Numbers
80 posts


Numbers
@Numbers19079000
Crypto Tracer 🤫 For those who come after
Metaverse Katılım Ocak 2023
33 Takip Edilen16 Takipçiler

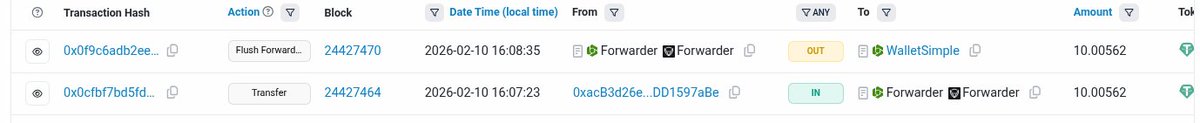
@web3_antivirus did the poisoner convince the user they'd received the 10 USDT test or is that a little something back🫠
English

Here we go again with another address poisoning attack, and this time the loss is $354K in $USDT.
The user copied a scam address from the tx history instead of the correct one, and 354,287 USDT went straight to the attacker since the addresses looked similar.
What makes this worse is how ordinary the wallet activity looked with plain $USDT transfers.

English

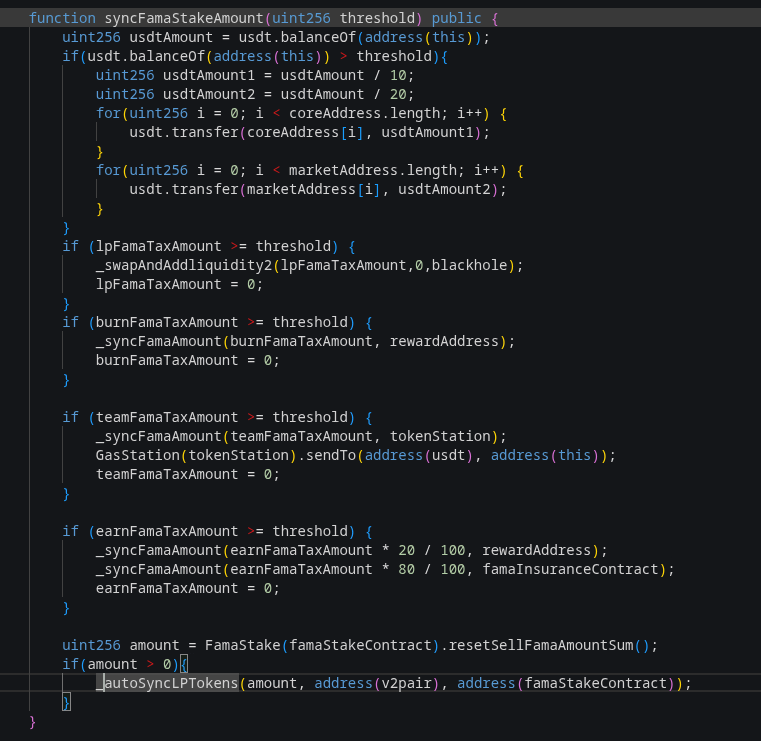
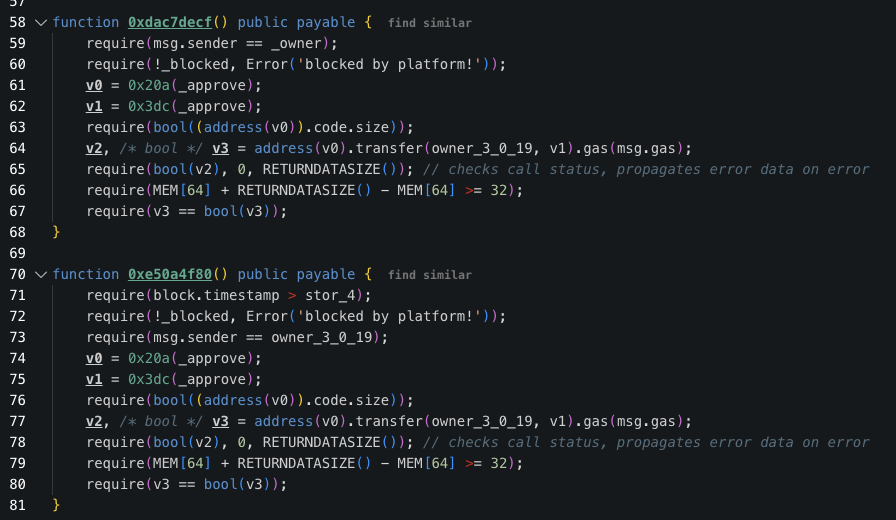
This is linked to a price manipulation exploit on #FAMA token on BSC
The attacker took advantage of the syncFamaStakeAccount() function which can transfer tokens from the pool to the stake contract, inflating the price of FAMA
skylens.certik.com/tx/bsc/0x3f830…
Numbers@Numbers19079000
@RAILGUN_Project $135k stolen funds shielded etherscan.io/tx/0x73cf7f457… Originate from an exploit here bscscan.com/tx/0x3f830b1b3…
English

