kubilavax Integrated (🦍⚡️)
13.5K posts


kubilavax Integrated (🦍⚡️)
@avaxcrypto
Web3 | @SentientAGI @RialoHQ @liquidtrading

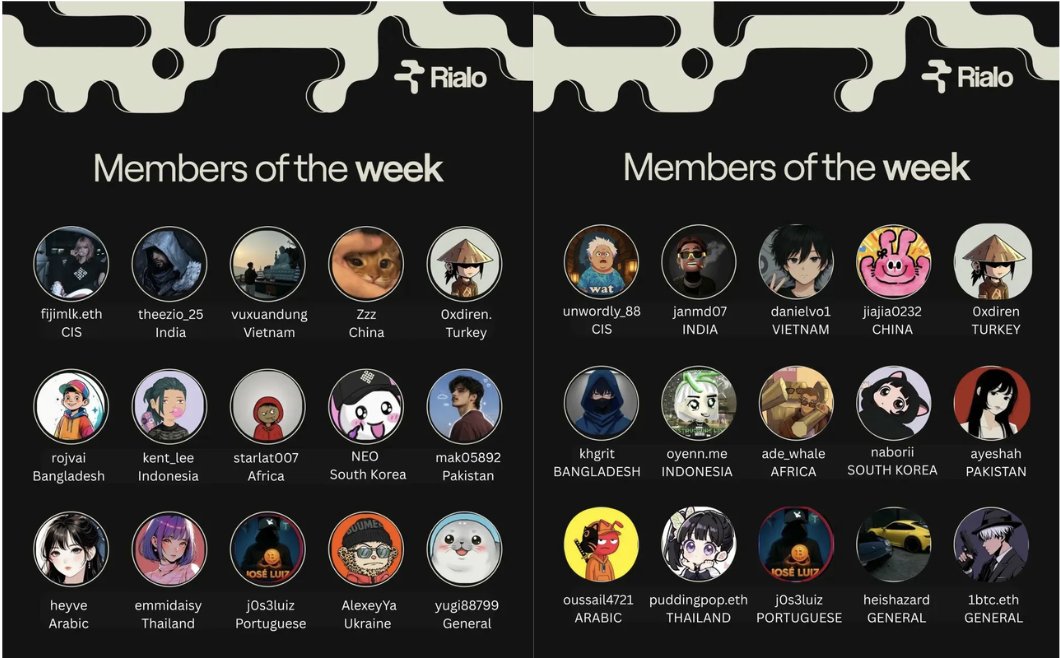
Congratulations to all members of the week well deserved, every single one of you. I am a member of the week. 5th time overall. Spending time with the Rialo family and contributing to this community never gets old. I am @RialoHQ . Are you ?





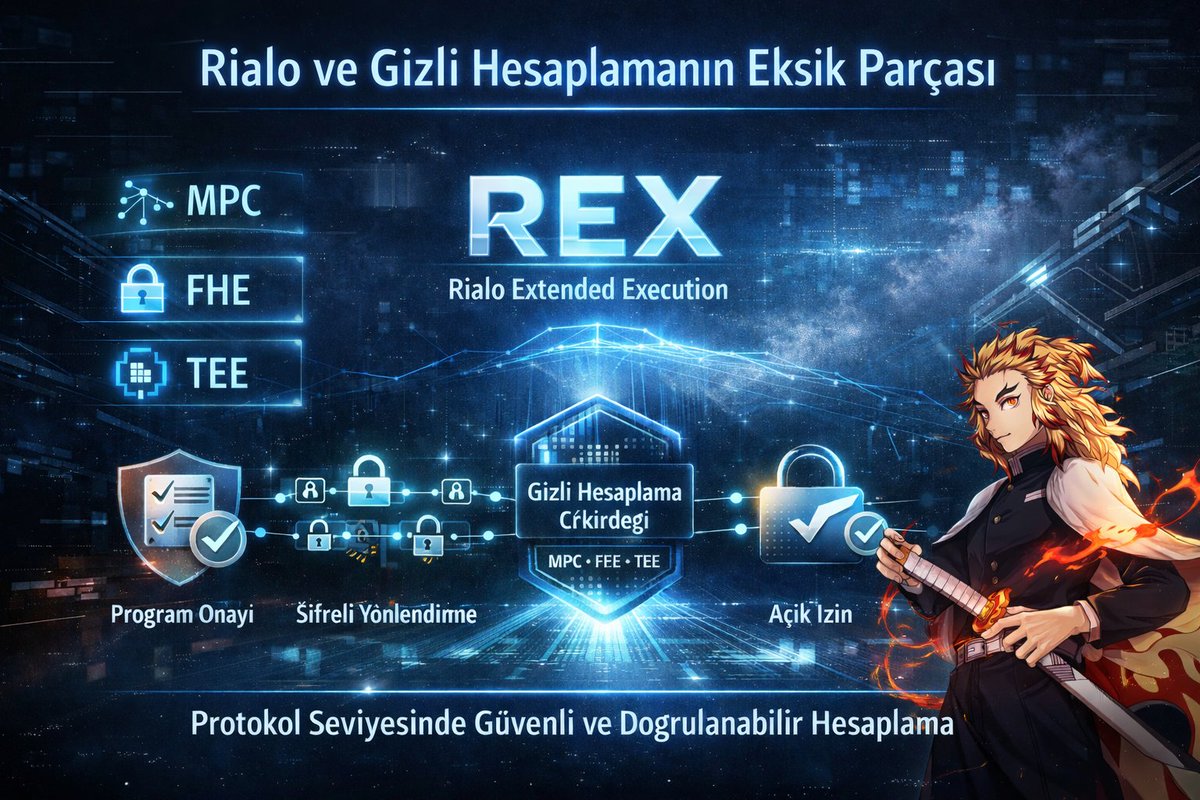
MPC. FHE. TEEs. All powerful on their own, but none solve the coordination problem. The hard part isn’t just encrypting computation; it’s the orchestration required to make it functional and secure. That’s what Rialo Extended Execution (REX) does. REX is a protocol-level orchestration system for confidential computation that manages the entire lifecycle of a secure request: Program Governance – Programs to be executed are verified and approved for specific execution runs before they ever touch the core. Encrypted