bob
180 posts



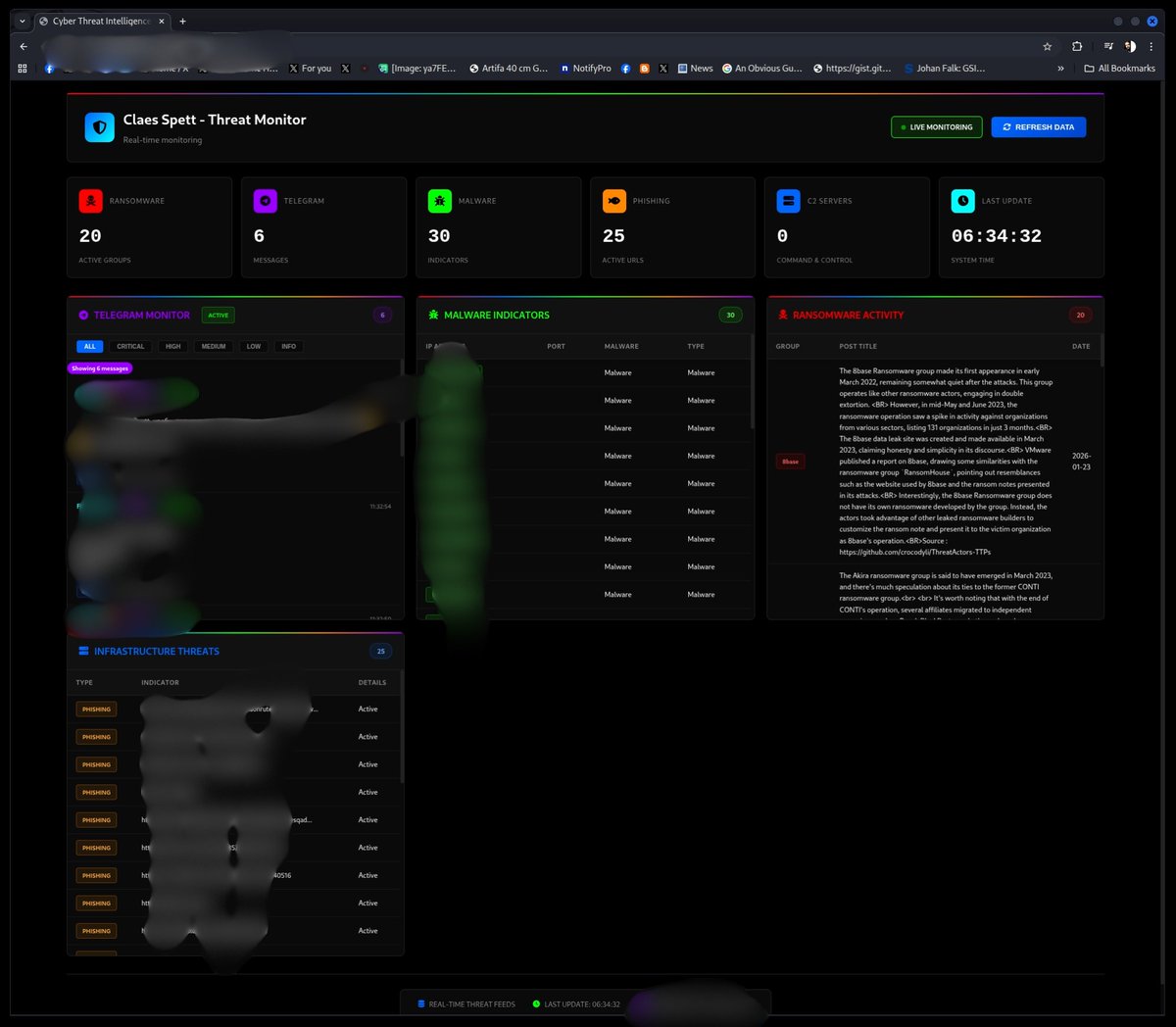
Today @BleepinComputer published a story on a company named Telus Digital being compromised by a Threat Group operating under the moniker "ShinyHunters', a reference to Pokemon. GTIG (Google Threat Intelligence Group) has been tracking ShinyHunters under the label UNC6395. UNC6395 has been targeting enterprise organizations since at least August, 2025 by exploiting compromised OAuth tokens to gain access to company SalesForce instances. Upon successful compromise, UNC6395 attempts vertical or horizontal movement by combing through the compromised SalesForce data. At a currently unknown time, UNC6395 successfully compromised Telus' SalesForce instance which allowed them to pivot elsewhere within the organization. The amount of data UNC6395 claims to have compromised is astronomical. They claim to have exfiltrated over ONE PETABYTE of data (compressed as .tar.xz). While Telus has confirmed the compromise, the exfiltration of ONE PETABYTE of data indicates the compromise may have occurred weeks, possibly months, ago. Telus as of this writing has not given additional details on the compromise (more on that later). I am unable to confirm the validity of the data, primarily because I do have the means to reliably comb through a petabyte of data. However, "snippets" and "samples" have been shared. Based off data seen, the compromised appears authentic. Here is a high-level overview of what was allegedly compromised and successfully exfiltrated. - Employee Full Legal Name - Employee National ID Number and/or SSN - Telus hashed passwords, API keys, OAuth tokens - Call record details - Call meta data - Telecom customer PII (First Name, Last Name, Address) - HR records - Agent performance records - SalesForce accounts, contacts, leads, and records - Financial records (ACH routing numbers, etc) - GitHub repository access to an additional 20 organizations adjacent to Telus (20,000 internal source code projects) - Customer and Agent call records in .wav - 14,139 customer database instances, all containing customer PII (unspecified) - GLEAN TELUS background check files. UNC6395 has access to FBI, RCMP, and CISA background checks. - GLEAN TELUS confidential reports on investigations - GLEAN TELUS confidential reports on tax filings (?) - ... just search "GLEAN" on Google If what UNC6395 states is true, this breach impacts approx. 230M companies across the globe. Based on information seen publicly, ... it looks bad. However, as of this writing, Telus has not done anything other than confirm the compromise with some journalists. I suspect they're currently performing a DFIR (Digital Forensics and Incident Response) and forming a strategy to combat this technologically, legally, logistically, and PR-wise. Is UNC6395 telling the truth? Is this compromise as severe as it appears to be? When will TELUS provide more details? Will impacted customers be notified? Is law enforcement mad their background checks are allegedly compromised? Find out next time on Dragon Ball Z