@RAILGUN_Project same attacker (different wallet) shielded another 11k
etherscan.io/tx/0x20158b052…
English

@RAILGUN_Project
$135k stolen funds shielded etherscan.io/tx/0x73cf7f457…
Originate from an exploit here bscscan.com/tx/0x3f830b1b3…
English

Attacker created their own MCoin/USDT LP which they funded with 1 MCoin and .00000001 USDT
When conducting an MCoin -> AI Pay token buy the function chose the attacker's LP as the best route and sent MCoin to it which they removed after.
They basically gained free AI Pay
TenArmorAlert@TenArmorAlert
🚨TenArmor Security Alert🚨 Our system has detected a suspicious attack involving #AiPay and #MCoin tokens on #BSC, resulting in an approximately loss of $30.1K. Attack transaction: bscscan.com/tx/0xa268528df… With TenArmor’s TenMonitor, you get early detection and automated response to on-chain attacks. Need protection? Reach out anytime! #TenArmorAlert #TenArmor
English

On January 16, 2025, at 21:15 UTC, a victim lost $6.7M due to a private key compromise.
The stolen funds were swapped into ETH. Of this amount, 1,899 ETH was bridged to the Bitcoin network and deposited into the Wasabi mixer, while the remaining 159 ETH was deposited into Tornado Cash.
Theft addresses
0x6509Cac8d378765dD2612705De25Fb06207dd4d8
0x376874A97Db6022cA5Eb9194EF164Da37936E229
0xB49eeb5DbED66C02e90A5084C6AAA0A891A95Ad8
0x88c46f87127e7455f2dc5e5B20A628e3695dF020
bc1qwqjuszqqk9p73eqcxn07t2teqt2pdgxquumwqk
While the attacker moved quickly to launder the stolen funds, partial recovery may have been possible if the incident had been reported immediately.
If you observe any suspicious activity on your wallet, report it as soon as possible to blockchain investigators or security professionals
A common mistake is contacting law enforcement first instead of investigators, in most cases, it's zero at least for that period
Stay smart.

English

@officer_secret @zachxbt Its not a traditional click and drain, funds were moved using transfer()
This 'victim' wallet hasn't even been used since 2021
etherscan.io/address/0x0d39…
so unless they found something holding PK or seed phrases 🤷♀️
English

. @zachxbt : It appears hundreds of wallets are currently being drained on various EVM chains for small amounts (<$2k total per victim) with a root cause not yet unidentified.
So far ~$107K has been drained from them with the theft total still increasing.
Suspicious address
0xAc2e5153170278e24667a580baEa056ad8Bf9bFB

