sudo rm -rf --no-preserve-root /@pcaversaccio
recently we've started to observe that the DPRK threat actor PolinRider (related to the Contagious Interview guys) is poisoning hundreds of old GitHub repos with "old-looking" but malicious commits that were actually pushed _recently_. i think what is happening overall is the following:
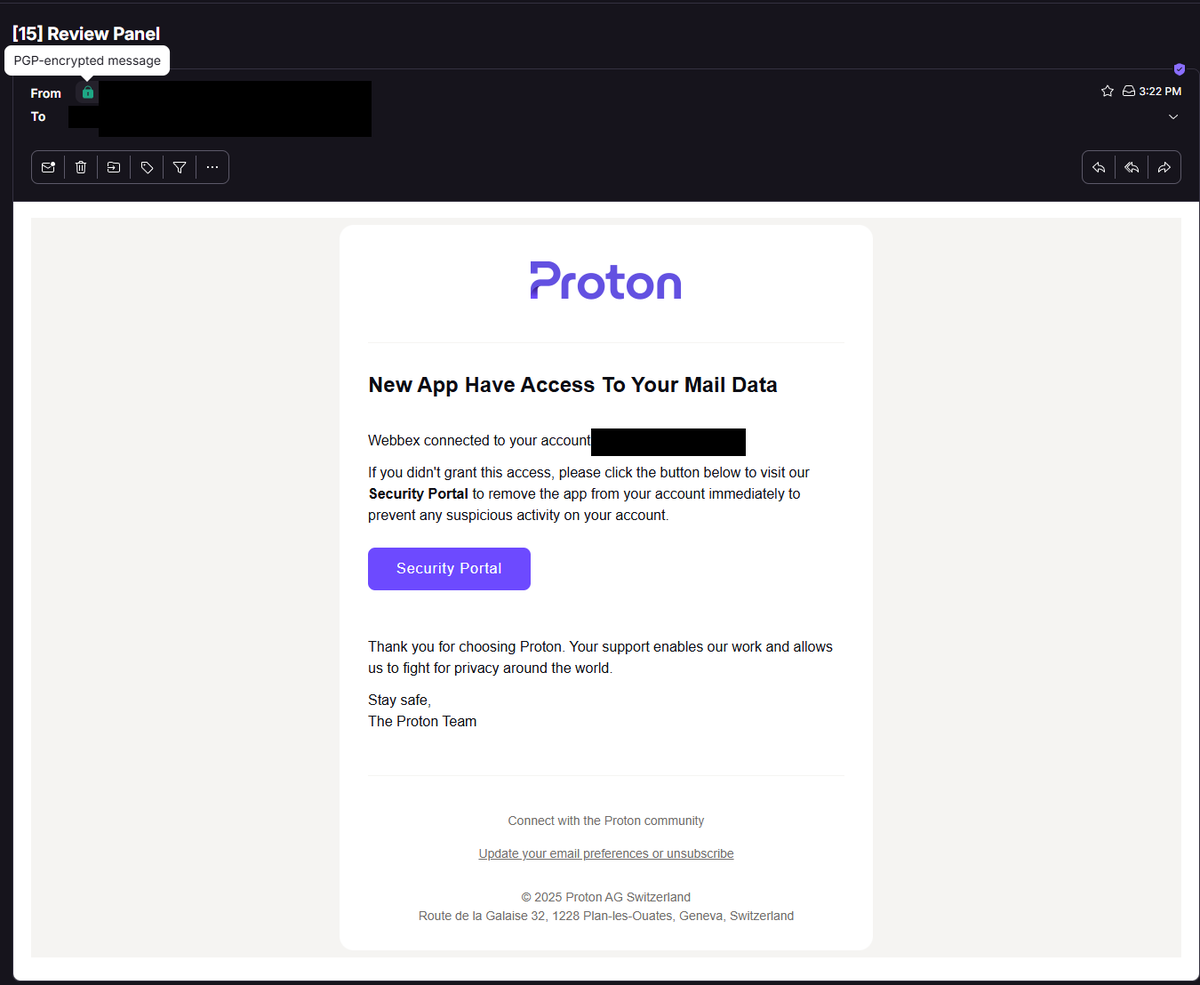
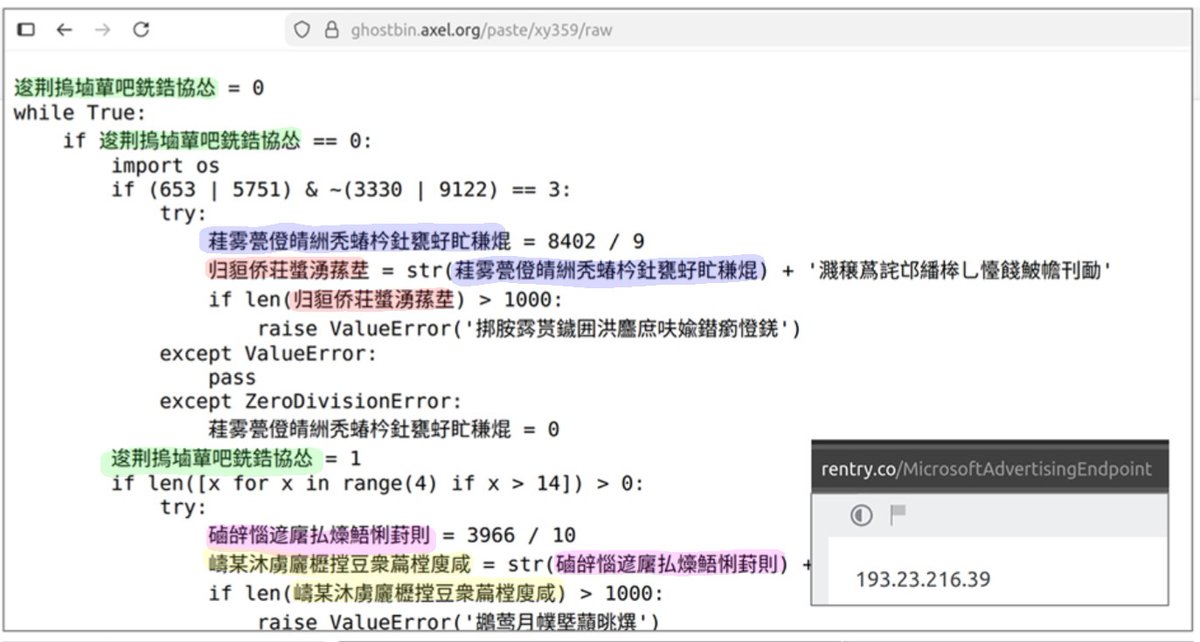
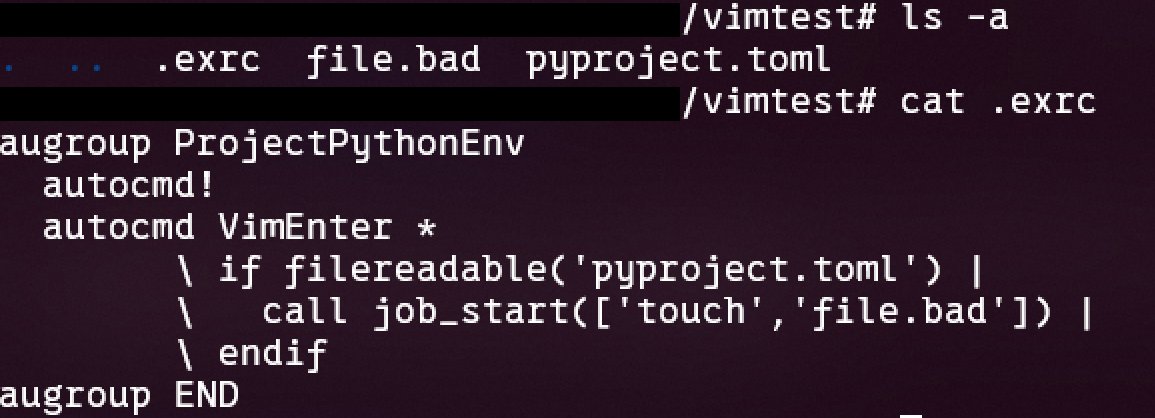
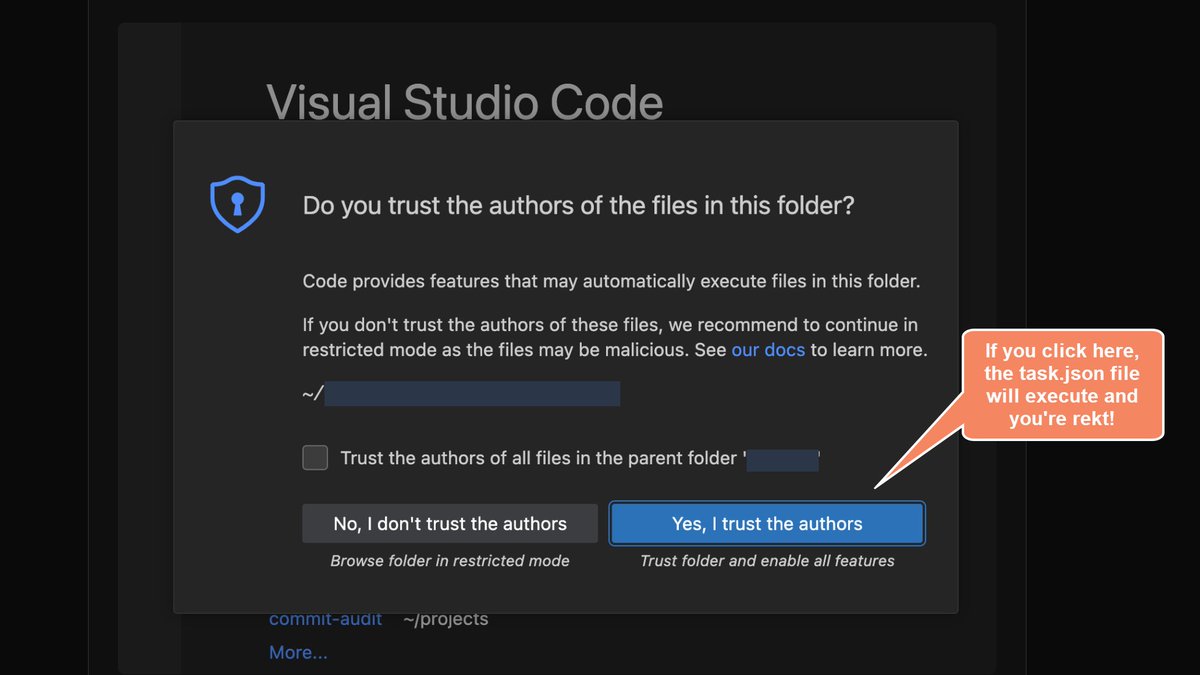
