Ryan Dowd retweetledi

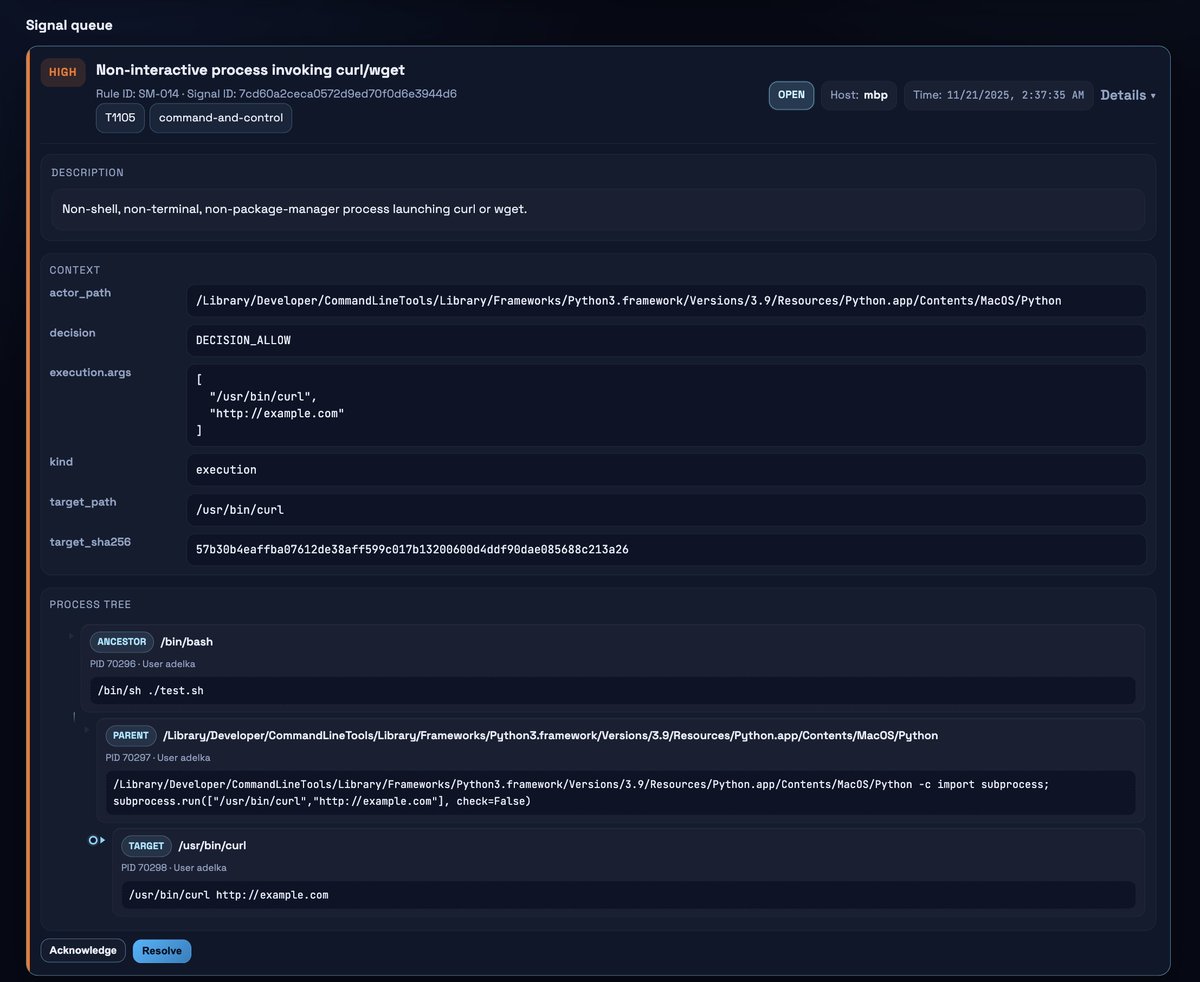
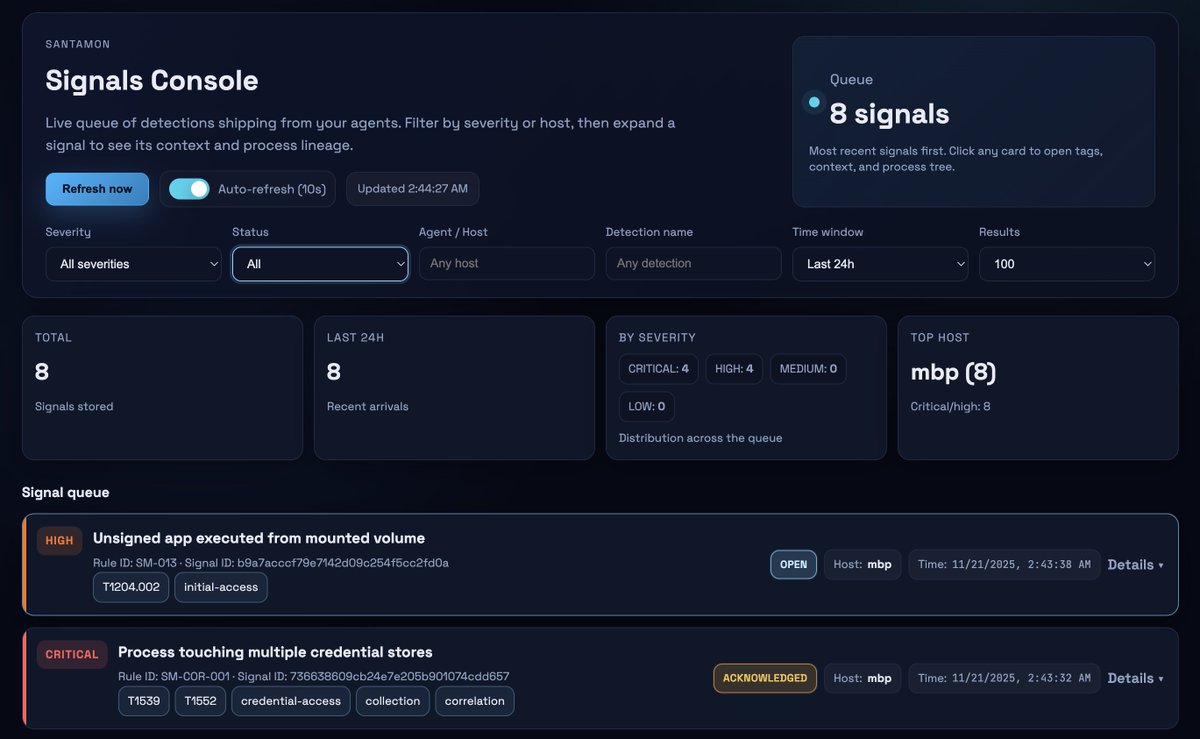
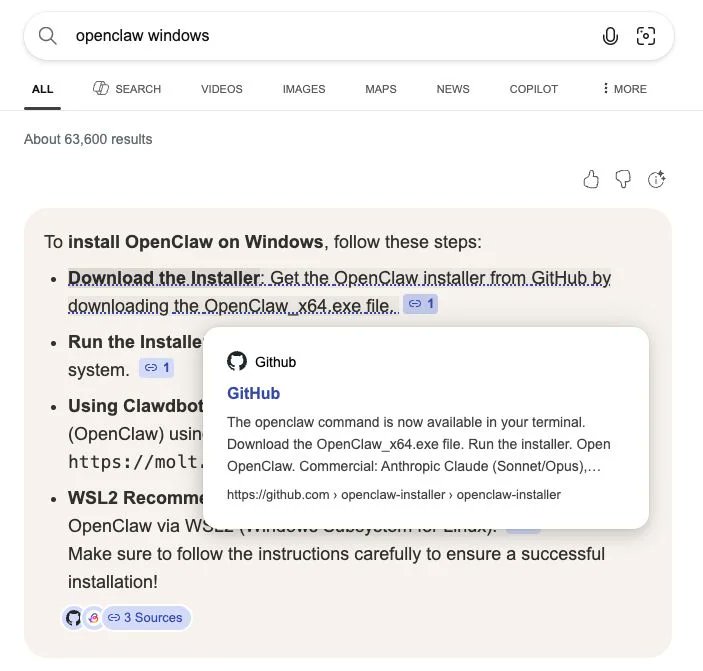
I teamed up with Ryan Dowd to investigate a fake OpenClaw installer hosted on GitHub. This was also picked up by Bing's AI and recommended as the correct way to install OpenClaw on Windows.
huntress.com/blog/openclaw-…
English