Ben
244 posts

Ben
@deobfuscately
threat intel @castle_io | building @synthient
Seattle, WA Beigetreten Kasım 2024
87 Folgt173 Follower

@FBIAnchorage Wait, was the botnet named Mossad or was Mossad operating one of the botnets?
English

🚨JUST IN🚨The Defense Criminal Investigative Service (DCIS), FBI Anchorage, and international partners disrupted four of the world’s largest Internet of Things (IoT) botnets that together were responsible for millions of infected devices and hundreds of thousands of DDoS attacks worldwide. 🔗ow.ly/PBQb50YwAHN
@USAO_AK | @DoD_IG

English
Ben retweetet

Synthient Helps Disrupt World's Largest DDoS Botnet
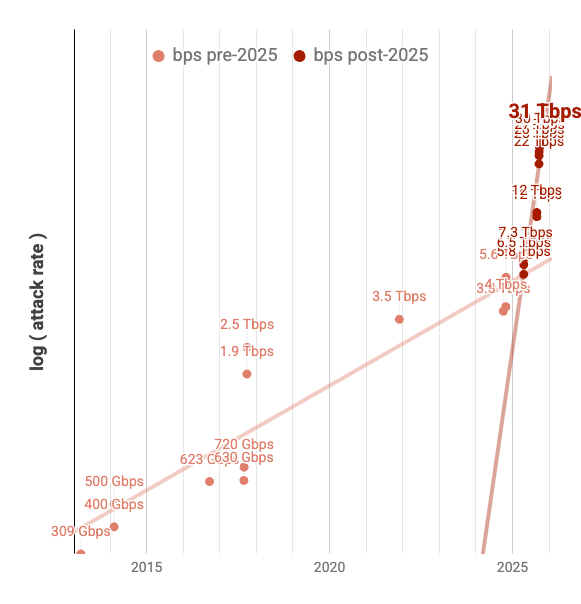
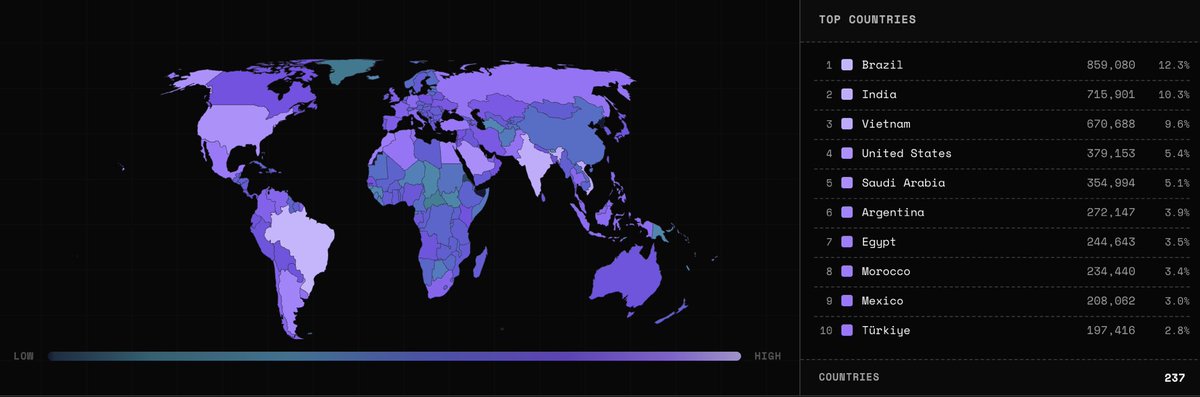
The U.S. Department of Justice, in coordination with international law enforcement, has announced a major operation to disrupt the infrastructure of four of the world’s largest IoT botnets, including Aisuru and Kimwolf. Together, these botnets hijacked over three million devices worldwide to launch record-breaking Distributed Denial of Service (DDoS) attacks.
The Kimwolf botnet specifically targeted devices traditionally firewalled from the broader internet, enslaving them to act as proxy traffic for criminal networks and launch attacks reaching up to 30 Terabits per second.
Synthient is proud to have contributed to the DOJ's efforts. By identifying active exploitation, sharing malware samples, and coordinating disclosures with impacted parties, we helped neutralize this threat. We remain dedicated to making the web a safer place and are grateful to have played a role in this historic takedown.
Link: justice.gov/usao-ak/pr/aut…
English