English

@rugpullfinder could be innocent 👀
BUT
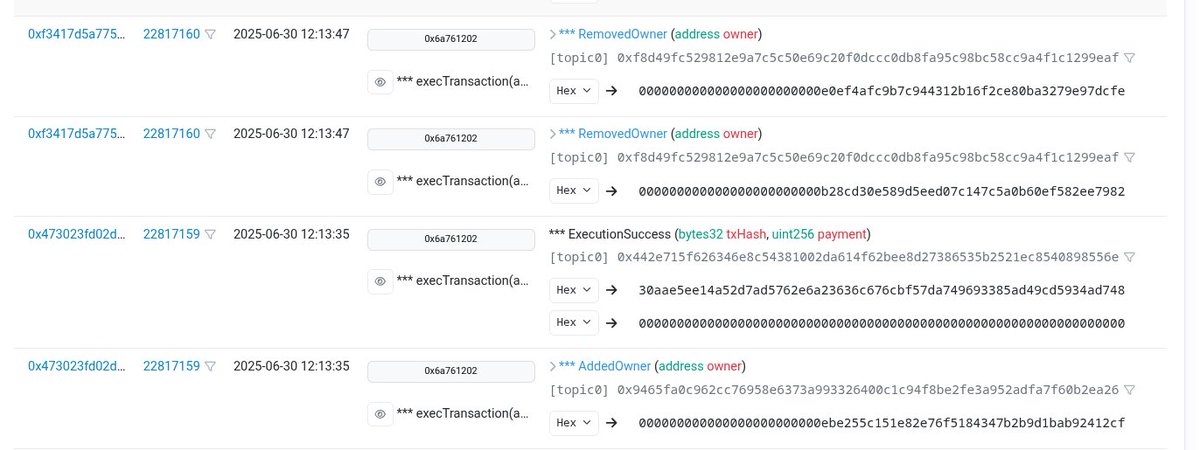
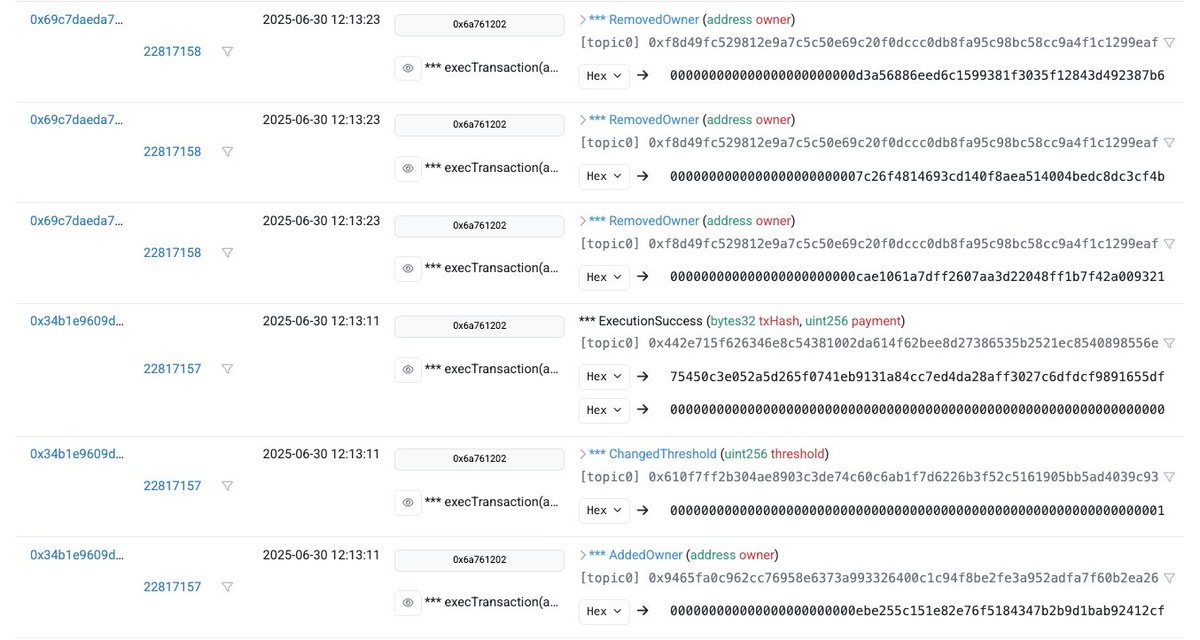
Swarm multisig changed owner -> revoked previous owners -> transferred $1M -> deposited to TC
Happened on more than one of their multisigs
#events" target="_blank" rel="nofollow noopener">etherscan.io/address/0x9BC9…
English

