Janggggg
1.1K posts


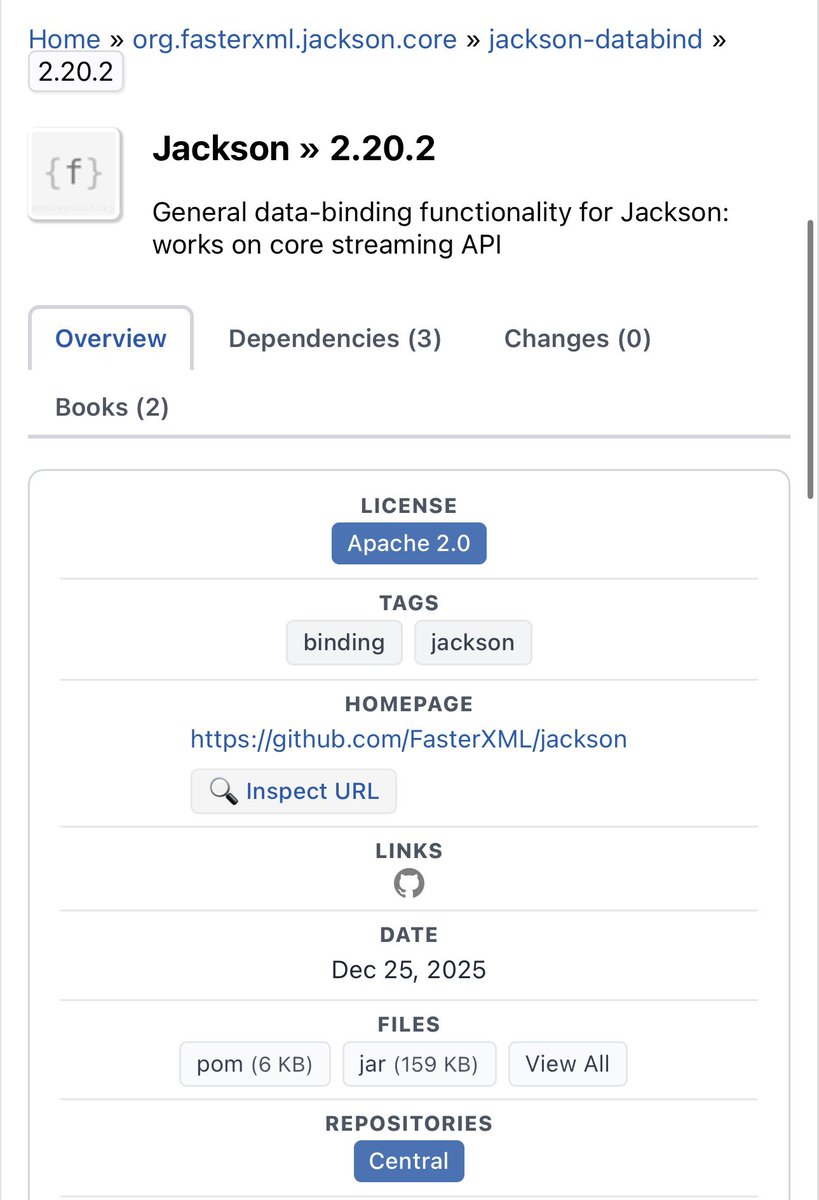
@testanull “What I’m looking for is a poisoned one — the prefix is ORG, not COM. Just a slight difference :-D
English

If anyone has downloaded this JAR, please let me know. I’d really appreciate it.
mvnrepository.com/artifact/org.f…
English
@pyn3rd Oh i am still able to download it rn, try this: repo1.maven.org/maven2/com/fas…
English
Janggggg retweetet

We promised we'd be back!
Join us on our journey, from repro'ing N-days to stumbling into 0-days in SolarWinds Web Help Desk, eventually achieving pre-auth RCE.
This research fuels the watchTowr Platform, our Preemptive Exposure Management technology.
labs.watchtowr.com/buy-a-help-des…
English
Janggggg retweetet

Ever wondered what happens when you pickle a mailbox? 🥒📬
(No, it’s not a recipe, it’s a vulnerability.)
Our team breaks down CVE-2025-20393 in a new deep dive post covering root cause, internals & exploitation details
starlabs.sg/blog/2026/01-p…
Written by @CurseRed & @bestswngs
English
Oracle E-Business Suite Authentication Bypass & RCE (CVE-2025-61882)
vred.mbbank.com.vn/p/oracle-e-bus…
English
Janggggg retweetet

From Zero to SYSTEM: Building PrintSpoofer from Scratch - @bl4ckarch
bl4ckarch.github.io/posts/PrintSpo…
English
testbnull.medium.com/and-then-and-t…
My note while trying to reproduce the famous react2shell bug,
no WAF bypass and bugbountytips inside, I promise ;)
Happy reading!
English
Janggggg retweetet

Oracle Cloud was breached in Jan 2025 through vulns in Oracle Access Manager. @SLCyberSec's Research team found a new pre-auth RCE vulnerability in Oracle Identity Manager (CVE-2025-61757). This is a critical vulnerability and is trivial to exploit. slcyber.io/research-cente…

