Kyle - chaoticflaws.bsky.social 🇺🇦 retweetet
Kyle - chaoticflaws.bsky.social 🇺🇦
11.2K posts


Kyle - chaoticflaws.bsky.social 🇺🇦
@chaoticflaws
I'm a forensicating addict, President of MISEC Nonprofit, MiseCon/Converge/BSides Detroit Organizer, CSO Antigen Security #MISEC #DFIR https://t.co/cPof2JggDD
Beigetreten Nisan 2014
1.4K Folgt975 Follower
Kyle - chaoticflaws.bsky.social 🇺🇦 retweetet

claude-red is a curated library of offensive security skills designed for the Claude skills system. Each skill is a structured SKILL.mdfile that primes Claude with expert-level methodology for a specific attack surface from SQLi to shellcode, EDR evasion to exploit development.
Resource: github.com/SnailSploit/Cl…

English
Kyle - chaoticflaws.bsky.social 🇺🇦 retweetet

Kyle - chaoticflaws.bsky.social 🇺🇦 retweetet

This is one of the more fascinating malware write-ups I've read in a while.
Sentinel LABS covered fast16, a 2005 sabotage framework that was doing things most people associate with much later operations.
The malware used a driver to tamper with calculation software, but it also had automated methods to propagate through the network. It looked for the right applications, used Windows-native mechanisms, and took advantage of shared drives with weak passwords or no passwords.
This is a good takeaway because the sabotage only works well if the corrupted results become consistent across systems, so if one workstation gives bad results, someone may spot it. Having the testing and validation documents in the same flat network makes tampering easier.
Also, the mechanisms used to tamper with research are fascinating. A chain of operations starting from a filesystem driver, and very specific software targeting.
Sentinel really nailed this one, connecting everything together. Just goes to show that trying something different can take you somewhere unexpected. You never know what’s out there, and there are definitely more, newer samples like this.
Full report: sentinelone.com/labs/fast16-my…
English
Kyle - chaoticflaws.bsky.social 🇺🇦 retweetet

I checked and it's been 2 years since my last blog post??? So anyway, here's a quick blog post about KDP pool - the latest KDP feature that will replace the secure pool in future Windows versions: windows-internals.com/goodbye-secure…

English
Kyle - chaoticflaws.bsky.social 🇺🇦 retweetet

‼️ Bitwarden Statement on Checkmarx Supply Chain Incident:
"The Bitwarden security team identified and contained a malicious package that was briefly distributed through the npm delivery path for @bitwarden/cli@2026.4.0 between 5:57 PM and 7:30 PM (ET) on April 22, 2026, in connection with a broader Checkmarx supply chain incident.
The investigation found no evidence that end user vault data was accessed or at risk, or that production data or production systems were compromised. Once the issue was detected, compromised access was revoked, the malicious npm release was deprecated, and remediation steps were initiated immediately.
The issue affected the npm distribution mechanism for the CLI during that limited window, not the integrity of the legitimate Bitwarden CLI codebase or stored vault data.
Users who did not download the package from npm during that window were not affected. Bitwarden has completed a review of internal environments, release paths, and related systems, and no additional impacted products or environments have been identified at this time. A CVE for Bitwarden CLI version 2026.4.0 is being issued in connection with this incident."
community.bitwarden.com/t/bitwarden-st…
English
Kyle - chaoticflaws.bsky.social 🇺🇦 retweetet