@rugpullfinder @blockdagnetwork @zachxbt think he did yeah.
This looks more like a cover up than a rug (or designed to look that way) but no one talked about it
etherscan.io/address/0xebe2…
1 of Swarm multisigs with similar activity before Tornado deposits
#events" target="_blank" rel="nofollow noopener">etherscan.io/address/0xd98a…
English

@rugpullfinder id be surprised if @blockdagnetwork didn't rug or 'fail'
Over a year in presale + random presale discounts and double ups
CEO and owner is not Antony as they state
False promises
English

hey @serpinxbt here I am requesting 69 ETH to cover the gas fees :)
yo @apoorveth I need a lifetime subscription for the Impersonator tool. Otherwise, I will delete the review.
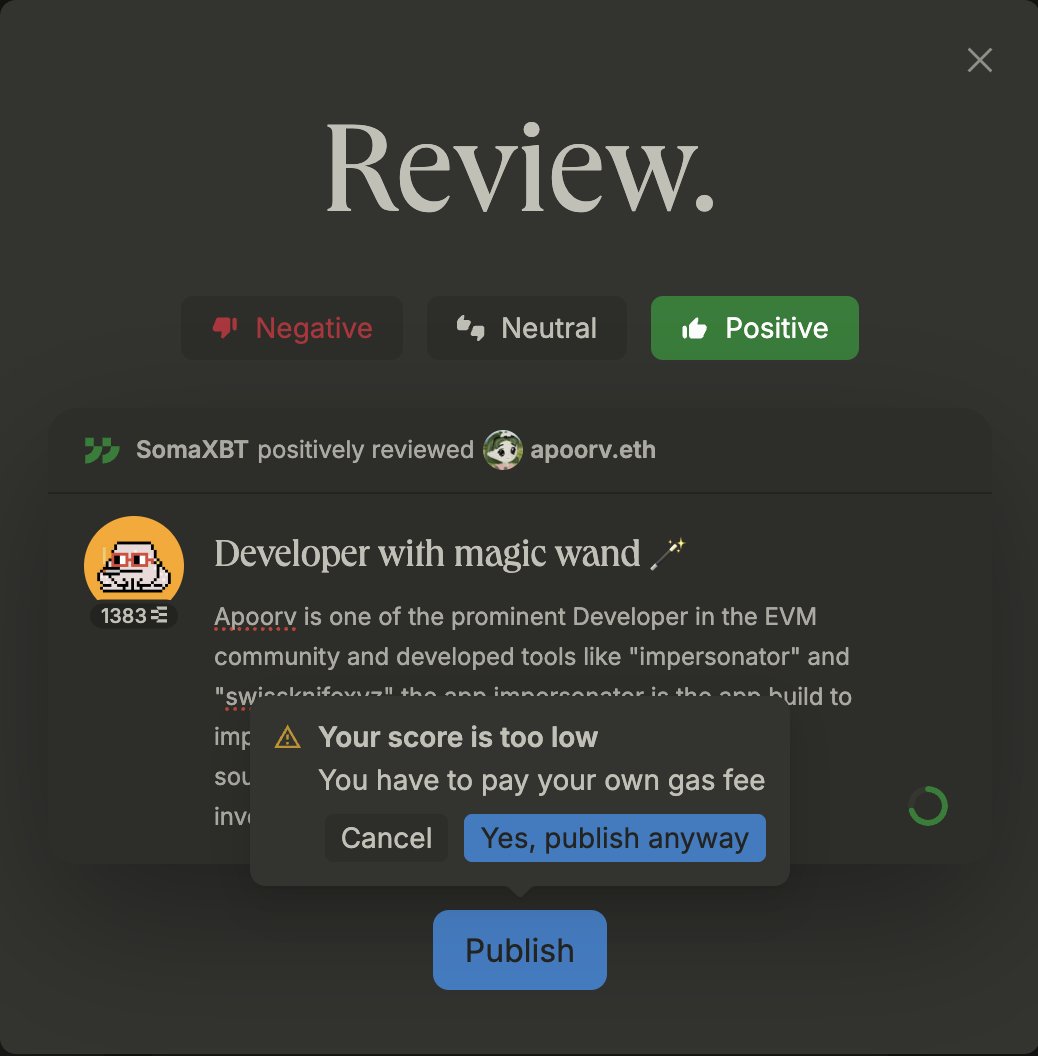
English