Everyone please go read my friends new blog post on the Russian Market
Obvane Group@ObvaneGroup
Russian Market reads less like a forum and more like a storefront with felonies. Obvane looks inside one of the largest criminal marketplaces online and the economy that formed around it. obvane.com/research/russi…
English

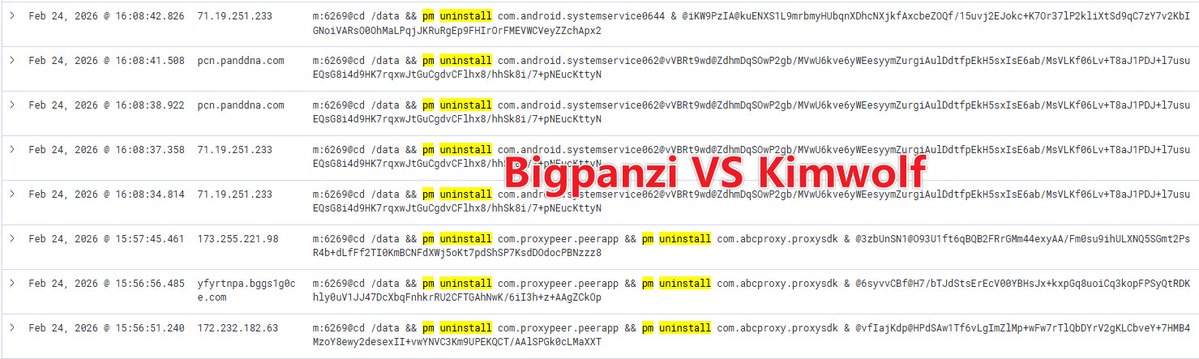
Not just bigpanzi 😄 other tv boxes also observed removing it
[
"com.n2.systemservice06",
"com.n2.systemservice061",
"com.n2.systemservice062",
"com.n2.systemservice063",
"com.n2.systemservice0644",
"com.android.systemservice0644",
"com.a.androidsvc",
"com.k.sdk",
"com.abcproxy.proxysdk",
"com.abcproxy.lolsdk"
]
English
Ben retweetet

@500mk500 Zscalar deleted your comment, lol
Zscaler ThreatLabz@Threatlabz
Zscaler ThreatLabz has published a technical analysis of Marco Stealer, an information stealer that our team discovered that harvests sensitive information including browser data and cryptocurrency wallets. Marco Stealer uses HTTP-based C2 communication with AES encrypted payloads. Read the full analysis here: zscaler.com/blogs/security…
English
Ben retweetet