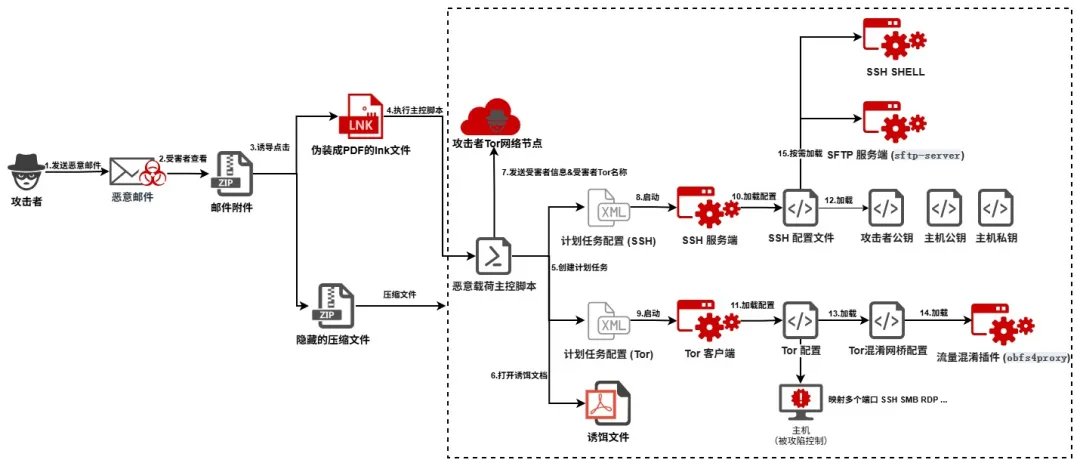
#APT #APT44 #Sandworm #VoodooBear #SSH #TOR #threat #malware
📍🇷🇺
💥🇺🇦🇪🇺🌍
⛓️ #Phishing > ZIP > #LNK (PDF decoy) > PS exec > Download next stage > Execute payloads (EXEs) > Persistence > Self-delete > SSH config + TOR > #C2 communication > Remote control
🔗360 Threat intel: mp.weixin.qq.com/s?__biz=MzUyMj…
English
Kyle - chaoticflaws.bsky.social 🇺🇦 retweetet
Kyle - chaoticflaws.bsky.social 🇺🇦 retweetet

AI agents are now a real, important persona alongside SOC analysts, security execs, and GRC managers.
Lenny Zeltser@lennyzeltser
English
Kyle - chaoticflaws.bsky.social 🇺🇦 retweetet
Kyle - chaoticflaws.bsky.social 🇺🇦 retweetet

I’ve been meaning to watch this talk for ages, and wow! 🤩 @fabian_bader managed to explain such a complex topic so clearly. I finally feel like I actually get Passkeys now! !🙌 youtube.com/watch?v=DQ4dnX…
Highly recommend giving this a watch

YouTube

English
Kyle - chaoticflaws.bsky.social 🇺🇦 retweetet

An update from NIST. Due to volume they’re only going to enrich CVEs that are meaningful to USG federal systems and critical software (some more nuance in the blog post). This means if you’re relying on the NVD data for your enterprise security program and use other software, your tools may not flag software you use as at risk. nist.gov/news-events/ne…
English
Kyle - chaoticflaws.bsky.social 🇺🇦 retweetet

Found some very common adware quietly killing antivirus products. Then we found an unregistered update domain, and anyone with $10 could have pushed any payload to 25,000+ endpoints, AV already disabled.
So we registered it first.
huntress.com/blog/pups-grow…
Big thanks to @_rdowd
English
Kyle - chaoticflaws.bsky.social 🇺🇦 retweetet