@bbbb technically no?
t.me/OfficialBabyXR…
added about as much bscscan.com/tx/0x3bb578104…
though they did have a backdoor to avoid that 2099 lock
English

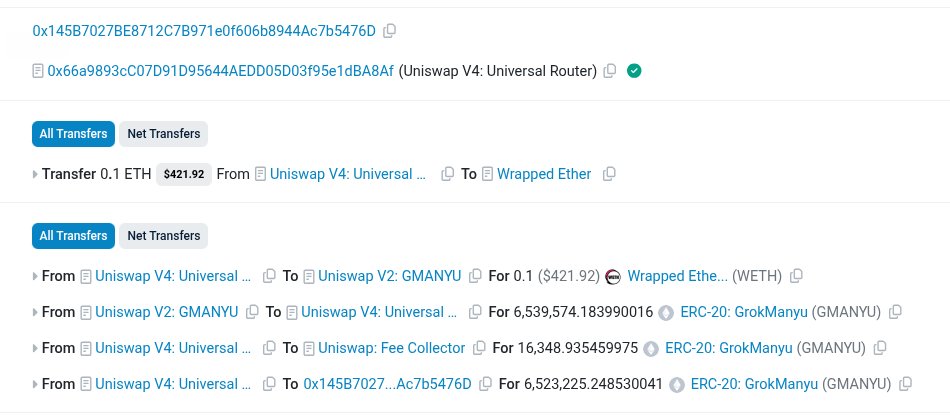
~$60k rugpull by the Grok Manyu team
contract address added as 'monetaryPolicy'
etherscan.io/tx/0x34102ebaa…
Rebase token which required monetaryPolicy role
etherscan.io/tx/0x227fd7f0a…
When they rebase it reduced the total supply allowing them to sell tokens for a higher price

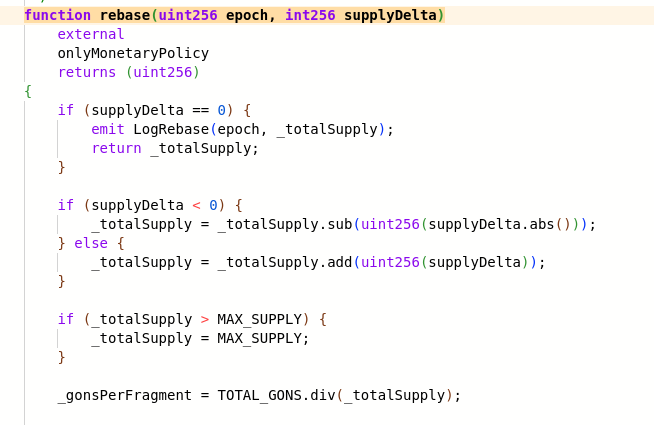
English

@dd3_cs yeah its insane. I don't know a huge amount about MEV but its not unusual to see fees that are far higher than profit
This is a good read mteam.space/posts/im-new-t…
English

@Numbers19079000 is that the standard bribe to get a bundle included in a block? kinda high lol
English

The problem is the amountOutMinimum (the minimum number of tokens you would accept for the trade) was set to zero, so the user expects at least zero USDT for their USDC

Ozymandias@Ozy_mandia
@lynk0x how ?
English