Tyler Doussan
19.9K posts


@Nebula_Matrix
I enjoy building ecosystems that provide utility to the partnership matrix being established within my network—@Champ_io, @ChampLedger_io 🎮🤝












It can always get worse, Anon. Heed these warnings. Resist as much as possible. This is bipartisan. Everyone deserves their right to privacy. Whether you want to say F ICE or call your homie a homo online — whatever side you’re on, you must fight this. Pay attention.



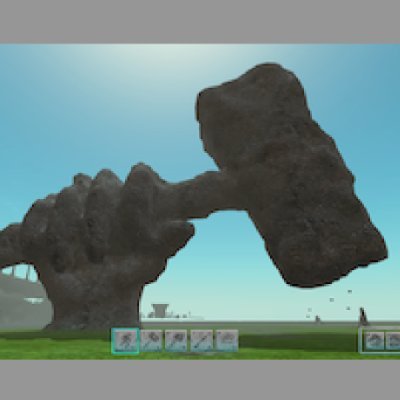

A lost temple has surfaced beneath Notus' dunes. Inside? The Sands of Time. It can restore cities, revive the fallen, and rewrite fate itself. But it all comes at a cost of blood. The gods are watching as the Priests of Khemet and the last Iskandrians march to war to claim the sands. Notus will never be the same. Berserk: Sands of Time begins soon.