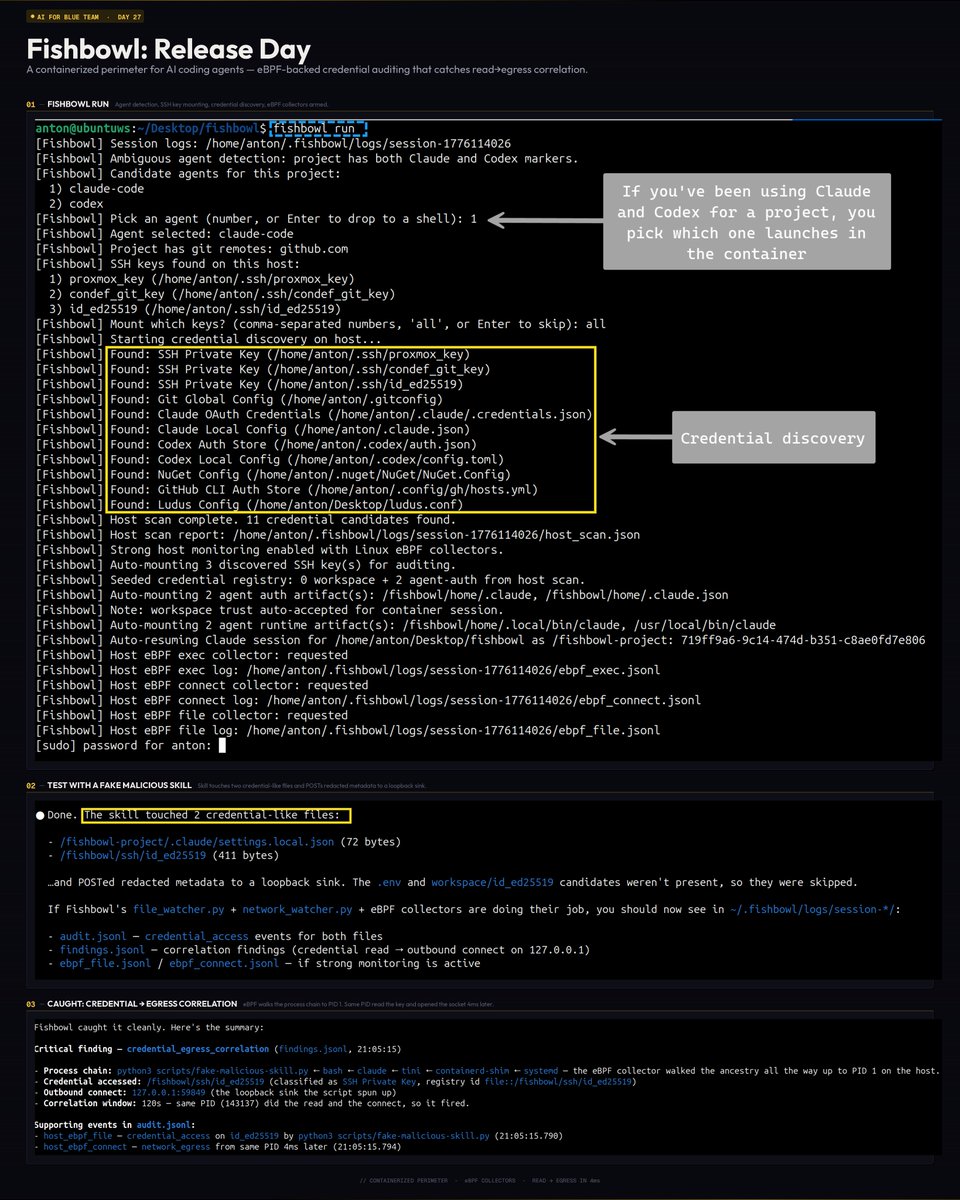
#AIForBlueTeam - Day 27!
Today I'm dropping a new tool 🔧
fishbowl is a containerized credential auditing perimeter for AI coding agents. It wraps Codex/Claude Code in Docker and audits credential access via eBPF.
Check out the git repo ( link below ) for more information and log samples.
English
Kyle - chaoticflaws.bsky.social 🇺🇦 retweetet

new YARA rule in signature-base for BlueHammer — a Windows LPE PoC that uses Defender itself to dump SAM.
short thread on how it works and what the rule keys on the thread🧵
github.com/Neo23x0/signat…
English
Kyle - chaoticflaws.bsky.social 🇺🇦 retweetet

robots take over the world or something i guess idk x.com/i/broadcasts/1…
English
Kyle - chaoticflaws.bsky.social 🇺🇦 retweetet

Registration is OPEN for Find Evil! the first hackathon for autonomous AI incident response. Built by the community, for the community. $22K+ in prizes.
Mission: Make Protocol SIFT, the framework connecting AI agents to the SIFT Workstation's full toolset, into a fully autonomous incident response agent.
SIFT Workstation is a beat to shreds, open-source incident response platform with 200+ tools. 19 years of community development. 60K+ downloads annually.
No incident response background required. New to AI? Good. Get your hands on the tools and learn with us.
Registration open April 1. Hackathon starts April 15. Submissions due June 15.
Register: findevil.devpost.com
Read more: robtlee73.substack.com/p/registration…
Sponsored by @SANSInstitute

English
Kyle - chaoticflaws.bsky.social 🇺🇦 retweetet

🚨 Big news: New TH Book 🏹
After years in Threat Hunting, I wrote the book I always wanted when I started.
The Art of Threat Hunting, practical, technical, no fluff.
⚡Hypothesis generation, queries & adaptation stuff, CTI-driven programs, documentation, team alignment. The full lifecycle.
🦖Full breakdown on the blog: rexorvc0.com
🔗Available on Amazon: amazon.com/Art-Threat-Hun…
#ThreatHunting #BlueTeam #Cybersecurity #Research #CTI #Malware #threat

English
Kyle - chaoticflaws.bsky.social 🇺🇦 retweetet
Kyle - chaoticflaws.bsky.social 🇺🇦 retweetet

We are still looking at the axios supply chain compromise, but we’ve attributed it to UNC1069, a suspected DPRK actor, who we covered in a blog this February. They are financially-motivated and historically DPRK uses these incidents to target crypto. cloud.google.com/blog/topics/th…
English