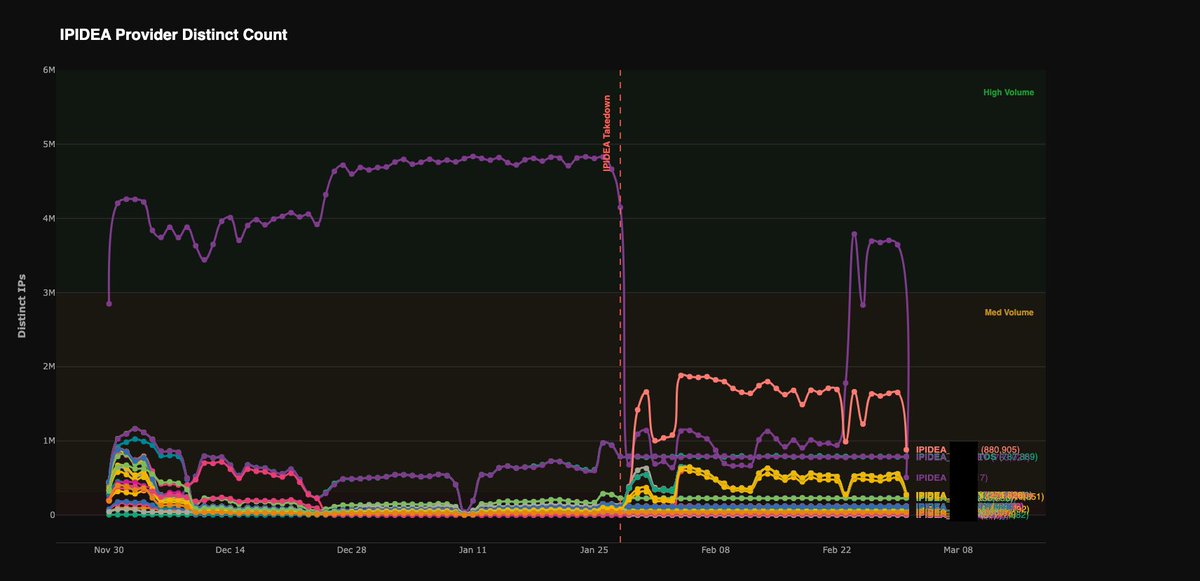
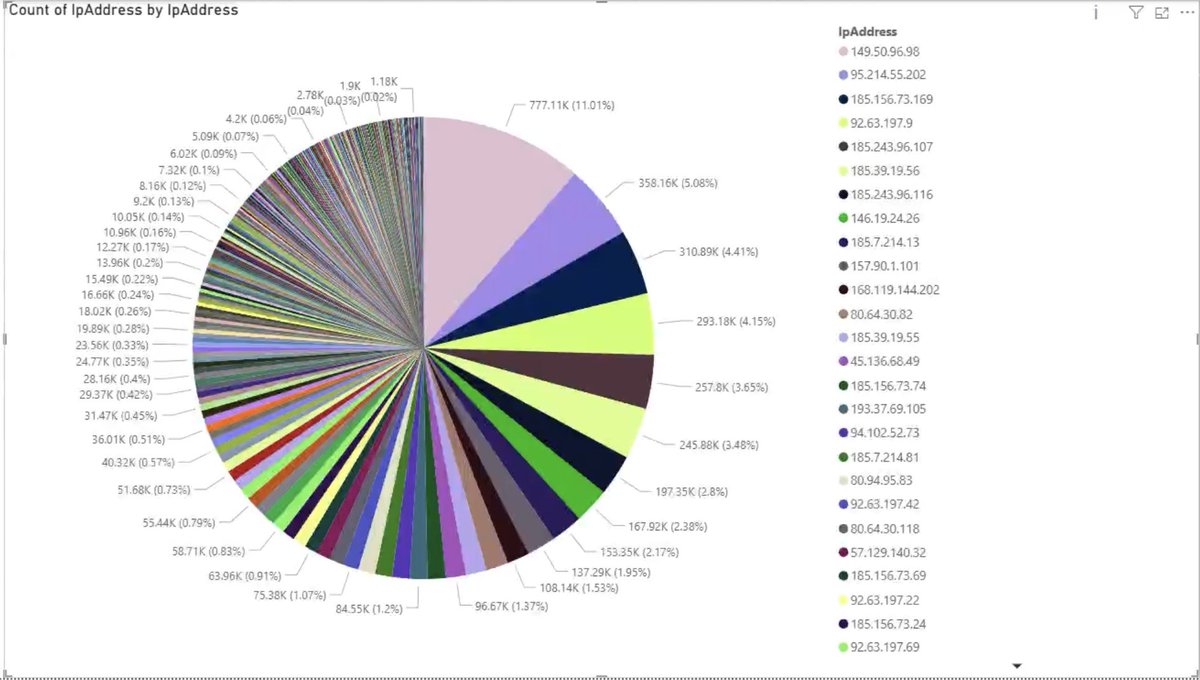
Google’s Threat Intelligence Team just disrupted one of the largest residential proxy network, IPIDEA.
Read more: cloud.google.com/blog/topics/th…
English
Ben retweetet

I exposed RDP to the internet for a year... it was hit with over 7 million authentication attempts from cyber criminals/botnets etc.
that's about 20K login attempts per day! to a single server.
#CyberCrime #Reality
English