🚨🔴 Scanner son visage pour accéder à un service sera la norme dans quelques temps ! Dès mars prochain, par défaut, Discord exigera votre pièce d'identité ou scanner votre visage 🤷🏾♂️ Je rappelle quand même que Discord s'est aussi fait pirater au passage... *Bon, je commence à activer mon plan "no-way-out" Ce monde de tout numérique devient fou... bien loin de la philosophie d l'internet des années 70... Courage, RÉSISTONS !



Nous apportons tout notre soutien à Mila, injustement diffamée. Nous n'approuvons pas l'humour noir sur la Shoah et le relativisme qu'il implique. Néanmoins @milafique a toujours été une amie des Juifs et d'Israël, l'accuser d'antisémitisme sur la base d'un mensonge est abject.




🚨🔴 ALERTE | Fédération Française de Volley 🇫🇷 : 26,5 Go de données – +1,2 million de lignes – CNI, photos, actes de naissance et documents signés exposés ⤵️ Une nouvelle fédération sportive piratée. La Fédération Française de Volley est victime d’une cyberattaque majeure. Une base de données interne de 26,5 Go, totalisant plus de 1,2 million de lignes, contenant des cartes nationales d’identité, photos personnelles, actes de naissance, documents signés, ainsi que des noms, prénoms, adresses e-mail, numéros de téléphone et données de localisation (région, ville, code postal), est actuellement mise en vente. ⚠️ Données compromises : • Noms et prénoms • Adresses e-mail • Numéros de téléphone • Secteur d’activité • Région, ville, code postal • Cartes nationales d’identité (CNI) • Photos personnelles • Actes de naissance • Documents signés et administratifs 🚨 Risques majeurs : • Usurpation d’identité • Fraudes documentaires • Phishing et escroqueries ciblées • Chantage et extorsion • Exploitation de profils sensibles • Atteinte grave à la vie privée







🚨ALERTE INFO Les « Black Panthers » se mobilisent et se préparent à défendre leur communauté contre les agressions de l’ICE.