English
Janggggg retweetet
Janggggg retweetet

We have published our AttackerKB @rapid7 Analysis for the recent GoAnywhere MFT vuln, CVE-2025-10035. It's an access control bypass + unsafe deserialization + an as-yet unknown issue in how an attacker can know a specific private key! attackerkb.com/topics/LbA9ANj…
English
Janggggg retweetet

NEED YOUR HELP!
My Friend/Teacher Soroush (@irsdl) Is looking for a new company to join, you know him as the .NET-God, the guy who has popped exchange, sharepoint, has maintained ysoserial_.net for years, contributed to the exploitation scene numerous times, taught all of you about what .net ghost webshells are, taught you about what viewstate exploitation is, how .net remoting exploitation issues can be solved, iis cookieless, web_config exploitation, countless of blogs, talks, techniques,...
but companies keep saying:
"we aren't hiring right now!"
if i was in position of hiring, woudln't wanna miss out on having one of THE BEST in my team
you're retweet is Extremely appreciated ❤️🔥
soroush, if you see this, don't hate me, had to do it without telling you
English
Janggggg retweetet

I had the pleasure of working with the web team at DFSEC for the last 2 years. If you feel you are wasting your time finding web 0days for marketing, I suggest you try this role as it requires you to think more outside the box to solve the hardest problems in web app security!
stypr@brokenpacifist
Dataflow Security has officially opened a position for a Web Security Researcher. dfsec.com/careers/
English

I made a quick write up discussing techniques to get code execution against Apache Spark SQL: muffsec.com/blog/getting-c…. I'm looking for advice on how to enumerate all the static methods that take a string argument for each JAR on the classpath.
English
Janggggg retweetet

We've added a new demo to NewRemotingTricks that makes deploying a MarshalByRefObject (e.g., WebClient) even easier: System.Lazy<T> creates an instance of T on serialization, which is probably more likely to be allowed than a XAML gadget getting through. github.com/codewhitesec/N…
English
@steventseeley @mufinnnnnnn github.com/waderwu/extrac… you might wanna try this, it can help building the codeql db for java closed-source lib :)
English

@mufinnnnnnn Other than that, you can try codeql, not sure if semgrep can do the number of argument filtering. Great blog post mate.
English

Someone sent me this good blog post last night which I had missed testbnull.medium.com/no-one-thing-w…
by @testanull
This is what I wanted to make a video about today but I don't need to anymore as the blog covers most of the tips (I was surprised seeing CVE-2024–38018 there too as I wanted to also mention it with a new ysonet release - I am still testing the code).
English
Janggggg retweetet

Semi-controversial thoughts on the recent #SharePoint patch & CVE-2025-53770 (ToolShell++ or ToolPain 🥸):
🪟On Microsoft’s effort:
I now believe MS genuinely tried to fix a flawed patch over the weekend before it was exploited by APTs. But several things went wrong beforehand:
- The initial patch left known bypasses which could have been avoided by a bit of testing.
- The original Defender workaround could also be bypassed.
- MS must have known about the ExcelData gadget since at least 2020:
srcincite.io/blog/2020/07/2…
but didn’t block it proactively.
- SP still relying on a blocklist that might be bypassed.
⌛️On exploitation of CVE-2025-53770:
I haven’t seen credible signs the new variant was exploited before the second patch.
I know the bypass chain, and none of the public payloads would have worked after the first patch.
🗞️On inaccurate information:
This blog post is misleading imho:
research.eye.security/sharepoint-und…
- It has used CVE-2025-53770 instead of CVE-2025-49704. Anyone reading that blog post would think the new variants were being exploited too.
- CVE-2025-49706 (auth check bypass) and its variant, CVE-2025-53771, won't do any good without the deserialization gadget afaik.
- It doesn't explain that attackers do not need to write a file to exploit this. Although it is obvious to technical folks, it may not be so obvious to others especially if we are giving advice.
- MS remains quiet on whether the vuln was exploited before the first patch. It would have been much better if MS could clear the water.
👎On the fallout: This will likely backfire on some researchers and vendors again due to inaccurate media hype even though this was a real N-day by the looks of it.
The part bypassing ParseAssemblyQualifiedName is difficult to be figured out quickly after the patch though; perhaps there are some smart people amongst bad guys too.
🤥On GitHub noise and our community:
GitHub is full of AI-generated or miscategorized PoCs for this vuln - e.g.
github.com/kaizensecurity…
We as a infosec/cybersec community should be better than this. Many of us went after the credit without actually adding much value in addition to what was published already.
I for one thought the bypasses are also being exploited too at some point last week (it was hard to verify them with all the noise and limited access to a working lab).
I salute those amongst us who keep calm and keep the world safer - no headlines, no ego, just consistent work that makes a real difference.🫡
Soroush Dalili@irsdl
Does anyone have a payload for CVE-2025-53770 (toolshell++), I have a feeling that what we have seen so far are related to CVE-2025-49704, and CVE-2025-53770 has not been exploited by malicious actors. Please prove me wrong! I'm not interested in the auth bypass part btw.
English

