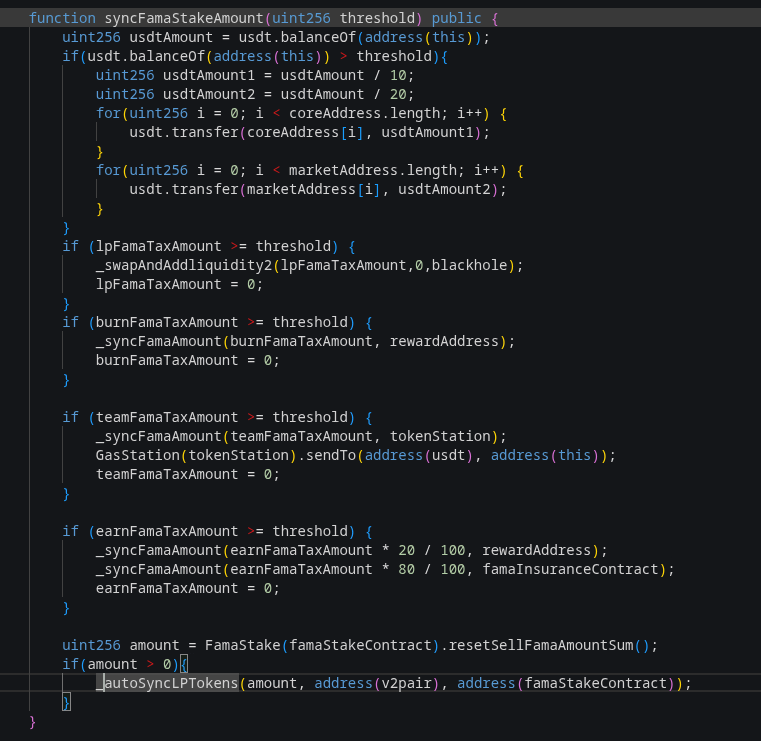
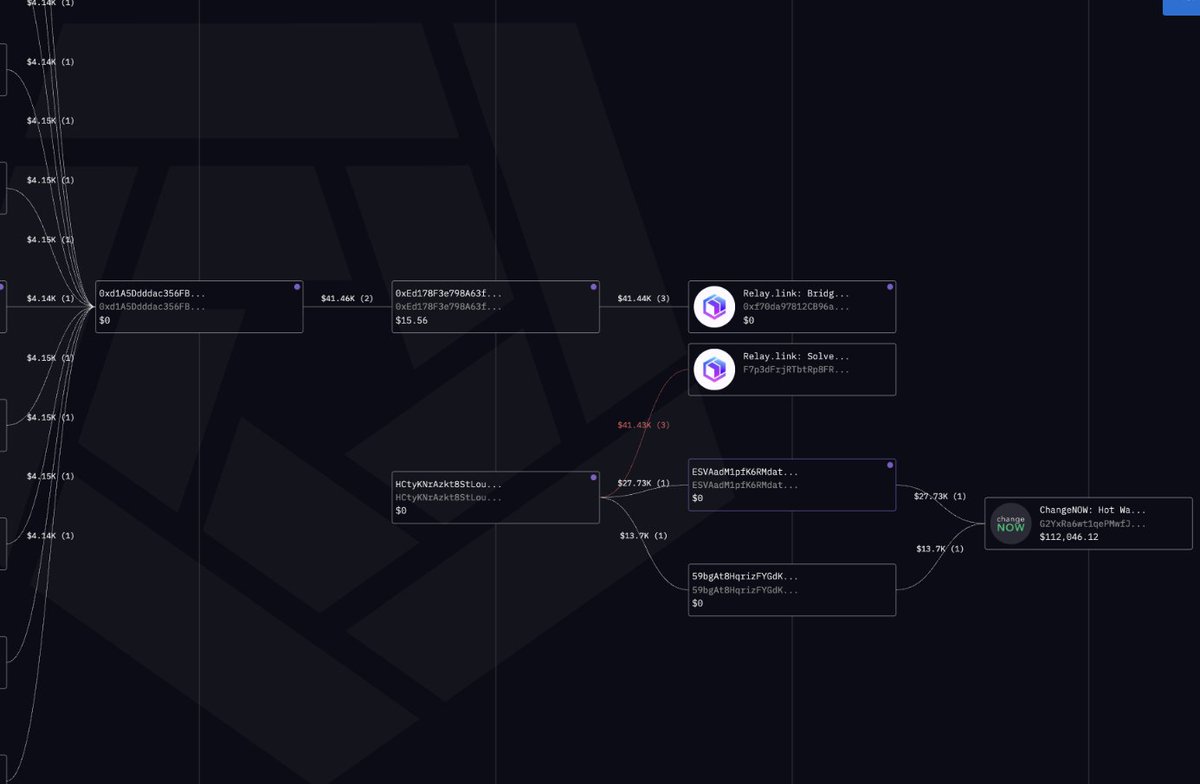
🚨 STO Protocol - Loss $16.1K (2026-02-23) Token: $STO (no CoinGecko listing) MC: Unknown TVL: $5.65K (STO/WBNB pair) Type: Logic Error — Deflationary Sell-Burn Drain The STO token burns sold tokens from the PancakePair on every subsequent sell via \_executePendingSellBurn(), which removes STO from the pair and calls sync() to update reserves. An attacker flash-loaned 360,894 WBNB, then executed 45 repeated sell cycles: each sell accumulated pendingBurnFromSell, and the next sell's \_update burned those tokens from the pair before the new swap, shrinking STO reserves and inflating the WBNB output. This created a compounding drain loop, extracting ~26.57 BNB ($16.1K) of excess WBNB from the pair. The root cause is that \_executePendingSellBurn (STO.sol:313-323) burns pair tokens and syncs reserves mid-swap flow, allowing an attacker to manipulate the AMM price curve within a single transaction. TX: bscscan.com/tx/0x8ba17bea9… Victim: bscscan.com/address/0x7c40… Token: bscscan.com/address/0xfe33…