Routing – Encrypted inputs are routed cryptographically to a computation core only after the appropriate program logic is loaded. Explicit Consent – Computation is performed only after explicit authorization from both the application and the user, enforced by strict policy. Confidential Compute Core – Secure execution using MPC, FHE, or TEEs, including protected Web2 API calls within an isolated environment. Verifiable Outputs – The system generates and verifies cryptographic attestations that prove a specific computation was correctly executed before routing the result to its destination. REX transforms Rialo into infrastructure for real-world secure computation: Private AI agents that process personal data without seeing it. Sensitive enterprise workflows that maintain competitive secrecy. Authenticated API automation for secure, off-chain interactions. Verifiable off-chain compute with immutable on-chain guarantees. This is native privacy at the protocol layer. Get Real. Get Rialo.

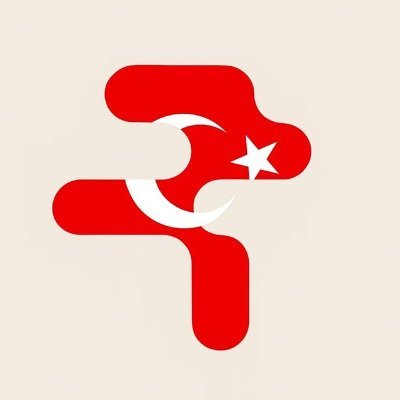
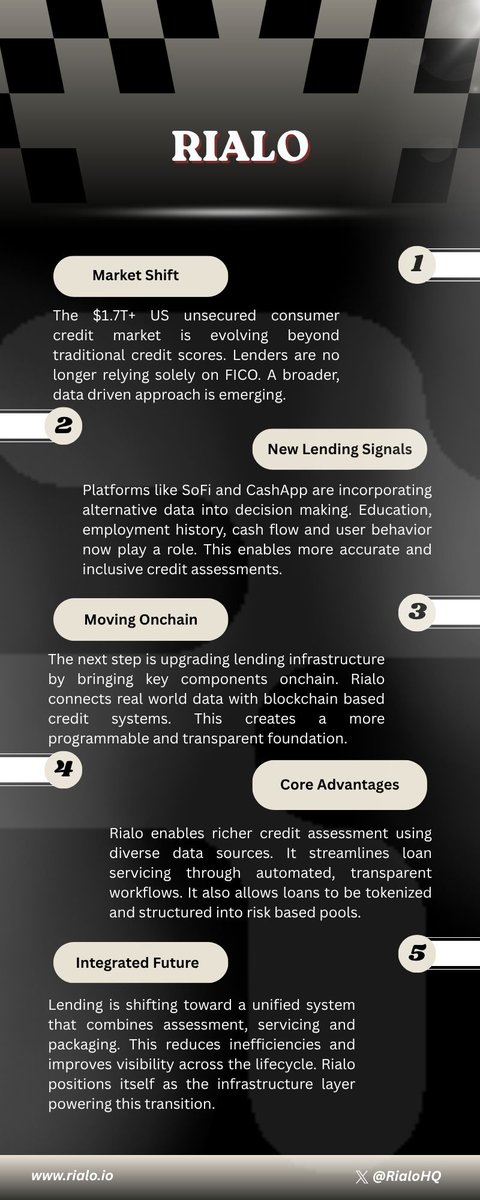
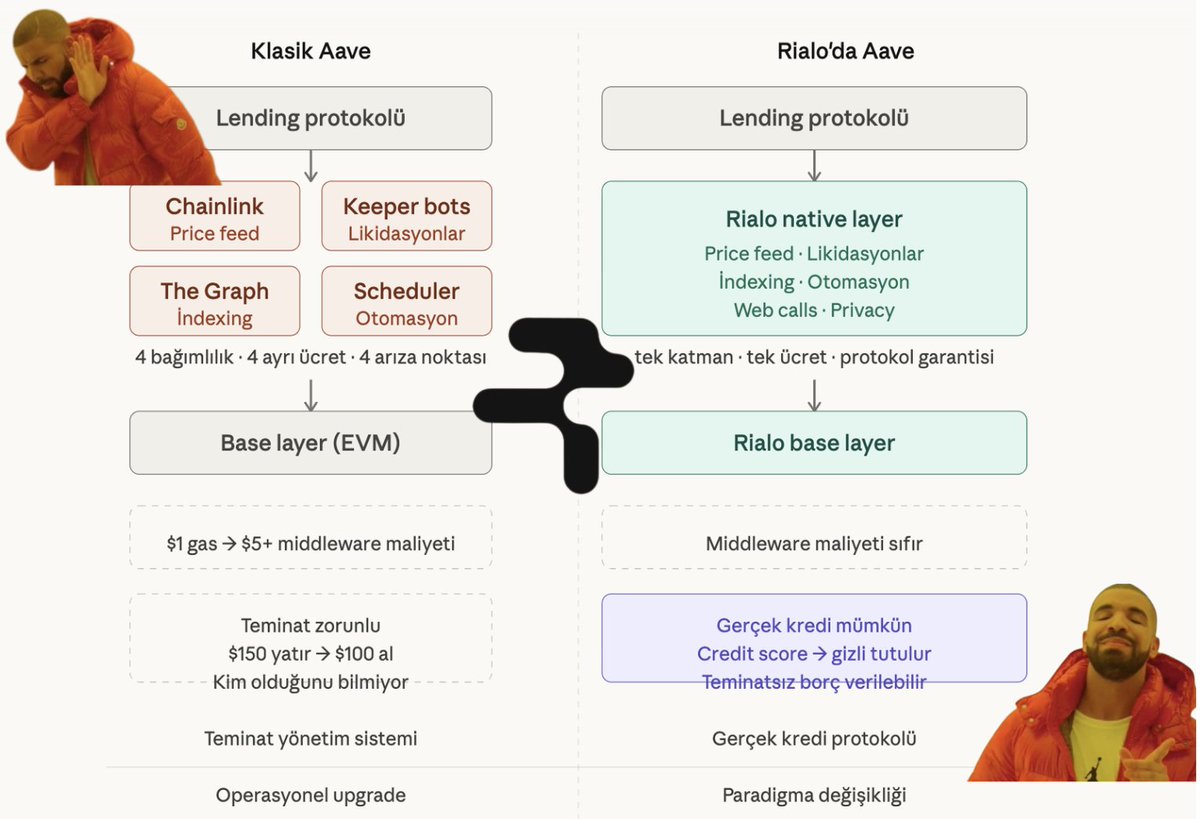
The RWA section is the one to read twice. You can't model risk from smoothed quarterly NAVs. Liquidation takes 30–90 days with 20–50% haircuts. The math breaks before it starts. But the deeper issue is older than DeFi: garbage in, garbage out. Smart contracts enforce rules perfectly, but they can't determine whether the inputs are true. Someone still has to feed real-world borrower data on-chain. If that party has bad incentives, you've rebuilt TradFi with extra steps. This is the oracle problem, applied to private credit. DeFi solved it for price feeds. Nobody has solved it for bespoke financial instruments: covenant compliance, borrower performance, collateral quality. That's the verification gap, and it's why private credit on permissionless rails keeps stalling. That's what we're building at Rialo.