1. devs get compromised via some automatic VS Code task (see e.g. x.com/pcaversaccio/s…), fake npm package (axios is used as an illustrative example: github.com/axios/axios/is…), or similar infostealer vector (this is the current assumption, i do not yet have hard evidence on the exact initial access method)
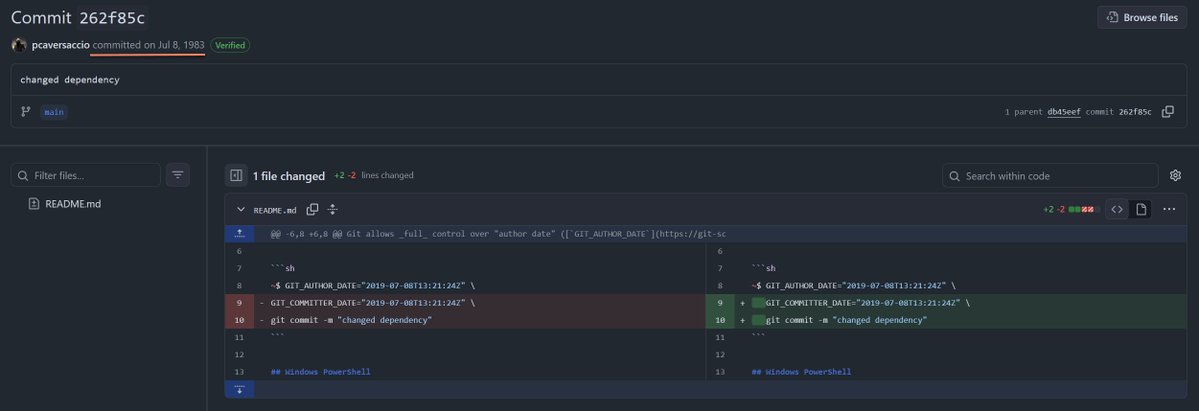
2. the attacker then sets the author and committer dates to match the date of the last legitimate commit in the repository
3. the infostealer malware takes the last commit, amends it with malicious changes, and (force) pushes it back to the repository (likely also using `--no-verify`), making the modification appear as if it belongs to the original timeline
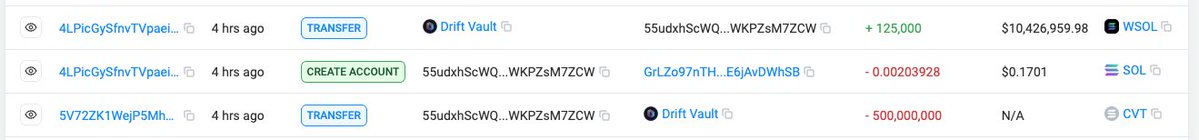
4. the repos are after shilled to other devs or used as part of future fake interview tasks
it's not new news that you can spoof the author and committer date, but i made a short demo repo for anyone to understand how this works: github.com/pcaversaccio/t…
a s/o to @KL4R10N for sharing intel & running forensics on it with me