Aakash Gupta@aakashgupta
North Korean intelligence agents built an entire fake company to compromise one JavaScript developer. And it worked.
UNC1069 didn't hack Axios. They befriended its maintainer. They cloned a real company founder's identity, built a branded Slack workspace with fake employee profiles and LinkedIn post channels, then scheduled a Microsoft Teams call with what appeared to be a full team. During the call, a fake error message said his system needed an update. He installed it. That update was the RAT.
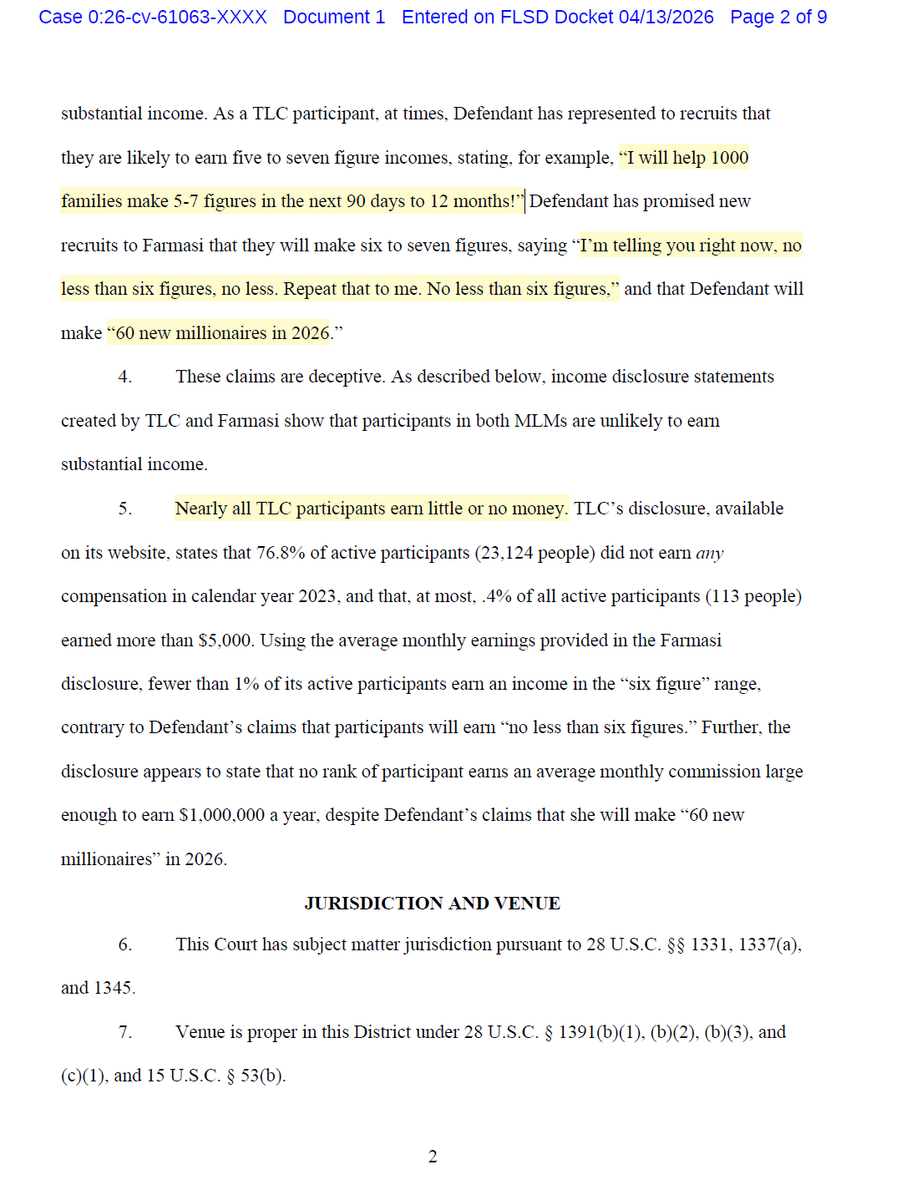
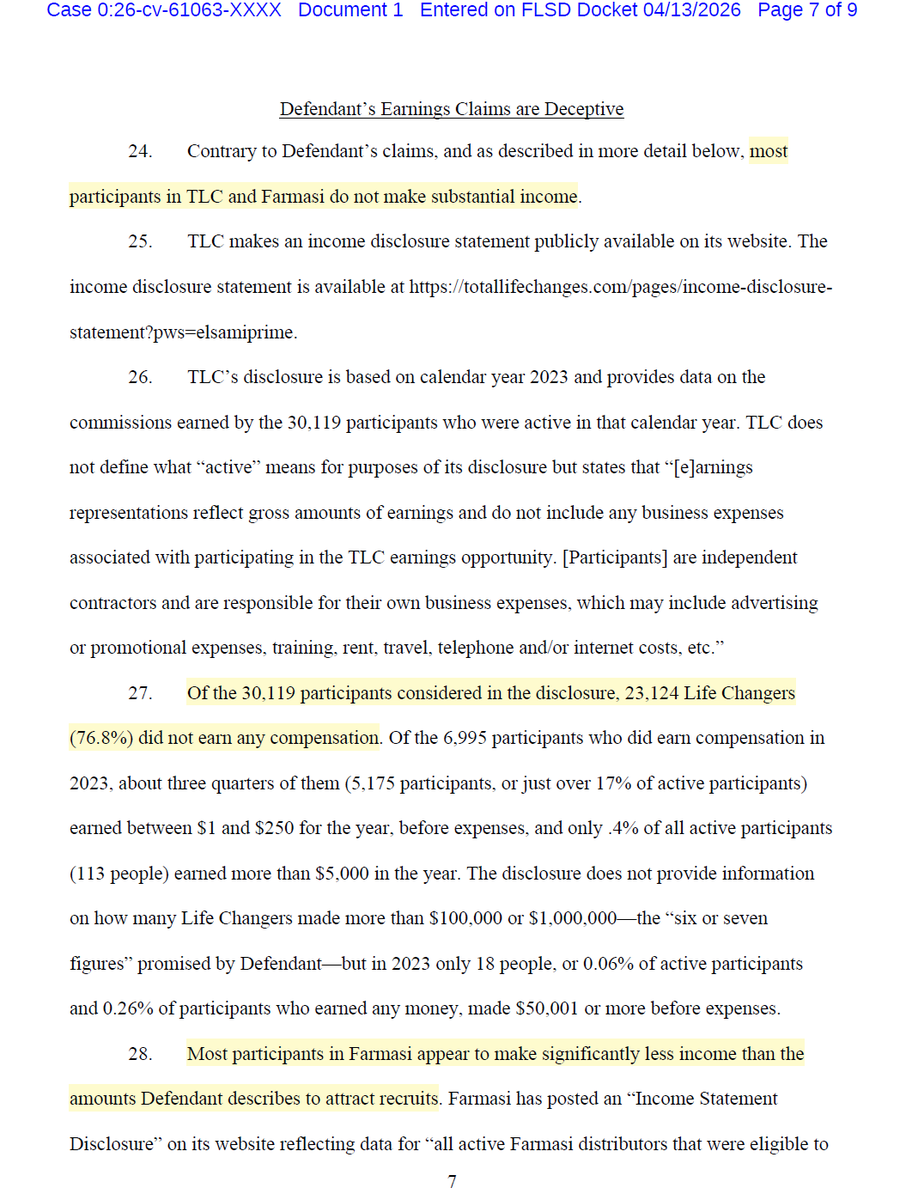
From one developer's laptop, they had everything: npm credentials, publishing access, the keys to a package installed in 80% of cloud environments. Axios gets 100 million downloads per week. The attackers published two poisoned versions at 12:21 AM UTC on a Sunday night, tagging both the latest and legacy branches within 39 minutes. The malicious dependency had been pre-staged 18 hours earlier with a clean decoy version to build registry history. Three separate RAT payloads were pre-built for macOS, Windows, and Linux. The malware self-deleted after execution to erase forensic evidence.
The poisoned versions were live for about three hours before npm pulled them. Huntress observed 135 endpoints across all operating systems calling the attacker's command-and-control server during that window. Wiz found the malicious versions in roughly 3% of environments scanned. Every affected machine needs full credential rotation: npm tokens, AWS keys, SSH keys, CI/CD secrets, everything in .env files.
The part that keeps getting worse: this isn't isolated. The same threat cluster compromised Trivy (a security scanner), KICS, LiteLLM, and multiple GitHub Actions in the two weeks before Axios. Google estimates hundreds of thousands of stolen secrets are now circulating from these combined attacks. The maintainer had 2FA enabled. He said himself: "I have 2FA/MFA on practically everything." The exact method of token compromise is still undetermined.
One person. One fake Teams call. 100 million weekly downloads weaponized in under three hours. The npm ecosystem runs on mass trust in individual maintainers who volunteer their time, and North Korean intelligence now has a repeatable playbook for turning that trust into a delivery mechanism.