Threshold cryptography is a cryptographic approach in which a secret key is distributed among multiple participants rather than being held by a single individual or system. In this model, a specific threshold value is defined, and a key related operation can only be performed when that specific number of participants come together. For example, in a "3 of 5" system, any three of the five participants can act in concert to generate a signature or authorize a transaction. This structure enhances security by eliminating the need to rely on a single point of trust. DKG, on the other hand, defines how this shared key is produced. While traditional methods involve a trusted distributor generating the key and splitting it into parts, DKG involves no such central authority. Instead, all participants contribute their own secret inputs to the process to collectively generate a shared key. The resulting key is a group secret something that no single participant knows individually, yet which can be utilized collectively. Polynomials form the mathematical foundation of DKG. Each participant embeds their own secret value into the constant term of a polynomial and uses this polynomial to generate shares for the other participants. Participants exchange these shares with one another over secure, private channels. Subsequently, each participant aggregates all the shares they have received to compute their own final key share. These final shares essentially represent the values of the shared polynomial which is itself a composite of all the participants contributions evaluated at specific points. When a threshold number of participants assemble, these shares are used either to reconstruct the original secret key or more commonly to perform cryptographic operations without ever revealing the key itself. At this stage, mathematical techniques such as Lagrange interpolation come into play, by utilizing a sufficient number of shares, it becomes possible to compute the constant term of the polynomial which corresponds to the value of the secret key. However, in most modern systems, the key is not directly reconstructed, instead, shares are used to generate outputs such as signatures. In threshold signature schemes, each participant generates a partial signature using their own key share. These partial signatures are then combined to produce a single valid signature. From an external perspective, this resulting signature appears as though it were generated by a standard private key and can be verified using the shared public key. Thus, the distributed structure is preserved while maintaining compatibility with standard cryptographic verification mechanisms. However, the basic DKG model assumes that participants behave honestly. In the real world, this assumption may not hold true, some participants may behave erroneously or maliciously. To address this issue, VSS is employed. VSS enables participants to prove the correctness of the shares they have generated. Participants publish cryptographic commitments regarding the coefficients of their polynomials, allowing others to verify whether the shares they have received align with these commitments. Consequently, the system becomes more resilient against erroneous or malicious behavior. DKG and threshold cryptography, working in tandem, offer a robust framework that eliminates the need for centralized trust. The private key never resides at a single point; operations are executed in a distributed manner yet, verifiable results are produced that, to the outside world, appear as though they were generated by a single key. @RialoHQ @RialoTR @slymnogunc







Distributed trust is the cornerstone of robust security. We are diving deep with a 5-part technical series on how threshold systems eliminate single points of failure by requiring a quorum of participants to execute cryptographic operations. The first two modules are now live: 01 | Distributed Key Generation: An analysis of how groups jointly generate shared keys without any participant gaining knowledge of the full secret. This lesson covers Shamir's Secret Sharing, Lagrange interpolation, and honest-world key generation. 02 | Verifiable Secret Sharing: Moving beyond the honest-world assumption. This module explores Feldman’s VSS for share verification and Pedersen’s protocol for achieving DKG without a trusted dealer through complaint-based disqualification. Stay tuned for the remaining three parts of the series. Link below: